mirror of
https://github.com/Security-Onion-Solutions/securityonion.git
synced 2026-03-20 11:45:35 +01:00
Compare commits
158 Commits
reyesj2-44
...
delta
| Author | SHA1 | Date | |
|---|---|---|---|
|
|
6e3986b0b0 | ||
|
|
2585bdd23f | ||
|
|
ca588d2e78 | ||
|
|
f756ecb396 | ||
|
|
82107f00a1 | ||
|
|
5c53244b54 | ||
|
|
3b269e8b82 | ||
|
|
7ece93d7e0 | ||
|
|
14d254e81b | ||
|
|
7af6efda1e | ||
|
|
ce972238fe | ||
|
|
442bd1499d | ||
|
|
30ea309dff | ||
|
|
bfeefeea2f | ||
|
|
8251d56a96 | ||
|
|
1b1e602716 | ||
|
|
034b1d045b | ||
|
|
20bf88b338 | ||
|
|
d3f819017b | ||
|
|
c92aedfff3 | ||
|
|
7aded184b3 | ||
|
|
d3938b61d2 | ||
|
|
c2c5aea244 | ||
|
|
83b7fecbbc | ||
|
|
d227cf71c8 | ||
|
|
020b9db610 | ||
|
|
cceaebe350 | ||
|
|
a982056363 | ||
|
|
db81834e06 | ||
|
|
318e4ec54b | ||
|
|
20bf05e9f3 | ||
|
|
4254769e68 | ||
|
|
c16ff2bd99 | ||
|
|
0c88b32fc2 | ||
|
|
0814f34f0e | ||
|
|
b6366e52ba | ||
|
|
825f377d2d | ||
|
|
74ad2990a7 | ||
|
|
738ce62d35 | ||
|
|
057ec6f0f1 | ||
|
|
20c4da50b1 | ||
|
|
5fb396fc09 | ||
|
|
a0b1e31717 | ||
|
|
cacae12ba3 | ||
|
|
83bd8a025c | ||
|
|
2a271b950b | ||
|
|
e19e83bebb | ||
|
|
066918e27d | ||
|
|
930985b770 | ||
|
|
346dc446de | ||
|
|
341471d38e | ||
|
|
2349750e13 | ||
|
|
00986dc2fd | ||
|
|
d60bef1371 | ||
|
|
5806a85214 | ||
|
|
2d97dfc8a1 | ||
|
|
d6263812a6 | ||
|
|
ef7d1771ab | ||
|
|
4dc377c99f | ||
|
|
a52e5d0474 | ||
|
|
1a943aefc5 | ||
|
|
4bb61d999d | ||
|
|
e0e0e3e97b | ||
|
|
6b039b3f94 | ||
|
|
d2d2f0cb5f | ||
|
|
e6ee7dac7c | ||
|
|
7bf63b822d | ||
|
|
1a7d72c630 | ||
|
|
4224713cc6 | ||
|
|
b452e70419 | ||
|
|
6809497730 | ||
|
|
70597a77ab | ||
|
|
f5faf86cb3 | ||
|
|
be4e253620 | ||
|
|
ebc1152376 | ||
|
|
625bfb3ba7 | ||
|
|
c11b83c712 | ||
|
|
a3b471c1d1 | ||
|
|
eaf3f10adc | ||
|
|
84f4e460f6 | ||
|
|
88841c9814 | ||
|
|
64bb0dfb5b | ||
|
|
ddb26a9f42 | ||
|
|
744d8fdd5e | ||
|
|
6feb06e623 | ||
|
|
afc14ec29d | ||
|
|
59134c65d0 | ||
|
|
614537998a | ||
|
|
d2cee468a0 | ||
|
|
94f454c311 | ||
|
|
17881c9a36 | ||
|
|
5b2def6fdd | ||
|
|
9b6d29212d | ||
|
|
c1bff03b1c | ||
|
|
b00f113658 | ||
|
|
7dcd923ebf | ||
|
|
1fcd8a7c1a | ||
|
|
4a89f7f26b | ||
|
|
a9196348ab | ||
|
|
12dec366e0 | ||
|
|
1713f6af76 | ||
|
|
7f4adb70bd | ||
|
|
e2483e4be0 | ||
|
|
322c0b8d56 | ||
|
|
81c1d8362d | ||
|
|
d1156ee3fd | ||
|
|
18f971954b | ||
|
|
e55ac7062c | ||
|
|
c178eada22 | ||
|
|
92213e302f | ||
|
|
72193b0249 | ||
|
|
066d7106b0 | ||
|
|
589de8e361 | ||
|
|
914cd8b611 | ||
|
|
845290595e | ||
|
|
544b60d111 | ||
|
|
aa0787b0ff | ||
|
|
89f144df75 | ||
|
|
cfccbe2bed | ||
|
|
3dd9a06d67 | ||
|
|
4bfe9039ed | ||
|
|
75cddbf444 | ||
|
|
89b18341c5 | ||
|
|
90137f7093 | ||
|
|
480187b1f5 | ||
|
|
b3ed54633f | ||
|
|
0360d4145c | ||
|
|
2bec5afcdd | ||
|
|
4539024280 | ||
|
|
398bd0c1da | ||
|
|
91759587f5 | ||
|
|
bc9841ea8c | ||
|
|
32241faf55 | ||
|
|
685e22bd68 | ||
|
|
88de779ff7 | ||
|
|
d452694c55 | ||
|
|
7fba8ac2b4 | ||
|
|
0738208627 | ||
|
|
a3720219d8 | ||
|
|
385726b87c | ||
|
|
d78a5867b8 | ||
|
|
ad960c2101 | ||
|
|
7f07c96a2f | ||
|
|
90bea975d0 | ||
|
|
e8adea3022 | ||
|
|
71839bc87f | ||
|
|
6809a40257 | ||
|
|
cea55a72c3 | ||
|
|
e38a4a21ee | ||
|
|
7ac1e767ab | ||
|
|
2c4d833a5b | ||
|
|
41d3dd0aa5 | ||
|
|
6050ab6b21 | ||
|
|
ae05251359 | ||
|
|
f23158aed5 | ||
|
|
b03b75315d | ||
|
|
cbd98efaf4 | ||
|
|
1f7bf1fd88 |
6
.github/DISCUSSION_TEMPLATE/2-4.yml
vendored
6
.github/DISCUSSION_TEMPLATE/2-4.yml
vendored
@@ -2,13 +2,11 @@ body:
|
||||
- type: markdown
|
||||
attributes:
|
||||
value: |
|
||||
⚠️ This category is solely for conversations related to Security Onion 2.4 ⚠️
|
||||
|
||||
If your organization needs more immediate, enterprise grade professional support, with one-on-one virtual meetings and screensharing, contact us via our website: https://securityonion.com/support
|
||||
- type: dropdown
|
||||
attributes:
|
||||
label: Version
|
||||
description: Which version of Security Onion 2.4.x are you asking about?
|
||||
description: Which version of Security Onion are you asking about?
|
||||
options:
|
||||
-
|
||||
- 2.4.10
|
||||
@@ -35,7 +33,7 @@ body:
|
||||
- 2.4.200
|
||||
- 2.4.201
|
||||
- 2.4.210
|
||||
- 3.0.0
|
||||
- 2.4.211
|
||||
- Other (please provide detail below)
|
||||
validations:
|
||||
required: true
|
||||
|
||||
177
.github/DISCUSSION_TEMPLATE/3-0.yml
vendored
Normal file
177
.github/DISCUSSION_TEMPLATE/3-0.yml
vendored
Normal file
@@ -0,0 +1,177 @@
|
||||
body:
|
||||
- type: markdown
|
||||
attributes:
|
||||
value: |
|
||||
If your organization needs more immediate, enterprise grade professional support, with one-on-one virtual meetings and screensharing, contact us via our website: https://securityonion.com/support
|
||||
- type: dropdown
|
||||
attributes:
|
||||
label: Version
|
||||
description: Which version of Security Onion are you asking about?
|
||||
options:
|
||||
-
|
||||
- 3.0.0
|
||||
- Other (please provide detail below)
|
||||
validations:
|
||||
required: true
|
||||
- type: dropdown
|
||||
attributes:
|
||||
label: Installation Method
|
||||
description: How did you install Security Onion?
|
||||
options:
|
||||
-
|
||||
- Security Onion ISO image
|
||||
- Cloud image (Amazon, Azure, Google)
|
||||
- Network installation on Oracle 9 (unsupported)
|
||||
- Other (please provide detail below)
|
||||
validations:
|
||||
required: true
|
||||
- type: dropdown
|
||||
attributes:
|
||||
label: Description
|
||||
description: >
|
||||
Is this discussion about installation, configuration, upgrading, or other?
|
||||
options:
|
||||
-
|
||||
- installation
|
||||
- configuration
|
||||
- upgrading
|
||||
- other (please provide detail below)
|
||||
validations:
|
||||
required: true
|
||||
- type: dropdown
|
||||
attributes:
|
||||
label: Installation Type
|
||||
description: >
|
||||
When you installed, did you choose Import, Eval, Standalone, Distributed, or something else?
|
||||
options:
|
||||
-
|
||||
- Import
|
||||
- Eval
|
||||
- Standalone
|
||||
- Distributed
|
||||
- other (please provide detail below)
|
||||
validations:
|
||||
required: true
|
||||
- type: dropdown
|
||||
attributes:
|
||||
label: Location
|
||||
description: >
|
||||
Is this deployment in the cloud, on-prem with Internet access, or airgap?
|
||||
options:
|
||||
-
|
||||
- cloud
|
||||
- on-prem with Internet access
|
||||
- airgap
|
||||
- other (please provide detail below)
|
||||
validations:
|
||||
required: true
|
||||
- type: dropdown
|
||||
attributes:
|
||||
label: Hardware Specs
|
||||
description: >
|
||||
Does your hardware meet or exceed the minimum requirements for your installation type as shown at https://securityonion.net/docs/hardware?
|
||||
options:
|
||||
-
|
||||
- Meets minimum requirements
|
||||
- Exceeds minimum requirements
|
||||
- Does not meet minimum requirements
|
||||
- other (please provide detail below)
|
||||
validations:
|
||||
required: true
|
||||
- type: input
|
||||
attributes:
|
||||
label: CPU
|
||||
description: How many CPU cores do you have?
|
||||
validations:
|
||||
required: true
|
||||
- type: input
|
||||
attributes:
|
||||
label: RAM
|
||||
description: How much RAM do you have?
|
||||
validations:
|
||||
required: true
|
||||
- type: input
|
||||
attributes:
|
||||
label: Storage for /
|
||||
description: How much storage do you have for the / partition?
|
||||
validations:
|
||||
required: true
|
||||
- type: input
|
||||
attributes:
|
||||
label: Storage for /nsm
|
||||
description: How much storage do you have for the /nsm partition?
|
||||
validations:
|
||||
required: true
|
||||
- type: dropdown
|
||||
attributes:
|
||||
label: Network Traffic Collection
|
||||
description: >
|
||||
Are you collecting network traffic from a tap or span port?
|
||||
options:
|
||||
-
|
||||
- tap
|
||||
- span port
|
||||
- other (please provide detail below)
|
||||
validations:
|
||||
required: true
|
||||
- type: dropdown
|
||||
attributes:
|
||||
label: Network Traffic Speeds
|
||||
description: >
|
||||
How much network traffic are you monitoring?
|
||||
options:
|
||||
-
|
||||
- Less than 1Gbps
|
||||
- 1Gbps to 10Gbps
|
||||
- more than 10Gbps
|
||||
validations:
|
||||
required: true
|
||||
- type: dropdown
|
||||
attributes:
|
||||
label: Status
|
||||
description: >
|
||||
Does SOC Grid show all services on all nodes as running OK?
|
||||
options:
|
||||
-
|
||||
- Yes, all services on all nodes are running OK
|
||||
- No, one or more services are failed (please provide detail below)
|
||||
validations:
|
||||
required: true
|
||||
- type: dropdown
|
||||
attributes:
|
||||
label: Salt Status
|
||||
description: >
|
||||
Do you get any failures when you run "sudo salt-call state.highstate"?
|
||||
options:
|
||||
-
|
||||
- Yes, there are salt failures (please provide detail below)
|
||||
- No, there are no failures
|
||||
validations:
|
||||
required: true
|
||||
- type: dropdown
|
||||
attributes:
|
||||
label: Logs
|
||||
description: >
|
||||
Are there any additional clues in /opt/so/log/?
|
||||
options:
|
||||
-
|
||||
- Yes, there are additional clues in /opt/so/log/ (please provide detail below)
|
||||
- No, there are no additional clues
|
||||
validations:
|
||||
required: true
|
||||
- type: textarea
|
||||
attributes:
|
||||
label: Detail
|
||||
description: Please read our discussion guidelines at https://github.com/Security-Onion-Solutions/securityonion/discussions/1720 and then provide detailed information to help us help you.
|
||||
placeholder: |-
|
||||
STOP! Before typing, please read our discussion guidelines at https://github.com/Security-Onion-Solutions/securityonion/discussions/1720 in their entirety!
|
||||
|
||||
If your organization needs more immediate, enterprise grade professional support, with one-on-one virtual meetings and screensharing, contact us via our website: https://securityonion.com/support
|
||||
validations:
|
||||
required: true
|
||||
- type: checkboxes
|
||||
attributes:
|
||||
label: Guidelines
|
||||
options:
|
||||
- label: I have read the discussion guidelines at https://github.com/Security-Onion-Solutions/securityonion/discussions/1720 and assert that I have followed the guidelines.
|
||||
required: true
|
||||
2
.github/workflows/pythontest.yml
vendored
2
.github/workflows/pythontest.yml
vendored
@@ -13,7 +13,7 @@ jobs:
|
||||
strategy:
|
||||
fail-fast: false
|
||||
matrix:
|
||||
python-version: ["3.13"]
|
||||
python-version: ["3.14"]
|
||||
python-code-path: ["salt/sensoroni/files/analyzers", "salt/manager/tools/sbin"]
|
||||
|
||||
steps:
|
||||
|
||||
66
README.md
66
README.md
@@ -1,50 +1,58 @@
|
||||
## Security Onion 2.4
|
||||
<p align="center">
|
||||
<img src="https://securityonionsolutions.com/logo/logo-so-onion-dark.svg" width="400" alt="Security Onion Logo">
|
||||
</p>
|
||||
|
||||
Security Onion 2.4 is here!
|
||||
# Security Onion
|
||||
|
||||
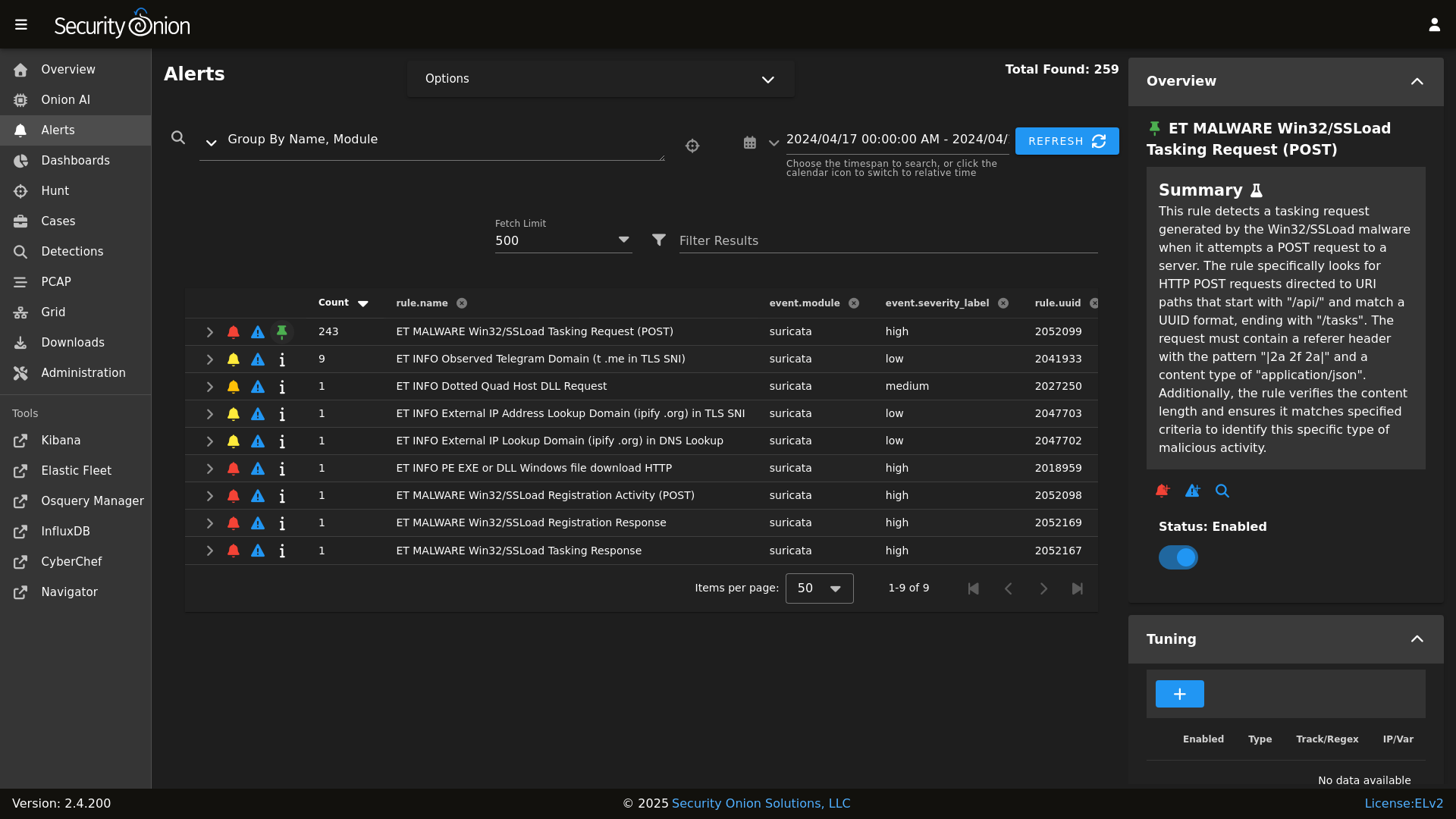
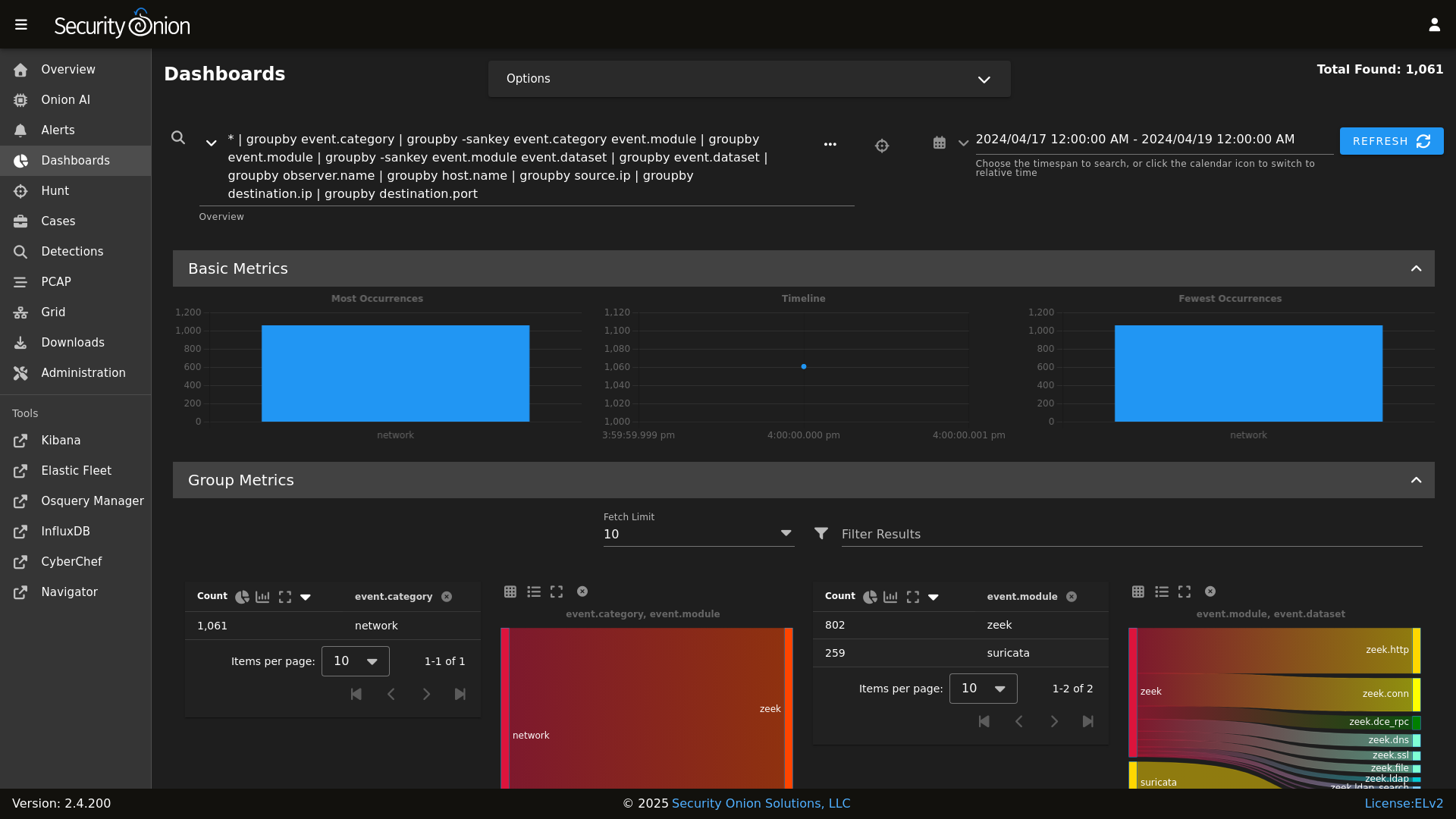
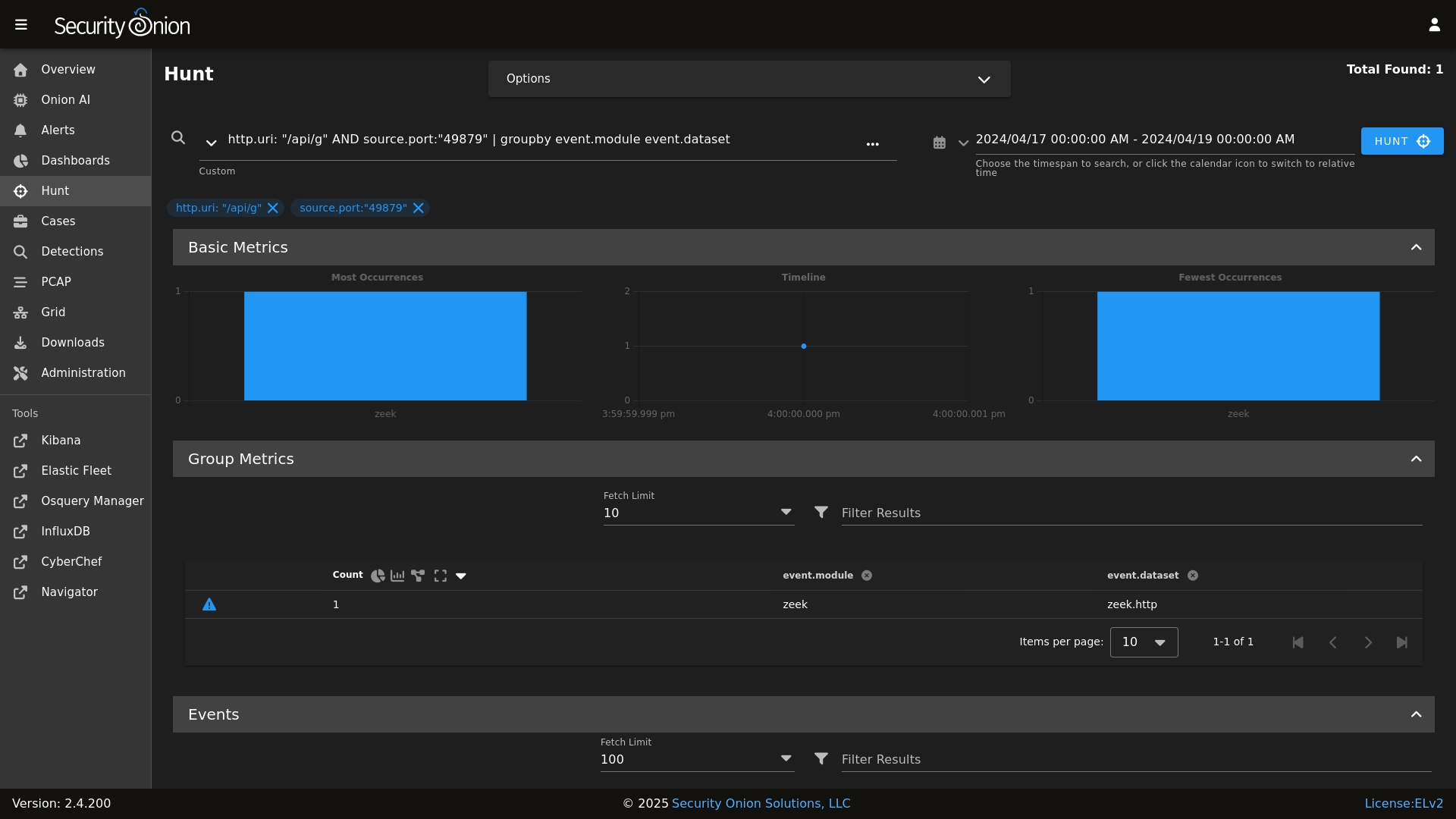
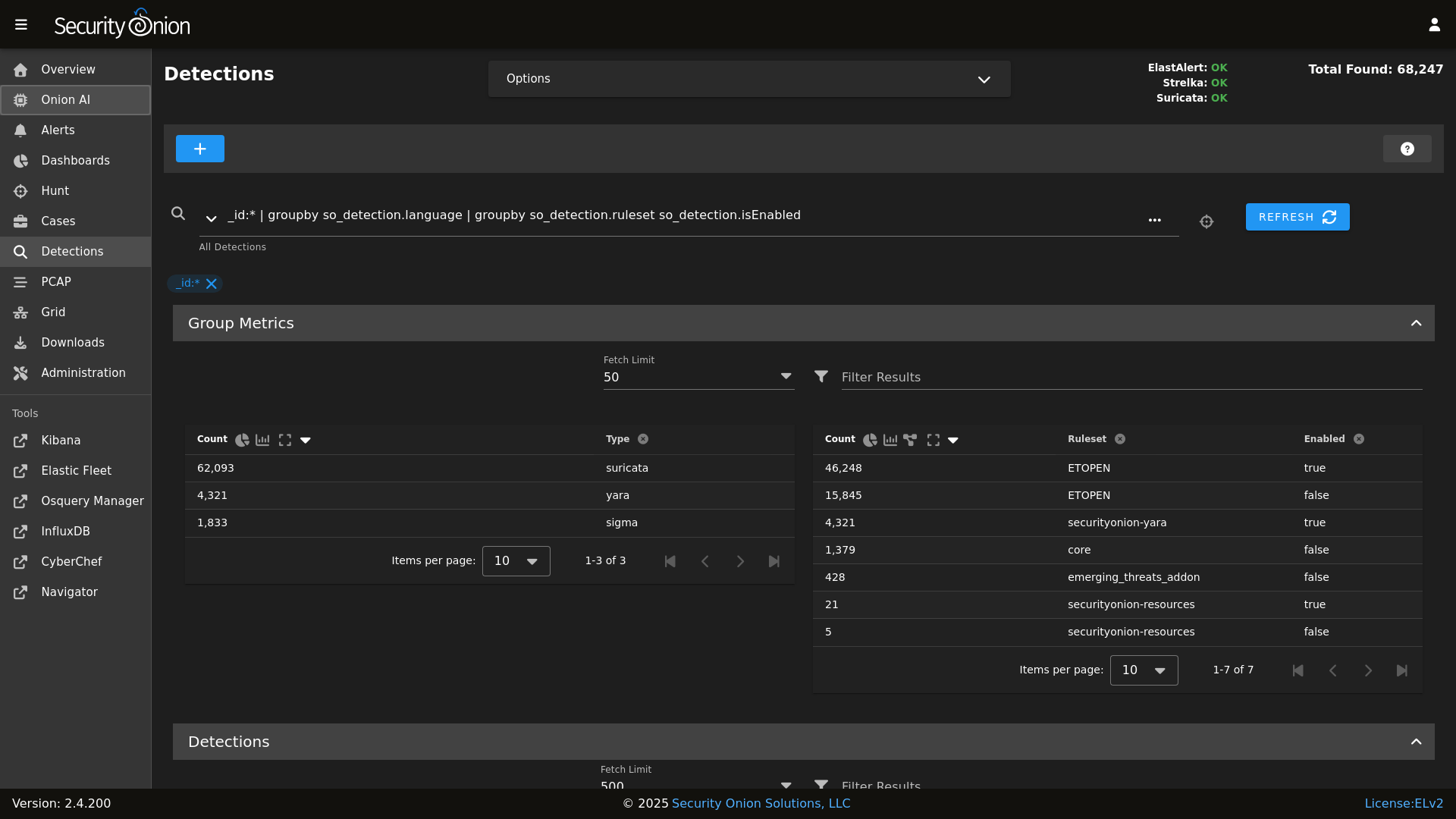
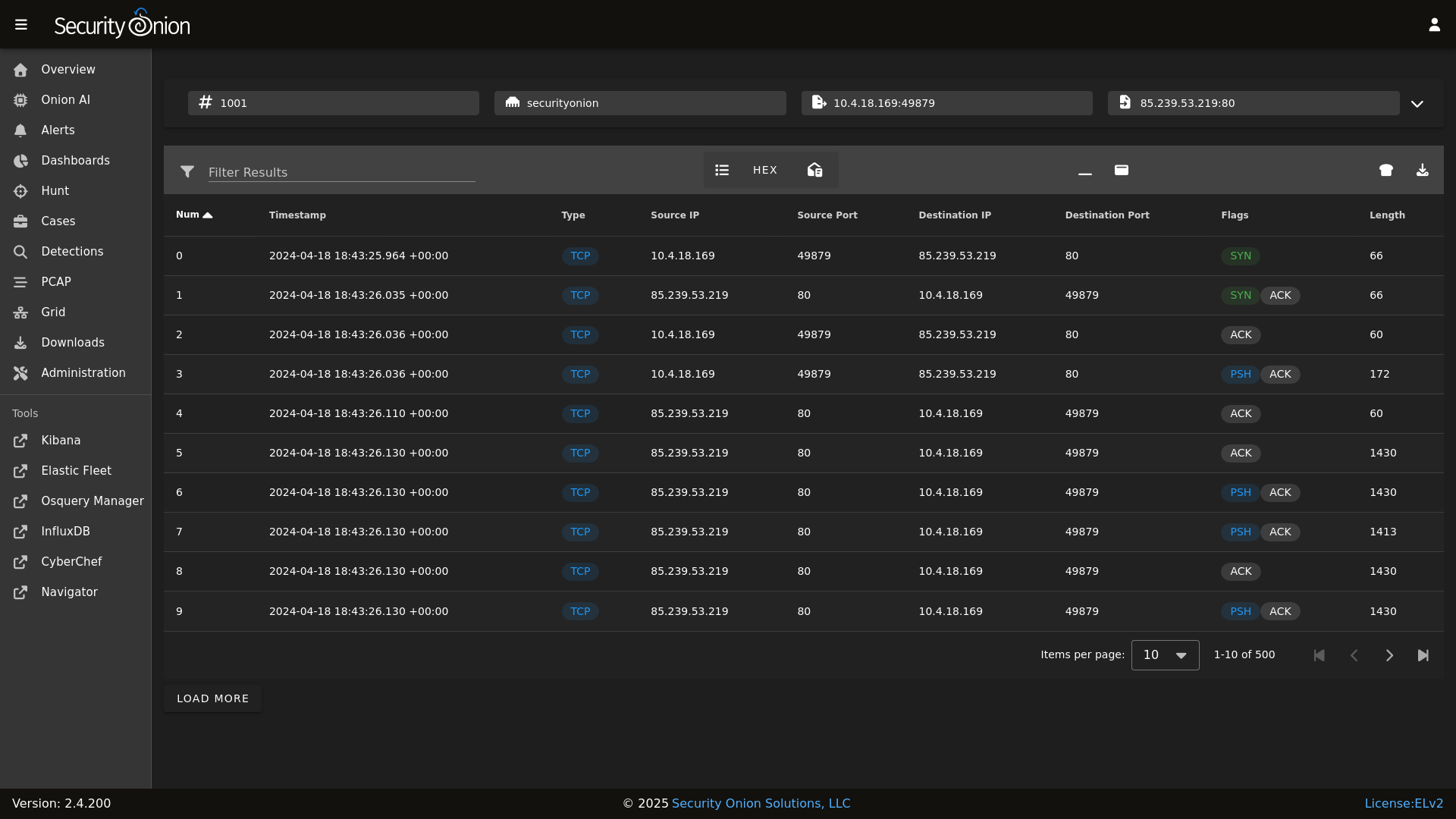
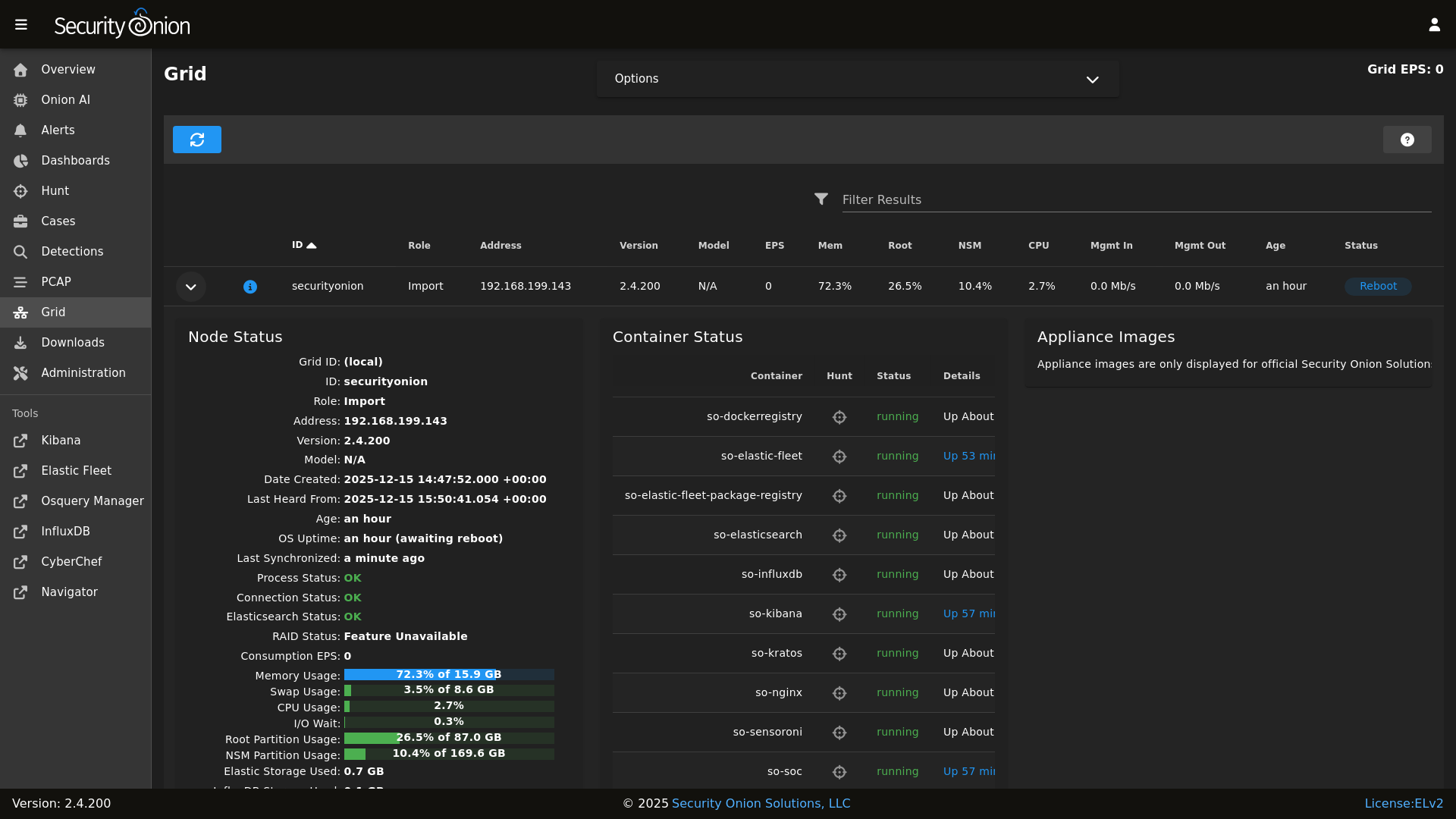
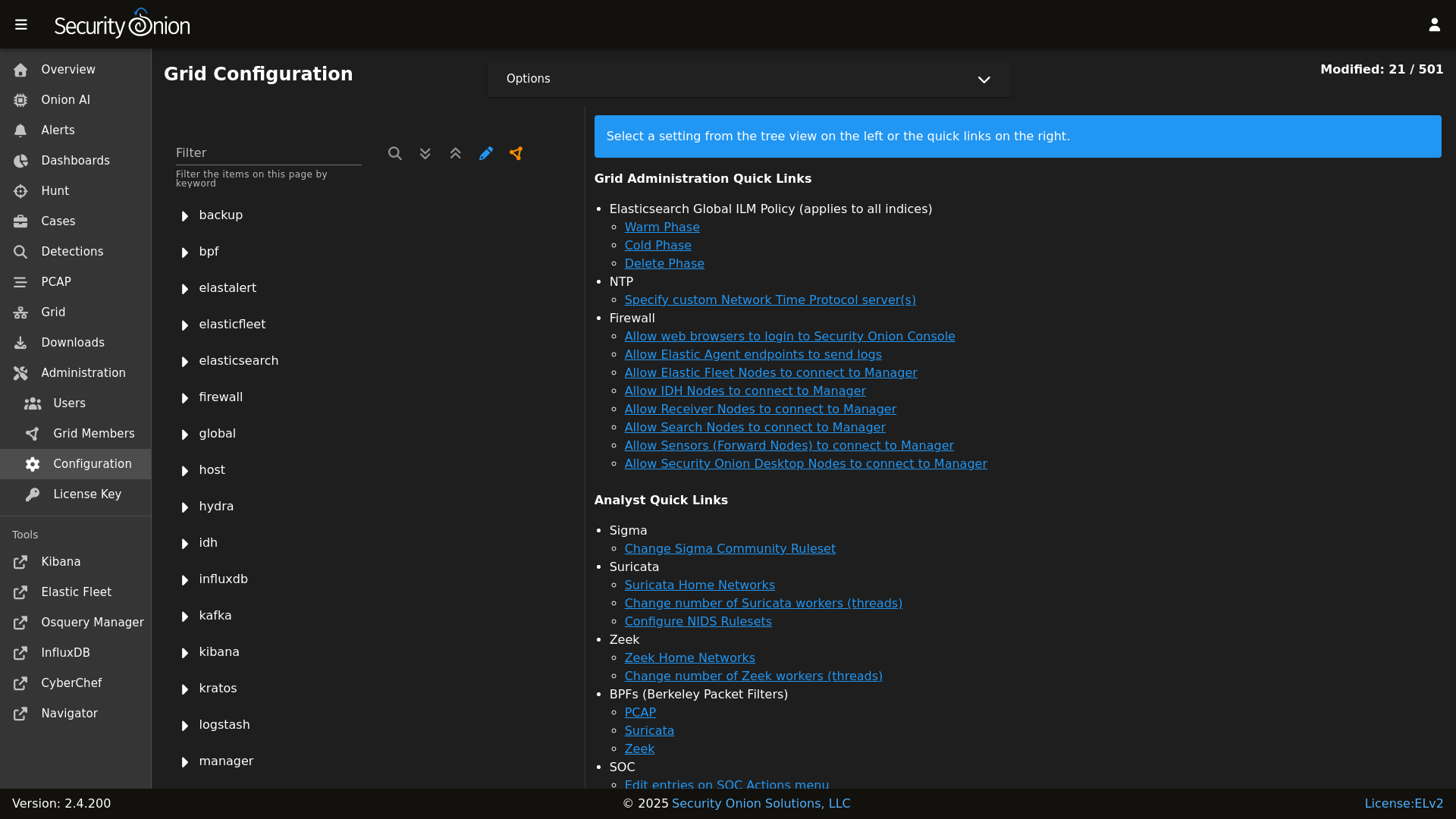
## Screenshots
|
||||
Security Onion is a free and open Linux distribution for threat hunting, enterprise security monitoring, and log management. It includes a comprehensive suite of tools designed to work together to provide visibility into your network and host activity.
|
||||
|
||||
Alerts
|
||||
|
||||
## ✨ Features
|
||||
|
||||
Dashboards
|
||||
|
||||
Security Onion includes everything you need to monitor your network and host systems:
|
||||
|
||||
Hunt
|
||||
|
||||
* **Security Onion Console (SOC)**: A unified web interface for analyzing security events and managing your grid.
|
||||
* **Elastic Stack**: Powerful search backed by Elasticsearch.
|
||||
* **Intrusion Detection**: Network-based IDS with Suricata and host-based monitoring with Elastic Fleet.
|
||||
* **Network Metadata**: Detailed network metadata generated by Zeek or Suricata.
|
||||
* **Full Packet Capture**: Retain and analyze raw network traffic with Suricata PCAP.
|
||||
|
||||
Detections
|
||||
|
||||
## ⭐ Security Onion Pro
|
||||
|
||||
PCAP
|
||||
|
||||
For organizations and enterprises requiring advanced capabilities, **Security Onion Pro** offers additional features designed for scale and efficiency:
|
||||
|
||||
Grid
|
||||
|
||||
* **Onion AI**: Leverage powerful AI-driven insights to accelerate your analysis and investigations.
|
||||
* **Enterprise Features**: Enhanced tools and integrations tailored for enterprise-grade security operations.
|
||||
|
||||
Config
|
||||
|
||||
For more information, visit the [Security Onion Pro](https://securityonionsolutions.com/pro) page.
|
||||
|
||||
### Release Notes
|
||||
## ☁️ Cloud Deployment
|
||||
|
||||
https://securityonion.net/docs/release-notes
|
||||
Security Onion is available and ready to deploy in the **AWS**, **Azure**, and **Google Cloud (GCP)** marketplaces.
|
||||
|
||||
### Requirements
|
||||
## 🚀 Getting Started
|
||||
|
||||
https://securityonion.net/docs/hardware
|
||||
| Goal | Resource |
|
||||
| :--- | :--- |
|
||||
| **Download** | [Security Onion ISO](https://securityonion.net/docs/download) |
|
||||
| **Requirements** | [Hardware Guide](https://securityonion.net/docs/hardware) |
|
||||
| **Install** | [Installation Instructions](https://securityonion.net/docs/installation) |
|
||||
| **What's New** | [Release Notes](https://securityonion.net/docs/release-notes) |
|
||||
|
||||
### Download
|
||||
## 📖 Documentation & Support
|
||||
|
||||
https://securityonion.net/docs/download
|
||||
For more detailed information, please visit our [Documentation](https://docs.securityonion.net).
|
||||
|
||||
### Installation
|
||||
* **FAQ**: [Frequently Asked Questions](https://securityonion.net/docs/faq)
|
||||
* **Community**: [Discussions & Support](https://securityonion.net/docs/community-support)
|
||||
* **Training**: [Official Training](https://securityonion.net/training)
|
||||
|
||||
https://securityonion.net/docs/installation
|
||||
## 🤝 Contributing
|
||||
|
||||
### FAQ
|
||||
We welcome contributions! Please see our [CONTRIBUTING.md](CONTRIBUTING.md) for guidelines on how to get involved.
|
||||
|
||||
https://securityonion.net/docs/faq
|
||||
## 🛡️ License
|
||||
|
||||
### Feedback
|
||||
Security Onion is licensed under the terms of the license found in the [LICENSE](LICENSE) file.
|
||||
|
||||
https://securityonion.net/docs/community-support
|
||||
---
|
||||
*Built with 🧅 by Security Onion Solutions.*
|
||||
|
||||
@@ -4,6 +4,7 @@
|
||||
|
||||
| Version | Supported |
|
||||
| ------- | ------------------ |
|
||||
| 3.x | :white_check_mark: |
|
||||
| 2.4.x | :white_check_mark: |
|
||||
| 2.3.x | :x: |
|
||||
| 16.04.x | :x: |
|
||||
|
||||
@@ -87,8 +87,6 @@ base:
|
||||
- zeek.adv_zeek
|
||||
- bpf.soc_bpf
|
||||
- bpf.adv_bpf
|
||||
- pcap.soc_pcap
|
||||
- pcap.adv_pcap
|
||||
- suricata.soc_suricata
|
||||
- suricata.adv_suricata
|
||||
- minions.{{ grains.id }}
|
||||
@@ -134,8 +132,6 @@ base:
|
||||
- zeek.adv_zeek
|
||||
- bpf.soc_bpf
|
||||
- bpf.adv_bpf
|
||||
- pcap.soc_pcap
|
||||
- pcap.adv_pcap
|
||||
- suricata.soc_suricata
|
||||
- suricata.adv_suricata
|
||||
- minions.{{ grains.id }}
|
||||
@@ -185,8 +181,6 @@ base:
|
||||
- zeek.adv_zeek
|
||||
- bpf.soc_bpf
|
||||
- bpf.adv_bpf
|
||||
- pcap.soc_pcap
|
||||
- pcap.adv_pcap
|
||||
- suricata.soc_suricata
|
||||
- suricata.adv_suricata
|
||||
- minions.{{ grains.id }}
|
||||
@@ -209,8 +203,6 @@ base:
|
||||
- zeek.adv_zeek
|
||||
- bpf.soc_bpf
|
||||
- bpf.adv_bpf
|
||||
- pcap.soc_pcap
|
||||
- pcap.adv_pcap
|
||||
- suricata.soc_suricata
|
||||
- suricata.adv_suricata
|
||||
- strelka.soc_strelka
|
||||
@@ -297,8 +289,6 @@ base:
|
||||
- zeek.adv_zeek
|
||||
- bpf.soc_bpf
|
||||
- bpf.adv_bpf
|
||||
- pcap.soc_pcap
|
||||
- pcap.adv_pcap
|
||||
- suricata.soc_suricata
|
||||
- suricata.adv_suricata
|
||||
- strelka.soc_strelka
|
||||
|
||||
@@ -1,24 +1,14 @@
|
||||
from os import path
|
||||
import subprocess
|
||||
|
||||
def check():
|
||||
|
||||
osfam = __grains__['os_family']
|
||||
retval = 'False'
|
||||
|
||||
if osfam == 'Debian':
|
||||
if path.exists('/var/run/reboot-required'):
|
||||
retval = 'True'
|
||||
cmd = 'needs-restarting -r > /dev/null 2>&1'
|
||||
|
||||
elif osfam == 'RedHat':
|
||||
cmd = 'needs-restarting -r > /dev/null 2>&1'
|
||||
|
||||
try:
|
||||
needs_restarting = subprocess.check_call(cmd, shell=True)
|
||||
except subprocess.CalledProcessError:
|
||||
retval = 'True'
|
||||
|
||||
else:
|
||||
retval = 'Unsupported OS: %s' % os
|
||||
try:
|
||||
needs_restarting = subprocess.check_call(cmd, shell=True)
|
||||
except subprocess.CalledProcessError:
|
||||
retval = 'True'
|
||||
|
||||
return retval
|
||||
|
||||
@@ -38,7 +38,6 @@
|
||||
] %}
|
||||
|
||||
{% set sensor_states = [
|
||||
'pcap',
|
||||
'suricata',
|
||||
'healthcheck',
|
||||
'tcpreplay',
|
||||
|
||||
@@ -1,10 +1,10 @@
|
||||
backup:
|
||||
locations:
|
||||
description: List of locations to back up to the destination.
|
||||
helpLink: backup.html
|
||||
helpLink: backup
|
||||
global: True
|
||||
destination:
|
||||
description: Directory to store the configuration backups in.
|
||||
helpLink: backup.html
|
||||
helpLink: backup
|
||||
global: True
|
||||
|
||||
@@ -1,21 +1,15 @@
|
||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
{% set PCAP_BPF_STATUS = 0 %}
|
||||
{% set STENO_BPF_COMPILED = "" %}
|
||||
|
||||
{% if GLOBALS.pcap_engine == "TRANSITION" %}
|
||||
{% set PCAPBPF = ["ip and host 255.255.255.1 and port 1"] %}
|
||||
{% else %}
|
||||
{% import_yaml 'bpf/defaults.yaml' as BPFDEFAULTS %}
|
||||
{% set BPFMERGED = salt['pillar.get']('bpf', BPFDEFAULTS.bpf, merge=True) %}
|
||||
{% import 'bpf/macros.jinja' as MACROS %}
|
||||
{{ MACROS.remove_comments(BPFMERGED, 'pcap') }}
|
||||
{% set PCAPBPF = BPFMERGED.pcap %}
|
||||
{% endif %}
|
||||
|
||||
{% if PCAPBPF %}
|
||||
{% set PCAP_BPF_CALC = salt['cmd.script']('salt://common/tools/sbin/so-bpf-compile', GLOBALS.sensor.interface + ' ' + PCAPBPF|join(" "),cwd='/root') %}
|
||||
{% if PCAP_BPF_CALC['retcode'] == 0 %}
|
||||
{% set PCAP_BPF_STATUS = 1 %}
|
||||
{% set STENO_BPF_COMPILED = ",\\\"--filter=" + PCAP_BPF_CALC['stdout'] + "\\\"" %}
|
||||
{% endif %}
|
||||
{% endif %}
|
||||
|
||||
@@ -3,14 +3,14 @@ bpf:
|
||||
description: List of BPF filters to apply to the PCAP engine.
|
||||
multiline: True
|
||||
forcedType: "[]string"
|
||||
helpLink: bpf.html
|
||||
helpLink: bpf
|
||||
suricata:
|
||||
description: List of BPF filters to apply to Suricata. This will apply to alerts and, if enabled, to metadata and PCAP logs generated by Suricata.
|
||||
multiline: True
|
||||
forcedType: "[]string"
|
||||
helpLink: bpf.html
|
||||
helpLink: bpf
|
||||
zeek:
|
||||
description: List of BPF filters to apply to Zeek.
|
||||
multiline: True
|
||||
forcedType: "[]string"
|
||||
helpLink: bpf.html
|
||||
helpLink: bpf
|
||||
|
||||
@@ -3,8 +3,6 @@
|
||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||
# Elastic License 2.0.
|
||||
|
||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
|
||||
include:
|
||||
- docker
|
||||
|
||||
@@ -18,9 +16,3 @@ trusttheca:
|
||||
- show_changes: False
|
||||
- makedirs: True
|
||||
|
||||
{% if GLOBALS.os_family == 'Debian' %}
|
||||
symlinkca:
|
||||
file.symlink:
|
||||
- target: /etc/pki/tls/certs/intca.crt
|
||||
- name: /etc/ssl/certs/intca.crt
|
||||
{% endif %}
|
||||
|
||||
@@ -1,12 +0,0 @@
|
||||
{
|
||||
"registry-mirrors": [
|
||||
"https://:5000"
|
||||
],
|
||||
"bip": "172.17.0.1/24",
|
||||
"default-address-pools": [
|
||||
{
|
||||
"base": "172.17.0.0/24",
|
||||
"size": 24
|
||||
}
|
||||
]
|
||||
}
|
||||
@@ -20,11 +20,6 @@ kernel.printk:
|
||||
sysctl.present:
|
||||
- value: "3 4 1 3"
|
||||
|
||||
# Remove variables.txt from /tmp - This is temp
|
||||
rmvariablesfile:
|
||||
file.absent:
|
||||
- name: /tmp/variables.txt
|
||||
|
||||
# Add socore Group
|
||||
socoregroup:
|
||||
group.present:
|
||||
@@ -149,28 +144,6 @@ common_sbin_jinja:
|
||||
- so-import-pcap
|
||||
{% endif %}
|
||||
|
||||
{% if GLOBALS.role == 'so-heavynode' %}
|
||||
remove_so-pcap-import_heavynode:
|
||||
file.absent:
|
||||
- name: /usr/sbin/so-pcap-import
|
||||
|
||||
remove_so-import-pcap_heavynode:
|
||||
file.absent:
|
||||
- name: /usr/sbin/so-import-pcap
|
||||
{% endif %}
|
||||
|
||||
{% if not GLOBALS.is_manager%}
|
||||
# prior to 2.4.50 these scripts were in common/tools/sbin on the manager because of soup and distributed to non managers
|
||||
# these two states remove the scripts from non manager nodes
|
||||
remove_soup:
|
||||
file.absent:
|
||||
- name: /usr/sbin/soup
|
||||
|
||||
remove_so-firewall:
|
||||
file.absent:
|
||||
- name: /usr/sbin/so-firewall
|
||||
{% endif %}
|
||||
|
||||
so-status_script:
|
||||
file.managed:
|
||||
- name: /usr/sbin/so-status
|
||||
|
||||
@@ -1,52 +1,5 @@
|
||||
# we cannot import GLOBALS from vars/globals.map.jinja in this state since it is called in setup.virt.init
|
||||
# since it is early in setup of a new VM, the pillars imported in GLOBALS are not yet defined
|
||||
{% if grains.os_family == 'Debian' %}
|
||||
commonpkgs:
|
||||
pkg.installed:
|
||||
- skip_suggestions: True
|
||||
- pkgs:
|
||||
- apache2-utils
|
||||
- wget
|
||||
- ntpdate
|
||||
- jq
|
||||
- curl
|
||||
- ca-certificates
|
||||
- software-properties-common
|
||||
- apt-transport-https
|
||||
- openssl
|
||||
- netcat-openbsd
|
||||
- sqlite3
|
||||
- libssl-dev
|
||||
- procps
|
||||
- python3-dateutil
|
||||
- python3-docker
|
||||
- python3-packaging
|
||||
- python3-lxml
|
||||
- git
|
||||
- rsync
|
||||
- vim
|
||||
- tar
|
||||
- unzip
|
||||
- bc
|
||||
{% if grains.oscodename != 'focal' %}
|
||||
- python3-rich
|
||||
{% endif %}
|
||||
|
||||
{% if grains.oscodename == 'focal' %}
|
||||
# since Ubuntu requires and internet connection we can use pip to install modules
|
||||
python3-pip:
|
||||
pkg.installed
|
||||
|
||||
python-rich:
|
||||
pip.installed:
|
||||
- name: rich
|
||||
- target: /usr/local/lib/python3.8/dist-packages/
|
||||
- require:
|
||||
- pkg: python3-pip
|
||||
{% endif %}
|
||||
{% endif %}
|
||||
|
||||
{% if grains.os_family == 'RedHat' %}
|
||||
|
||||
remove_mariadb:
|
||||
pkg.removed:
|
||||
@@ -84,5 +37,3 @@ commonpkgs:
|
||||
- unzip
|
||||
- wget
|
||||
- yum-utils
|
||||
|
||||
{% endif %}
|
||||
|
||||
@@ -3,8 +3,6 @@
|
||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||
# Elastic License 2.0.
|
||||
|
||||
{% if '2.4' in salt['cp.get_file_str']('/etc/soversion') %}
|
||||
|
||||
{% import_yaml '/opt/so/saltstack/local/pillar/global/soc_global.sls' as SOC_GLOBAL %}
|
||||
{% if SOC_GLOBAL.global.airgap %}
|
||||
{% set UPDATE_DIR='/tmp/soagupdate/SecurityOnion' %}
|
||||
@@ -13,14 +11,6 @@
|
||||
{% endif %}
|
||||
{% set SOVERSION = salt['file.read']('/etc/soversion').strip() %}
|
||||
|
||||
remove_common_soup:
|
||||
file.absent:
|
||||
- name: /opt/so/saltstack/default/salt/common/tools/sbin/soup
|
||||
|
||||
remove_common_so-firewall:
|
||||
file.absent:
|
||||
- name: /opt/so/saltstack/default/salt/common/tools/sbin/so-firewall
|
||||
|
||||
# This section is used to put the scripts in place in the Salt file system
|
||||
# in case a state run tries to overwrite what we do in the next section.
|
||||
copy_so-common_common_tools_sbin:
|
||||
@@ -120,23 +110,3 @@ copy_bootstrap-salt_sbin:
|
||||
- source: {{UPDATE_DIR}}/salt/salt/scripts/bootstrap-salt.sh
|
||||
- force: True
|
||||
- preserve: True
|
||||
|
||||
{# this is added in 2.4.120 to remove salt repo files pointing to saltproject.io to accomodate the move to broadcom and new bootstrap-salt script #}
|
||||
{% if salt['pkg.version_cmp'](SOVERSION, '2.4.120') == -1 %}
|
||||
{% set saltrepofile = '/etc/yum.repos.d/salt.repo' %}
|
||||
{% if grains.os_family == 'Debian' %}
|
||||
{% set saltrepofile = '/etc/apt/sources.list.d/salt.list' %}
|
||||
{% endif %}
|
||||
remove_saltproject_io_repo_manager:
|
||||
file.absent:
|
||||
- name: {{ saltrepofile }}
|
||||
{% endif %}
|
||||
|
||||
{% else %}
|
||||
fix_23_soup_sbin:
|
||||
cmd.run:
|
||||
- name: curl -s -f -o /usr/sbin/soup https://raw.githubusercontent.com/Security-Onion-Solutions/securityonion/2.3/main/salt/common/tools/sbin/soup
|
||||
fix_23_soup_salt:
|
||||
cmd.run:
|
||||
- name: curl -s -f -o /opt/so/saltstack/defalt/salt/common/tools/sbin/soup https://raw.githubusercontent.com/Security-Onion-Solutions/securityonion/2.3/main/salt/common/tools/sbin/soup
|
||||
{% endif %}
|
||||
|
||||
@@ -16,7 +16,7 @@
|
||||
|
||||
if [ "$#" -lt 2 ]; then
|
||||
cat 1>&2 <<EOF
|
||||
$0 compiles a BPF expression to be passed to stenotype to apply a socket filter.
|
||||
$0 compiles a BPF expression to be passed to PCAP to apply a socket filter.
|
||||
Its first argument is the interface (link type is required) and all other arguments
|
||||
are passed to TCPDump.
|
||||
|
||||
|
||||
@@ -333,8 +333,8 @@ get_elastic_agent_vars() {
|
||||
|
||||
if [ -f "$defaultsfile" ]; then
|
||||
ELASTIC_AGENT_TARBALL_VERSION=$(egrep " +version: " $defaultsfile | awk -F: '{print $2}' | tr -d '[:space:]')
|
||||
ELASTIC_AGENT_URL="https://repo.securityonion.net/file/so-repo/prod/2.4/elasticagent/elastic-agent_SO-$ELASTIC_AGENT_TARBALL_VERSION.tar.gz"
|
||||
ELASTIC_AGENT_MD5_URL="https://repo.securityonion.net/file/so-repo/prod/2.4/elasticagent/elastic-agent_SO-$ELASTIC_AGENT_TARBALL_VERSION.md5"
|
||||
ELASTIC_AGENT_URL="https://repo.securityonion.net/file/so-repo/prod/3/elasticagent/elastic-agent_SO-$ELASTIC_AGENT_TARBALL_VERSION.tar.gz"
|
||||
ELASTIC_AGENT_MD5_URL="https://repo.securityonion.net/file/so-repo/prod/3/elasticagent/elastic-agent_SO-$ELASTIC_AGENT_TARBALL_VERSION.md5"
|
||||
ELASTIC_AGENT_FILE="/nsm/elastic-fleet/artifacts/elastic-agent_SO-$ELASTIC_AGENT_TARBALL_VERSION.tar.gz"
|
||||
ELASTIC_AGENT_MD5="/nsm/elastic-fleet/artifacts/elastic-agent_SO-$ELASTIC_AGENT_TARBALL_VERSION.md5"
|
||||
ELASTIC_AGENT_EXPANSION_DIR=/nsm/elastic-fleet/artifacts/beats/elastic-agent
|
||||
@@ -349,21 +349,16 @@ get_random_value() {
|
||||
}
|
||||
|
||||
gpg_rpm_import() {
|
||||
if [[ $is_oracle ]]; then
|
||||
if [[ "$WHATWOULDYOUSAYYAHDOHERE" == "setup" ]]; then
|
||||
local RPMKEYSLOC="../salt/repo/client/files/$OS/keys"
|
||||
else
|
||||
local RPMKEYSLOC="$UPDATE_DIR/salt/repo/client/files/$OS/keys"
|
||||
fi
|
||||
RPMKEYS=('RPM-GPG-KEY-oracle' 'RPM-GPG-KEY-EPEL-9' 'SALT-PROJECT-GPG-PUBKEY-2023.pub' 'docker.pub' 'securityonion.pub')
|
||||
for RPMKEY in "${RPMKEYS[@]}"; do
|
||||
rpm --import $RPMKEYSLOC/$RPMKEY
|
||||
echo "Imported $RPMKEY"
|
||||
done
|
||||
elif [[ $is_rpm ]]; then
|
||||
echo "Importing the security onion GPG key"
|
||||
rpm --import ../salt/repo/client/files/oracle/keys/securityonion.pub
|
||||
if [[ "$WHATWOULDYOUSAYYAHDOHERE" == "setup" ]]; then
|
||||
local RPMKEYSLOC="../salt/repo/client/files/$OS/keys"
|
||||
else
|
||||
local RPMKEYSLOC="$UPDATE_DIR/salt/repo/client/files/$OS/keys"
|
||||
fi
|
||||
RPMKEYS=('RPM-GPG-KEY-oracle' 'RPM-GPG-KEY-EPEL-9' 'SALT-PROJECT-GPG-PUBKEY-2023.pub' 'docker.pub' 'securityonion.pub')
|
||||
for RPMKEY in "${RPMKEYS[@]}"; do
|
||||
rpm --import $RPMKEYSLOC/$RPMKEY
|
||||
echo "Imported $RPMKEY"
|
||||
done
|
||||
}
|
||||
|
||||
header() {
|
||||
@@ -550,6 +545,22 @@ retry() {
|
||||
return $exitcode
|
||||
}
|
||||
|
||||
rollover_index() {
|
||||
idx=$1
|
||||
exists=$(so-elasticsearch-query $idx -o /dev/null -w "%{http_code}")
|
||||
if [[ $exists -eq 200 ]]; then
|
||||
rollover=$(so-elasticsearch-query $idx/_rollover -o /dev/null -w "%{http_code}" -XPOST)
|
||||
|
||||
if [[ $rollover -eq 200 ]]; then
|
||||
echo "Successfully triggered rollover for $idx..."
|
||||
else
|
||||
echo "Could not trigger rollover for $idx..."
|
||||
fi
|
||||
else
|
||||
echo "Could not find index $idx..."
|
||||
fi
|
||||
}
|
||||
|
||||
run_check_net_err() {
|
||||
local cmd=$1
|
||||
local err_msg=${2:-"Unknown error occured, please check /root/$WHATWOULDYOUSAYYAHDOHERE.log for details."} # Really need to rename that variable
|
||||
@@ -615,69 +626,19 @@ salt_minion_count() {
|
||||
}
|
||||
|
||||
set_os() {
|
||||
if [ -f /etc/redhat-release ]; then
|
||||
if grep -q "Rocky Linux release 9" /etc/redhat-release; then
|
||||
OS=rocky
|
||||
OSVER=9
|
||||
is_rocky=true
|
||||
is_rpm=true
|
||||
elif grep -q "CentOS Stream release 9" /etc/redhat-release; then
|
||||
OS=centos
|
||||
OSVER=9
|
||||
is_centos=true
|
||||
is_rpm=true
|
||||
elif grep -q "AlmaLinux release 9" /etc/redhat-release; then
|
||||
OS=alma
|
||||
OSVER=9
|
||||
is_alma=true
|
||||
is_rpm=true
|
||||
elif grep -q "Red Hat Enterprise Linux release 9" /etc/redhat-release; then
|
||||
if [ -f /etc/oracle-release ]; then
|
||||
OS=oracle
|
||||
OSVER=9
|
||||
is_oracle=true
|
||||
is_rpm=true
|
||||
else
|
||||
OS=rhel
|
||||
OSVER=9
|
||||
is_rhel=true
|
||||
is_rpm=true
|
||||
fi
|
||||
fi
|
||||
cron_service_name="crond"
|
||||
elif [ -f /etc/os-release ]; then
|
||||
if grep -q "UBUNTU_CODENAME=focal" /etc/os-release; then
|
||||
OSVER=focal
|
||||
UBVER=20.04
|
||||
OS=ubuntu
|
||||
is_ubuntu=true
|
||||
is_deb=true
|
||||
elif grep -q "UBUNTU_CODENAME=jammy" /etc/os-release; then
|
||||
OSVER=jammy
|
||||
UBVER=22.04
|
||||
OS=ubuntu
|
||||
is_ubuntu=true
|
||||
is_deb=true
|
||||
elif grep -q "VERSION_CODENAME=bookworm" /etc/os-release; then
|
||||
OSVER=bookworm
|
||||
DEBVER=12
|
||||
is_debian=true
|
||||
OS=debian
|
||||
is_deb=true
|
||||
fi
|
||||
cron_service_name="cron"
|
||||
if [ -f /etc/redhat-release ] && grep -q "Red Hat Enterprise Linux release 9" /etc/redhat-release && [ -f /etc/oracle-release ]; then
|
||||
OS=oracle
|
||||
OSVER=9
|
||||
is_oracle=true
|
||||
is_rpm=true
|
||||
fi
|
||||
cron_service_name="crond"
|
||||
}
|
||||
|
||||
set_minionid() {
|
||||
MINIONID=$(lookup_grain id)
|
||||
}
|
||||
|
||||
set_palette() {
|
||||
if [[ $is_deb ]]; then
|
||||
update-alternatives --set newt-palette /etc/newt/palette.original
|
||||
fi
|
||||
}
|
||||
|
||||
set_version() {
|
||||
CURRENTVERSION=0.0.0
|
||||
|
||||
@@ -32,7 +32,6 @@ container_list() {
|
||||
"so-nginx"
|
||||
"so-pcaptools"
|
||||
"so-soc"
|
||||
"so-steno"
|
||||
"so-suricata"
|
||||
"so-telegraf"
|
||||
"so-zeek"
|
||||
@@ -58,7 +57,6 @@ container_list() {
|
||||
"so-pcaptools"
|
||||
"so-redis"
|
||||
"so-soc"
|
||||
"so-steno"
|
||||
"so-strelka-backend"
|
||||
"so-strelka-manager"
|
||||
"so-suricata"
|
||||
@@ -71,7 +69,6 @@ container_list() {
|
||||
"so-logstash"
|
||||
"so-nginx"
|
||||
"so-redis"
|
||||
"so-steno"
|
||||
"so-suricata"
|
||||
"so-soc"
|
||||
"so-telegraf"
|
||||
|
||||
@@ -131,6 +131,7 @@ if [[ $EXCLUDE_STARTUP_ERRORS == 'Y' ]]; then
|
||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|not configured for GeoIP" # SO does not bundle the maxminddb with Zeek
|
||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|HTTP 404: Not Found" # Salt loops until Kratos returns 200, during startup Kratos may not be ready
|
||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|Cancelling deferred write event maybeFenceReplicas because the event queue is now closed" # Kafka controller log during shutdown/restart
|
||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|Redis may have been restarted" # Redis likely restarted by salt
|
||||
fi
|
||||
|
||||
if [[ $EXCLUDE_FALSE_POSITIVE_ERRORS == 'Y' ]]; then
|
||||
@@ -179,7 +180,6 @@ if [[ $EXCLUDE_KNOWN_ERRORS == 'Y' ]]; then
|
||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|salt-minion-check" # bug in early 2.4 place Jinja script in non-jinja salt dir causing cron output errors
|
||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|monitoring.metrics" # known issue with elastic agent casting the field incorrectly if an integer value shows up before a float
|
||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|repodownload.conf" # known issue with reposync on pre-2.4.20
|
||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|missing versions record" # stenographer corrupt index
|
||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|soc.field." # known ingest type collisions issue with earlier versions of SO
|
||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|error parsing signature" # Malformed Suricata rule, from upstream provider
|
||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|sticky buffer has no matches" # Non-critical Suricata error
|
||||
|
||||
@@ -55,19 +55,22 @@ if [ $SKIP -ne 1 ]; then
|
||||
fi
|
||||
|
||||
delete_pcap() {
|
||||
PCAP_DATA="/nsm/pcap/"
|
||||
[ -d $PCAP_DATA ] && so-pcap-stop && rm -rf $PCAP_DATA/* && so-pcap-start
|
||||
PCAP_DATA="/nsm/suripcap/"
|
||||
[ -d $PCAP_DATA ] && rm -rf $PCAP_DATA/*
|
||||
}
|
||||
delete_suricata() {
|
||||
SURI_LOG="/nsm/suricata/"
|
||||
[ -d $SURI_LOG ] && so-suricata-stop && rm -rf $SURI_LOG/* && so-suricata-start
|
||||
[ -d $SURI_LOG ] && rm -rf $SURI_LOG/*
|
||||
}
|
||||
delete_zeek() {
|
||||
ZEEK_LOG="/nsm/zeek/logs/"
|
||||
[ -d $ZEEK_LOG ] && so-zeek-stop && rm -rf $ZEEK_LOG/* && so-zeek-start
|
||||
}
|
||||
|
||||
so-suricata-stop
|
||||
delete_pcap
|
||||
delete_suricata
|
||||
delete_zeek
|
||||
so-suricata-start
|
||||
|
||||
|
||||
|
||||
@@ -23,7 +23,6 @@ if [ $# -ge 1 ]; then
|
||||
fi
|
||||
|
||||
case $1 in
|
||||
"steno") docker stop so-steno && docker rm so-steno && salt-call state.apply pcap queue=True;;
|
||||
"elastic-fleet") docker stop so-elastic-fleet && docker rm so-elastic-fleet && salt-call state.apply elasticfleet queue=True;;
|
||||
*) docker stop so-$1 ; docker rm so-$1 ; salt-call state.apply $1 queue=True;;
|
||||
esac
|
||||
|
||||
@@ -72,7 +72,7 @@ clean() {
|
||||
done
|
||||
fi
|
||||
|
||||
## Clean up extracted pcaps from Steno
|
||||
## Clean up extracted pcaps
|
||||
PCAPS='/nsm/pcapout'
|
||||
OLDEST_PCAP=$(find $PCAPS -type f -printf '%T+ %p\n' | sort -n | head -n 1)
|
||||
if [ -z "$OLDEST_PCAP" -o "$OLDEST_PCAP" == ".." -o "$OLDEST_PCAP" == "." ]; then
|
||||
|
||||
@@ -23,7 +23,6 @@ if [ $# -ge 1 ]; then
|
||||
|
||||
case $1 in
|
||||
"all") salt-call state.highstate queue=True;;
|
||||
"steno") if docker ps | grep -q so-$1; then printf "\n$1 is already running!\n\n"; else docker rm so-$1 >/dev/null 2>&1 ; salt-call state.apply pcap queue=True; fi ;;
|
||||
"elastic-fleet") if docker ps | grep -q so-$1; then printf "\n$1 is already running!\n\n"; else docker rm so-$1 >/dev/null 2>&1 ; salt-call state.apply elasticfleet queue=True; fi ;;
|
||||
*) if docker ps | grep -E -q '^so-$1$'; then printf "\n$1 is already running\n\n"; else docker rm so-$1 >/dev/null 2>&1 ; salt-call state.apply $1 queue=True; fi ;;
|
||||
esac
|
||||
|
||||
@@ -1,34 +0,0 @@
|
||||
# Copyright Security Onion Solutions LLC and/or licensed to Security Onion Solutions LLC under one
|
||||
# or more contributor license agreements. Licensed under the Elastic License 2.0 as shown at
|
||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||
# Elastic License 2.0.
|
||||
|
||||
so-curator:
|
||||
docker_container.absent:
|
||||
- force: True
|
||||
|
||||
so-curator_so-status.disabled:
|
||||
file.line:
|
||||
- name: /opt/so/conf/so-status/so-status.conf
|
||||
- match: ^so-curator$
|
||||
- mode: delete
|
||||
|
||||
so-curator-cluster-close:
|
||||
cron.absent:
|
||||
- identifier: so-curator-cluster-close
|
||||
|
||||
so-curator-cluster-delete:
|
||||
cron.absent:
|
||||
- identifier: so-curator-cluster-delete
|
||||
|
||||
delete_curator_configuration:
|
||||
file.absent:
|
||||
- name: /opt/so/conf/curator
|
||||
- recurse: True
|
||||
|
||||
{% set files = salt.file.find(path='/usr/sbin', name='so-curator*') %}
|
||||
{% if files|length > 0 %}
|
||||
delete_curator_scripts:
|
||||
file.absent:
|
||||
- names: {{files|yaml}}
|
||||
{% endif %}
|
||||
@@ -1,6 +1,10 @@
|
||||
docker:
|
||||
range: '172.17.1.0/24'
|
||||
gateway: '172.17.1.1'
|
||||
ulimits:
|
||||
- name: nofile
|
||||
soft: 1048576
|
||||
hard: 1048576
|
||||
containers:
|
||||
'so-dockerregistry':
|
||||
final_octet: 20
|
||||
@@ -9,6 +13,7 @@ docker:
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
ulimits: []
|
||||
'so-elastic-fleet':
|
||||
final_octet: 21
|
||||
port_bindings:
|
||||
@@ -16,6 +21,7 @@ docker:
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
ulimits: []
|
||||
'so-elasticsearch':
|
||||
final_octet: 22
|
||||
port_bindings:
|
||||
@@ -24,6 +30,16 @@ docker:
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
ulimits:
|
||||
- name: memlock
|
||||
soft: -1
|
||||
hard: -1
|
||||
- name: nofile
|
||||
soft: 65536
|
||||
hard: 65536
|
||||
- name: nproc
|
||||
soft: 4096
|
||||
hard: 4096
|
||||
'so-influxdb':
|
||||
final_octet: 26
|
||||
port_bindings:
|
||||
@@ -31,6 +47,7 @@ docker:
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
ulimits: []
|
||||
'so-kibana':
|
||||
final_octet: 27
|
||||
port_bindings:
|
||||
@@ -38,6 +55,7 @@ docker:
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
ulimits: []
|
||||
'so-kratos':
|
||||
final_octet: 28
|
||||
port_bindings:
|
||||
@@ -46,6 +64,7 @@ docker:
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
ulimits: []
|
||||
'so-hydra':
|
||||
final_octet: 30
|
||||
port_bindings:
|
||||
@@ -54,6 +73,7 @@ docker:
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
ulimits: []
|
||||
'so-logstash':
|
||||
final_octet: 29
|
||||
port_bindings:
|
||||
@@ -70,6 +90,7 @@ docker:
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
ulimits: []
|
||||
'so-nginx':
|
||||
final_octet: 31
|
||||
port_bindings:
|
||||
@@ -81,6 +102,7 @@ docker:
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
ulimits: []
|
||||
'so-nginx-fleet-node':
|
||||
final_octet: 31
|
||||
port_bindings:
|
||||
@@ -88,6 +110,7 @@ docker:
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
ulimits: []
|
||||
'so-redis':
|
||||
final_octet: 33
|
||||
port_bindings:
|
||||
@@ -96,11 +119,13 @@ docker:
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
ulimits: []
|
||||
'so-sensoroni':
|
||||
final_octet: 99
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
ulimits: []
|
||||
'so-soc':
|
||||
final_octet: 34
|
||||
port_bindings:
|
||||
@@ -108,16 +133,19 @@ docker:
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
ulimits: []
|
||||
'so-strelka-backend':
|
||||
final_octet: 36
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
ulimits: []
|
||||
'so-strelka-filestream':
|
||||
final_octet: 37
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
ulimits: []
|
||||
'so-strelka-frontend':
|
||||
final_octet: 38
|
||||
port_bindings:
|
||||
@@ -125,11 +153,13 @@ docker:
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
ulimits: []
|
||||
'so-strelka-manager':
|
||||
final_octet: 39
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
ulimits: []
|
||||
'so-strelka-gatekeeper':
|
||||
final_octet: 40
|
||||
port_bindings:
|
||||
@@ -137,6 +167,7 @@ docker:
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
ulimits: []
|
||||
'so-strelka-coordinator':
|
||||
final_octet: 41
|
||||
port_bindings:
|
||||
@@ -144,11 +175,13 @@ docker:
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
ulimits: []
|
||||
'so-elastalert':
|
||||
final_octet: 42
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
ulimits: []
|
||||
'so-elastic-fleet-package-registry':
|
||||
final_octet: 44
|
||||
port_bindings:
|
||||
@@ -156,11 +189,13 @@ docker:
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
ulimits: []
|
||||
'so-idh':
|
||||
final_octet: 45
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
ulimits: []
|
||||
'so-elastic-agent':
|
||||
final_octet: 46
|
||||
port_bindings:
|
||||
@@ -169,28 +204,28 @@ docker:
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
ulimits: []
|
||||
'so-telegraf':
|
||||
final_octet: 99
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
'so-steno':
|
||||
final_octet: 99
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
ulimits: []
|
||||
'so-suricata':
|
||||
final_octet: 99
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
ulimits:
|
||||
- memlock=524288000
|
||||
ulimits: []
|
||||
'so-zeek':
|
||||
final_octet: 99
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
ulimits:
|
||||
- name: core
|
||||
soft: 0
|
||||
hard: 0
|
||||
'so-kafka':
|
||||
final_octet: 88
|
||||
port_bindings:
|
||||
@@ -201,3 +236,4 @@ docker:
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
ulimits: []
|
||||
|
||||
@@ -1,8 +1,8 @@
|
||||
{% import_yaml 'docker/defaults.yaml' as DOCKERDEFAULTS %}
|
||||
{% set DOCKER = salt['pillar.get']('docker', DOCKERDEFAULTS.docker, merge=True) %}
|
||||
{% set RANGESPLIT = DOCKER.range.split('.') %}
|
||||
{% set DOCKERMERGED = salt['pillar.get']('docker', DOCKERDEFAULTS.docker, merge=True) %}
|
||||
{% set RANGESPLIT = DOCKERMERGED.range.split('.') %}
|
||||
{% set FIRSTTHREE = RANGESPLIT[0] ~ '.' ~ RANGESPLIT[1] ~ '.' ~ RANGESPLIT[2] ~ '.' %}
|
||||
|
||||
{% for container, vals in DOCKER.containers.items() %}
|
||||
{% do DOCKER.containers[container].update({'ip': FIRSTTHREE ~ DOCKER.containers[container].final_octet}) %}
|
||||
{% for container, vals in DOCKERMERGED.containers.items() %}
|
||||
{% do DOCKERMERGED.containers[container].update({'ip': FIRSTTHREE ~ DOCKERMERGED.containers[container].final_octet}) %}
|
||||
{% endfor %}
|
||||
|
||||
24
salt/docker/files/daemon.json.jinja
Normal file
24
salt/docker/files/daemon.json.jinja
Normal file
@@ -0,0 +1,24 @@
|
||||
{% from 'docker/docker.map.jinja' import DOCKERMERGED -%}
|
||||
{
|
||||
"registry-mirrors": [
|
||||
"https://:5000"
|
||||
],
|
||||
"bip": "172.17.0.1/24",
|
||||
"default-address-pools": [
|
||||
{
|
||||
"base": "172.17.0.0/24",
|
||||
"size": 24
|
||||
}
|
||||
]
|
||||
{%- if DOCKERMERGED.ulimits %},
|
||||
"default-ulimits": {
|
||||
{%- for ULIMIT in DOCKERMERGED.ulimits %}
|
||||
"{{ ULIMIT.name }}": {
|
||||
"Name": "{{ ULIMIT.name }}",
|
||||
"Soft": {{ ULIMIT.soft }},
|
||||
"Hard": {{ ULIMIT.hard }}
|
||||
}{{ "," if not loop.last else "" }}
|
||||
{%- endfor %}
|
||||
}
|
||||
{%- endif %}
|
||||
}
|
||||
@@ -3,7 +3,7 @@
|
||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||
# Elastic License 2.0.
|
||||
|
||||
{% from 'docker/docker.map.jinja' import DOCKER %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKERMERGED %}
|
||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
|
||||
# docker service requires the ca.crt
|
||||
@@ -15,39 +15,6 @@ dockergroup:
|
||||
- name: docker
|
||||
- gid: 920
|
||||
|
||||
{% if GLOBALS.os_family == 'Debian' %}
|
||||
{% if grains.oscodename == 'bookworm' %}
|
||||
dockerheldpackages:
|
||||
pkg.installed:
|
||||
- pkgs:
|
||||
- containerd.io: 2.2.1-1~debian.12~bookworm
|
||||
- docker-ce: 5:29.2.1-1~debian.12~bookworm
|
||||
- docker-ce-cli: 5:29.2.1-1~debian.12~bookworm
|
||||
- docker-ce-rootless-extras: 5:29.2.1-1~debian.12~bookworm
|
||||
- hold: True
|
||||
- update_holds: True
|
||||
{% elif grains.oscodename == 'jammy' %}
|
||||
dockerheldpackages:
|
||||
pkg.installed:
|
||||
- pkgs:
|
||||
- containerd.io: 2.2.1-1~ubuntu.22.04~jammy
|
||||
- docker-ce: 5:29.2.1-1~ubuntu.22.04~jammy
|
||||
- docker-ce-cli: 5:29.2.1-1~ubuntu.22.04~jammy
|
||||
- docker-ce-rootless-extras: 5:29.2.1-1~ubuntu.22.04~jammy
|
||||
- hold: True
|
||||
- update_holds: True
|
||||
{% else %}
|
||||
dockerheldpackages:
|
||||
pkg.installed:
|
||||
- pkgs:
|
||||
- containerd.io: 1.7.21-1
|
||||
- docker-ce: 5:27.2.0-1~ubuntu.20.04~focal
|
||||
- docker-ce-cli: 5:27.2.0-1~ubuntu.20.04~focal
|
||||
- docker-ce-rootless-extras: 5:27.2.0-1~ubuntu.20.04~focal
|
||||
- hold: True
|
||||
- update_holds: True
|
||||
{% endif %}
|
||||
{% else %}
|
||||
dockerheldpackages:
|
||||
pkg.installed:
|
||||
- pkgs:
|
||||
@@ -57,7 +24,6 @@ dockerheldpackages:
|
||||
- docker-ce-rootless-extras: 29.2.1-1.el9
|
||||
- hold: True
|
||||
- update_holds: True
|
||||
{% endif %}
|
||||
|
||||
#disable docker from managing iptables
|
||||
iptables_disabled:
|
||||
@@ -75,10 +41,9 @@ dockeretc:
|
||||
file.directory:
|
||||
- name: /etc/docker
|
||||
|
||||
# Manager daemon.json
|
||||
docker_daemon:
|
||||
file.managed:
|
||||
- source: salt://common/files/daemon.json
|
||||
- source: salt://docker/files/daemon.json.jinja
|
||||
- name: /etc/docker/daemon.json
|
||||
- template: jinja
|
||||
|
||||
@@ -109,8 +74,8 @@ dockerreserveports:
|
||||
sos_docker_net:
|
||||
docker_network.present:
|
||||
- name: sobridge
|
||||
- subnet: {{ DOCKER.range }}
|
||||
- gateway: {{ DOCKER.gateway }}
|
||||
- subnet: {{ DOCKERMERGED.range }}
|
||||
- gateway: {{ DOCKERMERGED.gateway }}
|
||||
- options:
|
||||
com.docker.network.bridge.name: 'sobridge'
|
||||
com.docker.network.driver.mtu: '1500'
|
||||
|
||||
@@ -1,44 +1,82 @@
|
||||
docker:
|
||||
gateway:
|
||||
description: Gateway for the default docker interface.
|
||||
helpLink: docker.html
|
||||
helpLink: docker
|
||||
advanced: True
|
||||
range:
|
||||
description: Default docker IP range for containers.
|
||||
helpLink: docker.html
|
||||
helpLink: docker
|
||||
advanced: True
|
||||
ulimits:
|
||||
description: |
|
||||
Default ulimit settings applied to all containers via the Docker daemon. Each entry specifies a resource name (e.g. nofile, memlock, core, nproc) with soft and hard limits. Individual container ulimits override these defaults. Valid resource names include: cpu, fsize, data, stack, core, rss, nproc, nofile, memlock, as, locks, sigpending, msgqueue, nice, rtprio, rttime.
|
||||
forcedType: "[]{}"
|
||||
syntax: json
|
||||
advanced: True
|
||||
helpLink: docker.html
|
||||
uiElements:
|
||||
- field: name
|
||||
label: Resource Name
|
||||
required: True
|
||||
regex: ^(cpu|fsize|data|stack|core|rss|nproc|nofile|memlock|as|locks|sigpending|msgqueue|nice|rtprio|rttime)$
|
||||
regexFailureMessage: You must enter a valid ulimit name (cpu, fsize, data, stack, core, rss, nproc, nofile, memlock, as, locks, sigpending, msgqueue, nice, rtprio, rttime).
|
||||
- field: soft
|
||||
label: Soft Limit
|
||||
forcedType: int
|
||||
- field: hard
|
||||
label: Hard Limit
|
||||
forcedType: int
|
||||
containers:
|
||||
so-dockerregistry: &dockerOptions
|
||||
final_octet:
|
||||
description: Last octet of the container IP address.
|
||||
helpLink: docker.html
|
||||
helpLink: docker
|
||||
readonly: True
|
||||
advanced: True
|
||||
global: True
|
||||
port_bindings:
|
||||
description: List of port bindings for the container.
|
||||
helpLink: docker.html
|
||||
helpLink: docker
|
||||
advanced: True
|
||||
multiline: True
|
||||
forcedType: "[]string"
|
||||
custom_bind_mounts:
|
||||
description: List of custom local volume bindings.
|
||||
advanced: True
|
||||
helpLink: docker.html
|
||||
helpLink: docker
|
||||
multiline: True
|
||||
forcedType: "[]string"
|
||||
extra_hosts:
|
||||
description: List of additional host entries for the container.
|
||||
advanced: True
|
||||
helpLink: docker.html
|
||||
helpLink: docker
|
||||
multiline: True
|
||||
forcedType: "[]string"
|
||||
extra_env:
|
||||
description: List of additional ENV entries for the container.
|
||||
advanced: True
|
||||
helpLink: docker.html
|
||||
helpLink: docker
|
||||
multiline: True
|
||||
forcedType: "[]string"
|
||||
ulimits:
|
||||
description: |
|
||||
Ulimit settings for the container. Each entry specifies a resource name (e.g. nofile, memlock, core, nproc) with optional soft and hard limits. Valid resource names include: cpu, fsize, data, stack, core, rss, nproc, nofile, memlock, as, locks, sigpending, msgqueue, nice, rtprio, rttime.
|
||||
advanced: True
|
||||
helpLink: docker.html
|
||||
forcedType: "[]{}"
|
||||
syntax: json
|
||||
uiElements:
|
||||
- field: name
|
||||
label: Resource Name
|
||||
required: True
|
||||
regex: ^(cpu|fsize|data|stack|core|rss|nproc|nofile|memlock|as|locks|sigpending|msgqueue|nice|rtprio|rttime)$
|
||||
regexFailureMessage: You must enter a valid ulimit name (cpu, fsize, data, stack, core, rss, nproc, nofile, memlock, as, locks, sigpending, msgqueue, nice, rtprio, rttime).
|
||||
- field: soft
|
||||
label: Soft Limit
|
||||
forcedType: int
|
||||
- field: hard
|
||||
label: Hard Limit
|
||||
forcedType: int
|
||||
so-elastic-fleet: *dockerOptions
|
||||
so-elasticsearch: *dockerOptions
|
||||
so-influxdb: *dockerOptions
|
||||
@@ -62,43 +100,6 @@ docker:
|
||||
so-idh: *dockerOptions
|
||||
so-elastic-agent: *dockerOptions
|
||||
so-telegraf: *dockerOptions
|
||||
so-steno: *dockerOptions
|
||||
so-suricata:
|
||||
final_octet:
|
||||
description: Last octet of the container IP address.
|
||||
helpLink: docker.html
|
||||
readonly: True
|
||||
advanced: True
|
||||
global: True
|
||||
port_bindings:
|
||||
description: List of port bindings for the container.
|
||||
helpLink: docker.html
|
||||
advanced: True
|
||||
multiline: True
|
||||
forcedType: "[]string"
|
||||
custom_bind_mounts:
|
||||
description: List of custom local volume bindings.
|
||||
advanced: True
|
||||
helpLink: docker.html
|
||||
multiline: True
|
||||
forcedType: "[]string"
|
||||
extra_hosts:
|
||||
description: List of additional host entries for the container.
|
||||
advanced: True
|
||||
helpLink: docker.html
|
||||
multiline: True
|
||||
forcedType: "[]string"
|
||||
extra_env:
|
||||
description: List of additional ENV entries for the container.
|
||||
advanced: True
|
||||
helpLink: docker.html
|
||||
multiline: True
|
||||
forcedType: "[]string"
|
||||
ulimits:
|
||||
description: Ulimits for the container, in bytes.
|
||||
advanced: True
|
||||
helpLink: docker.html
|
||||
multiline: True
|
||||
forcedType: "[]string"
|
||||
so-suricata: *dockerOptions
|
||||
so-zeek: *dockerOptions
|
||||
so-kafka: *dockerOptions
|
||||
|
||||
@@ -6,7 +6,7 @@
|
||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
||||
{% if sls.split('.')[0] in allowed_states %}
|
||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKER %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKERMERGED %}
|
||||
|
||||
include:
|
||||
- elastalert.config
|
||||
@@ -24,7 +24,7 @@ so-elastalert:
|
||||
- user: so-elastalert
|
||||
- networks:
|
||||
- sobridge:
|
||||
- ipv4_address: {{ DOCKER.containers['so-elastalert'].ip }}
|
||||
- ipv4_address: {{ DOCKERMERGED.containers['so-elastalert'].ip }}
|
||||
- detach: True
|
||||
- binds:
|
||||
- /opt/so/rules/elastalert:/opt/elastalert/rules/:ro
|
||||
@@ -33,24 +33,30 @@ so-elastalert:
|
||||
- /opt/so/conf/elastalert/predefined/:/opt/elastalert/predefined/:ro
|
||||
- /opt/so/conf/elastalert/custom/:/opt/elastalert/custom/:ro
|
||||
- /opt/so/conf/elastalert/elastalert_config.yaml:/opt/elastalert/config.yaml:ro
|
||||
{% if DOCKER.containers['so-elastalert'].custom_bind_mounts %}
|
||||
{% for BIND in DOCKER.containers['so-elastalert'].custom_bind_mounts %}
|
||||
{% if DOCKERMERGED.containers['so-elastalert'].custom_bind_mounts %}
|
||||
{% for BIND in DOCKERMERGED.containers['so-elastalert'].custom_bind_mounts %}
|
||||
- {{ BIND }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
- extra_hosts:
|
||||
- {{ GLOBALS.manager }}:{{ GLOBALS.manager_ip }}
|
||||
{% if DOCKER.containers['so-elastalert'].extra_hosts %}
|
||||
{% for XTRAHOST in DOCKER.containers['so-elastalert'].extra_hosts %}
|
||||
{% if DOCKERMERGED.containers['so-elastalert'].extra_hosts %}
|
||||
{% for XTRAHOST in DOCKERMERGED.containers['so-elastalert'].extra_hosts %}
|
||||
- {{ XTRAHOST }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
{% if DOCKER.containers['so-elastalert'].extra_env %}
|
||||
{% if DOCKERMERGED.containers['so-elastalert'].extra_env %}
|
||||
- environment:
|
||||
{% for XTRAENV in DOCKER.containers['so-elastalert'].extra_env %}
|
||||
{% for XTRAENV in DOCKERMERGED.containers['so-elastalert'].extra_env %}
|
||||
- {{ XTRAENV }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
{% if DOCKERMERGED.containers['so-elastalert'].ulimits %}
|
||||
- ulimits:
|
||||
{% for ULIMIT in DOCKERMERGED.containers['so-elastalert'].ulimits %}
|
||||
- {{ ULIMIT.name }}={{ ULIMIT.soft }}:{{ ULIMIT.hard }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
- require:
|
||||
- cmd: wait_for_elasticsearch
|
||||
- file: elastarules
|
||||
|
||||
@@ -1 +0,0 @@
|
||||
THIS IS A PLACEHOLDER FILE
|
||||
@@ -1,47 +1,48 @@
|
||||
elastalert:
|
||||
enabled:
|
||||
description: Enables or disables the ElastAlert 2 process. This process is critical for ensuring alerts arrive in SOC, and for outbound notification delivery.
|
||||
helpLink: elastalert.html
|
||||
forcedType: bool
|
||||
helpLink: elastalert
|
||||
alerter_parameters:
|
||||
title: Custom Configuration Parameters
|
||||
description: Optional configuration parameters made available as defaults for all rules and alerters. Use YAML format for these parameters, and reference the ElastAlert 2 documentation, located at https://elastalert2.readthedocs.io, for available configuration parameters. Requires a valid Security Onion license key.
|
||||
global: True
|
||||
multiline: True
|
||||
syntax: yaml
|
||||
helpLink: elastalert.html
|
||||
helpLink: elastalert
|
||||
forcedType: string
|
||||
jira_api_key:
|
||||
title: Jira API Key
|
||||
description: Optional configuration parameter for Jira API Key, used instead of the Jira username and password. Requires a valid Security Onion license key.
|
||||
global: True
|
||||
sensitive: True
|
||||
helpLink: elastalert.html
|
||||
helpLink: elastalert
|
||||
forcedType: string
|
||||
jira_pass:
|
||||
title: Jira Password
|
||||
description: Optional configuration parameter for Jira password. Requires a valid Security Onion license key.
|
||||
global: True
|
||||
sensitive: True
|
||||
helpLink: elastalert.html
|
||||
helpLink: elastalert
|
||||
forcedType: string
|
||||
jira_user:
|
||||
title: Jira Username
|
||||
description: Optional configuration parameter for Jira username. Requires a valid Security Onion license key.
|
||||
global: True
|
||||
helpLink: elastalert.html
|
||||
helpLink: elastalert
|
||||
forcedType: string
|
||||
smtp_pass:
|
||||
title: SMTP Password
|
||||
description: Optional configuration parameter for SMTP password, required for authenticating email servers. Requires a valid Security Onion license key.
|
||||
global: True
|
||||
sensitive: True
|
||||
helpLink: elastalert.html
|
||||
helpLink: elastalert
|
||||
forcedType: string
|
||||
smtp_user:
|
||||
title: SMTP Username
|
||||
description: Optional configuration parameter for SMTP username, required for authenticating email servers. Requires a valid Security Onion license key.
|
||||
global: True
|
||||
helpLink: elastalert.html
|
||||
helpLink: elastalert
|
||||
forcedType: string
|
||||
files:
|
||||
custom:
|
||||
@@ -49,91 +50,131 @@ elastalert:
|
||||
description: Optional custom Certificate Authority for connecting to an AlertManager server. To utilize this custom file, the alertmanager_ca_certs key must be set to /opt/elastalert/custom/alertmanager_ca.crt in the Alerter Parameters setting. Requires a valid Security Onion license key.
|
||||
global: True
|
||||
file: True
|
||||
helpLink: elastalert.html
|
||||
helpLink: elastalert
|
||||
gelf_ca__crt:
|
||||
description: Optional custom Certificate Authority for connecting to a Graylog server. To utilize this custom file, the graylog_ca_certs key must be set to /opt/elastalert/custom/graylog_ca.crt in the Alerter Parameters setting. Requires a valid Security Onion license key.
|
||||
global: True
|
||||
file: True
|
||||
helpLink: elastalert.html
|
||||
helpLink: elastalert
|
||||
http_post_ca__crt:
|
||||
description: Optional custom Certificate Authority for connecting to a generic HTTP server, via the legacy HTTP POST alerter. To utilize this custom file, the http_post_ca_certs key must be set to /opt/elastalert/custom/http_post2_ca.crt in the Alerter Parameters setting. Requires a valid Security Onion license key.
|
||||
global: True
|
||||
file: True
|
||||
helpLink: elastalert.html
|
||||
helpLink: elastalert
|
||||
http_post2_ca__crt:
|
||||
description: Optional custom Certificate Authority for connecting to a generic HTTP server, via the newer HTTP POST 2 alerter. To utilize this custom file, the http_post2_ca_certs key must be set to /opt/elastalert/custom/http_post2_ca.crt in the Alerter Parameters setting. Requires a valid Security Onion license key.
|
||||
global: True
|
||||
file: True
|
||||
helpLink: elastalert.html
|
||||
helpLink: elastalert
|
||||
ms_teams_ca__crt:
|
||||
description: Optional custom Certificate Authority for connecting to Microsoft Teams server. To utilize this custom file, the ms_teams_ca_certs key must be set to /opt/elastalert/custom/ms_teams_ca.crt in the Alerter Parameters setting. Requires a valid Security Onion license key.
|
||||
global: True
|
||||
file: True
|
||||
helpLink: elastalert.html
|
||||
helpLink: elastalert
|
||||
pagerduty_ca__crt:
|
||||
description: Optional custom Certificate Authority for connecting to PagerDuty server. To utilize this custom file, the pagerduty_ca_certs key must be set to /opt/elastalert/custom/pagerduty_ca.crt in the Alerter Parameters setting. Requires a valid Security Onion license key.
|
||||
global: True
|
||||
file: True
|
||||
helpLink: elastalert.html
|
||||
helpLink: elastalert
|
||||
rocket_chat_ca__crt:
|
||||
description: Optional custom Certificate Authority for connecting to PagerDuty server. To utilize this custom file, the rocket_chart_ca_certs key must be set to /opt/elastalert/custom/rocket_chat_ca.crt in the Alerter Parameters setting. Requires a valid Security Onion license key.
|
||||
global: True
|
||||
file: True
|
||||
helpLink: elastalert.html
|
||||
helpLink: elastalert
|
||||
smtp__crt:
|
||||
description: Optional custom certificate for connecting to an SMTP server. To utilize this custom file, the smtp_cert_file key must be set to /opt/elastalert/custom/smtp.crt in the Alerter Parameters setting. Requires a valid Security Onion license key.
|
||||
global: True
|
||||
file: True
|
||||
helpLink: elastalert.html
|
||||
helpLink: elastalert
|
||||
smtp__key:
|
||||
description: Optional custom certificate key for connecting to an SMTP server. To utilize this custom file, the smtp_key_file key must be set to /opt/elastalert/custom/smtp.key in the Alerter Parameters setting. Requires a valid Security Onion license key.
|
||||
global: True
|
||||
file: True
|
||||
helpLink: elastalert.html
|
||||
helpLink: elastalert
|
||||
slack_ca__crt:
|
||||
description: Optional custom Certificate Authority for connecting to Slack. To utilize this custom file, the slack_ca_certs key must be set to /opt/elastalert/custom/slack_ca.crt in the Alerter Parameters setting. Requires a valid Security Onion license key.
|
||||
global: True
|
||||
file: True
|
||||
helpLink: elastalert.html
|
||||
helpLink: elastalert
|
||||
config:
|
||||
scan_subdirectories:
|
||||
description: Recursively scan subdirectories for rules.
|
||||
forcedType: bool
|
||||
advanced: True
|
||||
global: True
|
||||
helpLink: elastalert
|
||||
disable_rules_on_error:
|
||||
description: Disable rules on failure.
|
||||
forcedType: bool
|
||||
global: True
|
||||
helpLink: elastalert.html
|
||||
helpLink: elastalert
|
||||
run_every:
|
||||
minutes:
|
||||
description: Amount of time in minutes between searches.
|
||||
global: True
|
||||
helpLink: elastalert.html
|
||||
helpLink: elastalert
|
||||
buffer_time:
|
||||
minutes:
|
||||
description: Amount of time in minutes to look through.
|
||||
global: True
|
||||
helpLink: elastalert.html
|
||||
helpLink: elastalert
|
||||
old_query_limit:
|
||||
minutes:
|
||||
description: Amount of time in minutes between queries to start at the most recently run query.
|
||||
global: True
|
||||
helpLink: elastalert.html
|
||||
helpLink: elastalert
|
||||
es_conn_timeout:
|
||||
description: Timeout in seconds for connecting to and reading from Elasticsearch.
|
||||
global: True
|
||||
helpLink: elastalert.html
|
||||
helpLink: elastalert
|
||||
max_query_size:
|
||||
description: The maximum number of documents that will be returned from Elasticsearch in a single query.
|
||||
global: True
|
||||
helpLink: elastalert.html
|
||||
helpLink: elastalert
|
||||
use_ssl:
|
||||
description: Use SSL to connect to Elasticsearch.
|
||||
forcedType: bool
|
||||
advanced: True
|
||||
global: True
|
||||
helpLink: elastalert
|
||||
verify_certs:
|
||||
description: Verify TLS certificates when connecting to Elasticsearch.
|
||||
forcedType: bool
|
||||
advanced: True
|
||||
global: True
|
||||
helpLink: elastalert
|
||||
alert_time_limit:
|
||||
days:
|
||||
description: The retry window for failed alerts.
|
||||
global: True
|
||||
helpLink: elastalert.html
|
||||
helpLink: elastalert
|
||||
index_settings:
|
||||
shards:
|
||||
description: The number of shards for elastalert indices.
|
||||
global: True
|
||||
helpLink: elastalert.html
|
||||
helpLink: elastalert
|
||||
replicas:
|
||||
description: The number of replicas for elastalert indices.
|
||||
global: True
|
||||
helpLink: elastalert.html
|
||||
helpLink: elastalert
|
||||
logging:
|
||||
incremental:
|
||||
description: When incremental is false (the default), the logging configuration is applied in full, replacing any existing logging setup. When true, only the level attributes of existing loggers and handlers are updated, leaving the rest of the logging configuration unchanged.
|
||||
forcedType: bool
|
||||
advanced: True
|
||||
global: True
|
||||
helpLink: elastalert
|
||||
disable_existing_loggers:
|
||||
description: Disable existing loggers.
|
||||
forcedType: bool
|
||||
advanced: True
|
||||
global: True
|
||||
helpLink: elastalert
|
||||
loggers:
|
||||
'':
|
||||
propagate:
|
||||
description: Propagate log messages to parent loggers.
|
||||
forcedType: bool
|
||||
advanced: True
|
||||
global: True
|
||||
helpLink: elastalert
|
||||
|
||||
@@ -6,7 +6,7 @@
|
||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
||||
{% if sls.split('.')[0] in allowed_states %}
|
||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKER %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKERMERGED %}
|
||||
|
||||
include:
|
||||
- elastic-fleet-package-registry.config
|
||||
@@ -21,30 +21,36 @@ so-elastic-fleet-package-registry:
|
||||
- user: 948
|
||||
- networks:
|
||||
- sobridge:
|
||||
- ipv4_address: {{ DOCKER.containers['so-elastic-fleet-package-registry'].ip }}
|
||||
- ipv4_address: {{ DOCKERMERGED.containers['so-elastic-fleet-package-registry'].ip }}
|
||||
- extra_hosts:
|
||||
- {{ GLOBALS.hostname }}:{{ GLOBALS.node_ip }}
|
||||
{% if DOCKER.containers['so-elastic-fleet-package-registry'].extra_hosts %}
|
||||
{% for XTRAHOST in DOCKER.containers['so-elastic-fleet-package-registry'].extra_hosts %}
|
||||
{% if DOCKERMERGED.containers['so-elastic-fleet-package-registry'].extra_hosts %}
|
||||
{% for XTRAHOST in DOCKERMERGED.containers['so-elastic-fleet-package-registry'].extra_hosts %}
|
||||
- {{ XTRAHOST }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
- port_bindings:
|
||||
{% for BINDING in DOCKER.containers['so-elastic-fleet-package-registry'].port_bindings %}
|
||||
{% for BINDING in DOCKERMERGED.containers['so-elastic-fleet-package-registry'].port_bindings %}
|
||||
- {{ BINDING }}
|
||||
{% endfor %}
|
||||
{% if DOCKER.containers['so-elastic-fleet-package-registry'].custom_bind_mounts %}
|
||||
{% if DOCKERMERGED.containers['so-elastic-fleet-package-registry'].custom_bind_mounts %}
|
||||
- binds:
|
||||
{% for BIND in DOCKER.containers['so-elastic-fleet-package-registry'].custom_bind_mounts %}
|
||||
{% for BIND in DOCKERMERGED.containers['so-elastic-fleet-package-registry'].custom_bind_mounts %}
|
||||
- {{ BIND }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
{% if DOCKER.containers['so-elastic-fleet-package-registry'].extra_env %}
|
||||
{% if DOCKERMERGED.containers['so-elastic-fleet-package-registry'].extra_env %}
|
||||
- environment:
|
||||
{% for XTRAENV in DOCKER.containers['so-elastic-fleet-package-registry'].extra_env %}
|
||||
{% for XTRAENV in DOCKERMERGED.containers['so-elastic-fleet-package-registry'].extra_env %}
|
||||
- {{ XTRAENV }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
{% if DOCKERMERGED.containers['so-elastic-fleet-package-registry'].ulimits %}
|
||||
- ulimits:
|
||||
{% for ULIMIT in DOCKERMERGED.containers['so-elastic-fleet-package-registry'].ulimits %}
|
||||
- {{ ULIMIT.name }}={{ ULIMIT.soft }}:{{ ULIMIT.hard }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
delete_so-elastic-fleet-package-registry_so-status.disabled:
|
||||
file.uncomment:
|
||||
- name: /opt/so/conf/so-status/so-status.conf
|
||||
|
||||
@@ -1,4 +1,5 @@
|
||||
elastic_fleet_package_registry:
|
||||
enabled:
|
||||
description: Enables or disables the Fleet package registry process. This process must remain enabled to allow Elastic Agent packages to be updated.
|
||||
forcedType: bool
|
||||
advanced: True
|
||||
|
||||
@@ -6,7 +6,7 @@
|
||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
||||
{% if sls.split('.')[0] in allowed_states %}
|
||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKER %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKERMERGED %}
|
||||
|
||||
include:
|
||||
- ca
|
||||
@@ -22,17 +22,17 @@ so-elastic-agent:
|
||||
- user: 949
|
||||
- networks:
|
||||
- sobridge:
|
||||
- ipv4_address: {{ DOCKER.containers['so-elastic-agent'].ip }}
|
||||
- ipv4_address: {{ DOCKERMERGED.containers['so-elastic-agent'].ip }}
|
||||
- extra_hosts:
|
||||
- {{ GLOBALS.manager }}:{{ GLOBALS.manager_ip }}
|
||||
- {{ GLOBALS.hostname }}:{{ GLOBALS.node_ip }}
|
||||
{% if DOCKER.containers['so-elastic-agent'].extra_hosts %}
|
||||
{% for XTRAHOST in DOCKER.containers['so-elastic-agent'].extra_hosts %}
|
||||
{% if DOCKERMERGED.containers['so-elastic-agent'].extra_hosts %}
|
||||
{% for XTRAHOST in DOCKERMERGED.containers['so-elastic-agent'].extra_hosts %}
|
||||
- {{ XTRAHOST }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
- port_bindings:
|
||||
{% for BINDING in DOCKER.containers['so-elastic-agent'].port_bindings %}
|
||||
{% for BINDING in DOCKERMERGED.containers['so-elastic-agent'].port_bindings %}
|
||||
- {{ BINDING }}
|
||||
{% endfor %}
|
||||
- binds:
|
||||
@@ -41,19 +41,25 @@ so-elastic-agent:
|
||||
- /etc/pki/tls/certs/intca.crt:/etc/pki/tls/certs/intca.crt:ro
|
||||
- /nsm:/nsm:ro
|
||||
- /opt/so/log:/opt/so/log:ro
|
||||
{% if DOCKER.containers['so-elastic-agent'].custom_bind_mounts %}
|
||||
{% for BIND in DOCKER.containers['so-elastic-agent'].custom_bind_mounts %}
|
||||
{% if DOCKERMERGED.containers['so-elastic-agent'].custom_bind_mounts %}
|
||||
{% for BIND in DOCKERMERGED.containers['so-elastic-agent'].custom_bind_mounts %}
|
||||
- {{ BIND }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
- environment:
|
||||
- FLEET_CA=/etc/pki/tls/certs/intca.crt
|
||||
- LOGS_PATH=logs
|
||||
{% if DOCKER.containers['so-elastic-agent'].extra_env %}
|
||||
{% for XTRAENV in DOCKER.containers['so-elastic-agent'].extra_env %}
|
||||
{% if DOCKERMERGED.containers['so-elastic-agent'].extra_env %}
|
||||
{% for XTRAENV in DOCKERMERGED.containers['so-elastic-agent'].extra_env %}
|
||||
- {{ XTRAENV }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
{% if DOCKERMERGED.containers['so-elastic-agent'].ulimits %}
|
||||
- ulimits:
|
||||
{% for ULIMIT in DOCKERMERGED.containers['so-elastic-agent'].ulimits %}
|
||||
- {{ ULIMIT.name }}={{ ULIMIT.soft }}:{{ ULIMIT.hard }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
- require:
|
||||
- file: create-elastic-agent-config
|
||||
- file: trusttheca
|
||||
|
||||
@@ -1,4 +1,5 @@
|
||||
elasticagent:
|
||||
enabled:
|
||||
description: Enables or disables the Elastic Agent process. This process must remain enabled to allow collection of node events.
|
||||
forcedType: bool
|
||||
advanced: True
|
||||
|
||||
@@ -6,7 +6,7 @@
|
||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
||||
{% if sls.split('.')[0] in allowed_states %}
|
||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKER %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKERMERGED %}
|
||||
{% from 'elasticfleet/map.jinja' import ELASTICFLEETMERGED %}
|
||||
|
||||
{# This value is generated during node install and stored in minion pillar #}
|
||||
@@ -94,17 +94,17 @@ so-elastic-fleet:
|
||||
- user: 947
|
||||
- networks:
|
||||
- sobridge:
|
||||
- ipv4_address: {{ DOCKER.containers['so-elastic-fleet'].ip }}
|
||||
- ipv4_address: {{ DOCKERMERGED.containers['so-elastic-fleet'].ip }}
|
||||
- extra_hosts:
|
||||
- {{ GLOBALS.manager }}:{{ GLOBALS.manager_ip }}
|
||||
- {{ GLOBALS.hostname }}:{{ GLOBALS.node_ip }}
|
||||
{% if DOCKER.containers['so-elastic-fleet'].extra_hosts %}
|
||||
{% for XTRAHOST in DOCKER.containers['so-elastic-fleet'].extra_hosts %}
|
||||
{% if DOCKERMERGED.containers['so-elastic-fleet'].extra_hosts %}
|
||||
{% for XTRAHOST in DOCKERMERGED.containers['so-elastic-fleet'].extra_hosts %}
|
||||
- {{ XTRAHOST }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
- port_bindings:
|
||||
{% for BINDING in DOCKER.containers['so-elastic-fleet'].port_bindings %}
|
||||
{% for BINDING in DOCKERMERGED.containers['so-elastic-fleet'].port_bindings %}
|
||||
- {{ BINDING }}
|
||||
{% endfor %}
|
||||
- binds:
|
||||
@@ -112,8 +112,8 @@ so-elastic-fleet:
|
||||
- /etc/pki/elasticfleet-server.key:/etc/pki/elasticfleet-server.key:ro
|
||||
- /etc/pki/tls/certs/intca.crt:/etc/pki/tls/certs/intca.crt:ro
|
||||
- /opt/so/log/elasticfleet:/usr/share/elastic-agent/logs
|
||||
{% if DOCKER.containers['so-elastic-fleet'].custom_bind_mounts %}
|
||||
{% for BIND in DOCKER.containers['so-elastic-fleet'].custom_bind_mounts %}
|
||||
{% if DOCKERMERGED.containers['so-elastic-fleet'].custom_bind_mounts %}
|
||||
{% for BIND in DOCKERMERGED.containers['so-elastic-fleet'].custom_bind_mounts %}
|
||||
- {{ BIND }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
@@ -128,11 +128,17 @@ so-elastic-fleet:
|
||||
- FLEET_CA=/etc/pki/tls/certs/intca.crt
|
||||
- FLEET_SERVER_ELASTICSEARCH_CA=/etc/pki/tls/certs/intca.crt
|
||||
- LOGS_PATH=logs
|
||||
{% if DOCKER.containers['so-elastic-fleet'].extra_env %}
|
||||
{% for XTRAENV in DOCKER.containers['so-elastic-fleet'].extra_env %}
|
||||
{% if DOCKERMERGED.containers['so-elastic-fleet'].extra_env %}
|
||||
{% for XTRAENV in DOCKERMERGED.containers['so-elastic-fleet'].extra_env %}
|
||||
- {{ XTRAENV }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
{% if DOCKERMERGED.containers['so-elastic-fleet'].ulimits %}
|
||||
- ulimits:
|
||||
{% for ULIMIT in DOCKERMERGED.containers['so-elastic-fleet'].ulimits %}
|
||||
- {{ ULIMIT.name }}={{ ULIMIT.soft }}:{{ ULIMIT.hard }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
- watch:
|
||||
- file: trusttheca
|
||||
- x509: etc_elasticfleet_key
|
||||
|
||||
@@ -1,14 +1,15 @@
|
||||
elasticfleet:
|
||||
enabled:
|
||||
description: Enables or disables the Elastic Fleet process. This process is critical for managing Elastic Agents.
|
||||
forcedType: bool
|
||||
advanced: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
enable_manager_output:
|
||||
description: Setting this option to False should only be considered if there is at least one receiver node in the grid. If True, Elastic Agent will send events to the manager and receivers. If False, events will only be send to the receivers.
|
||||
advanced: True
|
||||
global: True
|
||||
forcedType: bool
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
files:
|
||||
soc:
|
||||
elastic-defend-disabled-filters__yaml:
|
||||
@@ -17,7 +18,7 @@ elasticfleet:
|
||||
syntax: yaml
|
||||
file: True
|
||||
global: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
advanced: True
|
||||
elastic-defend-custom-filters__yaml:
|
||||
title: Custom Elastic Defend filters
|
||||
@@ -25,31 +26,32 @@ elasticfleet:
|
||||
syntax: yaml
|
||||
file: True
|
||||
global: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
advanced: True
|
||||
logging:
|
||||
zeek:
|
||||
excluded:
|
||||
description: This is a list of Zeek logs that are excluded from being shipped through the data processing pipeline. If you remove a log from this list, Elastic Agent will attempt to process it. If an ingest node pipeline is not available to process the logs, you may experience errors.
|
||||
forcedType: "[]string"
|
||||
helpLink: zeek.html
|
||||
helpLink: zeek
|
||||
config:
|
||||
defend_filters:
|
||||
enable_auto_configuration:
|
||||
description: Enable auto-configuration and management of the Elastic Defend Exclusion filters.
|
||||
forcedType: bool
|
||||
global: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
advanced: True
|
||||
subscription_integrations:
|
||||
description: Enable the installation of integrations that require an Elastic license.
|
||||
global: True
|
||||
forcedType: bool
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
auto_upgrade_integrations:
|
||||
description: Enables or disables automatically upgrading Elastic Agent integrations.
|
||||
global: True
|
||||
forcedType: bool
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
outputs:
|
||||
logstash:
|
||||
bulk_max_size:
|
||||
@@ -57,67 +59,68 @@ elasticfleet:
|
||||
global: True
|
||||
forcedType: int
|
||||
advanced: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
worker:
|
||||
description: The number of workers per configured host publishing events.
|
||||
global: True
|
||||
forcedType: int
|
||||
advanced: true
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
queue_mem_events:
|
||||
title: queued events
|
||||
description: The number of events the queue can store. This value should be evenly divisible by the smaller of 'bulk_max_size' to avoid sending partial batches to the output.
|
||||
global: True
|
||||
forcedType: int
|
||||
advanced: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
timeout:
|
||||
description: The number of seconds to wait for responses from the Logstash server before timing out. Eg 30s
|
||||
regex: ^[0-9]+s$
|
||||
advanced: True
|
||||
global: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
loadbalance:
|
||||
description: If true and multiple Logstash hosts are configured, the output plugin load balances published events onto all Logstash hosts. If false, the output plugin sends all events to one host (determined at random) and switches to another host if the selected one becomes unresponsive.
|
||||
forcedType: bool
|
||||
advanced: True
|
||||
global: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
compression_level:
|
||||
description: The gzip compression level. The compression level must be in the range of 1 (best speed) to 9 (best compression).
|
||||
regex: ^[1-9]$
|
||||
forcedType: int
|
||||
advanced: True
|
||||
global: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
server:
|
||||
custom_fqdn:
|
||||
description: Custom FQDN for Agents to connect to. One per line.
|
||||
global: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
advanced: True
|
||||
forcedType: "[]string"
|
||||
enable_auto_configuration:
|
||||
description: Enable auto-configuration of Logstash Outputs & Fleet Host URLs.
|
||||
forcedType: bool
|
||||
global: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
advanced: True
|
||||
endpoints_enrollment:
|
||||
description: Endpoint enrollment key.
|
||||
global: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
sensitive: True
|
||||
advanced: True
|
||||
es_token:
|
||||
description: Elastic auth token.
|
||||
global: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
sensitive: True
|
||||
advanced: True
|
||||
grid_enrollment:
|
||||
description: Grid enrollment key.
|
||||
global: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
sensitive: True
|
||||
advanced: True
|
||||
optional_integrations:
|
||||
@@ -125,57 +128,57 @@ elasticfleet:
|
||||
enabled_nodes:
|
||||
description: Fleet nodes with the Sublime Platform integration enabled. Enter one per line.
|
||||
global: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
advanced: True
|
||||
forcedType: "[]string"
|
||||
api_key:
|
||||
description: API key for Sublime Platform.
|
||||
global: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
advanced: True
|
||||
forcedType: string
|
||||
sensitive: True
|
||||
base_url:
|
||||
description: Base URL for Sublime Platform.
|
||||
global: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
advanced: True
|
||||
forcedType: string
|
||||
poll_interval:
|
||||
description: Poll interval for alerts from Sublime Platform.
|
||||
global: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
advanced: True
|
||||
forcedType: string
|
||||
limit:
|
||||
description: The maximum number of message groups to return from Sublime Platform.
|
||||
global: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
advanced: True
|
||||
forcedType: int
|
||||
kismet:
|
||||
base_url:
|
||||
description: Base URL for Kismet.
|
||||
global: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
advanced: True
|
||||
forcedType: string
|
||||
poll_interval:
|
||||
description: Poll interval for wireless device data from Kismet. Integration is currently configured to return devices seen as active by any Kismet sensor within the last 10 minutes.
|
||||
global: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
advanced: True
|
||||
forcedType: string
|
||||
api_key:
|
||||
description: API key for Kismet.
|
||||
global: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
advanced: True
|
||||
forcedType: string
|
||||
sensitive: True
|
||||
enabled_nodes:
|
||||
description: Fleet nodes with the Kismet integration enabled. Enter one per line.
|
||||
global: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
advanced: True
|
||||
forcedType: "[]string"
|
||||
|
||||
@@ -6,8 +6,6 @@
|
||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
{% import_yaml 'elasticsearch/defaults.yaml' as ELASTICSEARCHDEFAULTS with context %}
|
||||
|
||||
{% set HIGHLANDER = salt['pillar.get']('global:highlander', False) %}
|
||||
|
||||
{# this is a list of dicts containing hostname:ip for elasticsearch nodes that need to know about each other for cluster #}
|
||||
{% set ELASTICSEARCH_SEED_HOSTS = [] %}
|
||||
{% set node_data = salt['pillar.get']('elasticsearch:nodes', {GLOBALS.role.split('-')[1]: {GLOBALS.hostname: {'ip': GLOBALS.node_ip}}}) %}
|
||||
@@ -36,14 +34,8 @@
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
{% elif grains.id.split('_') | last == 'searchnode' %}
|
||||
{% if HIGHLANDER %}
|
||||
{% do ELASTICSEARCHDEFAULTS.elasticsearch.config.node.roles.extend(['ml', 'master', 'transform']) %}
|
||||
{% endif %}
|
||||
{% do ELASTICSEARCHDEFAULTS.elasticsearch.config.update({'discovery': {'seed_hosts': [GLOBALS.manager]}}) %}
|
||||
{% endif %}
|
||||
{% if HIGHLANDER %}
|
||||
{% do ELASTICSEARCHDEFAULTS.elasticsearch.config.xpack.ml.update({'enabled': true}) %}
|
||||
{% endif %}
|
||||
|
||||
{% do ELASTICSEARCHDEFAULTS.elasticsearch.config.node.update({'name': GLOBALS.hostname}) %}
|
||||
{% do ELASTICSEARCHDEFAULTS.elasticsearch.config.cluster.update({'name': GLOBALS.hostname}) %}
|
||||
|
||||
@@ -98,10 +98,6 @@ esrolesdir:
|
||||
- group: 939
|
||||
- makedirs: True
|
||||
|
||||
eslibdir:
|
||||
file.absent:
|
||||
- name: /opt/so/conf/elasticsearch/lib
|
||||
|
||||
esingestdynamicconf:
|
||||
file.recurse:
|
||||
- name: /opt/so/conf/elasticsearch/ingest
|
||||
@@ -119,11 +115,6 @@ esingestconf:
|
||||
- group: 939
|
||||
- show_changes: False
|
||||
|
||||
# Remove .fleet_final_pipeline-1 because we are using global@custom now
|
||||
so-fleet-final-pipeline-remove:
|
||||
file.absent:
|
||||
- name: /opt/so/conf/elasticsearch/ingest/.fleet_final_pipeline-1
|
||||
|
||||
# Auto-generate Elasticsearch ingest node pipelines from pillar
|
||||
{% for pipeline, config in ELASTICSEARCHMERGED.pipelines.items() %}
|
||||
es_ingest_conf_{{pipeline}}:
|
||||
|
||||
@@ -119,7 +119,7 @@ elasticsearch:
|
||||
ignore_missing_component_templates: []
|
||||
index_patterns:
|
||||
- so-case*
|
||||
priority: 500
|
||||
priority: 501
|
||||
template:
|
||||
mappings:
|
||||
date_detection: false
|
||||
@@ -131,8 +131,6 @@ elasticsearch:
|
||||
match_mapping_type: string
|
||||
settings:
|
||||
index:
|
||||
lifecycle:
|
||||
name: so-case-logs
|
||||
mapping:
|
||||
total_fields:
|
||||
limit: 1500
|
||||
@@ -143,14 +141,7 @@ elasticsearch:
|
||||
sort:
|
||||
field: '@timestamp'
|
||||
order: desc
|
||||
policy:
|
||||
phases:
|
||||
hot:
|
||||
actions: {}
|
||||
min_age: 0ms
|
||||
so-common:
|
||||
close: 30
|
||||
delete: 365
|
||||
index_sorting: false
|
||||
index_template:
|
||||
composed_of:
|
||||
@@ -214,7 +205,9 @@ elasticsearch:
|
||||
- common-settings
|
||||
- common-dynamic-mappings
|
||||
- winlog-mappings
|
||||
data_stream: {}
|
||||
data_stream:
|
||||
allow_custom_routing: false
|
||||
hidden: false
|
||||
ignore_missing_component_templates: []
|
||||
index_patterns:
|
||||
- logs-*-so*
|
||||
@@ -274,7 +267,7 @@ elasticsearch:
|
||||
ignore_missing_component_templates: []
|
||||
index_patterns:
|
||||
- so-detection*
|
||||
priority: 500
|
||||
priority: 501
|
||||
template:
|
||||
mappings:
|
||||
date_detection: false
|
||||
@@ -286,8 +279,6 @@ elasticsearch:
|
||||
match_mapping_type: string
|
||||
settings:
|
||||
index:
|
||||
lifecycle:
|
||||
name: so-detection-logs
|
||||
mapping:
|
||||
total_fields:
|
||||
limit: 1500
|
||||
@@ -298,11 +289,6 @@ elasticsearch:
|
||||
sort:
|
||||
field: '@timestamp'
|
||||
order: desc
|
||||
policy:
|
||||
phases:
|
||||
hot:
|
||||
actions: {}
|
||||
min_age: 0ms
|
||||
sos-backup:
|
||||
index_sorting: false
|
||||
index_template:
|
||||
@@ -462,7 +448,7 @@ elasticsearch:
|
||||
ignore_missing_component_templates: []
|
||||
index_patterns:
|
||||
- endgame*
|
||||
priority: 500
|
||||
priority: 501
|
||||
template:
|
||||
mappings:
|
||||
date_detection: false
|
||||
@@ -510,8 +496,6 @@ elasticsearch:
|
||||
priority: 50
|
||||
min_age: 30d
|
||||
so-idh:
|
||||
close: 30
|
||||
delete: 365
|
||||
index_sorting: false
|
||||
index_template:
|
||||
composed_of:
|
||||
@@ -566,10 +550,13 @@ elasticsearch:
|
||||
- dtc-user_agent-mappings
|
||||
- common-settings
|
||||
- common-dynamic-mappings
|
||||
data_stream:
|
||||
allow_custom_routing: false
|
||||
hidden: false
|
||||
ignore_missing_component_templates: []
|
||||
index_patterns:
|
||||
- so-idh-*
|
||||
priority: 500
|
||||
- logs-idh-so*
|
||||
priority: 501
|
||||
template:
|
||||
mappings:
|
||||
date_detection: false
|
||||
@@ -679,11 +666,13 @@ elasticsearch:
|
||||
- common-dynamic-mappings
|
||||
- winlog-mappings
|
||||
- hash-mappings
|
||||
data_stream: {}
|
||||
data_stream:
|
||||
allow_custom_routing: false
|
||||
hidden: false
|
||||
ignore_missing_component_templates: []
|
||||
index_patterns:
|
||||
- logs-import-so*
|
||||
priority: 500
|
||||
priority: 501
|
||||
template:
|
||||
mappings:
|
||||
date_detection: false
|
||||
@@ -738,7 +727,7 @@ elasticsearch:
|
||||
ignore_missing_component_templates: []
|
||||
index_patterns:
|
||||
- so-ip*
|
||||
priority: 500
|
||||
priority: 501
|
||||
template:
|
||||
mappings:
|
||||
date_detection: false
|
||||
@@ -753,19 +742,12 @@ elasticsearch:
|
||||
mapping:
|
||||
total_fields:
|
||||
limit: 1500
|
||||
lifecycle:
|
||||
name: so-ip-mappings-logs
|
||||
number_of_replicas: 0
|
||||
number_of_shards: 1
|
||||
refresh_interval: 30s
|
||||
sort:
|
||||
field: '@timestamp'
|
||||
order: desc
|
||||
policy:
|
||||
phases:
|
||||
hot:
|
||||
actions: {}
|
||||
min_age: 0ms
|
||||
so-items:
|
||||
index_sorting: false
|
||||
index_template:
|
||||
@@ -774,7 +756,7 @@ elasticsearch:
|
||||
ignore_missing_component_templates: []
|
||||
index_patterns:
|
||||
- .items-default-**
|
||||
priority: 500
|
||||
priority: 501
|
||||
template:
|
||||
mappings:
|
||||
date_detection: false
|
||||
@@ -853,8 +835,6 @@ elasticsearch:
|
||||
priority: 50
|
||||
min_age: 30d
|
||||
so-kratos:
|
||||
close: 30
|
||||
delete: 365
|
||||
index_sorting: false
|
||||
index_template:
|
||||
composed_of:
|
||||
@@ -875,7 +855,7 @@ elasticsearch:
|
||||
ignore_missing_component_templates: []
|
||||
index_patterns:
|
||||
- logs-kratos-so*
|
||||
priority: 500
|
||||
priority: 501
|
||||
template:
|
||||
mappings:
|
||||
date_detection: false
|
||||
@@ -923,8 +903,6 @@ elasticsearch:
|
||||
priority: 50
|
||||
min_age: 30d
|
||||
so-hydra:
|
||||
close: 30
|
||||
delete: 365
|
||||
index_sorting: false
|
||||
index_template:
|
||||
composed_of:
|
||||
@@ -985,7 +963,7 @@ elasticsearch:
|
||||
ignore_missing_component_templates: []
|
||||
index_patterns:
|
||||
- logs-hydra-so*
|
||||
priority: 500
|
||||
priority: 501
|
||||
template:
|
||||
mappings:
|
||||
date_detection: false
|
||||
@@ -1040,7 +1018,7 @@ elasticsearch:
|
||||
ignore_missing_component_templates: []
|
||||
index_patterns:
|
||||
- .lists-default-**
|
||||
priority: 500
|
||||
priority: 501
|
||||
template:
|
||||
mappings:
|
||||
date_detection: false
|
||||
@@ -1526,6 +1504,9 @@ elasticsearch:
|
||||
- so-fleet_integrations.ip_mappings-1
|
||||
- so-fleet_globals-1
|
||||
- so-fleet_agent_id_verification-1
|
||||
data_stream:
|
||||
allow_custom_routing: false
|
||||
hidden: false
|
||||
ignore_missing_component_templates:
|
||||
- logs-elastic_agent.cloudbeat@custom
|
||||
index_patterns:
|
||||
@@ -1761,6 +1742,9 @@ elasticsearch:
|
||||
- so-fleet_integrations.ip_mappings-1
|
||||
- so-fleet_globals-1
|
||||
- so-fleet_agent_id_verification-1
|
||||
data_stream:
|
||||
allow_custom_routing: false
|
||||
hidden: false
|
||||
ignore_missing_component_templates:
|
||||
- logs-elastic_agent.heartbeat@custom
|
||||
index_patterns:
|
||||
@@ -3020,8 +3004,6 @@ elasticsearch:
|
||||
priority: 50
|
||||
min_age: 30d
|
||||
so-logs-soc:
|
||||
close: 30
|
||||
delete: 365
|
||||
index_sorting: false
|
||||
index_template:
|
||||
composed_of:
|
||||
@@ -3076,11 +3058,13 @@ elasticsearch:
|
||||
- dtc-user_agent-mappings
|
||||
- common-settings
|
||||
- common-dynamic-mappings
|
||||
data_stream: {}
|
||||
data_stream:
|
||||
allow_custom_routing: false
|
||||
hidden: false
|
||||
ignore_missing_component_templates: []
|
||||
index_patterns:
|
||||
- logs-soc-so*
|
||||
priority: 500
|
||||
priority: 501
|
||||
template:
|
||||
mappings:
|
||||
date_detection: false
|
||||
@@ -3670,10 +3654,13 @@ elasticsearch:
|
||||
- vulnerability-mappings
|
||||
- common-settings
|
||||
- common-dynamic-mappings
|
||||
data_stream:
|
||||
allow_custom_routing: false
|
||||
hidden: false
|
||||
ignore_missing_component_templates: []
|
||||
index_patterns:
|
||||
- logs-logstash-default*
|
||||
priority: 500
|
||||
priority: 501
|
||||
template:
|
||||
mappings:
|
||||
date_detection: false
|
||||
@@ -3971,10 +3958,13 @@ elasticsearch:
|
||||
- vulnerability-mappings
|
||||
- common-settings
|
||||
- common-dynamic-mappings
|
||||
data_stream:
|
||||
allow_custom_routing: false
|
||||
hidden: false
|
||||
ignore_missing_component_templates: []
|
||||
index_patterns:
|
||||
- logs-redis-default*
|
||||
priority: 500
|
||||
- logs-redis.log*
|
||||
priority: 501
|
||||
template:
|
||||
mappings:
|
||||
date_detection: false
|
||||
@@ -4085,11 +4075,13 @@ elasticsearch:
|
||||
- common-settings
|
||||
- common-dynamic-mappings
|
||||
- hash-mappings
|
||||
data_stream: {}
|
||||
data_stream:
|
||||
allow_custom_routing: false
|
||||
hidden: false
|
||||
ignore_missing_component_templates: []
|
||||
index_patterns:
|
||||
- logs-strelka-so*
|
||||
priority: 500
|
||||
priority: 501
|
||||
template:
|
||||
mappings:
|
||||
date_detection: false
|
||||
@@ -4199,11 +4191,13 @@ elasticsearch:
|
||||
- common-settings
|
||||
- common-dynamic-mappings
|
||||
- hash-mappings
|
||||
data_stream: {}
|
||||
data_stream:
|
||||
allow_custom_routing: false
|
||||
hidden: false
|
||||
ignore_missing_component_templates: []
|
||||
index_patterns:
|
||||
- logs-suricata-so*
|
||||
priority: 500
|
||||
priority: 501
|
||||
template:
|
||||
mappings:
|
||||
date_detection: false
|
||||
@@ -4313,11 +4307,13 @@ elasticsearch:
|
||||
- common-settings
|
||||
- common-dynamic-mappings
|
||||
- hash-mappings
|
||||
data_stream: {}
|
||||
data_stream:
|
||||
allow_custom_routing: false
|
||||
hidden: false
|
||||
ignore_missing_component_templates: []
|
||||
index_patterns:
|
||||
- logs-suricata.alerts-*
|
||||
priority: 500
|
||||
priority: 501
|
||||
template:
|
||||
mappings:
|
||||
date_detection: false
|
||||
@@ -4427,11 +4423,13 @@ elasticsearch:
|
||||
- vulnerability-mappings
|
||||
- common-settings
|
||||
- common-dynamic-mappings
|
||||
data_stream: {}
|
||||
data_stream:
|
||||
allow_custom_routing: false
|
||||
hidden: false
|
||||
ignore_missing_component_templates: []
|
||||
index_patterns:
|
||||
- logs-syslog-so*
|
||||
priority: 500
|
||||
priority: 501
|
||||
template:
|
||||
mappings:
|
||||
date_detection: false
|
||||
@@ -4543,11 +4541,13 @@ elasticsearch:
|
||||
- common-settings
|
||||
- common-dynamic-mappings
|
||||
- hash-mappings
|
||||
data_stream: {}
|
||||
data_stream:
|
||||
allow_custom_routing: false
|
||||
hidden: false
|
||||
ignore_missing_component_templates: []
|
||||
index_patterns:
|
||||
- logs-zeek-so*
|
||||
priority: 500
|
||||
priority: 501
|
||||
template:
|
||||
mappings:
|
||||
date_detection: false
|
||||
|
||||
@@ -6,7 +6,7 @@
|
||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
||||
{% if sls.split('.')[0] in allowed_states %}
|
||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKER %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKERMERGED %}
|
||||
{% from 'elasticsearch/config.map.jinja' import ELASTICSEARCH_NODES %}
|
||||
{% from 'elasticsearch/config.map.jinja' import ELASTICSEARCH_SEED_HOSTS %}
|
||||
{% from 'elasticsearch/config.map.jinja' import ELASTICSEARCHMERGED %}
|
||||
@@ -28,15 +28,15 @@ so-elasticsearch:
|
||||
- user: elasticsearch
|
||||
- networks:
|
||||
- sobridge:
|
||||
- ipv4_address: {{ DOCKER.containers['so-elasticsearch'].ip }}
|
||||
- ipv4_address: {{ DOCKERMERGED.containers['so-elasticsearch'].ip }}
|
||||
- extra_hosts:
|
||||
{% for node in ELASTICSEARCH_NODES %}
|
||||
{% for hostname, ip in node.items() %}
|
||||
- {{hostname}}:{{ip}}
|
||||
{% endfor %}
|
||||
{% endfor %}
|
||||
{% if DOCKER.containers['so-elasticsearch'].extra_hosts %}
|
||||
{% for XTRAHOST in DOCKER.containers['so-elasticsearch'].extra_hosts %}
|
||||
{% if DOCKERMERGED.containers['so-elasticsearch'].extra_hosts %}
|
||||
{% for XTRAHOST in DOCKERMERGED.containers['so-elasticsearch'].extra_hosts %}
|
||||
- {{ XTRAHOST }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
@@ -45,17 +45,19 @@ so-elasticsearch:
|
||||
- discovery.type=single-node
|
||||
{% endif %}
|
||||
- ES_JAVA_OPTS=-Xms{{ GLOBALS.elasticsearch.es_heap }} -Xmx{{ GLOBALS.elasticsearch.es_heap }} -Des.transport.cname_in_publish_address=true -Dlog4j2.formatMsgNoLookups=true
|
||||
ulimits:
|
||||
- memlock=-1:-1
|
||||
- nofile=65536:65536
|
||||
- nproc=4096
|
||||
{% if DOCKER.containers['so-elasticsearch'].extra_env %}
|
||||
{% for XTRAENV in DOCKER.containers['so-elasticsearch'].extra_env %}
|
||||
{% if DOCKERMERGED.containers['so-elasticsearch'].extra_env %}
|
||||
{% for XTRAENV in DOCKERMERGED.containers['so-elasticsearch'].extra_env %}
|
||||
- {{ XTRAENV }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
{% if DOCKERMERGED.containers['so-elasticsearch'].ulimits %}
|
||||
- ulimits:
|
||||
{% for ULIMIT in DOCKERMERGED.containers['so-elasticsearch'].ulimits %}
|
||||
- {{ ULIMIT.name }}={{ ULIMIT.soft }}:{{ ULIMIT.hard }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
- port_bindings:
|
||||
{% for BINDING in DOCKER.containers['so-elasticsearch'].port_bindings %}
|
||||
{% for BINDING in DOCKERMERGED.containers['so-elasticsearch'].port_bindings %}
|
||||
- {{ BINDING }}
|
||||
{% endfor %}
|
||||
- binds:
|
||||
@@ -75,8 +77,8 @@ so-elasticsearch:
|
||||
- {{ repo }}:{{ repo }}:rw
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
{% if DOCKER.containers['so-elasticsearch'].custom_bind_mounts %}
|
||||
{% for BIND in DOCKER.containers['so-elasticsearch'].custom_bind_mounts %}
|
||||
{% if DOCKERMERGED.containers['so-elasticsearch'].custom_bind_mounts %}
|
||||
{% for BIND in DOCKERMERGED.containers['so-elasticsearch'].custom_bind_mounts %}
|
||||
- {{ BIND }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
|
||||
0
salt/elasticsearch/files/ingest-dynamic/.gitkeep
Normal file
0
salt/elasticsearch/files/ingest-dynamic/.gitkeep
Normal file
@@ -1,5 +1,3 @@
|
||||
{%- set HIGHLANDER = salt['pillar.get']('global:highlander', False) -%}
|
||||
{%- raw -%}
|
||||
{
|
||||
"description" : "common",
|
||||
"processors" : [
|
||||
@@ -67,19 +65,7 @@
|
||||
{ "append": { "if": "ctx.dataset_tag_temp != null", "field": "tags", "value": "{{dataset_tag_temp.1}}" } },
|
||||
{ "grok": { "if": "ctx.http?.response?.status_code != null", "field": "http.response.status_code", "patterns": ["%{NUMBER:http.response.status_code:long} %{GREEDYDATA}"]} },
|
||||
{ "set": { "if": "ctx?.metadata?.kafka != null" , "field": "kafka.id", "value": "{{metadata.kafka.partition}}{{metadata.kafka.offset}}{{metadata.kafka.timestamp}}", "ignore_failure": true } },
|
||||
{ "remove": { "field": [ "message2", "type", "fields", "category", "module", "dataset", "dataset_tag_temp", "event.dataset_temp" ], "ignore_missing": true, "ignore_failure": true } }
|
||||
{%- endraw %}
|
||||
{%- if HIGHLANDER %}
|
||||
,
|
||||
{
|
||||
"pipeline": {
|
||||
"name": "ecs"
|
||||
}
|
||||
}
|
||||
{%- endif %}
|
||||
{%- raw %}
|
||||
,
|
||||
{ "remove": { "field": [ "message2", "type", "fields", "category", "module", "dataset", "dataset_tag_temp", "event.dataset_temp" ], "ignore_missing": true, "ignore_failure": true } },
|
||||
{ "pipeline": { "name": "global@custom", "ignore_missing_pipeline": true, "description": "[Fleet] Global pipeline for all data streams" } }
|
||||
]
|
||||
}
|
||||
{% endraw %}
|
||||
@@ -1,8 +1,9 @@
|
||||
elasticsearch:
|
||||
enabled:
|
||||
description: Enables or disables the Elasticsearch process. This process provides the log event storage system. WARNING - Disabling this process is unsupported.
|
||||
forcedType: bool
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
version:
|
||||
description: "This specifies the version of the following containers: so-elastic-fleet-package-registry, so-elastic-agent, so-elastic-fleet, so-kibana, so-logstash and so-elasticsearch. Modifying this value in the Elasticsearch defaults.yaml will result in catastrophic grid failure."
|
||||
readonly: True
|
||||
@@ -10,20 +11,20 @@ elasticsearch:
|
||||
advanced: True
|
||||
esheap:
|
||||
description: Specify the memory heap size in (m)egabytes for Elasticsearch.
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
index_clean:
|
||||
description: Determines if indices should be considered for deletion by available disk space in the cluster. Otherwise, indices will only be deleted by the age defined in the ILM settings. This setting only applies to EVAL, STANDALONE, and HEAVY NODE installations. Other installations can only use ILM settings.
|
||||
forcedType: bool
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
vm:
|
||||
max_map_count:
|
||||
description: The maximum number of memory map areas a process may use. Elasticsearch uses a mmapfs directory by default to store its indices. The default operating system limits on mmap counts could be too low, which may result in out of memory exceptions.
|
||||
forcedType: int
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
retention:
|
||||
retention_pct:
|
||||
decription: Total percentage of space used by Elasticsearch for multi node clusters
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
global: True
|
||||
config:
|
||||
cluster:
|
||||
@@ -31,55 +32,102 @@ elasticsearch:
|
||||
description: The name of the Security Onion Elasticsearch cluster, for identification purposes.
|
||||
readonly: True
|
||||
global: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
logsdb:
|
||||
enabled:
|
||||
description: Enables or disables the Elasticsearch logsdb index mode. When enabled, most logs-* datastreams will convert to logsdb from standard after rolling over.
|
||||
forcedType: bool
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
routing:
|
||||
allocation:
|
||||
disk:
|
||||
threshold_enabled:
|
||||
threshold_enabled:
|
||||
description: Specifies whether the Elasticsearch node will monitor the available disk space for low disk space conditions and take action to protect the cluster.
|
||||
helpLink: elasticsearch.html
|
||||
forcedType: bool
|
||||
helpLink: elasticsearch
|
||||
watermark:
|
||||
low:
|
||||
description: The lower percentage of used disk space representing a healthy node.
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
high:
|
||||
description: The higher percentage of used disk space representing an unhealthy node.
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
flood_stage:
|
||||
description: The max percentage of used disk space that will cause the node to take protective actions, such as blocking incoming events.
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
action:
|
||||
destructive_requires_name:
|
||||
description: Requires explicit index names when deleting indices. Prevents accidental deletion of indices via wildcard patterns.
|
||||
advanced: True
|
||||
forcedType: bool
|
||||
helpLink: elasticsearch
|
||||
script:
|
||||
max_compilations_rate:
|
||||
max_compilations_rate:
|
||||
description: Max rate of script compilations permitted in the Elasticsearch cluster. Larger values will consume more resources.
|
||||
global: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
indices:
|
||||
id_field_data:
|
||||
enabled:
|
||||
description: Enables or disables loading of field data on the _id field.
|
||||
advanced: True
|
||||
forcedType: bool
|
||||
helpLink: elasticsearch
|
||||
query:
|
||||
bool:
|
||||
max_clause_count:
|
||||
max_clause_count:
|
||||
description: Max number of boolean clauses per query.
|
||||
global: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
xpack:
|
||||
ml:
|
||||
enabled:
|
||||
description: Enables or disables machine learning on the node.
|
||||
forcedType: bool
|
||||
advanced: True
|
||||
helpLink: elasticsearch
|
||||
security:
|
||||
enabled:
|
||||
description: Enables or disables Elasticsearch security features.
|
||||
forcedType: bool
|
||||
advanced: True
|
||||
helpLink: elasticsearch
|
||||
authc:
|
||||
anonymous:
|
||||
authz_exception:
|
||||
description: Controls whether an authorization exception is thrown when anonymous user does not have the required privileges.
|
||||
advanced: True
|
||||
forcedType: bool
|
||||
helpLink: elasticsearch
|
||||
http:
|
||||
ssl:
|
||||
enabled:
|
||||
description: Enables or disables TLS/SSL for the HTTP layer.
|
||||
advanced: True
|
||||
forcedType: bool
|
||||
helpLink: elasticsearch
|
||||
transport:
|
||||
ssl:
|
||||
enabled:
|
||||
description: Enables or disables TLS/SSL for the transport layer.
|
||||
advanced: True
|
||||
forcedType: bool
|
||||
helpLink: elasticsearch
|
||||
pipelines:
|
||||
custom001: &pipelines
|
||||
description:
|
||||
description: Description of the ingest node pipeline
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
processors:
|
||||
description: Processors for the ingest node pipeline
|
||||
global: True
|
||||
advanced: True
|
||||
multiline: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
custom002: *pipelines
|
||||
custom003: *pipelines
|
||||
custom004: *pipelines
|
||||
@@ -99,24 +147,24 @@ elasticsearch:
|
||||
description: Number of replicas required for all indices. Multiple replicas protects against data loss, but also increases storage costs. This setting will be applied to all indices.
|
||||
forcedType: int
|
||||
global: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
refresh_interval:
|
||||
description: Seconds between index refreshes. Shorter intervals can cause query performance to suffer since this is a synchronous and resource-intensive operation.
|
||||
global: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
number_of_shards:
|
||||
description: Number of shards required for this index. Using multiple shards increases fault tolerance, but also increases storage and network costs.
|
||||
global: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
sort:
|
||||
field:
|
||||
description: The field to sort by. Must set index_sorting to True.
|
||||
global: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
order:
|
||||
description: The order to sort by. Must set index_sorting to True.
|
||||
global: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
policy:
|
||||
phases:
|
||||
hot:
|
||||
@@ -126,16 +174,16 @@ elasticsearch:
|
||||
description: Priority of index. This is used for recovery after a node restart. Indices with higher priorities are recovered before indices with lower priorities.
|
||||
forcedType: int
|
||||
global: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
rollover:
|
||||
max_age:
|
||||
description: Maximum age of index. Once an index reaches this limit, it will be rolled over into a new index.
|
||||
global: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
max_primary_shard_size:
|
||||
description: Maximum primary shard size. Once an index reaches this limit, it will be rolled over into a new index.
|
||||
global: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
shrink:
|
||||
method:
|
||||
description: Shrink the index to a new index with fewer primary shards. Shrink operation is by count or size.
|
||||
@@ -183,13 +231,13 @@ elasticsearch:
|
||||
regex: ^[0-9]{1,5}d$
|
||||
forcedType: string
|
||||
global: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
actions:
|
||||
set_priority:
|
||||
priority:
|
||||
description: Used for index recovery after a node restart. Indices with higher priorities are recovered before indices with lower priorities.
|
||||
global: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
allocate:
|
||||
number_of_replicas:
|
||||
description: Set the number of replicas. Remains the same as the previous phase by default.
|
||||
@@ -202,14 +250,14 @@ elasticsearch:
|
||||
regex: ^[0-9]{1,5}d$
|
||||
forcedType: string
|
||||
global: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
actions:
|
||||
set_priority:
|
||||
priority:
|
||||
description: Priority of index. This is used for recovery after a node restart. Indices with higher priorities are recovered before indices with lower priorities.
|
||||
forcedType: int
|
||||
global: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
shrink:
|
||||
method:
|
||||
description: Shrink the index to a new index with fewer primary shards. Shrink operation is by count or size.
|
||||
@@ -262,13 +310,14 @@ elasticsearch:
|
||||
regex: ^[0-9]{1,5}d$
|
||||
forcedType: string
|
||||
global: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
so-logs: &indexSettings
|
||||
index_sorting:
|
||||
index_sorting:
|
||||
description: Sorts the index by event time, at the cost of additional processing resource consumption.
|
||||
forcedType: bool
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
index_template:
|
||||
index_patterns:
|
||||
description: Patterns for matching multiple indices or tables.
|
||||
@@ -276,7 +325,7 @@ elasticsearch:
|
||||
multiline: True
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
template:
|
||||
settings:
|
||||
index:
|
||||
@@ -285,35 +334,35 @@ elasticsearch:
|
||||
forcedType: int
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
mapping:
|
||||
total_fields:
|
||||
limit:
|
||||
description: Max number of fields that can exist on a single index. Larger values will consume more resources.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
refresh_interval:
|
||||
description: Seconds between index refreshes. Shorter intervals can cause query performance to suffer since this is a synchronous and resource-intensive operation.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
number_of_shards:
|
||||
description: Number of shards required for this index. Using multiple shards increases fault tolerance, but also increases storage and network costs.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
sort:
|
||||
field:
|
||||
description: The field to sort by. Must set index_sorting to True.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
order:
|
||||
description: The order to sort by. Must set index_sorting to True.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
mappings:
|
||||
_meta:
|
||||
package:
|
||||
@@ -321,43 +370,43 @@ elasticsearch:
|
||||
description: Meta settings for the mapping.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
managed_by:
|
||||
description: Meta settings for the mapping.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
managed:
|
||||
description: Meta settings for the mapping.
|
||||
forcedType: bool
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
composed_of:
|
||||
description: The index template is composed of these component templates.
|
||||
forcedType: "[]string"
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
priority:
|
||||
description: The priority of the index template.
|
||||
forcedType: int
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
data_stream:
|
||||
hidden:
|
||||
description: Hide the data stream.
|
||||
forcedType: bool
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
allow_custom_routing:
|
||||
description: Allow custom routing for the data stream.
|
||||
forcedType: bool
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
policy:
|
||||
phases:
|
||||
hot:
|
||||
@@ -365,7 +414,7 @@ elasticsearch:
|
||||
description: Minimum age of index. This determines when the index should be moved to the hot tier.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
actions:
|
||||
set_priority:
|
||||
priority:
|
||||
@@ -373,18 +422,18 @@ elasticsearch:
|
||||
forcedType: int
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
rollover:
|
||||
max_age:
|
||||
description: Maximum age of index. Once an index reaches this limit, it will be rolled over into a new index.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
max_primary_shard_size:
|
||||
description: Maximum primary shard size. Once an index reaches this limit, it will be rolled over into a new index.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
shrink:
|
||||
method:
|
||||
description: Shrink the index to a new index with fewer primary shards. Shrink operation is by count or size.
|
||||
@@ -433,7 +482,7 @@ elasticsearch:
|
||||
forcedType: string
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
actions:
|
||||
set_priority:
|
||||
priority:
|
||||
@@ -441,18 +490,18 @@ elasticsearch:
|
||||
forcedType: int
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
rollover:
|
||||
max_age:
|
||||
description: Maximum age of index. Once an index reaches this limit, it will be rolled over into a new index.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
max_primary_shard_size:
|
||||
description: Maximum primary shard size. Once an index reaches this limit, it will be rolled over into a new index.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
shrink:
|
||||
method:
|
||||
description: Shrink the index to a new index with fewer primary shards. Shrink operation is by count or size.
|
||||
@@ -506,7 +555,7 @@ elasticsearch:
|
||||
forcedType: string
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
actions:
|
||||
set_priority:
|
||||
priority:
|
||||
@@ -514,7 +563,7 @@ elasticsearch:
|
||||
forcedType: int
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
allocate:
|
||||
number_of_replicas:
|
||||
description: Set the number of replicas. Remains the same as the previous phase by default.
|
||||
@@ -528,25 +577,25 @@ elasticsearch:
|
||||
forcedType: string
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
_meta:
|
||||
package:
|
||||
name:
|
||||
description: Meta settings for the mapping.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
managed_by:
|
||||
description: Meta settings for the mapping.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
managed:
|
||||
description: Meta settings for the mapping.
|
||||
forcedType: bool
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
so-logs-system_x_auth: *indexSettings
|
||||
so-logs-system_x_syslog: *indexSettings
|
||||
so-logs-system_x_system: *indexSettings
|
||||
@@ -609,20 +658,21 @@ elasticsearch:
|
||||
so-metrics-fleet_server_x_agent_status: &fleetMetricsSettings
|
||||
index_sorting:
|
||||
description: Sorts the index by event time, at the cost of additional processing resource consumption.
|
||||
forcedType: bool
|
||||
advanced: True
|
||||
readonly: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
index_template:
|
||||
ignore_missing_component_templates:
|
||||
description: Ignore component templates if they aren't in Elasticsearch.
|
||||
advanced: True
|
||||
readonly: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
index_patterns:
|
||||
description: Patterns for matching multiple indices or tables.
|
||||
advanced: True
|
||||
readonly: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
template:
|
||||
settings:
|
||||
index:
|
||||
@@ -630,33 +680,35 @@ elasticsearch:
|
||||
description: Type of mode used for this index. Time series indices can be used for metrics to reduce necessary storage.
|
||||
advanced: True
|
||||
readonly: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
number_of_replicas:
|
||||
description: Number of replicas required for this index. Multiple replicas protects against data loss, but also increases storage costs.
|
||||
advanced: True
|
||||
readonly: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
composed_of:
|
||||
description: The index template is composed of these component templates.
|
||||
advanced: True
|
||||
readonly: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
priority:
|
||||
description: The priority of the index template.
|
||||
advanced: True
|
||||
readonly: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
data_stream:
|
||||
hidden:
|
||||
description: Hide the data stream.
|
||||
forcedType: bool
|
||||
advanced: True
|
||||
readonly: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
allow_custom_routing:
|
||||
description: Allow custom routing for the data stream.
|
||||
forcedType: bool
|
||||
advanced: True
|
||||
readonly: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
so-metrics-fleet_server_x_agent_versions: *fleetMetricsSettings
|
||||
so_roles:
|
||||
so-manager: &soroleSettings
|
||||
@@ -667,7 +719,7 @@ elasticsearch:
|
||||
forcedType: "[]string"
|
||||
global: False
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
so-managersearch: *soroleSettings
|
||||
so-standalone: *soroleSettings
|
||||
so-searchnode: *soroleSettings
|
||||
|
||||
@@ -27,14 +27,12 @@ iptables_config:
|
||||
- source: salt://firewall/iptables.jinja
|
||||
- template: jinja
|
||||
|
||||
{% if grains.os_family == 'RedHat' %}
|
||||
disable_firewalld:
|
||||
service.dead:
|
||||
- name: firewalld
|
||||
- enable: False
|
||||
- require:
|
||||
- file: iptables_config
|
||||
{% endif %}
|
||||
|
||||
iptables_restore:
|
||||
cmd.run:
|
||||
@@ -44,7 +42,6 @@ iptables_restore:
|
||||
- onlyif:
|
||||
- iptables-restore --test {{ iptmap.configfile }}
|
||||
|
||||
{% if grains.os_family == 'RedHat' %}
|
||||
enable_firewalld:
|
||||
service.running:
|
||||
- name: firewalld
|
||||
@@ -52,7 +49,6 @@ enable_firewalld:
|
||||
- onfail:
|
||||
- file: iptables_config
|
||||
- cmd: iptables_restore
|
||||
{% endif %}
|
||||
|
||||
{% else %}
|
||||
|
||||
|
||||
@@ -1,14 +1,6 @@
|
||||
{% set iptmap = salt['grains.filter_by']({
|
||||
'Debian': {
|
||||
'service': 'netfilter-persistent',
|
||||
'iptpkg': 'iptables',
|
||||
'persistpkg': 'iptables-persistent',
|
||||
'configfile': '/etc/iptables/rules.v4'
|
||||
},
|
||||
'RedHat': {
|
||||
'service': 'iptables',
|
||||
'iptpkg': 'iptables-nft',
|
||||
'persistpkg': 'iptables-nft-services',
|
||||
'configfile': '/etc/sysconfig/iptables'
|
||||
},
|
||||
}) %}
|
||||
{% set iptmap = {
|
||||
'service': 'iptables',
|
||||
'iptpkg': 'iptables-nft',
|
||||
'persistpkg': 'iptables-nft-services',
|
||||
'configfile': '/etc/sysconfig/iptables'
|
||||
} %}
|
||||
|
||||
@@ -1,5 +1,5 @@
|
||||
{%- from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
{%- from 'docker/docker.map.jinja' import DOCKER %}
|
||||
{%- from 'docker/docker.map.jinja' import DOCKERMERGED %}
|
||||
{%- from 'firewall/map.jinja' import FIREWALL_MERGED %}
|
||||
{%- set role = GLOBALS.role.split('-')[1] %}
|
||||
{%- from 'firewall/containers.map.jinja' import NODE_CONTAINERS %}
|
||||
@@ -8,9 +8,9 @@
|
||||
{%- set D1 = [] %}
|
||||
{%- set D2 = [] %}
|
||||
{%- for container in NODE_CONTAINERS %}
|
||||
{%- set IP = DOCKER.containers[container].ip %}
|
||||
{%- if DOCKER.containers[container].port_bindings is defined %}
|
||||
{%- for binding in DOCKER.containers[container].port_bindings %}
|
||||
{%- set IP = DOCKERMERGED.containers[container].ip %}
|
||||
{%- if DOCKERMERGED.containers[container].port_bindings is defined %}
|
||||
{%- for binding in DOCKERMERGED.containers[container].port_bindings %}
|
||||
{#- cant split int so we convert to string #}
|
||||
{%- set binding = binding|string %}
|
||||
{#- split the port binding by /. if proto not specified, default is tcp #}
|
||||
@@ -33,13 +33,13 @@
|
||||
{%- set hostPort = bsa[0] %}
|
||||
{%- set containerPort = bsa[1] %}
|
||||
{%- endif %}
|
||||
{%- do PR.append("-A POSTROUTING -s " ~ DOCKER.containers[container].ip ~ "/32 -d " ~ DOCKER.containers[container].ip ~ "/32 -p " ~ proto ~ " -m " ~ proto ~ " --dport " ~ containerPort ~ " -j MASQUERADE") %}
|
||||
{%- do PR.append("-A POSTROUTING -s " ~ DOCKERMERGED.containers[container].ip ~ "/32 -d " ~ DOCKERMERGED.containers[container].ip ~ "/32 -p " ~ proto ~ " -m " ~ proto ~ " --dport " ~ containerPort ~ " -j MASQUERADE") %}
|
||||
{%- if bindip | length and bindip != '0.0.0.0' %}
|
||||
{%- do D1.append("-A DOCKER -d " ~ bindip ~ "/32 ! -i sobridge -p " ~ proto ~ " -m " ~ proto ~ " --dport " ~ hostPort ~ " -j DNAT --to-destination " ~ DOCKER.containers[container].ip ~ ":" ~ containerPort) %}
|
||||
{%- do D1.append("-A DOCKER -d " ~ bindip ~ "/32 ! -i sobridge -p " ~ proto ~ " -m " ~ proto ~ " --dport " ~ hostPort ~ " -j DNAT --to-destination " ~ DOCKERMERGED.containers[container].ip ~ ":" ~ containerPort) %}
|
||||
{%- else %}
|
||||
{%- do D1.append("-A DOCKER ! -i sobridge -p " ~ proto ~ " -m " ~ proto ~ " --dport " ~ hostPort ~ " -j DNAT --to-destination " ~ DOCKER.containers[container].ip ~ ":" ~ containerPort) %}
|
||||
{%- do D1.append("-A DOCKER ! -i sobridge -p " ~ proto ~ " -m " ~ proto ~ " --dport " ~ hostPort ~ " -j DNAT --to-destination " ~ DOCKERMERGED.containers[container].ip ~ ":" ~ containerPort) %}
|
||||
{%- endif %}
|
||||
{%- do D2.append("-A DOCKER -d " ~ DOCKER.containers[container].ip ~ "/32 ! -i sobridge -o sobridge -p " ~ proto ~ " -m " ~ proto ~ " --dport " ~ containerPort ~ " -j ACCEPT") %}
|
||||
{%- do D2.append("-A DOCKER -d " ~ DOCKERMERGED.containers[container].ip ~ "/32 ! -i sobridge -o sobridge -p " ~ proto ~ " -m " ~ proto ~ " --dport " ~ containerPort ~ " -j ACCEPT") %}
|
||||
{%- endfor %}
|
||||
{%- endif %}
|
||||
{%- endfor %}
|
||||
@@ -52,7 +52,7 @@
|
||||
:DOCKER - [0:0]
|
||||
-A PREROUTING -m addrtype --dst-type LOCAL -j DOCKER
|
||||
-A OUTPUT ! -d 127.0.0.0/8 -m addrtype --dst-type LOCAL -j DOCKER
|
||||
-A POSTROUTING -s {{DOCKER.range}} ! -o sobridge -j MASQUERADE
|
||||
-A POSTROUTING -s {{DOCKERMERGED.range}} ! -o sobridge -j MASQUERADE
|
||||
{%- for rule in PR %}
|
||||
{{ rule }}
|
||||
{%- endfor %}
|
||||
|
||||
@@ -1,11 +1,11 @@
|
||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKER %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKERMERGED %}
|
||||
{% import_yaml 'firewall/defaults.yaml' as FIREWALL_DEFAULT %}
|
||||
|
||||
{# add our ip to self #}
|
||||
{% do FIREWALL_DEFAULT.firewall.hostgroups.self.append(GLOBALS.node_ip) %}
|
||||
{# add dockernet range #}
|
||||
{% do FIREWALL_DEFAULT.firewall.hostgroups.dockernet.append(DOCKER.range) %}
|
||||
{% do FIREWALL_DEFAULT.firewall.hostgroups.dockernet.append(DOCKERMERGED.range) %}
|
||||
|
||||
{% if GLOBALS.role == 'so-idh' %}
|
||||
{% from 'idh/opencanary_config.map.jinja' import IDH_PORTGROUPS %}
|
||||
|
||||
@@ -3,7 +3,7 @@ firewall:
|
||||
analyst: &hostgroupsettings
|
||||
description: List of IP or CIDR blocks to allow access to this hostgroup.
|
||||
forcedType: "[]string"
|
||||
helpLink: firewall.html
|
||||
helpLink: firewall
|
||||
multiline: True
|
||||
regex: ^(([0-9]{1,3}\.){3}[0-9]{1,3}(\/([0-9]|[1-2][0-9]|3[0-2]))?)?$
|
||||
regexFailureMessage: You must enter a valid IP address or CIDR.
|
||||
@@ -11,7 +11,7 @@ firewall:
|
||||
anywhere: &hostgroupsettingsadv
|
||||
description: List of IP or CIDR blocks to allow access to this hostgroup.
|
||||
forcedType: "[]string"
|
||||
helpLink: firewall.html
|
||||
helpLink: firewall
|
||||
multiline: True
|
||||
advanced: True
|
||||
regex: ^(([0-9]{1,3}\.){3}[0-9]{1,3}(\/([0-9]|[1-2][0-9]|3[0-2]))?)?$
|
||||
@@ -22,7 +22,7 @@ firewall:
|
||||
dockernet: &ROhostgroupsettingsadv
|
||||
description: List of IP or CIDR blocks to allow access to this hostgroup.
|
||||
forcedType: "[]string"
|
||||
helpLink: firewall.html
|
||||
helpLink: firewall
|
||||
multiline: True
|
||||
advanced: True
|
||||
readonly: True
|
||||
@@ -53,7 +53,7 @@ firewall:
|
||||
customhostgroup0: &customhostgroupsettings
|
||||
description: List of IP or CIDR blocks to allow to this hostgroup.
|
||||
forcedType: "[]string"
|
||||
helpLink: firewall.html
|
||||
helpLink: firewall
|
||||
advanced: True
|
||||
multiline: True
|
||||
regex: ^(([0-9]{1,3}\.){3}[0-9]{1,3}(\/([0-9]|[1-2][0-9]|3[0-2]))?)?$
|
||||
@@ -73,14 +73,14 @@ firewall:
|
||||
tcp: &tcpsettings
|
||||
description: List of TCP ports for this port group.
|
||||
forcedType: "[]string"
|
||||
helpLink: firewall.html
|
||||
helpLink: firewall
|
||||
advanced: True
|
||||
multiline: True
|
||||
duplicates: True
|
||||
udp: &udpsettings
|
||||
description: List of UDP ports for this port group.
|
||||
forcedType: "[]string"
|
||||
helpLink: firewall.html
|
||||
helpLink: firewall
|
||||
advanced: True
|
||||
multiline: True
|
||||
duplicates: True
|
||||
@@ -206,7 +206,7 @@ firewall:
|
||||
advanced: True
|
||||
multiline: True
|
||||
forcedType: "[]string"
|
||||
helpLink: firewall.html
|
||||
helpLink: firewall
|
||||
duplicates: True
|
||||
sensor:
|
||||
portgroups: *portgroupsdocker
|
||||
@@ -262,7 +262,7 @@ firewall:
|
||||
advanced: True
|
||||
multiline: True
|
||||
forcedType: "[]string"
|
||||
helpLink: firewall.html
|
||||
helpLink: firewall
|
||||
duplicates: True
|
||||
dockernet:
|
||||
portgroups: *portgroupshost
|
||||
|
||||
@@ -1,3 +1,3 @@
|
||||
global:
|
||||
pcapengine: STENO
|
||||
pcapengine: SURICATA
|
||||
pipeline: REDIS
|
||||
@@ -18,13 +18,11 @@ global:
|
||||
regexFailureMessage: You must enter either ZEEK or SURICATA.
|
||||
global: True
|
||||
pcapengine:
|
||||
description: Which engine to use for generating pcap. Options are STENO, SURICATA or TRANSITION.
|
||||
regex: ^(STENO|SURICATA|TRANSITION)$
|
||||
description: Which engine to use for generating pcap. Currently only SURICATA is supported.
|
||||
regex: ^(SURICATA)$
|
||||
options:
|
||||
- STENO
|
||||
- SURICATA
|
||||
- TRANSITION
|
||||
regexFailureMessage: You must enter either STENO, SURICATA or TRANSITION.
|
||||
regexFailureMessage: You must enter either SURICATA.
|
||||
global: True
|
||||
ids:
|
||||
description: Which IDS engine to use. Currently only Suricata is supported.
|
||||
|
||||
@@ -1,7 +1,7 @@
|
||||
host:
|
||||
mainint:
|
||||
description: Main interface of the grid host.
|
||||
helpLink: host.html
|
||||
helpLink: ip-address
|
||||
mainip:
|
||||
description: Main IP address of the grid host.
|
||||
helpLink: host.html
|
||||
helpLink: ip-address
|
||||
|
||||
@@ -11,7 +11,7 @@
|
||||
|
||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
||||
{% if sls.split('.')[0] in allowed_states %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKER %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKERMERGED %}
|
||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
{% if 'api' in salt['pillar.get']('features', []) %}
|
||||
|
||||
@@ -26,32 +26,38 @@ so-hydra:
|
||||
- name: so-hydra
|
||||
- networks:
|
||||
- sobridge:
|
||||
- ipv4_address: {{ DOCKER.containers['so-hydra'].ip }}
|
||||
- ipv4_address: {{ DOCKERMERGED.containers['so-hydra'].ip }}
|
||||
- binds:
|
||||
- /opt/so/conf/hydra/:/hydra-conf:ro
|
||||
- /opt/so/log/hydra/:/hydra-log:rw
|
||||
- /nsm/hydra/db:/hydra-data:rw
|
||||
{% if DOCKER.containers['so-hydra'].custom_bind_mounts %}
|
||||
{% for BIND in DOCKER.containers['so-hydra'].custom_bind_mounts %}
|
||||
{% if DOCKERMERGED.containers['so-hydra'].custom_bind_mounts %}
|
||||
{% for BIND in DOCKERMERGED.containers['so-hydra'].custom_bind_mounts %}
|
||||
- {{ BIND }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
- port_bindings:
|
||||
{% for BINDING in DOCKER.containers['so-hydra'].port_bindings %}
|
||||
{% for BINDING in DOCKERMERGED.containers['so-hydra'].port_bindings %}
|
||||
- {{ BINDING }}
|
||||
{% endfor %}
|
||||
{% if DOCKER.containers['so-hydra'].extra_hosts %}
|
||||
{% if DOCKERMERGED.containers['so-hydra'].extra_hosts %}
|
||||
- extra_hosts:
|
||||
{% for XTRAHOST in DOCKER.containers['so-hydra'].extra_hosts %}
|
||||
{% for XTRAHOST in DOCKERMERGED.containers['so-hydra'].extra_hosts %}
|
||||
- {{ XTRAHOST }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
{% if DOCKER.containers['so-hydra'].extra_env %}
|
||||
{% if DOCKERMERGED.containers['so-hydra'].extra_env %}
|
||||
- environment:
|
||||
{% for XTRAENV in DOCKER.containers['so-hydra'].extra_env %}
|
||||
{% for XTRAENV in DOCKERMERGED.containers['so-hydra'].extra_env %}
|
||||
- {{ XTRAENV }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
{% if DOCKERMERGED.containers['so-hydra'].ulimits %}
|
||||
- ulimits:
|
||||
{% for ULIMIT in DOCKERMERGED.containers['so-hydra'].ulimits %}
|
||||
- {{ ULIMIT.name }}={{ ULIMIT.soft }}:{{ ULIMIT.hard }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
- restart_policy: unless-stopped
|
||||
- watch:
|
||||
- file: hydraconfig
|
||||
@@ -67,7 +73,7 @@ delete_so-hydra_so-status.disabled:
|
||||
|
||||
wait_for_hydra:
|
||||
http.wait_for_successful_query:
|
||||
- name: 'http://{{ GLOBALS.manager }}:4444/'
|
||||
- name: 'http://{{ GLOBALS.manager }}:4444/health/alive'
|
||||
- ssl: True
|
||||
- verify_ssl: False
|
||||
- status:
|
||||
|
||||
@@ -1,7 +1,8 @@
|
||||
hydra:
|
||||
enabled:
|
||||
description: Enables or disables the API authentication system, used for service account authentication. Enabling this feature requires a valid Security Onion license key. Defaults to False.
|
||||
helpLink: connect.html
|
||||
description: Enables or disables the API authentication system, used for service account authentication. Enabling this feature requires a valid Security Onion license key. Defaults to False.
|
||||
forcedType: bool
|
||||
helpLink: connect-api
|
||||
global: True
|
||||
config:
|
||||
ttl:
|
||||
@@ -9,16 +10,16 @@ hydra:
|
||||
description: Amount of time that the generated access token will be valid. Specified in the form of 2h, which means 2 hours.
|
||||
global: True
|
||||
forcedType: string
|
||||
helpLink: connect.html
|
||||
helpLink: connect-api
|
||||
log:
|
||||
level:
|
||||
description: Log level to use for Kratos logs.
|
||||
global: True
|
||||
helpLink: connect.html
|
||||
helpLink: connect-api
|
||||
format:
|
||||
description: Log output format for Kratos logs.
|
||||
global: True
|
||||
helpLink: connect.html
|
||||
helpLink: connect-api
|
||||
secrets:
|
||||
system:
|
||||
description: Secrets used for token generation. Generated during installation.
|
||||
@@ -26,4 +27,4 @@ hydra:
|
||||
sensitive: True
|
||||
advanced: True
|
||||
forcedType: "[]string"
|
||||
helpLink: connect.html
|
||||
helpLink: connect-api
|
||||
|
||||
@@ -6,7 +6,7 @@
|
||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
||||
{% if sls.split('.')[0] in allowed_states %}
|
||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKER %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKERMERGED %}
|
||||
|
||||
include:
|
||||
- idh.config
|
||||
@@ -22,23 +22,29 @@ so-idh:
|
||||
- /nsm/idh:/var/tmp:rw
|
||||
- /opt/so/conf/idh/http-skins:/usr/local/lib/python3.12/site-packages/opencanary/modules/data/http/skin:ro
|
||||
- /opt/so/conf/idh/opencanary.conf:/etc/opencanaryd/opencanary.conf:ro
|
||||
{% if DOCKER.containers['so-idh'].custom_bind_mounts %}
|
||||
{% for BIND in DOCKER.containers['so-idh'].custom_bind_mounts %}
|
||||
{% if DOCKERMERGED.containers['so-idh'].custom_bind_mounts %}
|
||||
{% for BIND in DOCKERMERGED.containers['so-idh'].custom_bind_mounts %}
|
||||
- {{ BIND }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
{% if DOCKER.containers['so-idh'].extra_hosts %}
|
||||
{% if DOCKERMERGED.containers['so-idh'].extra_hosts %}
|
||||
- extra_hosts:
|
||||
{% for XTRAHOST in DOCKER.containers['so-idh'].extra_hosts %}
|
||||
{% for XTRAHOST in DOCKERMERGED.containers['so-idh'].extra_hosts %}
|
||||
- {{ XTRAHOST }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
{% if DOCKER.containers['so-idh'].extra_env %}
|
||||
{% if DOCKERMERGED.containers['so-idh'].extra_env %}
|
||||
- environment:
|
||||
{% for XTRAENV in DOCKER.containers['so-idh'].extra_env %}
|
||||
{% for XTRAENV in DOCKERMERGED.containers['so-idh'].extra_env %}
|
||||
- {{ XTRAENV }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
{% if DOCKERMERGED.containers['so-idh'].ulimits %}
|
||||
- ulimits:
|
||||
{% for ULIMIT in DOCKERMERGED.containers['so-idh'].ulimits %}
|
||||
- {{ ULIMIT.name }}={{ ULIMIT.soft }}:{{ ULIMIT.hard }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
- watch:
|
||||
- file: opencanary_config
|
||||
- require:
|
||||
|
||||
@@ -3,7 +3,6 @@
|
||||
include:
|
||||
- idh.openssh
|
||||
|
||||
{% if grains.os_family == 'RedHat' %}
|
||||
idh_sshd_selinux:
|
||||
selinux.port_policy_present:
|
||||
- port: {{ openssh_map.config.port }}
|
||||
@@ -13,7 +12,6 @@ idh_sshd_selinux:
|
||||
- file: openssh_config
|
||||
- require:
|
||||
- pkg: python_selinux_mgmt_tools
|
||||
{% endif %}
|
||||
|
||||
openssh_config:
|
||||
file.replace:
|
||||
|
||||
@@ -16,8 +16,6 @@ openssh:
|
||||
- name: {{ openssh_map.service }}
|
||||
{% endif %}
|
||||
|
||||
{% if grains.os_family == 'RedHat' %}
|
||||
python_selinux_mgmt_tools:
|
||||
pkg.installed:
|
||||
- name: policycoreutils-python-utils
|
||||
{% endif %}
|
||||
|
||||
@@ -1,7 +1,12 @@
|
||||
idh:
|
||||
enabled:
|
||||
description: Enables or disables the Intrusion Detection Honeypot (IDH) process.
|
||||
helpLink: idh.html
|
||||
description: Enables or disables the Intrusion Detection Honeypot (IDH) process.
|
||||
forcedType: bool
|
||||
helpLink: idh
|
||||
restrict_management_ip:
|
||||
description: Restricts management IP access to the IDH node.
|
||||
forcedType: bool
|
||||
helpLink: idh
|
||||
opencanary:
|
||||
config:
|
||||
logger:
|
||||
@@ -10,7 +15,7 @@ idh:
|
||||
readonly: True
|
||||
advanced: True
|
||||
global: True
|
||||
helpLink: idh.html
|
||||
helpLink: idh
|
||||
kwargs:
|
||||
formatters:
|
||||
plain:
|
||||
@@ -24,53 +29,54 @@ idh:
|
||||
filename: *loggingOptions
|
||||
portscan_x_enabled: &serviceOptions
|
||||
description: To enable this opencanary module, set this value to true. To disable set to false. This option only applies to IDH nodes within your grid.
|
||||
helpLink: idh.html
|
||||
forcedType: bool
|
||||
helpLink: idh
|
||||
portscan_x_logfile: *loggingOptions
|
||||
portscan_x_synrate:
|
||||
description: Portscan - syn rate limiting
|
||||
advanced: True
|
||||
helpLink: idh.html
|
||||
helpLink: idh
|
||||
portscan_x_nmaposrate:
|
||||
description: Portscan - nmap OS rate limiting
|
||||
advanced: True
|
||||
helpLink: idh.html
|
||||
helpLink: idh
|
||||
portscan_x_lorate:
|
||||
description: Portscan - lo rate limiting
|
||||
advanced: True
|
||||
helpLink: idh.html
|
||||
helpLink: idh
|
||||
tcpbanner_x_maxnum:
|
||||
description: Portscan - maxnum
|
||||
advanced: True
|
||||
helpLink: idh.html
|
||||
helpLink: idh
|
||||
tcpbanner_x_enabled: *serviceOptions
|
||||
tcpbanner_1_x_enabled: *serviceOptions
|
||||
tcpbanner_1_x_port: &portOptions
|
||||
description: Port the service should listen on.
|
||||
advanced: True
|
||||
helpLink: idh.html
|
||||
helpLink: idh
|
||||
tcpbanner_1_x_datareceivedbanner: &bannerOptions
|
||||
description: Data Received Banner
|
||||
advanced: True
|
||||
helpLink: idh.html
|
||||
helpLink: idh
|
||||
tcpbanner_1_x_initbanner: *bannerOptions
|
||||
tcpbanner_1_x_alertstring_x_enabled: *serviceOptions
|
||||
tcpbanner_1_x_keep_alive_x_enabled: *serviceOptions
|
||||
tcpbanner_1_x_keep_alive_secret:
|
||||
description: Keep Alive Secret
|
||||
advanced: True
|
||||
helpLink: idh.html
|
||||
helpLink: idh
|
||||
tcpbanner_1_x_keep_alive_probes:
|
||||
description: Keep Alive Probes
|
||||
advanced: True
|
||||
helpLink: idh.html
|
||||
helpLink: idh
|
||||
tcpbanner_1_x_keep_alive_interval:
|
||||
description: Keep Alive Interval
|
||||
advanced: True
|
||||
helpLink: idh.html
|
||||
helpLink: idh
|
||||
tcpbanner_1_x_keep_alive_idle:
|
||||
description: Keep Alive Idle
|
||||
advanced: True
|
||||
helpLink: idh.html
|
||||
helpLink: idh
|
||||
ftp_x_enabled: *serviceOptions
|
||||
ftp_x_port: *portOptions
|
||||
ftp_x_banner: *bannerOptions
|
||||
@@ -82,11 +88,11 @@ idh:
|
||||
http_x_skin: &skinOptions
|
||||
description: HTTP skin
|
||||
advanced: True
|
||||
helpLink: idh.html
|
||||
helpLink: idh
|
||||
http_x_skinlist: &skinlistOptions
|
||||
description: List of skins to use for the service.
|
||||
advanced: True
|
||||
helpLink: idh.html
|
||||
helpLink: idh
|
||||
httpproxy_x_enabled: *serviceOptions
|
||||
httpproxy_x_port: *portOptions
|
||||
httpproxy_x_skin: *skinOptions
|
||||
@@ -95,7 +101,7 @@ idh:
|
||||
mssql_x_version: &versionOptions
|
||||
description: Specify the version the service should present.
|
||||
advanced: True
|
||||
helpLink: idh.html
|
||||
helpLink: idh
|
||||
mssql_x_port: *portOptions
|
||||
mysql_x_enabled: *serviceOptions
|
||||
mysql_x_port: *portOptions
|
||||
@@ -119,16 +125,17 @@ idh:
|
||||
telnet_x_honeycreds:
|
||||
description: Credentials list for the telnet service.
|
||||
advanced: True
|
||||
helpLink: idh.html
|
||||
helpLink: idh
|
||||
tftp_x_enabled: *serviceOptions
|
||||
tftp_x_port: *portOptions
|
||||
vnc_x_enabled: *serviceOptions
|
||||
vnc_x_port: *portOptions
|
||||
openssh:
|
||||
enable:
|
||||
enable:
|
||||
description: This is the real SSH service for the host machine.
|
||||
helpLink: idh.html
|
||||
forcedType: bool
|
||||
helpLink: idh
|
||||
config:
|
||||
port:
|
||||
description: Port that the real SSH service will listen on and will only be accessible from the manager.
|
||||
helpLink: idh.html
|
||||
helpLink: idh
|
||||
|
||||
@@ -6,7 +6,7 @@
|
||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
||||
{% if sls.split('.')[0] in allowed_states %}
|
||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKER %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKERMERGED %}
|
||||
{% set PASSWORD = salt['pillar.get']('secrets:influx_pass') %}
|
||||
{% set TOKEN = salt['pillar.get']('influxdb:token') %}
|
||||
|
||||
@@ -21,7 +21,7 @@ so-influxdb:
|
||||
- hostname: influxdb
|
||||
- networks:
|
||||
- sobridge:
|
||||
- ipv4_address: {{ DOCKER.containers['so-influxdb'].ip }}
|
||||
- ipv4_address: {{ DOCKERMERGED.containers['so-influxdb'].ip }}
|
||||
- environment:
|
||||
- INFLUXD_CONFIG_PATH=/conf/config.yaml
|
||||
- INFLUXDB_HTTP_LOG_ENABLED=false
|
||||
@@ -31,8 +31,8 @@ so-influxdb:
|
||||
- DOCKER_INFLUXDB_INIT_ORG=Security Onion
|
||||
- DOCKER_INFLUXDB_INIT_BUCKET=telegraf/so_short_term
|
||||
- DOCKER_INFLUXDB_INIT_ADMIN_TOKEN={{ TOKEN }}
|
||||
{% if DOCKER.containers['so-influxdb'].extra_env %}
|
||||
{% for XTRAENV in DOCKER.containers['so-influxdb'].extra_env %}
|
||||
{% if DOCKERMERGED.containers['so-influxdb'].extra_env %}
|
||||
{% for XTRAENV in DOCKERMERGED.containers['so-influxdb'].extra_env %}
|
||||
- {{ XTRAENV }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
@@ -43,21 +43,27 @@ so-influxdb:
|
||||
- /nsm/influxdb:/var/lib/influxdb2:rw
|
||||
- /etc/pki/influxdb.crt:/conf/influxdb.crt:ro
|
||||
- /etc/pki/influxdb.key:/conf/influxdb.key:ro
|
||||
{% if DOCKER.containers['so-influxdb'].custom_bind_mounts %}
|
||||
{% for BIND in DOCKER.containers['so-influxdb'].custom_bind_mounts %}
|
||||
{% if DOCKERMERGED.containers['so-influxdb'].custom_bind_mounts %}
|
||||
{% for BIND in DOCKERMERGED.containers['so-influxdb'].custom_bind_mounts %}
|
||||
- {{ BIND }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
- port_bindings:
|
||||
{% for BINDING in DOCKER.containers['so-influxdb'].port_bindings %}
|
||||
{% for BINDING in DOCKERMERGED.containers['so-influxdb'].port_bindings %}
|
||||
- {{ BINDING }}
|
||||
{% endfor %}
|
||||
{% if DOCKER.containers['so-influxdb'].extra_hosts %}
|
||||
{% if DOCKERMERGED.containers['so-influxdb'].extra_hosts %}
|
||||
- extra_hosts:
|
||||
{% for XTRAHOST in DOCKER.containers['so-influxdb'].extra_hosts %}
|
||||
{% for XTRAHOST in DOCKERMERGED.containers['so-influxdb'].extra_hosts %}
|
||||
- {{ XTRAHOST }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
{% if DOCKERMERGED.containers['so-influxdb'].ulimits %}
|
||||
- ulimits:
|
||||
{% for ULIMIT in DOCKERMERGED.containers['so-influxdb'].ulimits %}
|
||||
- {{ ULIMIT.name }}={{ ULIMIT.soft }}:{{ ULIMIT.hard }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
- watch:
|
||||
- file: influxdbconf
|
||||
- x509: influxdb_key
|
||||
|
||||
@@ -1,358 +1,372 @@
|
||||
influxdb:
|
||||
enabled:
|
||||
description: Enables the grid metrics collection storage system. Security Onion grid health monitoring requires this process to remain enabled. WARNING - Disabling the process is unsupported, and will cause unexpected results.
|
||||
helpLink: influxdb.html
|
||||
forcedType: bool
|
||||
helpLink: influxdb
|
||||
config:
|
||||
assets-path:
|
||||
description: Path to the InfluxDB user interface assets located inside the so-influxdb container.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
bolt-path:
|
||||
description: Path to the bolt DB file located inside the so-influxdb container.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
engine-path:
|
||||
description: Path to the engine directory located inside the so-influxdb container. This directory stores the time series data.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
feature-flags:
|
||||
description: List of key=value flags to enable.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
flux-log-enabled:
|
||||
description: Controls whether detailed flux query logging is enabled.
|
||||
forcedType: bool
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
hardening-enabled:
|
||||
description: If true, enforces outbound connections from the InfluxDB process must never attempt to reach an internal, private network address.
|
||||
forcedType: bool
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
http-bind-address:
|
||||
description: The URL and port on which InfluxDB will listen for new connections.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
http-idle-timeout:
|
||||
description: Keep-alive timeout while a connection waits for new requests. A value of 0 is the same as no timeout enforced.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
http-read-header-timeout:
|
||||
description: The duration to wait for a request header before closing the connection. A value of 0 is the same as no timeout enforced.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
http-read-timeout:
|
||||
description: The duration to wait for the request to be fully read before closing the connection. A value of 0 is the same as no timeout enforced.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
http-write-timeout:
|
||||
description: The duration to wait for the response to be fully written before closing the connection. A value of 0 is the same as no timeout enforced.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
influxql-max-select-buckets:
|
||||
description: Maximum number of group-by clauses in a SELECT statement. A value of 0 is the same as unlimited.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
influxql-max-select-point:
|
||||
description: Maximum number of points that can be queried in a SELECT statement. A value of 0 is the same as unlimited.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
influxql-max-select-series:
|
||||
description: Maximum number of series that can be returned in a SELECT statement. A value of 0 is the same as unlimited.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
instance-id:
|
||||
description: Unique instance ID for this server, to avoid collisions in a replicated cluster.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
log-level:
|
||||
description: The log level to use for outputting log statements. Allowed values are debug, info, or error.
|
||||
global: True
|
||||
advanced: false
|
||||
regex: ^(info|debug|error)$
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
metrics-disabled:
|
||||
description: If true, the HTTP endpoint that exposes internal InfluxDB metrics will be inaccessible.
|
||||
forcedType: bool
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
no-tasks:
|
||||
description: If true, the task system will not process any queued tasks. Useful for troubleshooting startup problems.
|
||||
forcedType: bool
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
pprof-disabled:
|
||||
description: If true, the profiling data HTTP endpoint will be inaccessible.
|
||||
forcedType: bool
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
query-concurrency:
|
||||
description: Maximum number of queries to execute concurrently. A value of 0 is the same as unlimited.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
query-initial-memory-bytes:
|
||||
description: The initial number of bytes of memory to allocate for a new query.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
query-max-memory-bytes:
|
||||
description: The number of bytes of memory to allocate to all running queries. Should typically be the query bytes times the max concurrent queries.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
query-memory-bytes:
|
||||
description: Maximum number of bytes of memory to allocate to a query.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
query-queue-size:
|
||||
description: Maximum number of queries that can be queued at one time. If this value is reached, new queries will not be queued. A value of 0 is the same as unlimited.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
reporting-disabled:
|
||||
description: If true, prevents InfluxDB from sending telemetry updates to InfluxData's servers.
|
||||
forcedType: bool
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
secret-store:
|
||||
description: Determines the type of storage used for secrets. Allowed values are bolt or vault.
|
||||
global: True
|
||||
advanced: True
|
||||
regex: ^(bolt|vault)$
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
session-length:
|
||||
description: Number of minutes that a user login session can remain authenticated.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
session-renew-disabled:
|
||||
description: If true, user login sessions will renew after each request.
|
||||
forcedType: bool
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
sqlite-path:
|
||||
description: Path to the Sqlite3 database inside the container. This database stored user data and other information about the database.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
storage-cache-max-memory-size:
|
||||
description: Maximum number of bytes to allocate to cache data per shard. If exceeded, new data writes will be rejected.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
storage-cache-snapshot-memory-size:
|
||||
description: Number of bytes to allocate to cache snapshot data. When the cache reaches this size, it will be written to disk to increase available memory.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
storage-cache-snapshot-write-cold-duration:
|
||||
description: Duration between snapshot writes to disk when the shard data hasn't been modified.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
storage-compact-full-write-cold-duration:
|
||||
description: Duration between shard compactions when the shard data hasn't been modified.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
storage-compact-throughput-burst:
|
||||
description: Maximum throughput (number of bytes per second) that compactions be written to disk.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
storage-max-concurrent-compactions:
|
||||
description: Maximum number of concurrent compactions. A value of 0 is the same as half the available CPU processors (procs).
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
storage-max-index-log-file-size:
|
||||
description: Maximum number of bytes of a write-ahead log (WAL) file before it will be compacted into an index on disk.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
storage-no-validate-field-size:
|
||||
description: If true, incoming requests will skip the field size validation.
|
||||
forcedType: bool
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
storage-retention-check-interval:
|
||||
description: Interval between reviewing each bucket's retention policy and the age of the associated data.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
storage-series-file-max-concurrent-snapshot-compactions:
|
||||
description: Maximum number of concurrent snapshot compactions across all database partitions.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
storage-series-id-set-cache-size:
|
||||
description: Maximum size of the series cache results. Higher values may increase performance for repeated data lookups.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
storage-shard-precreator-advance-period:
|
||||
description: The duration before a successor shard group is created after the end-time has been reached.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
storage-shard-precreator-check-interval:
|
||||
description: Interval between checking if new shards should be created.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
storage-tsm-use-madv-willneed:
|
||||
description: If true, InfluxDB will manage TSM memory paging.
|
||||
forcedType: bool
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
storage-validate-keys:
|
||||
description: If true, validates incoming requests for supported characters.
|
||||
forcedType: bool
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
storage-wal-fsync-delay:
|
||||
description: Duration to wait before calling fsync. Useful for handling conflicts on slower disks.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
storage-wal-max-concurrent-writes:
|
||||
description: Maximum number of concurrent write-ahead log (WAL) writes to disk. The value of 0 is the same as CPU processors (procs) x 2.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
storage-wal-max-write-delay:
|
||||
description: Maximum duration to wait before writing the write-ahead log (WAL) to disk, when the concurrency limit has been exceeded. A value of 0 is the same as no timeout.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
storage-write-timeout:
|
||||
description: Maximum time to wait for a write-ahead log (WAL) to write to disk before aborting.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
store:
|
||||
description: The type of data store to use for HTTP resources. Allowed values are disk or memory. Memory should not be used for production Security Onion installations.
|
||||
global: True
|
||||
advanced: True
|
||||
regex: ^(disk|memory)$
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
tls-cert:
|
||||
description: The container path to the certificate to use for TLS encryption of the HTTP requests and responses.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
tls-key:
|
||||
description: The container path to the certificate key to use for TLS encryption of the HTTP requests and responses.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
tls-min-version:
|
||||
description: The minimum supported version of TLS to be enforced on all incoming HTTP requests.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
tls-strict-ciphers:
|
||||
description: If true, the allowed ciphers used with TLS connections are ECDHE_RSA_WITH_AES_256_GCM_SHA384, ECDHE_RSA_WITH_AES_256_CBC_SHA, RSA_WITH_AES_256_GCM_SHA384, or RSA_WITH_AES_256_CBC_SHA.
|
||||
forcedType: bool
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
tracing-type:
|
||||
description: The tracing format for debugging purposes. Allowed values are log or jaeger, or leave blank to disable tracing.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
ui-disabled:
|
||||
helpLink: influxdb
|
||||
ui-disabled:
|
||||
description: If true, the InfluxDB HTTP user interface will be disabled. This will prevent use of the included InfluxDB dashboard visualizations.
|
||||
forcedType: bool
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
vault-addr:
|
||||
description: Vault server address.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
vault-cacert:
|
||||
description: Path to the Vault's single certificate authority certificate file within the container.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
vault-capath:
|
||||
description: Path to the Vault's certificate authority directory within the container.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
vault-client-cert:
|
||||
description: Vault client certificate path within the container.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
vault-client-key:
|
||||
description: Vault client certificate key path within the container.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
vault-client-timeout:
|
||||
description: Duration to wait for a response from the Vault server before aborting.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
vault-max-retries:
|
||||
description: Maximum number of retries when attempting to contact the Vault server. A value of 0 is the same as disabling retries.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
vault-skip-verify:
|
||||
helpLink: influxdb
|
||||
vault-skip-verify:
|
||||
description: Skip certification validation of the Vault server.
|
||||
forcedType: bool
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
vault-tls-server-name:
|
||||
description: SNI host to specify when using TLS to connect to the Vault server.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
vault-token:
|
||||
description: Vault token used for authentication.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
buckets:
|
||||
so_short_term:
|
||||
duration:
|
||||
description: Amount of time (in seconds) to keep short term data.
|
||||
global: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
shard_duration:
|
||||
description: Amount of the time (in seconds) range covered by the shard group.
|
||||
global: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
so_long_term:
|
||||
duration:
|
||||
description: Amount of time (in seconds) to keep long term downsampled data.
|
||||
global: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
shard_duration:
|
||||
description: Amount of the time (in seconds) range covered by the shard group.
|
||||
global: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
downsample:
|
||||
so_long_term:
|
||||
resolution:
|
||||
description: Amount of time to turn into a single data point.
|
||||
global: True
|
||||
helpLink: influxdb.html
|
||||
helpLink: influxdb
|
||||
|
||||
@@ -1,27 +0,0 @@
|
||||
[{
|
||||
"apiVersion": "influxdata.com/v2alpha1",
|
||||
"kind": "CheckThreshold",
|
||||
"metadata": {
|
||||
"name": "steno-packet-loss"
|
||||
},
|
||||
"spec": {
|
||||
"description": "Triggers when the average percent of packet loss is above the defined threshold. To tune this alert, modify the value for the appropriate alert level.",
|
||||
"every": "1m",
|
||||
"name": "Stenographer Packet Loss",
|
||||
"query": "from(bucket: \"telegraf/so_short_term\")\n |\u003e range(start: v.timeRangeStart, stop: v.timeRangeStop)\n |\u003e filter(fn: (r) =\u003e r[\"_measurement\"] == \"stenodrop\")\n |\u003e filter(fn: (r) =\u003e r[\"_field\"] == \"drop\")\n |\u003e aggregateWindow(every: 1m, fn: mean, createEmpty: false)\n |\u003e yield(name: \"mean\")",
|
||||
"status": "active",
|
||||
"statusMessageTemplate": "Stenographer Packet Loss on node ${r.host} has reached the ${ r._level } threshold. The current packet loss is ${ r.drop }%.",
|
||||
"thresholds": [
|
||||
{
|
||||
"level": "CRIT",
|
||||
"type": "greater",
|
||||
"value": 5
|
||||
},
|
||||
{
|
||||
"level": "WARN",
|
||||
"type": "greater",
|
||||
"value": 3
|
||||
}
|
||||
]
|
||||
}
|
||||
}]
|
||||
File diff suppressed because one or more lines are too long
@@ -12,7 +12,7 @@
|
||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
||||
{% if sls.split('.')[0] in allowed_states %}
|
||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKER %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKERMERGED %}
|
||||
{% set KAFKANODES = salt['pillar.get']('kafka:nodes') %}
|
||||
{% set KAFKA_EXTERNAL_ACCESS = salt['pillar.get']('kafka:config:external_access:enabled', default=False) %}
|
||||
{% if 'gmd' in salt['pillar.get']('features', []) %}
|
||||
@@ -31,22 +31,22 @@ so-kafka:
|
||||
- name: so-kafka
|
||||
- networks:
|
||||
- sobridge:
|
||||
- ipv4_address: {{ DOCKER.containers['so-kafka'].ip }}
|
||||
- ipv4_address: {{ DOCKERMERGED.containers['so-kafka'].ip }}
|
||||
- user: kafka
|
||||
- environment:
|
||||
KAFKA_HEAP_OPTS: -Xmx2G -Xms1G
|
||||
KAFKA_OPTS: "-javaagent:/opt/jolokia/agents/jolokia-agent-jvm-javaagent.jar=port=8778,host={{ DOCKER.containers['so-kafka'].ip }},policyLocation=file:/opt/jolokia/jolokia.xml {%- if KAFKA_EXTERNAL_ACCESS %} -Djava.security.auth.login.config=/opt/kafka/config/kafka_server_jaas.conf {% endif -%}"
|
||||
KAFKA_OPTS: "-javaagent:/opt/jolokia/agents/jolokia-agent-jvm-javaagent.jar=port=8778,host={{ DOCKERMERGED.containers['so-kafka'].ip }},policyLocation=file:/opt/jolokia/jolokia.xml {%- if KAFKA_EXTERNAL_ACCESS %} -Djava.security.auth.login.config=/opt/kafka/config/kafka_server_jaas.conf {% endif -%}"
|
||||
- extra_hosts:
|
||||
{% for node in KAFKANODES %}
|
||||
- {{ node }}:{{ KAFKANODES[node].ip }}
|
||||
{% endfor %}
|
||||
{% if DOCKER.containers['so-kafka'].extra_hosts %}
|
||||
{% for XTRAHOST in DOCKER.containers['so-kafka'].extra_hosts %}
|
||||
{% if DOCKERMERGED.containers['so-kafka'].extra_hosts %}
|
||||
{% for XTRAHOST in DOCKERMERGED.containers['so-kafka'].extra_hosts %}
|
||||
- {{ XTRAHOST }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
- port_bindings:
|
||||
{% for BINDING in DOCKER.containers['so-kafka'].port_bindings %}
|
||||
{% for BINDING in DOCKERMERGED.containers['so-kafka'].port_bindings %}
|
||||
- {{ BINDING }}
|
||||
{% endfor %}
|
||||
- binds:
|
||||
@@ -60,6 +60,12 @@ so-kafka:
|
||||
{% if KAFKA_EXTERNAL_ACCESS %}
|
||||
- /opt/so/conf/kafka/kafka_server_jaas.conf:/opt/kafka/config/kafka_server_jaas.conf:ro
|
||||
{% endif %}
|
||||
{% if DOCKERMERGED.containers['so-kafka'].ulimits %}
|
||||
- ulimits:
|
||||
{% for ULIMIT in DOCKERMERGED.containers['so-kafka'].ulimits %}
|
||||
- {{ ULIMIT.name }}={{ ULIMIT.soft }}:{{ ULIMIT.hard }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
- watch:
|
||||
{% for sc in ['server', 'client'] %}
|
||||
- file: kafka_kraft_{{sc}}_properties
|
||||
|
||||
@@ -1,257 +1,258 @@
|
||||
kafka:
|
||||
enabled:
|
||||
description: Set to True to enable Kafka. To avoid grid problems, do not enable Kafka until the related configuration is in place. Requires a valid Security Onion license key.
|
||||
helpLink: kafka.html
|
||||
forcedType: bool
|
||||
helpLink: kafka
|
||||
cluster_id:
|
||||
description: The ID of the Kafka cluster.
|
||||
readonly: True
|
||||
advanced: True
|
||||
sensitive: True
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
controllers:
|
||||
description: A comma-separated list of hostnames that will act as Kafka controllers. These hosts will be responsible for managing the Kafka cluster. Note that only manager and receiver nodes are eligible to run Kafka. This configuration needs to be set before enabling Kafka. Failure to do so may result in Kafka topics becoming unavailable requiring manual intervention to restore functionality or reset Kafka, either of which can result in data loss.
|
||||
forcedType: string
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
reset:
|
||||
description: Disable and reset the Kafka cluster. This will remove all Kafka data including logs that may have not yet been ingested into Elasticsearch and reverts the grid to using REDIS as the global pipeline. This is useful when testing different Kafka configurations such as rearranging Kafka brokers / controllers allowing you to reset the cluster rather than manually fixing any issues arising from attempting to reassign a Kafka broker into a controller. Enter 'YES_RESET_KAFKA' and submit to disable and reset Kafka. Make any configuration changes required and re-enable Kafka when ready. This action CANNOT be reversed.
|
||||
advanced: True
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
logstash:
|
||||
description: By default logstash is disabled when Kafka is enabled. This option allows you to specify any hosts you would like to re-enable logstash on alongside Kafka.
|
||||
forcedType: "[]string"
|
||||
multiline: True
|
||||
advanced: True
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
config:
|
||||
password:
|
||||
description: The password used for the Kafka certificates.
|
||||
readonly: True
|
||||
sensitive: True
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
trustpass:
|
||||
description: The password used for the Kafka truststore.
|
||||
readonly: True
|
||||
sensitive: True
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
broker:
|
||||
auto_x_create_x_topics_x_enable:
|
||||
description: Enable the auto creation of topics.
|
||||
title: auto.create.topics.enable
|
||||
forcedType: bool
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
default_x_replication_x_factor:
|
||||
description: The default replication factor for automatically created topics. This value must be less than the amount of brokers in the cluster. Hosts specified in controllers should not be counted towards total broker count.
|
||||
title: default.replication.factor
|
||||
forcedType: int
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
inter_x_broker_x_listener_x_name:
|
||||
description: The name of the listener used for inter-broker communication.
|
||||
title: inter.broker.listener.name
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
listeners:
|
||||
description: Set of URIs that is listened on and the listener names in a comma-seperated list.
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
listener_x_security_x_protocol_x_map:
|
||||
description: Comma-seperated mapping of listener name and security protocols.
|
||||
title: listener.security.protocol.map
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
log_x_dirs:
|
||||
description: Where Kafka logs are stored within the Docker container.
|
||||
title: log.dirs
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
log_x_retention_x_check_x_interval_x_ms:
|
||||
description: Frequency at which log files are checked if they are qualified for deletion.
|
||||
title: log.retention.check.interval.ms
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
log_x_retention_x_hours:
|
||||
description: How long, in hours, a log file is kept.
|
||||
title: log.retention.hours
|
||||
forcedType: int
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
log_x_segment_x_bytes:
|
||||
description: The maximum allowable size for a log file.
|
||||
title: log.segment.bytes
|
||||
forcedType: int
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
num_x_io_x_threads:
|
||||
description: The number of threads used by Kafka.
|
||||
title: num.io.threads
|
||||
forcedType: int
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
num_x_network_x_threads:
|
||||
description: The number of threads used for network communication.
|
||||
title: num.network.threads
|
||||
forcedType: int
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
num_x_partitions:
|
||||
description: The number of log partitions assigned per topic.
|
||||
title: num.partitions
|
||||
forcedType: int
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
num_x_recovery_x_threads_x_per_x_data_x_dir:
|
||||
description: The number of threads used for log recuperation at startup and purging at shutdown. This ammount of threads is used per data directory.
|
||||
title: num.recovery.threads.per.data.dir
|
||||
forcedType: int
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
offsets_x_topic_x_replication_x_factor:
|
||||
description: The offsets topic replication factor.
|
||||
title: offsets.topic.replication.factor
|
||||
forcedType: int
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
process_x_roles:
|
||||
description: The role performed by Kafka brokers.
|
||||
title: process.roles
|
||||
readonly: True
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
socket_x_receive_x_buffer_x_bytes:
|
||||
description: Size, in bytes of the SO_RCVBUF buffer. A value of -1 will use the OS default.
|
||||
title: socket.receive.buffer.bytes
|
||||
#forcedType: int - soc needs to allow -1 as an int before we can use this
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
socket_x_request_x_max_x_bytes:
|
||||
description: The maximum bytes allowed for a request to the socket.
|
||||
title: socket.request.max.bytes
|
||||
forcedType: int
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
socket_x_send_x_buffer_x_bytes:
|
||||
description: Size, in bytes of the SO_SNDBUF buffer. A value of -1 will use the OS default.
|
||||
title: socket.send.buffer.byte
|
||||
#forcedType: int - soc needs to allow -1 as an int before we can use this
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
ssl_x_keystore_x_location:
|
||||
description: The key store file location within the Docker container.
|
||||
title: ssl.keystore.location
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
ssl_x_keystore_x_password:
|
||||
description: The key store file password. Invalid for PEM format.
|
||||
title: ssl.keystore.password
|
||||
sensitive: True
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
ssl_x_keystore_x_type:
|
||||
description: The key store file format.
|
||||
title: ssl.keystore.type
|
||||
regex: ^(JKS|PKCS12|PEM)$
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
ssl_x_truststore_x_location:
|
||||
description: The trust store file location within the Docker container.
|
||||
title: ssl.truststore.location
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
ssl_x_truststore_x_type:
|
||||
description: The trust store file format.
|
||||
title: ssl.truststore.type
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
ssl_x_truststore_x_password:
|
||||
description: The trust store file password. If null, the trust store file is still use, but integrity checking is disabled. Invalid for PEM format.
|
||||
title: ssl.truststore.password
|
||||
sensitive: True
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
transaction_x_state_x_log_x_min_x_isr:
|
||||
description: Overrides min.insync.replicas for the transaction topic. When a producer configures acks to "all" (or "-1"), this setting determines the minimum number of replicas required to acknowledge a write as successful. Failure to meet this minimum triggers an exception (either NotEnoughReplicas or NotEnoughReplicasAfterAppend). When used in conjunction, min.insync.replicas and acks enable stronger durability guarantees. For instance, creating a topic with a replication factor of 3, setting min.insync.replicas to 2, and using acks of "all" ensures that the producer raises an exception if a majority of replicas fail to receive a write.
|
||||
title: transaction.state.log.min.isr
|
||||
forcedType: int
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
transaction_x_state_x_log_x_replication_x_factor:
|
||||
description: Set the replication factor higher for the transaction topic to ensure availability. Internal topic creation will not proceed until the cluster size satisfies this replication factor prerequisite.
|
||||
title: transaction.state.log.replication.factor
|
||||
forcedType: int
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
client:
|
||||
security_x_protocol:
|
||||
description: 'Broker communication protocol. Options are: SASL_SSL, PLAINTEXT, SSL, SASL_PLAINTEXT'
|
||||
title: security.protocol
|
||||
regex: ^(SASL_SSL|PLAINTEXT|SSL|SASL_PLAINTEXT)
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
ssl_x_keystore_x_location:
|
||||
description: The key store file location within the Docker container.
|
||||
title: ssl.keystore.location
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
ssl_x_keystore_x_password:
|
||||
description: The key store file password. Invalid for PEM format.
|
||||
title: ssl.keystore.password
|
||||
sensitive: True
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
ssl_x_keystore_x_type:
|
||||
description: The key store file format.
|
||||
title: ssl.keystore.type
|
||||
regex: ^(JKS|PKCS12|PEM)$
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
ssl_x_truststore_x_location:
|
||||
description: The trust store file location within the Docker container.
|
||||
title: ssl.truststore.location
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
ssl_x_truststore_x_type:
|
||||
description: The trust store file format.
|
||||
title: ssl.truststore.type
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
ssl_x_truststore_x_password:
|
||||
description: The trust store file password. If null, the trust store file is still use, but integrity checking is disabled. Invalid for PEM format.
|
||||
title: ssl.truststore.password
|
||||
sensitive: True
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
controller:
|
||||
controller_x_listener_x_names:
|
||||
description: Set listeners used by the controller in a comma-seperated list.
|
||||
title: controller.listener.names
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
listeners:
|
||||
description: Set of URIs that is listened on and the listener names in a comma-seperated list.
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
listener_x_security_x_protocol_x_map:
|
||||
description: Comma-seperated mapping of listener name and security protocols.
|
||||
title: listener.security.protocol.map
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
log_x_dirs:
|
||||
description: Where Kafka logs are stored within the Docker container.
|
||||
title: log.dirs
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
log_x_retention_x_check_x_interval_x_ms:
|
||||
description: Frequency at which log files are checked if they are qualified for deletion.
|
||||
title: log.retention.check.interval.ms
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
log_x_retention_x_hours:
|
||||
description: How long, in hours, a log file is kept.
|
||||
title: log.retention.hours
|
||||
forcedType: int
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
log_x_segment_x_bytes:
|
||||
description: The maximum allowable size for a log file.
|
||||
title: log.segment.bytes
|
||||
forcedType: int
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
process_x_roles:
|
||||
description: The role performed by controller node.
|
||||
title: process.roles
|
||||
readonly: True
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
external_access:
|
||||
enabled:
|
||||
description: Enables or disables access to Kafka topics using user/password authentication. Used for producing / consuming messages via an external client.
|
||||
forcedType: bool
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
listeners:
|
||||
description: Set of URIs that is listened on and the listener names in a comma-seperated list.
|
||||
title: listeners
|
||||
readonly: True
|
||||
advanced: True
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
listener_x_security_x_protocol_x_map:
|
||||
description: External listener name and mapped security protocol.
|
||||
title: listener.security.protocol.map
|
||||
readonly: True
|
||||
advanced: True
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
sasl_x_enabled_x_mechanisms:
|
||||
description: SASL/PLAIN is a simple username/password authentication mechanism, used with TLS to implement secure authentication.
|
||||
title: sasl.enabled.mechanisms
|
||||
readonly: True
|
||||
advanced: True
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
sasl_x_mechanism_x_inter_x_broker_x_protocol:
|
||||
description: SASL mechanism used for inter-broker communication
|
||||
title: sasl.mechanism.inter.broker.protocol
|
||||
readonly: True
|
||||
advanced: True
|
||||
helpLink: kafka.html
|
||||
helpLink: kafka
|
||||
remote_users:
|
||||
user01: &remote_user
|
||||
username:
|
||||
|
||||
@@ -5,7 +5,7 @@
|
||||
|
||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
||||
{% if sls.split('.')[0] in allowed_states %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKER %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKERMERGED %}
|
||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
|
||||
include:
|
||||
@@ -20,20 +20,20 @@ so-kibana:
|
||||
- user: kibana
|
||||
- networks:
|
||||
- sobridge:
|
||||
- ipv4_address: {{ DOCKER.containers['so-kibana'].ip }}
|
||||
- ipv4_address: {{ DOCKERMERGED.containers['so-kibana'].ip }}
|
||||
- environment:
|
||||
- ELASTICSEARCH_HOST={{ GLOBALS.manager }}
|
||||
- ELASTICSEARCH_PORT=9200
|
||||
- MANAGER={{ GLOBALS.manager }}
|
||||
{% if DOCKER.containers['so-kibana'].extra_env %}
|
||||
{% for XTRAENV in DOCKER.containers['so-kibana'].extra_env %}
|
||||
{% if DOCKERMERGED.containers['so-kibana'].extra_env %}
|
||||
{% for XTRAENV in DOCKERMERGED.containers['so-kibana'].extra_env %}
|
||||
- {{ XTRAENV }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
- extra_hosts:
|
||||
- {{ GLOBALS.manager }}:{{ GLOBALS.manager_ip }}
|
||||
{% if DOCKER.containers['so-kibana'].extra_hosts %}
|
||||
{% for XTRAHOST in DOCKER.containers['so-kibana'].extra_hosts %}
|
||||
{% if DOCKERMERGED.containers['so-kibana'].extra_hosts %}
|
||||
{% for XTRAHOST in DOCKERMERGED.containers['so-kibana'].extra_hosts %}
|
||||
- {{ XTRAHOST }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
@@ -42,15 +42,21 @@ so-kibana:
|
||||
- /opt/so/log/kibana:/var/log/kibana:rw
|
||||
- /opt/so/conf/kibana/customdashboards:/usr/share/kibana/custdashboards:ro
|
||||
- /sys/fs/cgroup:/sys/fs/cgroup:ro
|
||||
{% if DOCKER.containers['so-kibana'].custom_bind_mounts %}
|
||||
{% for BIND in DOCKER.containers['so-kibana'].custom_bind_mounts %}
|
||||
{% if DOCKERMERGED.containers['so-kibana'].custom_bind_mounts %}
|
||||
{% for BIND in DOCKERMERGED.containers['so-kibana'].custom_bind_mounts %}
|
||||
- {{ BIND }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
- port_bindings:
|
||||
{% for BINDING in DOCKER.containers['so-kibana'].port_bindings %}
|
||||
{% for BINDING in DOCKERMERGED.containers['so-kibana'].port_bindings %}
|
||||
- {{ BINDING }}
|
||||
{% endfor %}
|
||||
{% if DOCKERMERGED.containers['so-kibana'].ulimits %}
|
||||
- ulimits:
|
||||
{% for ULIMIT in DOCKERMERGED.containers['so-kibana'].ulimits %}
|
||||
- {{ ULIMIT.name }}={{ ULIMIT.soft }}:{{ ULIMIT.hard }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
- watch:
|
||||
- file: kibanaconfig
|
||||
|
||||
|
||||
@@ -5,7 +5,6 @@
|
||||
|
||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
{% import_yaml 'kibana/defaults.yaml' as KIBANADEFAULTS with context %}
|
||||
{% set HIGHLANDER = salt['pillar.get']('global:highlander', False) %}
|
||||
|
||||
{% do KIBANADEFAULTS.kibana.config.server.update({'publicBaseUrl': 'https://' ~ GLOBALS.url_base ~ '/kibana'}) %}
|
||||
{% do KIBANADEFAULTS.kibana.config.elasticsearch.update({'hosts': ['https://' ~ GLOBALS.manager ~ ':9200']}) %}
|
||||
|
||||
@@ -3,7 +3,6 @@
|
||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||
# Elastic License 2.0.
|
||||
|
||||
{% set HIGHLANDER = salt['pillar.get']('global:highlander', False) %}
|
||||
include:
|
||||
- kibana.enabled
|
||||
|
||||
@@ -29,27 +28,3 @@ so-kibana-dashboard-load:
|
||||
- require:
|
||||
- sls: kibana.enabled
|
||||
- file: dashboard_saved_objects_template
|
||||
{%- if HIGHLANDER %}
|
||||
dashboard_saved_objects_template_hl:
|
||||
file.managed:
|
||||
- name: /opt/so/conf/kibana/hl.ndjson.template
|
||||
- source: salt://kibana/files/hl.ndjson
|
||||
- user: 932
|
||||
- group: 939
|
||||
- show_changes: False
|
||||
|
||||
dashboard_saved_objects_hl_changes:
|
||||
file.absent:
|
||||
- names:
|
||||
- /opt/so/state/kibana_hl.txt
|
||||
- onchanges:
|
||||
- file: dashboard_saved_objects_template_hl
|
||||
|
||||
so-kibana-dashboard-load_hl:
|
||||
cmd.run:
|
||||
- name: /usr/sbin/so-kibana-config-load -i /opt/so/conf/kibana/hl.ndjson.template
|
||||
- cwd: /opt/so
|
||||
- require:
|
||||
- sls: kibana.enabled
|
||||
- file: dashboard_saved_objects_template_hl
|
||||
{%- endif %}
|
||||
|
||||
@@ -1,10 +1,46 @@
|
||||
kibana:
|
||||
enabled:
|
||||
enabled:
|
||||
description: Enables or disables the Kibana front-end interface to Elasticsearch. Due to Kibana being used for loading certain configuration details in Elasticsearch, this process should remain enabled. WARNING - Disabling the process is unsupported, and will cause unexpected results.
|
||||
helpLink: kibana.html
|
||||
forcedType: bool
|
||||
helpLink: kibana
|
||||
config:
|
||||
server:
|
||||
rewriteBasePath:
|
||||
description: Specifies whether Kibana should rewrite requests that are prefixed with the server basePath.
|
||||
forcedType: bool
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: kibana
|
||||
elasticsearch:
|
||||
requestTimeout:
|
||||
description: The length of time before the request reaches timeout.
|
||||
global: True
|
||||
helpLink: kibana.html
|
||||
helpLink: kibana
|
||||
telemetry:
|
||||
enabled:
|
||||
description: Enables or disables telemetry data collection in Kibana.
|
||||
forcedType: bool
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: kibana
|
||||
xpack:
|
||||
security:
|
||||
secureCookies:
|
||||
description: Sets the secure flag on session cookies. Cookies are only sent over HTTPS when enabled.
|
||||
forcedType: bool
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: kibana
|
||||
showInsecureClusterWarning:
|
||||
description: Shows a warning in Kibana when the cluster does not have security enabled.
|
||||
forcedType: bool
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: kibana
|
||||
apm:
|
||||
enabled:
|
||||
description: Enables or disables the APM agent in Kibana.
|
||||
forcedType: bool
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: kibana
|
||||
|
||||
@@ -1,6 +1,5 @@
|
||||
#!/bin/bash
|
||||
. /usr/sbin/so-common
|
||||
{% set HIGHLANDER = salt['pillar.get']('global:highlander', False) %}
|
||||
wait_for_web_response "http://localhost:5601/api/spaces/space/default" "default" 300 "curl -K /opt/so/conf/elasticsearch/curl.config"
|
||||
## This hackery will be removed if using Elastic Auth ##
|
||||
|
||||
@@ -9,10 +8,6 @@ SESSIONCOOKIE=$(curl -K /opt/so/conf/elasticsearch/curl.config -c - -X GET http:
|
||||
|
||||
# Disable certain Features from showing up in the Kibana UI
|
||||
echo
|
||||
echo "Setting up default Space:"
|
||||
{% if HIGHLANDER %}
|
||||
curl -K /opt/so/conf/elasticsearch/curl.config -b "sid=$SESSIONCOOKIE" -L -X PUT "localhost:5601/api/spaces/space/default" -H 'kbn-xsrf: true' -H 'Content-Type: application/json' -d' {"id":"default","name":"Default","disabledFeatures":["enterpriseSearch"]} ' >> /opt/so/log/kibana/misc.log
|
||||
{% else %}
|
||||
echo "Setting up default Kibana Space:"
|
||||
curl -K /opt/so/conf/elasticsearch/curl.config -b "sid=$SESSIONCOOKIE" -L -X PUT "localhost:5601/api/spaces/space/default" -H 'kbn-xsrf: true' -H 'Content-Type: application/json' -d' {"id":"default","name":"Default","disabledFeatures":["ml","enterpriseSearch","logs","infrastructure","apm","uptime","monitoring","stackAlerts","actions","securitySolutionCasesV3","inventory","dataQuality","searchSynonyms","enterpriseSearchApplications","enterpriseSearchAnalytics","securitySolutionTimeline","securitySolutionNotes","entityManager"]} ' >> /opt/so/log/kibana/misc.log
|
||||
{% endif %}
|
||||
echo
|
||||
|
||||
@@ -5,7 +5,7 @@
|
||||
|
||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
||||
{% if sls.split('.')[0] in allowed_states %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKER %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKERMERGED %}
|
||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
|
||||
include:
|
||||
@@ -19,32 +19,38 @@ so-kratos:
|
||||
- name: so-kratos
|
||||
- networks:
|
||||
- sobridge:
|
||||
- ipv4_address: {{ DOCKER.containers['so-kratos'].ip }}
|
||||
- ipv4_address: {{ DOCKERMERGED.containers['so-kratos'].ip }}
|
||||
- binds:
|
||||
- /opt/so/conf/kratos/:/kratos-conf:ro
|
||||
- /opt/so/log/kratos/:/kratos-log:rw
|
||||
- /nsm/kratos/db:/kratos-data:rw
|
||||
{% if DOCKER.containers['so-kratos'].custom_bind_mounts %}
|
||||
{% for BIND in DOCKER.containers['so-kratos'].custom_bind_mounts %}
|
||||
{% if DOCKERMERGED.containers['so-kratos'].custom_bind_mounts %}
|
||||
{% for BIND in DOCKERMERGED.containers['so-kratos'].custom_bind_mounts %}
|
||||
- {{ BIND }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
- port_bindings:
|
||||
{% for BINDING in DOCKER.containers['so-kratos'].port_bindings %}
|
||||
{% for BINDING in DOCKERMERGED.containers['so-kratos'].port_bindings %}
|
||||
- {{ BINDING }}
|
||||
{% endfor %}
|
||||
{% if DOCKER.containers['so-kratos'].extra_hosts %}
|
||||
{% if DOCKERMERGED.containers['so-kratos'].extra_hosts %}
|
||||
- extra_hosts:
|
||||
{% for XTRAHOST in DOCKER.containers['so-kratos'].extra_hosts %}
|
||||
{% for XTRAHOST in DOCKERMERGED.containers['so-kratos'].extra_hosts %}
|
||||
- {{ XTRAHOST }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
{% if DOCKER.containers['so-kratos'].extra_env %}
|
||||
{% if DOCKERMERGED.containers['so-kratos'].extra_env %}
|
||||
- environment:
|
||||
{% for XTRAENV in DOCKER.containers['so-kratos'].extra_env %}
|
||||
{% for XTRAENV in DOCKERMERGED.containers['so-kratos'].extra_env %}
|
||||
- {{ XTRAENV }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
{% if DOCKERMERGED.containers['so-kratos'].ulimits %}
|
||||
- ulimits:
|
||||
{% for ULIMIT in DOCKERMERGED.containers['so-kratos'].ulimits %}
|
||||
- {{ ULIMIT.name }}={{ ULIMIT.soft }}:{{ ULIMIT.hard }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
- restart_policy: unless-stopped
|
||||
- watch:
|
||||
- file: kratosschema
|
||||
|
||||
@@ -1,88 +1,91 @@
|
||||
kratos:
|
||||
enabled:
|
||||
description: Enables or disables the Kratos authentication system. WARNING - Disabling this process will cause the grid to malfunction. Re-enabling this setting will require manual effort via SSH.
|
||||
forcedType: bool
|
||||
advanced: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
|
||||
oidc:
|
||||
enabled:
|
||||
enabled:
|
||||
description: Set to True to enable OIDC / Single Sign-On (SSO) to SOC. Requires a valid Security Onion license key.
|
||||
forcedType: bool
|
||||
global: True
|
||||
helpLink: oidc.html
|
||||
helpLink: oidc
|
||||
config:
|
||||
id:
|
||||
description: Customize the OIDC provider name. This name appears on the login page. Required. It is strongly recommended to leave this to the default value, unless you are aware of the other configuration pieces that will be affected by changing it.
|
||||
global: True
|
||||
forcedType: string
|
||||
helpLink: oidc.html
|
||||
helpLink: oidc
|
||||
provider:
|
||||
description: "Specify the provider type. Required. Valid values are: auth0, generic, github, google, microsoft"
|
||||
global: True
|
||||
forcedType: string
|
||||
regex: "auth0|generic|github|google|microsoft"
|
||||
regexFailureMessage: "Valid values are: auth0, generic, github, google, microsoft"
|
||||
helpLink: oidc.html
|
||||
helpLink: oidc
|
||||
client_id:
|
||||
description: Specify the client ID, also referenced as the application ID. Required.
|
||||
global: True
|
||||
forcedType: string
|
||||
helpLink: oidc.html
|
||||
helpLink: oidc
|
||||
client_secret:
|
||||
description: Specify the client secret. Required.
|
||||
global: True
|
||||
forcedType: string
|
||||
helpLink: oidc.html
|
||||
helpLink: oidc
|
||||
microsoft_tenant:
|
||||
description: Specify the Microsoft Active Directory Tenant ID. Required when provider is 'microsoft'.
|
||||
global: True
|
||||
forcedType: string
|
||||
helpLink: oidc.html
|
||||
helpLink: oidc
|
||||
subject_source:
|
||||
description: The source of the subject identifier. Typically 'userinfo'. Only used when provider is 'microsoft'.
|
||||
global: True
|
||||
forcedType: string
|
||||
regex: me|userinfo
|
||||
regexFailureMessage: "Valid values are: me, userinfo"
|
||||
helpLink: oidc.html
|
||||
helpLink: oidc
|
||||
auth_url:
|
||||
description: Provider's auth URL. Required when provider is 'generic'.
|
||||
global: True
|
||||
forcedType: string
|
||||
helpLink: oidc.html
|
||||
helpLink: oidc
|
||||
issuer_url:
|
||||
description: Provider's issuer URL. Required when provider is 'auth0' or 'generic'.
|
||||
global: True
|
||||
forcedType: string
|
||||
helpLink: oidc.html
|
||||
helpLink: oidc
|
||||
mapper_url:
|
||||
description: A file path or URL in Jsonnet format, used to map OIDC claims to the Kratos schema. Defaults to an included file that maps the email claim. Note that the contents of the included file can be customized via the "OIDC Claims Mapping" setting.
|
||||
advanced: True
|
||||
global: True
|
||||
forcedType: string
|
||||
helpLink: oidc.html
|
||||
helpLink: oidc
|
||||
token_url:
|
||||
description: Provider's token URL. Required when provider is 'generic'.
|
||||
global: True
|
||||
forcedType: string
|
||||
helpLink: oidc.html
|
||||
helpLink: oidc
|
||||
scope:
|
||||
description: List of scoped data categories to request in the authentication response. Typically 'email' and 'profile' are the minimum required scopes. However, GitHub requires `user:email', instead and Auth0 requires 'profile', 'email', and 'openid'.
|
||||
global: True
|
||||
forcedType: "[]string"
|
||||
helpLink: oidc.html
|
||||
helpLink: oidc
|
||||
pkce:
|
||||
description: Set to 'force' if the OIDC provider does not support auto-detection of PKCE, but does support PKCE. Set to `never` to disable PKCE. The default setting automatically attempts to detect if PKCE is supported. The provider's `well-known/openid-configuration` JSON response must contain the `S256` algorithm within the `code_challenge_methods_supported` list in order for the auto-detection to correctly detect PKCE is supported.
|
||||
global: True
|
||||
forcedType: string
|
||||
helpLink: oidc.html
|
||||
helpLink: oidc
|
||||
requested_claims:
|
||||
id_token:
|
||||
email:
|
||||
essential:
|
||||
description: Specifies whether the email claim is necessary. Typically leave this value set to true.
|
||||
forcedType: bool
|
||||
advanced: True
|
||||
global: True
|
||||
helpLink: oidc.html
|
||||
helpLink: oidc
|
||||
files:
|
||||
oidc__jsonnet:
|
||||
title: OIDC Claims Mapping
|
||||
@@ -90,164 +93,169 @@ kratos:
|
||||
advanced: True
|
||||
file: True
|
||||
global: True
|
||||
helpLink: oidc.html
|
||||
helpLink: oidc
|
||||
|
||||
config:
|
||||
session:
|
||||
lifespan:
|
||||
description: Defines the length of a login session.
|
||||
global: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
whoami:
|
||||
required_aal:
|
||||
description: Sets the Authenticator Assurance Level. Leave as default to ensure proper security protections remain in place.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
selfservice:
|
||||
methods:
|
||||
password:
|
||||
enabled:
|
||||
enabled:
|
||||
description: Set to True to enable traditional password authentication to SOC. Typically set to true, except when exclusively using OIDC authentication. Some external tool interfaces may not be accessible if local password authentication is disabled.
|
||||
forcedType: bool
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: oidc.html
|
||||
helpLink: oidc
|
||||
config:
|
||||
haveibeenpwned_enabled:
|
||||
description: Set to True to check if a newly chosen password has ever been found in a published list of previously-compromised passwords. Requires outbound Internet connectivity when enabled.
|
||||
forcedType: bool
|
||||
global: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
totp:
|
||||
enabled:
|
||||
enabled:
|
||||
description: Set to True to enable Time-based One-Time Password (TOTP) multi-factor authentication (MFA) to SOC. Enable to ensure proper security protections remain in place. Be aware that disabling this setting, after users have already setup TOTP, may prevent users from logging in.
|
||||
forcedType: bool
|
||||
global: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
config:
|
||||
issuer:
|
||||
description: The name to show in the MFA authenticator app. Useful for differentiating between installations that share the same user email address.
|
||||
global: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
webauthn:
|
||||
enabled:
|
||||
description: Set to True to enable Security Keys (WebAuthn / PassKeys) for passwordless or multi-factor authentication (MFA) SOC logins. Security Keys are a Public-Key Infrastructure (PKI) based authentication method, typically involving biometric hardware devices, such as laptop fingerprint scanners and USB hardware keys. Be aware that disabling this setting, after users have already setup their accounts with Security Keys, may prevent users from logging in.
|
||||
forcedType: bool
|
||||
global: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
config:
|
||||
passwordless:
|
||||
passwordless:
|
||||
description: Set to True to utilize Security Keys (WebAuthn / PassKeys) for passwordless logins. Set to false to utilize Security Keys as a multi-factor authentication (MFA) method supplementing password logins. Be aware that changing this value, after users have already setup their accounts with the previous value, may prevent users from logging in.
|
||||
forcedType: bool
|
||||
global: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
rp:
|
||||
id:
|
||||
description: The internal identification used for registering new Security Keys. Leave as default to ensure Security Keys function properly.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
origin:
|
||||
description: The URL used to login to SOC. Leave as default to ensure Security Keys function properly.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
display_name:
|
||||
description: The name assigned to the security key. Note that URL_BASE is replaced with the hostname or IP address used to login to SOC, to help distinguish multiple Security Onion installations.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
|
||||
flows:
|
||||
settings:
|
||||
privileged_session_max_age:
|
||||
description: The length of time after a successful authentication for a user's session to remain elevated to a privileged session. Privileged sessions are able to change passwords and other security settings for that user. If a session is no longer privileged then the user is redirected to the login form in order to confirm the security change.
|
||||
global: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
ui_url:
|
||||
description: User accessible URL containing the user self-service profile and security settings. Leave as default to ensure proper operation.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
required_aal:
|
||||
description: Sets the Authenticator Assurance Level for accessing user self-service profile and security settings. Leave as default to ensure proper security enforcement remains in place.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
verification:
|
||||
ui_url:
|
||||
description: User accessible URL containing the Security Onion login page. Leave as default to ensure proper operation.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
login:
|
||||
ui_url:
|
||||
description: User accessible URL containing the Security Onion login page. Leave as default to ensure proper operation.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
lifespan:
|
||||
description: Defines the duration that a login form will remain valid.
|
||||
global: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
error:
|
||||
ui_url:
|
||||
description: User accessible URL containing the Security Onion login page. Leave as default to ensure proper operation.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
registration:
|
||||
ui_url:
|
||||
description: User accessible URL containing the Security Onion login page. Leave as default to ensure proper operation.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
default_browser_return_url:
|
||||
description: Security Onion Console landing page URL. Leave as default to ensure proper operation.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
allowed_return_urls:
|
||||
description: Internal redirect URL. Leave as default to ensure proper operation.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
log:
|
||||
level:
|
||||
description: Log level to use for Kratos logs.
|
||||
global: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
format:
|
||||
description: Log output format for Kratos logs.
|
||||
global: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
secrets:
|
||||
default:
|
||||
description: Secret key used for protecting session cookie data. Generated during installation.
|
||||
global: True
|
||||
sensitive: True
|
||||
advanced: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
serve:
|
||||
public:
|
||||
base_url:
|
||||
description: User accessible URL for authenticating to Kratos. Leave as default for proper operation.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
admin:
|
||||
base_url:
|
||||
description: User accessible URL for accessing Kratos administration API. Leave as default for proper operation.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
hashers:
|
||||
bcrypt:
|
||||
cost:
|
||||
description: Bcrypt hashing algorithm cost. Higher values consume more CPU and take longer to complete. Actual cost is computed as 2^X where X is the value in this setting.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
courier:
|
||||
smtp:
|
||||
connection_uri:
|
||||
description: SMTPS URL for sending outbound account-related emails. Not utilized with the standard Security Onion installation.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: kratos.html
|
||||
helpLink: kratos
|
||||
|
||||
@@ -180,16 +180,6 @@ logrotate:
|
||||
- extension .log
|
||||
- dateext
|
||||
- dateyesterday
|
||||
/opt/so/log/stenographer/*_x_log:
|
||||
- daily
|
||||
- rotate 14
|
||||
- missingok
|
||||
- copytruncate
|
||||
- compress
|
||||
- create
|
||||
- extension .log
|
||||
- dateext
|
||||
- dateyesterday
|
||||
/opt/so/log/salt/so-salt-minion-check:
|
||||
- daily
|
||||
- rotate 14
|
||||
|
||||
@@ -112,13 +112,6 @@ logrotate:
|
||||
multiline: True
|
||||
global: True
|
||||
forcedType: "[]string"
|
||||
"/opt/so/log/stenographer/*_x_log":
|
||||
description: List of logrotate options for this file.
|
||||
title: /opt/so/log/stenographer/*.log
|
||||
advanced: True
|
||||
multiline: True
|
||||
global: True
|
||||
forcedType: "[]string"
|
||||
"/opt/so/log/salt/so-salt-minion-check":
|
||||
description: List of logrotate options for this file.
|
||||
title: /opt/so/log/salt/so-salt-minion-check
|
||||
|
||||
@@ -36,10 +36,6 @@ logstash:
|
||||
- gid: 931
|
||||
- home: /opt/so/conf/logstash
|
||||
|
||||
lslibdir:
|
||||
file.absent:
|
||||
- name: /opt/so/conf/logstash/lib
|
||||
|
||||
logstash_sbin:
|
||||
file.recurse:
|
||||
- name: /usr/sbin
|
||||
|
||||
@@ -6,7 +6,7 @@
|
||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
||||
{% if sls.split('.')[0] in allowed_states %}
|
||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKER %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKERMERGED %}
|
||||
{% from 'logstash/map.jinja' import LOGSTASH_MERGED %}
|
||||
{% from 'logstash/map.jinja' import LOGSTASH_NODES %}
|
||||
{% set lsheap = LOGSTASH_MERGED.settings.lsheap %}
|
||||
@@ -32,7 +32,7 @@ so-logstash:
|
||||
- name: so-logstash
|
||||
- networks:
|
||||
- sobridge:
|
||||
- ipv4_address: {{ DOCKER.containers['so-logstash'].ip }}
|
||||
- ipv4_address: {{ DOCKERMERGED.containers['so-logstash'].ip }}
|
||||
- user: logstash
|
||||
- extra_hosts:
|
||||
{% for node in LOGSTASH_NODES %}
|
||||
@@ -40,20 +40,20 @@ so-logstash:
|
||||
- {{hostname}}:{{ip}}
|
||||
{% endfor %}
|
||||
{% endfor %}
|
||||
{% if DOCKER.containers['so-logstash'].extra_hosts %}
|
||||
{% for XTRAHOST in DOCKER.containers['so-logstash'].extra_hosts %}
|
||||
{% if DOCKERMERGED.containers['so-logstash'].extra_hosts %}
|
||||
{% for XTRAHOST in DOCKERMERGED.containers['so-logstash'].extra_hosts %}
|
||||
- {{ XTRAHOST }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
- environment:
|
||||
- LS_JAVA_OPTS=-Xms{{ lsheap }} -Xmx{{ lsheap }}
|
||||
{% if DOCKER.containers['so-logstash'].extra_env %}
|
||||
{% for XTRAENV in DOCKER.containers['so-logstash'].extra_env %}
|
||||
{% if DOCKERMERGED.containers['so-logstash'].extra_env %}
|
||||
{% for XTRAENV in DOCKERMERGED.containers['so-logstash'].extra_env %}
|
||||
- {{ XTRAENV }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
- port_bindings:
|
||||
{% for BINDING in DOCKER.containers['so-logstash'].port_bindings %}
|
||||
{% for BINDING in DOCKERMERGED.containers['so-logstash'].port_bindings %}
|
||||
- {{ BINDING }}
|
||||
{% endfor %}
|
||||
- binds:
|
||||
@@ -91,11 +91,17 @@ so-logstash:
|
||||
- /opt/so/log/fleet/:/osquery/logs:ro
|
||||
- /opt/so/log/strelka:/strelka:ro
|
||||
{% endif %}
|
||||
{% if DOCKER.containers['so-logstash'].custom_bind_mounts %}
|
||||
{% for BIND in DOCKER.containers['so-logstash'].custom_bind_mounts %}
|
||||
{% if DOCKERMERGED.containers['so-logstash'].custom_bind_mounts %}
|
||||
{% for BIND in DOCKERMERGED.containers['so-logstash'].custom_bind_mounts %}
|
||||
- {{ BIND }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
{% if DOCKERMERGED.containers['so-logstash'].ulimits %}
|
||||
- ulimits:
|
||||
{% for ULIMIT in DOCKERMERGED.containers['so-logstash'].ulimits %}
|
||||
- {{ ULIMIT.name }}={{ ULIMIT.soft }}:{{ ULIMIT.hard }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
- watch:
|
||||
- file: lsetcsync
|
||||
- file: trusttheca
|
||||
|
||||
@@ -1,13 +1,14 @@
|
||||
logstash:
|
||||
enabled:
|
||||
enabled:
|
||||
description: Enables or disables the Logstash log event forwarding process. On most grid installations, when this process is disabled log events are unable to be ingested into the SOC backend.
|
||||
helpLink: logstash.html
|
||||
forcedType: bool
|
||||
helpLink: logstash
|
||||
assigned_pipelines:
|
||||
roles:
|
||||
standalone: &assigned_pipelines
|
||||
description: List of defined pipelines to add to this role.
|
||||
advanced: True
|
||||
helpLink: logstash.html
|
||||
helpLink: logstash
|
||||
multiline: True
|
||||
forcedType: "[]string"
|
||||
duplicates: True
|
||||
@@ -21,7 +22,7 @@ logstash:
|
||||
receiver: &defined_pipelines
|
||||
description: List of pipeline configurations assign to this group.
|
||||
advanced: True
|
||||
helpLink: logstash.html
|
||||
helpLink: logstash
|
||||
multiline: True
|
||||
forcedType: "[]string"
|
||||
duplicates: True
|
||||
@@ -39,7 +40,7 @@ logstash:
|
||||
advanced: True
|
||||
multiline: True
|
||||
forcedType: string
|
||||
helpLink: logstash.html
|
||||
helpLink: logstash
|
||||
duplicates: True
|
||||
custom002: *pipeline_config
|
||||
custom003: *pipeline_config
|
||||
@@ -53,35 +54,35 @@ logstash:
|
||||
settings:
|
||||
lsheap:
|
||||
description: Heap size to use for logstash
|
||||
helpLink: logstash.html
|
||||
helpLink: logstash
|
||||
global: False
|
||||
config:
|
||||
api_x_http_x_host:
|
||||
description: Host interface to listen to connections.
|
||||
helpLink: logstash.html
|
||||
helpLink: logstash
|
||||
readonly: True
|
||||
advanced: True
|
||||
path_x_logs:
|
||||
description: Path inside the container to wrote logs.
|
||||
helpLink: logstash.html
|
||||
helpLink: logstash
|
||||
readonly: True
|
||||
advanced: True
|
||||
pipeline_x_workers:
|
||||
description: Number of worker threads to process events in logstash.
|
||||
helpLink: logstash.html
|
||||
helpLink: logstash
|
||||
global: False
|
||||
pipeline_x_batch_x_size:
|
||||
description: Logstash batch size.
|
||||
helpLink: logstash.html
|
||||
helpLink: logstash
|
||||
global: False
|
||||
pipeline_x_ecs_compatibility:
|
||||
description: Sets ECS compatibility. This is set per pipeline so you should never need to change this.
|
||||
helpLink: logstash.html
|
||||
helpLink: logstash
|
||||
readonly: True
|
||||
advanced: True
|
||||
dmz_nodes:
|
||||
description: "List of receiver nodes in DMZs. Prevents sensors from sending to these receivers. Primarily used for external Elastic agents."
|
||||
helpLink: logstash.html
|
||||
helpLink: logstash
|
||||
multiline: True
|
||||
advanced: True
|
||||
forcedType: "[]string"
|
||||
|
||||
@@ -1,2 +1,2 @@
|
||||
https://repo.securityonion.net/file/so-repo/prod/2.4/oracle/9
|
||||
https://repo-alt.securityonion.net/prod/2.4/oracle/9
|
||||
https://repo.securityonion.net/file/so-repo/prod/3/oracle/9
|
||||
https://repo-alt.securityonion.net/prod/3/oracle/9
|
||||
@@ -63,11 +63,9 @@ yara_log_dir:
|
||||
- user
|
||||
- group
|
||||
|
||||
{% if GLOBALS.os_family == 'RedHat' %}
|
||||
install_createrepo:
|
||||
pkg.installed:
|
||||
- name: createrepo_c
|
||||
{% endif %}
|
||||
|
||||
repo_conf_dir:
|
||||
file.directory:
|
||||
|
||||
@@ -2,81 +2,82 @@ manager:
|
||||
reposync:
|
||||
enabled:
|
||||
description: This is the daily task of syncing the Security Onion OS packages. It is recommended that this setting remain enabled to ensure important updates are applied to the grid on an automated, scheduled basis.
|
||||
forcedType: bool
|
||||
global: True
|
||||
helpLink: soup.html
|
||||
helpLink: soup
|
||||
hour:
|
||||
description: The hour of the day in which the repo sync takes place.
|
||||
global: True
|
||||
helpLink: soup.html
|
||||
helpLink: soup
|
||||
minute:
|
||||
description: The minute within the hour to run the repo sync.
|
||||
global: True
|
||||
helpLink: soup.html
|
||||
helpLink: soup
|
||||
elastalert:
|
||||
description: Enable elastalert 1=enabled 0=disabled.
|
||||
global: True
|
||||
helpLink: elastalert.html
|
||||
helpLink: elastalert
|
||||
no_proxy:
|
||||
description: String of hosts to ignore the proxy settings for.
|
||||
global: True
|
||||
helpLink: proxy.html
|
||||
helpLink: proxy
|
||||
proxy:
|
||||
description: Proxy server to use for updates.
|
||||
global: True
|
||||
helpLink: proxy.html
|
||||
helpLink: proxy
|
||||
additionalCA:
|
||||
description: Additional CA certificates to trust in PEM format.
|
||||
global: True
|
||||
advanced: True
|
||||
multiline: True
|
||||
forcedType: string
|
||||
helpLink: proxy.html
|
||||
helpLink: proxy
|
||||
insecureSkipVerify:
|
||||
description: Disable TLS verification for outgoing requests. This will make your installation less secure to MITM attacks. Recommended only for debugging purposes.
|
||||
advanced: True
|
||||
forcedType: bool
|
||||
global: True
|
||||
helpLink: proxy.html
|
||||
helpLink: proxy
|
||||
agent_monitoring:
|
||||
enabled:
|
||||
description: Enable monitoring elastic agents for health issues. Can be used to trigger an alert when a 'critical' agent hasn't checked in with fleet for longer than the configured offline threshold.
|
||||
global: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
forcedType: bool
|
||||
config:
|
||||
critical_agents:
|
||||
description: List of 'critical' agents to log when they haven't checked in longer than the maximum allowed time. If there are no 'critical' agents specified all offline agents will be logged once they reach the offline threshold.
|
||||
global: True
|
||||
multiline: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
forcedType: "[]string"
|
||||
custom_kquery:
|
||||
description: For more granular control over what agents to monitor for offline|degraded status add a kquery here. It is recommended to create & test within Elastic Fleet first to ensure your agents are targeted correctly using the query. eg 'status:offline AND tags:INFRA'
|
||||
global: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
forcedType: string
|
||||
advanced: True
|
||||
offline_threshold:
|
||||
description: The maximum allowed time in hours a 'critical' agent has been offline before being logged.
|
||||
global: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
forcedType: int
|
||||
realert_threshold:
|
||||
description: The time to pass before another alert for an offline agent exceeding the offline_threshold is generated.
|
||||
global: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
forcedType: int
|
||||
page_size:
|
||||
description: The amount of agents that can be processed per API request to fleet.
|
||||
global: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
forcedType: int
|
||||
advanced: True
|
||||
run_interval:
|
||||
description: The time in minutes between checking fleet agent statuses.
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elastic-fleet.html
|
||||
helpLink: elastic-fleet
|
||||
forcedType: int
|
||||
managed_integrations:
|
||||
description: List of integrations to add into SOC config UI. Enter the full or partial integration name. Eg. 1password, 1pass
|
||||
@@ -84,4 +85,4 @@ manager:
|
||||
multiline: True
|
||||
global: True
|
||||
advanced: True
|
||||
helpLink: elasticsearch.html
|
||||
helpLink: elasticsearch
|
||||
@@ -134,8 +134,8 @@ function require() {
|
||||
function verifyEnvironment() {
|
||||
require "jq"
|
||||
require "curl"
|
||||
response=$(curl -Ss -L ${hydraUrl}/)
|
||||
[[ "$response" != *"Error 404"* ]] && fail "Unable to communicate with Hydra; specify URL via HYDRA_URL environment variable"
|
||||
response=$(curl -Ss -L ${hydraUrl}/health/alive)
|
||||
[[ "$response" != '{"status":"ok"}' ]] && fail "Unable to communicate with Hydra; specify URL via HYDRA_URL environment variable"
|
||||
}
|
||||
|
||||
function createFile() {
|
||||
|
||||
@@ -462,19 +462,14 @@ function add_sensor_to_minion() {
|
||||
echo " lb_procs: '$CORECOUNT'"
|
||||
echo "suricata:"
|
||||
echo " enabled: True "
|
||||
echo " pcap:"
|
||||
echo " enabled: True"
|
||||
if [[ $is_pcaplimit ]]; then
|
||||
echo " pcap:"
|
||||
echo " maxsize: $MAX_PCAP_SPACE"
|
||||
fi
|
||||
echo " config:"
|
||||
echo " af-packet:"
|
||||
echo " threads: '$CORECOUNT'"
|
||||
echo "pcap:"
|
||||
echo " enabled: True"
|
||||
if [[ $is_pcaplimit ]]; then
|
||||
echo " config:"
|
||||
echo " diskfreepercentage: $DFREEPERCENT"
|
||||
fi
|
||||
echo " "
|
||||
} >> $PILLARFILE
|
||||
if [ $? -ne 0 ]; then
|
||||
|
||||
@@ -143,7 +143,7 @@ show_usage() {
|
||||
echo " -v Show verbose output (files changed/added/deleted)"
|
||||
echo " -vv Show very verbose output (includes file diffs)"
|
||||
echo " --test Test mode - show what would change without making changes"
|
||||
echo " branch Git branch to checkout (default: 2.4/main)"
|
||||
echo " branch Git branch to checkout (default: 3/main)"
|
||||
echo ""
|
||||
echo "Examples:"
|
||||
echo " $0 # Normal operation"
|
||||
@@ -193,7 +193,7 @@ done
|
||||
|
||||
# Set default branch if not provided
|
||||
if [ -z "$BRANCH" ]; then
|
||||
BRANCH=2.4/main
|
||||
BRANCH=3/main
|
||||
fi
|
||||
|
||||
got_root
|
||||
|
||||
@@ -22,7 +22,7 @@ def showUsage(args):
|
||||
print(' removelistitem - Remove a list item from a yaml key, if it exists and is a list. Requires KEY and LISTITEM args.', file=sys.stderr)
|
||||
print(' replacelistobject - Replace a list object based on a condition. Requires KEY, CONDITION_FIELD, CONDITION_VALUE, and JSON_OBJECT args.', file=sys.stderr)
|
||||
print(' add - Add a new key and set its value. Fails if key already exists. Requires KEY and VALUE args.', file=sys.stderr)
|
||||
print(' get - Displays (to stdout) the value stored in the given key. Requires KEY arg.', file=sys.stderr)
|
||||
print(' get [-r] - Displays (to stdout) the value stored in the given key. Requires KEY arg. Use -r for raw output without YAML formatting.', file=sys.stderr)
|
||||
print(' remove - Removes a yaml key, if it exists. Requires KEY arg.', file=sys.stderr)
|
||||
print(' replace - Replaces (or adds) a new key and set its value. Requires KEY and VALUE args.', file=sys.stderr)
|
||||
print(' help - Prints this usage information.', file=sys.stderr)
|
||||
@@ -256,7 +256,7 @@ def replacelistobject(args):
|
||||
def addKey(content, key, value):
|
||||
pieces = key.split(".", 1)
|
||||
if len(pieces) > 1:
|
||||
if not pieces[0] in content:
|
||||
if pieces[0] not in content or content[pieces[0]] is None:
|
||||
content[pieces[0]] = {}
|
||||
addKey(content[pieces[0]], pieces[1], value)
|
||||
elif key in content:
|
||||
@@ -332,6 +332,11 @@ def getKeyValue(content, key):
|
||||
|
||||
|
||||
def get(args):
|
||||
raw = False
|
||||
if len(args) > 0 and args[0] == '-r':
|
||||
raw = True
|
||||
args = args[1:]
|
||||
|
||||
if len(args) != 2:
|
||||
print('Missing filename or key arg', file=sys.stderr)
|
||||
showUsage(None)
|
||||
@@ -346,7 +351,15 @@ def get(args):
|
||||
print(f"Key '{key}' not found by so-yaml.py", file=sys.stderr)
|
||||
return 2
|
||||
|
||||
print(yaml.safe_dump(output))
|
||||
if raw:
|
||||
if isinstance(output, bool):
|
||||
print(str(output).lower())
|
||||
elif isinstance(output, (dict, list)):
|
||||
print(yaml.safe_dump(output).strip())
|
||||
else:
|
||||
print(output)
|
||||
else:
|
||||
print(yaml.safe_dump(output))
|
||||
return 0
|
||||
|
||||
|
||||
|
||||
@@ -395,6 +395,17 @@ class TestRemove(unittest.TestCase):
|
||||
self.assertEqual(result, 0)
|
||||
self.assertIn("45\n...", mock_stdout.getvalue())
|
||||
|
||||
def test_get_int_raw(self):
|
||||
with patch('sys.stdout', new=StringIO()) as mock_stdout:
|
||||
filename = "/tmp/so-yaml_test-get.yaml"
|
||||
file = open(filename, "w")
|
||||
file.write("{key1: { child1: 123, child2: { deep1: 45 } }, key2: false, key3: [e,f,g]}")
|
||||
file.close()
|
||||
|
||||
result = soyaml.get(["-r", filename, "key1.child2.deep1"])
|
||||
self.assertEqual(result, 0)
|
||||
self.assertEqual("45\n", mock_stdout.getvalue())
|
||||
|
||||
def test_get_str(self):
|
||||
with patch('sys.stdout', new=StringIO()) as mock_stdout:
|
||||
filename = "/tmp/so-yaml_test-get.yaml"
|
||||
@@ -406,6 +417,51 @@ class TestRemove(unittest.TestCase):
|
||||
self.assertEqual(result, 0)
|
||||
self.assertIn("hello\n...", mock_stdout.getvalue())
|
||||
|
||||
def test_get_str_raw(self):
|
||||
with patch('sys.stdout', new=StringIO()) as mock_stdout:
|
||||
filename = "/tmp/so-yaml_test-get.yaml"
|
||||
file = open(filename, "w")
|
||||
file.write("{key1: { child1: 123, child2: { deep1: \"hello\" } }, key2: false, key3: [e,f,g]}")
|
||||
file.close()
|
||||
|
||||
result = soyaml.get(["-r", filename, "key1.child2.deep1"])
|
||||
self.assertEqual(result, 0)
|
||||
self.assertEqual("hello\n", mock_stdout.getvalue())
|
||||
|
||||
def test_get_bool(self):
|
||||
with patch('sys.stdout', new=StringIO()) as mock_stdout:
|
||||
filename = "/tmp/so-yaml_test-get.yaml"
|
||||
file = open(filename, "w")
|
||||
file.write("{key1: { child1: 123, child2: { deep1: 45 } }, key2: false, key3: [e,f,g]}")
|
||||
file.close()
|
||||
|
||||
result = soyaml.get([filename, "key2"])
|
||||
self.assertEqual(result, 0)
|
||||
self.assertIn("false\n...", mock_stdout.getvalue())
|
||||
|
||||
def test_get_bool_raw(self):
|
||||
with patch('sys.stdout', new=StringIO()) as mock_stdout:
|
||||
filename = "/tmp/so-yaml_test-get.yaml"
|
||||
file = open(filename, "w")
|
||||
file.write("{key1: { child1: 123, child2: { deep1: 45 } }, key2: false, key3: [e,f,g]}")
|
||||
file.close()
|
||||
|
||||
result = soyaml.get(["-r", filename, "key2"])
|
||||
self.assertEqual(result, 0)
|
||||
self.assertEqual("false\n", mock_stdout.getvalue())
|
||||
|
||||
def test_get_dict_raw(self):
|
||||
with patch('sys.stdout', new=StringIO()) as mock_stdout:
|
||||
filename = "/tmp/so-yaml_test-get.yaml"
|
||||
file = open(filename, "w")
|
||||
file.write("{key1: { child1: 123, child2: { deep1: 45 } }, key2: false, key3: [e,f,g]}")
|
||||
file.close()
|
||||
|
||||
result = soyaml.get(["-r", filename, "key1"])
|
||||
self.assertEqual(result, 0)
|
||||
self.assertIn("child1: 123", mock_stdout.getvalue())
|
||||
self.assertNotIn("...", mock_stdout.getvalue())
|
||||
|
||||
def test_get_list(self):
|
||||
with patch('sys.stdout', new=StringIO()) as mock_stdout:
|
||||
filename = "/tmp/so-yaml_test-get.yaml"
|
||||
|
||||
File diff suppressed because it is too large
Load Diff
@@ -1,184 +0,0 @@
|
||||
#!/bin/bash
|
||||
|
||||
# Copyright Security Onion Solutions LLC and/or licensed to Security Onion Solutions LLC under one
|
||||
# or more contributor license agreements. Licensed under the Elastic License 2.0 as shown at
|
||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||
# Elastic License 2.0.
|
||||
|
||||
|
||||
. /usr/sbin/so-common
|
||||
|
||||
UPDATE_URL=https://raw.githubusercontent.com/Security-Onion-Solutions/securityonion/refs/heads/3/main/VERSION
|
||||
|
||||
# Check if already running version 3
|
||||
CURRENT_VERSION=$(cat /etc/soversion 2>/dev/null)
|
||||
if [[ "$CURRENT_VERSION" =~ ^3\. ]]; then
|
||||
echo ""
|
||||
echo "========================================================================="
|
||||
echo " Already Running Security Onion 3"
|
||||
echo "========================================================================="
|
||||
echo ""
|
||||
echo " This system is already running Security Onion $CURRENT_VERSION."
|
||||
echo " Use 'soup' to update within the 3.x release line."
|
||||
echo ""
|
||||
exit 0
|
||||
fi
|
||||
|
||||
echo ""
|
||||
echo "Checking PCAP settings."
|
||||
echo ""
|
||||
|
||||
# Check pcapengine setting - must be SURICATA before upgrading to version 3
|
||||
PCAP_ENGINE=$(lookup_pillar "pcapengine")
|
||||
|
||||
PCAP_DELETED=false
|
||||
|
||||
prompt_delete_pcap() {
|
||||
read -rp " Would you like to delete all remaining Stenographer PCAP data? (y/N): " DELETE_PCAP
|
||||
if [[ "$DELETE_PCAP" =~ ^[Yy]$ ]]; then
|
||||
echo ""
|
||||
echo " WARNING: This will permanently delete all Stenographer PCAP data"
|
||||
echo " on all nodes. This action cannot be undone."
|
||||
echo ""
|
||||
read -rp " Are you sure? (y/N): " CONFIRM_DELETE
|
||||
if [[ "$CONFIRM_DELETE" =~ ^[Yy]$ ]]; then
|
||||
echo ""
|
||||
echo " Deleting Stenographer PCAP data on all nodes..."
|
||||
salt '*' cmd.run "rm -rf /nsm/pcap/* && rm -rf /nsm/pcapindex/*"
|
||||
echo " Done."
|
||||
PCAP_DELETED=true
|
||||
else
|
||||
echo ""
|
||||
echo " Delete cancelled."
|
||||
fi
|
||||
fi
|
||||
}
|
||||
|
||||
pcapengine_not_changed() {
|
||||
echo ""
|
||||
echo " PCAP engine must be set to SURICATA before upgrading to Security Onion 3."
|
||||
echo " You can change this in SOC by navigating to:"
|
||||
echo " Configuration -> global -> pcapengine"
|
||||
}
|
||||
|
||||
prompt_change_engine() {
|
||||
local current_engine=$1
|
||||
echo ""
|
||||
read -rp " Would you like to change the PCAP engine to SURICATA now? (y/N): " CHANGE_ENGINE
|
||||
if [[ "$CHANGE_ENGINE" =~ ^[Yy]$ ]]; then
|
||||
if [[ "$PCAP_DELETED" != "true" ]]; then
|
||||
echo ""
|
||||
echo " WARNING: Stenographer PCAP data was not deleted. If you proceed,"
|
||||
echo " this data will no longer be accessible through SOC and will never"
|
||||
echo " be automatically deleted. You will need to manually remove it later."
|
||||
echo ""
|
||||
read -rp " Continue with changing pcapengine to SURICATA? (y/N): " CONFIRM_CHANGE
|
||||
if [[ ! "$CONFIRM_CHANGE" =~ ^[Yy]$ ]]; then
|
||||
pcapengine_not_changed
|
||||
return 1
|
||||
fi
|
||||
fi
|
||||
echo ""
|
||||
echo " Updating PCAP engine to SURICATA..."
|
||||
so-yaml.py replace /opt/so/saltstack/local/pillar/global/soc_global.sls global.pcapengine SURICATA
|
||||
echo " Done."
|
||||
return 0
|
||||
else
|
||||
pcapengine_not_changed
|
||||
return 1
|
||||
fi
|
||||
}
|
||||
|
||||
case "$PCAP_ENGINE" in
|
||||
SURICATA)
|
||||
echo "PCAP engine settings OK."
|
||||
;;
|
||||
TRANSITION|STENO)
|
||||
echo ""
|
||||
echo "========================================================================="
|
||||
echo " PCAP Engine Check Failed"
|
||||
echo "========================================================================="
|
||||
echo ""
|
||||
echo " Your PCAP engine is currently set to $PCAP_ENGINE."
|
||||
echo ""
|
||||
echo " Before upgrading to Security Onion 3, Stenographer PCAP data must be"
|
||||
echo " removed and the PCAP engine must be set to SURICATA."
|
||||
echo ""
|
||||
echo " To check remaining Stenographer PCAP usage, run:"
|
||||
echo " salt '*' cmd.run 'du -sh /nsm/pcap'"
|
||||
echo ""
|
||||
|
||||
prompt_delete_pcap
|
||||
if ! prompt_change_engine "$PCAP_ENGINE"; then
|
||||
echo ""
|
||||
exit 1
|
||||
fi
|
||||
;;
|
||||
*)
|
||||
echo ""
|
||||
echo "========================================================================="
|
||||
echo " PCAP Engine Check Failed"
|
||||
echo "========================================================================="
|
||||
echo ""
|
||||
echo " Unable to determine the PCAP engine setting (got: '$PCAP_ENGINE')."
|
||||
echo " Please ensure the PCAP engine is set to SURICATA."
|
||||
echo " In SOC, navigate to Configuration -> global -> pcapengine"
|
||||
echo " and change the value to SURICATA."
|
||||
echo ""
|
||||
exit 1
|
||||
;;
|
||||
esac
|
||||
|
||||
echo ""
|
||||
echo "Checking Versions."
|
||||
echo ""
|
||||
|
||||
# Check if Security Onion 3 has been released
|
||||
VERSION=$(curl -sSf "$UPDATE_URL" 2>/dev/null)
|
||||
|
||||
if [[ -z "$VERSION" ]]; then
|
||||
echo ""
|
||||
echo "========================================================================="
|
||||
echo " Unable to Check Version"
|
||||
echo "========================================================================="
|
||||
echo ""
|
||||
echo " Could not retrieve version information from:"
|
||||
echo " $UPDATE_URL"
|
||||
echo ""
|
||||
echo " Please check your network connection and try again."
|
||||
echo ""
|
||||
exit 1
|
||||
fi
|
||||
|
||||
if [[ "$VERSION" == "UNRELEASED" ]]; then
|
||||
echo ""
|
||||
echo "========================================================================="
|
||||
echo " Security Onion 3 Not Available"
|
||||
echo "========================================================================="
|
||||
echo ""
|
||||
echo " Security Onion 3 has not been released yet."
|
||||
echo ""
|
||||
echo " Please check back later or visit https://securityonion.net for updates."
|
||||
echo ""
|
||||
exit 1
|
||||
fi
|
||||
|
||||
# Validate version format (e.g., 3.0.2)
|
||||
if [[ ! "$VERSION" =~ ^[0-9]+\.[0-9]+\.[0-9]+$ ]]; then
|
||||
echo ""
|
||||
echo "========================================================================="
|
||||
echo " Invalid Version"
|
||||
echo "========================================================================="
|
||||
echo ""
|
||||
echo " Received unexpected version format: '$VERSION'"
|
||||
echo ""
|
||||
echo " Please check back later or visit https://securityonion.net for updates."
|
||||
echo ""
|
||||
exit 1
|
||||
fi
|
||||
|
||||
echo "Security Onion 3 ($VERSION) is available. Upgrading..."
|
||||
echo ""
|
||||
|
||||
# All checks passed - proceed with upgrade
|
||||
BRANCH=3/main soup
|
||||
@@ -3,6 +3,7 @@ nginx:
|
||||
external_suricata: False
|
||||
ssl:
|
||||
replace_cert: False
|
||||
alt_names: []
|
||||
config:
|
||||
throttle_login_burst: 12
|
||||
throttle_login_rate: 20
|
||||
|
||||
@@ -6,7 +6,7 @@
|
||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
||||
{% if sls.split('.')[0] in allowed_states %}
|
||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKER %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKERMERGED %}
|
||||
{% from 'nginx/map.jinja' import NGINXMERGED %}
|
||||
|
||||
include:
|
||||
@@ -37,11 +37,11 @@ so-nginx:
|
||||
- hostname: so-nginx
|
||||
- networks:
|
||||
- sobridge:
|
||||
- ipv4_address: {{ DOCKER.containers[container_config].ip }}
|
||||
- ipv4_address: {{ DOCKERMERGED.containers[container_config].ip }}
|
||||
- extra_hosts:
|
||||
- {{ GLOBALS.manager }}:{{ GLOBALS.manager_ip }}
|
||||
{% if DOCKER.containers[container_config].extra_hosts %}
|
||||
{% for XTRAHOST in DOCKER.containers[container_config].extra_hosts %}
|
||||
{% if DOCKERMERGED.containers[container_config].extra_hosts %}
|
||||
{% for XTRAHOST in DOCKERMERGED.containers[container_config].extra_hosts %}
|
||||
- {{ XTRAHOST }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
@@ -64,20 +64,26 @@ so-nginx:
|
||||
- /opt/so/rules/nids/suri:/surirules:ro
|
||||
{% endif %}
|
||||
{% endif %}
|
||||
{% if DOCKER.containers[container_config].custom_bind_mounts %}
|
||||
{% for BIND in DOCKER.containers[container_config].custom_bind_mounts %}
|
||||
{% if DOCKERMERGED.containers[container_config].custom_bind_mounts %}
|
||||
{% for BIND in DOCKERMERGED.containers[container_config].custom_bind_mounts %}
|
||||
- {{ BIND }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
{% if DOCKER.containers[container_config].extra_env %}
|
||||
{% if DOCKERMERGED.containers[container_config].extra_env %}
|
||||
- environment:
|
||||
{% for XTRAENV in DOCKER.containers[container_config].extra_env %}
|
||||
{% for XTRAENV in DOCKERMERGED.containers[container_config].extra_env %}
|
||||
- {{ XTRAENV }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
{% if DOCKERMERGED.containers[container_config].ulimits %}
|
||||
- ulimits:
|
||||
{% for ULIMIT in DOCKERMERGED.containers[container_config].ulimits %}
|
||||
- {{ ULIMIT.name }}={{ ULIMIT.soft }}:{{ ULIMIT.hard }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
- cap_add: NET_BIND_SERVICE
|
||||
- port_bindings:
|
||||
{% for BINDING in DOCKER.containers[container_config].port_bindings %}
|
||||
{% for BINDING in DOCKERMERGED.containers[container_config].port_bindings %}
|
||||
- {{ BINDING }}
|
||||
{% endfor %}
|
||||
- watch:
|
||||
|
||||
@@ -1,5 +1,5 @@
|
||||
{%- from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
{%- from 'docker/docker.map.jinja' import DOCKER %}
|
||||
{%- from 'docker/docker.map.jinja' import DOCKERMERGED %}
|
||||
{%- from 'nginx/map.jinja' import NGINXMERGED %}
|
||||
{%- set role = grains.id.split('_') | last %}
|
||||
{%- set influxpass = salt['pillar.get']('secrets:influx_pass') %}
|
||||
@@ -60,6 +60,8 @@ http {
|
||||
{%- endif %}
|
||||
|
||||
{%- if GLOBALS.is_manager %}
|
||||
{%- set all_names = [GLOBALS.hostname, GLOBALS.url_base] + NGINXMERGED.ssl.alt_names %}
|
||||
{%- set full_server_name = all_names | unique | join(' ') %}
|
||||
|
||||
server {
|
||||
listen 80 default_server;
|
||||
@@ -69,7 +71,7 @@ http {
|
||||
|
||||
server {
|
||||
listen 8443;
|
||||
server_name {{ GLOBALS.url_base }};
|
||||
server_name {{ full_server_name }};
|
||||
root /opt/socore/html;
|
||||
location /artifacts/ {
|
||||
try_files $uri =206;
|
||||
@@ -112,7 +114,7 @@ http {
|
||||
|
||||
server {
|
||||
listen 7788;
|
||||
server_name {{ GLOBALS.url_base }};
|
||||
server_name {{ full_server_name }};
|
||||
root /nsm/rules;
|
||||
location / {
|
||||
allow all;
|
||||
@@ -128,7 +130,7 @@ http {
|
||||
server {
|
||||
listen 7789 ssl;
|
||||
http2 on;
|
||||
server_name {{ GLOBALS.url_base }};
|
||||
server_name {{ full_server_name }};
|
||||
root /surirules;
|
||||
|
||||
add_header Content-Security-Policy "default-src 'self' 'unsafe-inline' 'unsafe-eval' https: data: blob: wss:; frame-ancestors 'self'";
|
||||
@@ -161,7 +163,7 @@ http {
|
||||
server {
|
||||
listen 443 ssl;
|
||||
http2 on;
|
||||
server_name {{ GLOBALS.url_base }};
|
||||
server_name {{ full_server_name }};
|
||||
root /opt/socore/html;
|
||||
index index.html;
|
||||
|
||||
@@ -385,15 +387,13 @@ http {
|
||||
error_page 429 = @error429;
|
||||
|
||||
location @error401 {
|
||||
if ($request_uri ~* (^/connect/.*|^/oauth2/.*)) {
|
||||
if ($request_uri ~* (^/api/.*|^/connect/.*|^/oauth2/.*)) {
|
||||
return 401;
|
||||
}
|
||||
|
||||
if ($request_uri ~* ^/(?!(^/api/.*))) {
|
||||
add_header Strict-Transport-Security "max-age=31536000; includeSubDomains";
|
||||
}
|
||||
add_header Strict-Transport-Security "max-age=31536000; includeSubDomains";
|
||||
|
||||
if ($request_uri ~* ^/(?!(api/|login|auth|oauth2|$))) {
|
||||
if ($request_uri ~* ^/(?!(login|auth|oauth2|$))) {
|
||||
add_header Set-Cookie "AUTH_REDIRECT=$request_uri;Path=/;Max-Age=14400";
|
||||
}
|
||||
return 302 /auth/self-service/login/browser;
|
||||
|
||||
@@ -1,12 +1,13 @@
|
||||
nginx:
|
||||
enabled:
|
||||
enabled:
|
||||
description: Enables or disables the Nginx web server and reverse proxy. WARNING - Disabling this process will prevent access to SOC and other important web interfaces and APIs. Re-enabling the process is a manual effort. Do not change this setting without instruction from Security Onion support.
|
||||
forcedType: bool
|
||||
advanced: True
|
||||
helpLink: nginx.html
|
||||
helpLink: nginx
|
||||
external_suricata:
|
||||
description: Enable this to allow external access to Suricata Rulesets managed by Detections.
|
||||
advanced: True
|
||||
helplink: nginx.html
|
||||
helpLink: nginx
|
||||
forcedType: bool
|
||||
ssl:
|
||||
replace_cert:
|
||||
@@ -15,27 +16,33 @@ nginx:
|
||||
advanced: True
|
||||
forcedType: bool
|
||||
title: Replace Default Cert
|
||||
helpLink: nginx.html
|
||||
helpLink: nginx
|
||||
ssl__key:
|
||||
description: If you enabled the replace_cert option, paste the contents of your .key file here.
|
||||
file: True
|
||||
title: SSL/TLS Key File
|
||||
advanced: True
|
||||
global: True
|
||||
helpLink: nginx.html
|
||||
helpLink: nginx
|
||||
ssl__crt:
|
||||
description: If you enabled the replace_cert option, paste the contents of your .crt file here.
|
||||
file: True
|
||||
title: SSL/TLS Cert File
|
||||
advanced: True
|
||||
global: True
|
||||
helpLink: nginx.html
|
||||
helpLink: nginx
|
||||
alt_names:
|
||||
description: Provide a list of alternate names to allow remote systems the ability to refer to the SOC API as another hostname.
|
||||
global: True
|
||||
forcedType: '[]string'
|
||||
multiline: True
|
||||
helpLink: nginx
|
||||
config:
|
||||
throttle_login_burst:
|
||||
description: Number of login requests that can burst without triggering request throttling. Higher values allow more repeated login attempts. Values greater than zero are required in order to provide a usable login flow.
|
||||
global: True
|
||||
helpLink: nginx.html
|
||||
helpLink: nginx
|
||||
throttle_login_rate:
|
||||
description: Number of login API requests per minute that can be processed without triggering a rate limit. Higher values allow more repeated login attempts. Requests are counted by unique client IP and averaged over time. Note that a single login flow will perform multiple requests to the login API, so this value will need to be adjusted accordingly.
|
||||
global: True
|
||||
helpLink: nginx.html
|
||||
helpLink: nginx
|
||||
|
||||
@@ -49,6 +49,17 @@ managerssl_key:
|
||||
- docker_container: so-nginx
|
||||
|
||||
# Create a cert for the reverse proxy
|
||||
{% set san_list = [GLOBALS.hostname, GLOBALS.node_ip, GLOBALS.url_base] + NGINXMERGED.ssl.alt_names %}
|
||||
{% set unique_san_list = san_list | unique %}
|
||||
{% set managerssl_san_list = [] %}
|
||||
{% for item in unique_san_list %}
|
||||
{% if item | ipaddr %}
|
||||
{% do managerssl_san_list.append("IP:" + item) %}
|
||||
{% else %}
|
||||
{% do managerssl_san_list.append("DNS:" + item) %}
|
||||
{% endif %}
|
||||
{% endfor %}
|
||||
{% set managerssl_san = managerssl_san_list | join(', ') %}
|
||||
managerssl_crt:
|
||||
x509.certificate_managed:
|
||||
- name: /etc/pki/managerssl.crt
|
||||
@@ -56,7 +67,7 @@ managerssl_crt:
|
||||
- signing_policy: managerssl
|
||||
- private_key: /etc/pki/managerssl.key
|
||||
- CN: {{ GLOBALS.hostname }}
|
||||
- subjectAltName: "DNS:{{ GLOBALS.hostname }}, IP:{{ GLOBALS.node_ip }}, DNS:{{ GLOBALS.url_base }}"
|
||||
- subjectAltName: {{ managerssl_san }}
|
||||
- days_remaining: 7
|
||||
- days_valid: 820
|
||||
- backup: True
|
||||
|
||||
@@ -2,7 +2,6 @@
|
||||
# or more contributor license agreements. Licensed under the Elastic License 2.0 as shown at
|
||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||
# Elastic License 2.0.
|
||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
{% from 'ntp/config.map.jinja' import NTPCONFIG %}
|
||||
|
||||
chrony_pkg:
|
||||
@@ -17,11 +16,7 @@ chronyconf:
|
||||
- defaults:
|
||||
NTPCONFIG: {{ NTPCONFIG }}
|
||||
|
||||
{% if GLOBALS.os_family == 'RedHat' %}
|
||||
chronyd:
|
||||
{% else %}
|
||||
chrony:
|
||||
{% endif %}
|
||||
service.running:
|
||||
- enable: True
|
||||
- watch:
|
||||
|
||||
@@ -3,4 +3,4 @@ ntp:
|
||||
servers:
|
||||
description: NTP Server List
|
||||
title: NTP Servers
|
||||
helpLink: ntp.html
|
||||
helpLink: ntp
|
||||
|
||||
@@ -2,19 +2,20 @@ patch:
|
||||
os:
|
||||
enabled:
|
||||
description: Enable OS updates. WARNING - Disabling this setting will prevent important operating system updates from being applied on a scheduled basis.
|
||||
helpLink: soup.html
|
||||
forcedType: bool
|
||||
helpLink: soup
|
||||
schedule_to_run:
|
||||
description: Currently running schedule for updates.
|
||||
helpLink: soup.html
|
||||
helpLink: soup
|
||||
schedules:
|
||||
auto:
|
||||
splay: &splayOptions
|
||||
description: Seconds to splay updates.
|
||||
helpLink: soup.html
|
||||
helpLink: soup
|
||||
schedule:
|
||||
hours:
|
||||
description: Run the OS updates every X hours.
|
||||
helpLink: soup.html
|
||||
helpLink: soup
|
||||
monday:
|
||||
splay: *splayOptions
|
||||
schedule:
|
||||
@@ -51,7 +52,7 @@ patch:
|
||||
Monday: &dailyOptions
|
||||
description: List of times to apply OS patches daily.
|
||||
multiline: True
|
||||
helpLink: soup.html
|
||||
helpLink: soup
|
||||
Tuesday: *dailyOptions
|
||||
Wednesday: *dailyOptions
|
||||
Thursday: *dailyOptions
|
||||
@@ -64,7 +65,7 @@ patch:
|
||||
Monday: &weekdayOptions
|
||||
description: List of times for weekdays.
|
||||
multiline: True
|
||||
helpLink: soup.html
|
||||
helpLink: soup
|
||||
Tuesday: *weekdayOptions
|
||||
Wednesday: *weekdayOptions
|
||||
Thursday: *weekdayOptions
|
||||
@@ -75,5 +76,5 @@ patch:
|
||||
Saturday: &weekendOptions
|
||||
description: List of times for weekend days.
|
||||
multiline: true
|
||||
helpLink: soup.html
|
||||
helpLink: soup
|
||||
Sunday: *weekendOptions
|
||||
|
||||
@@ -1,22 +0,0 @@
|
||||
# Copyright Security Onion Solutions LLC and/or licensed to Security Onion Solutions LLC under one
|
||||
# or more contributor license agreements. Licensed under the Elastic License 2.0 as shown at
|
||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||
# Elastic License 2.0.
|
||||
|
||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
||||
{% if sls.split('.')[0] in allowed_states or sls in allowed_states%}
|
||||
|
||||
stenoca:
|
||||
file.directory:
|
||||
- name: /opt/so/conf/steno/certs
|
||||
- user: 941
|
||||
- group: 939
|
||||
- makedirs: True
|
||||
|
||||
{% else %}
|
||||
|
||||
{{sls}}_state_not_allowed:
|
||||
test.fail_without_changes:
|
||||
- name: {{sls}}_state_not_allowed
|
||||
|
||||
{% endif %}
|
||||
59
salt/pcap/cleanup.sls
Normal file
59
salt/pcap/cleanup.sls
Normal file
@@ -0,0 +1,59 @@
|
||||
# Copyright Security Onion Solutions LLC and/or licensed to Security Onion Solutions LLC under one
|
||||
# or more contributor license agreements. Licensed under the Elastic License 2.0 as shown at
|
||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||
# Elastic License 2.0.
|
||||
|
||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
|
||||
{% if GLOBALS.is_sensor %}
|
||||
|
||||
delete_so-steno_so-status.conf:
|
||||
file.line:
|
||||
- name: /opt/so/conf/so-status/so-status.conf
|
||||
- mode: delete
|
||||
- match: so-steno
|
||||
|
||||
remove_stenographer_user:
|
||||
user.absent:
|
||||
- name: stenographer
|
||||
- force: True
|
||||
|
||||
remove_stenographer_log_dir:
|
||||
file.absent:
|
||||
- name: /opt/so/log/stenographer
|
||||
|
||||
remove_stenoloss_script:
|
||||
file.absent:
|
||||
- name: /opt/so/conf/telegraf/scripts/stenoloss.sh
|
||||
|
||||
remove_steno_conf_dir:
|
||||
file.absent:
|
||||
- name: /opt/so/conf/steno
|
||||
|
||||
remove_so_pcap_export:
|
||||
file.absent:
|
||||
- name: /usr/sbin/so-pcap-export
|
||||
|
||||
remove_so_pcap_restart:
|
||||
file.absent:
|
||||
- name: /usr/sbin/so-pcap-restart
|
||||
|
||||
remove_so_pcap_start:
|
||||
file.absent:
|
||||
- name: /usr/sbin/so-pcap-start
|
||||
|
||||
remove_so_pcap_stop:
|
||||
file.absent:
|
||||
- name: /usr/sbin/so-pcap-stop
|
||||
|
||||
so-steno:
|
||||
docker_container.absent:
|
||||
- force: True
|
||||
|
||||
{% else %}
|
||||
|
||||
{{sls}}.non_sensor_node:
|
||||
test.show_notification:
|
||||
- text: "Stenographer cleanup not applicable on non-sensor nodes."
|
||||
|
||||
{% endif %}
|
||||
Some files were not shown because too many files have changed in this diff Show More
Reference in New Issue
Block a user