mirror of
https://github.com/Security-Onion-Solutions/securityonion.git
synced 2026-03-23 21:12:39 +01:00
Compare commits
2 Commits
bravo
...
reyesj2-44
| Author | SHA1 | Date | |
|---|---|---|---|
|
|
7e7b8dc8a8 | ||
|
|
2c6c502067 |
4
.github/DISCUSSION_TEMPLATE/2-4.yml
vendored
4
.github/DISCUSSION_TEMPLATE/2-4.yml
vendored
@@ -2,11 +2,13 @@ body:
|
||||
- type: markdown
|
||||
attributes:
|
||||
value: |
|
||||
⚠️ This category is solely for conversations related to Security Onion 2.4 ⚠️
|
||||
|
||||
If your organization needs more immediate, enterprise grade professional support, with one-on-one virtual meetings and screensharing, contact us via our website: https://securityonion.com/support
|
||||
- type: dropdown
|
||||
attributes:
|
||||
label: Version
|
||||
description: Which version of Security Onion are you asking about?
|
||||
description: Which version of Security Onion 2.4.x are you asking about?
|
||||
options:
|
||||
-
|
||||
- 2.4.10
|
||||
|
||||
66
README.md
66
README.md
@@ -1,58 +1,50 @@
|
||||
<p align="center">
|
||||
<img src="https://securityonionsolutions.com/logo/logo-so-onion-dark.svg" width="400" alt="Security Onion Logo">
|
||||
</p>
|
||||
## Security Onion 2.4
|
||||
|
||||
# Security Onion
|
||||
Security Onion 2.4 is here!
|
||||
|
||||
Security Onion is a free and open Linux distribution for threat hunting, enterprise security monitoring, and log management. It includes a comprehensive suite of tools designed to work together to provide visibility into your network and host activity.
|
||||
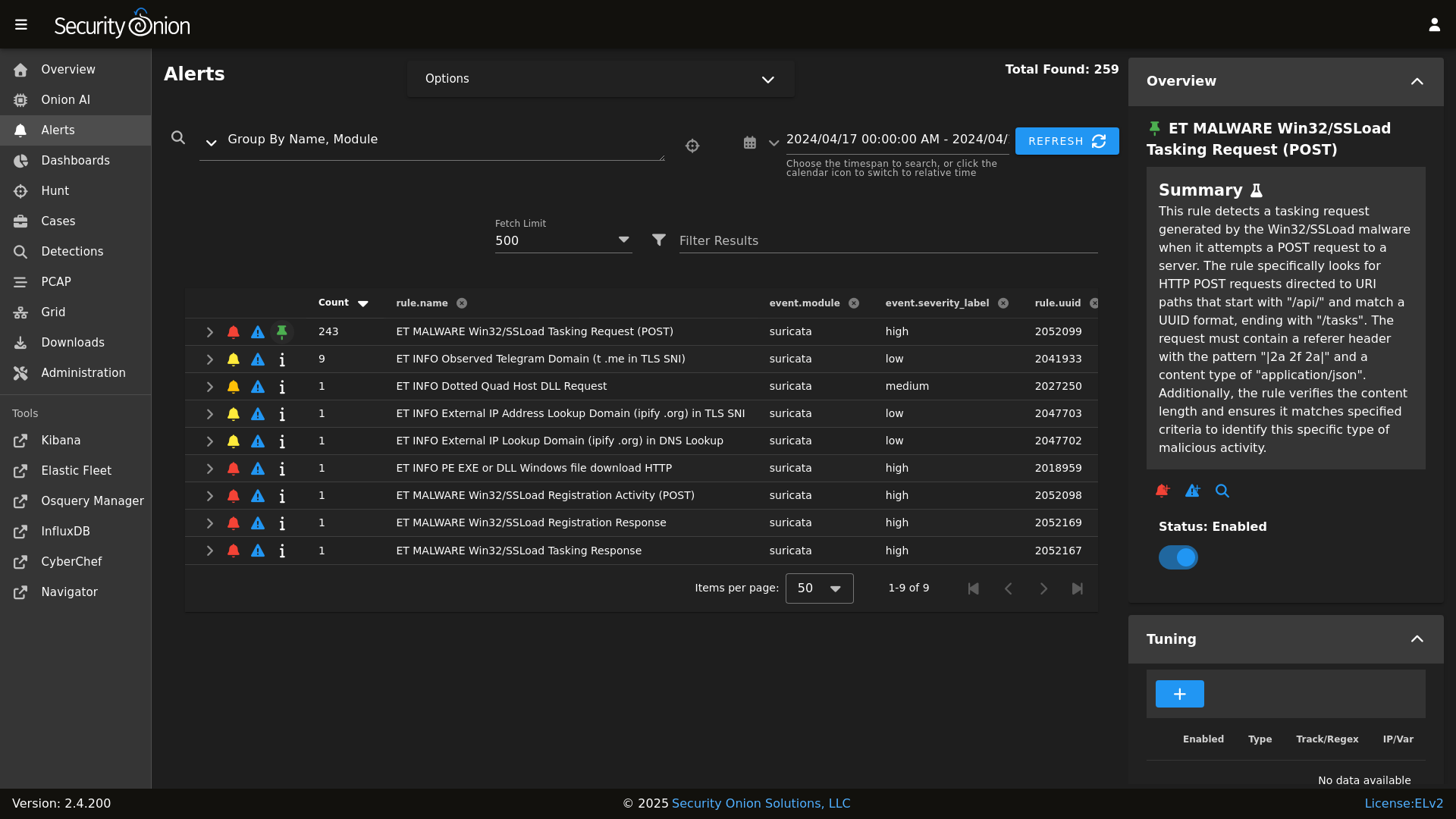
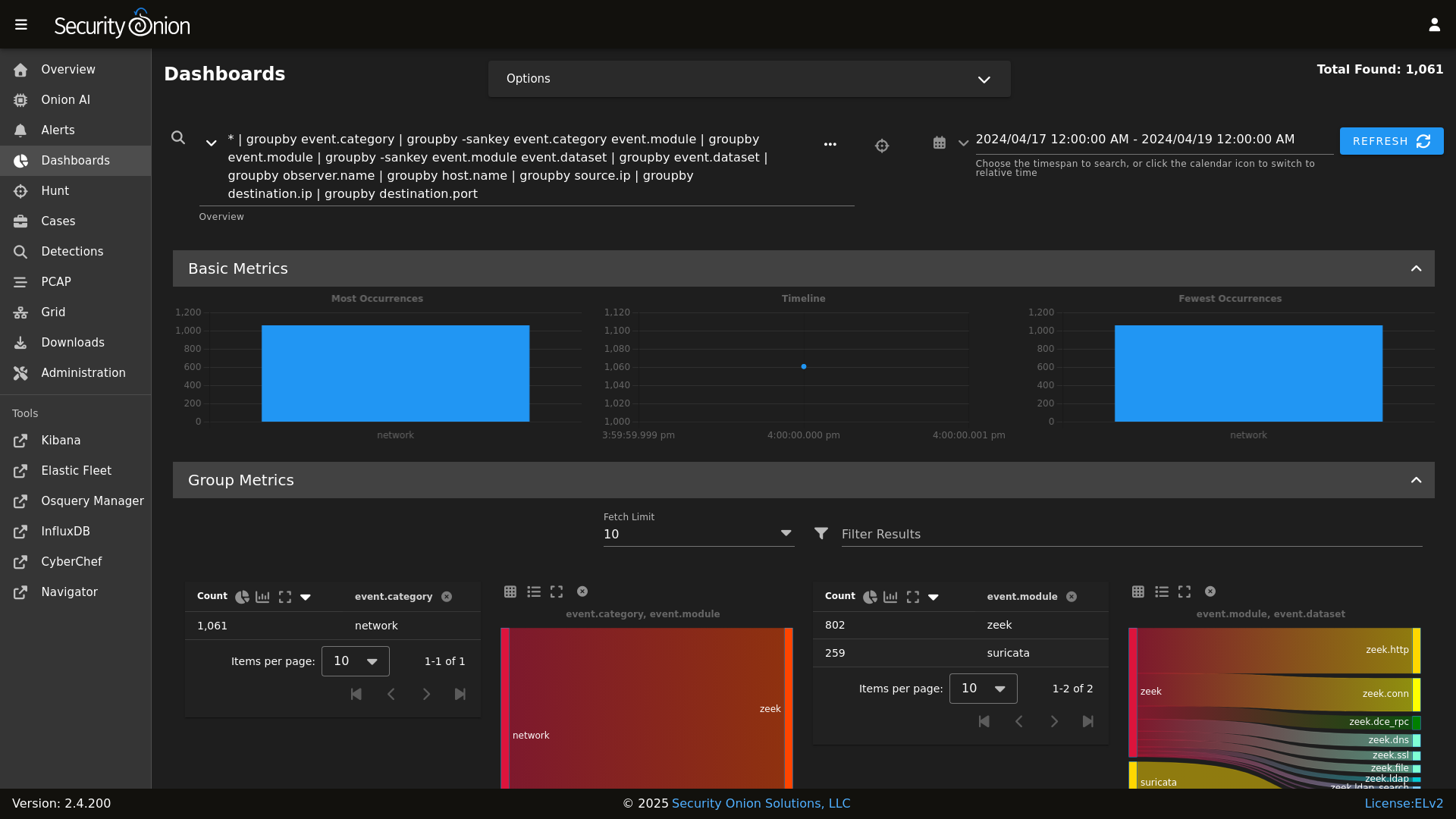
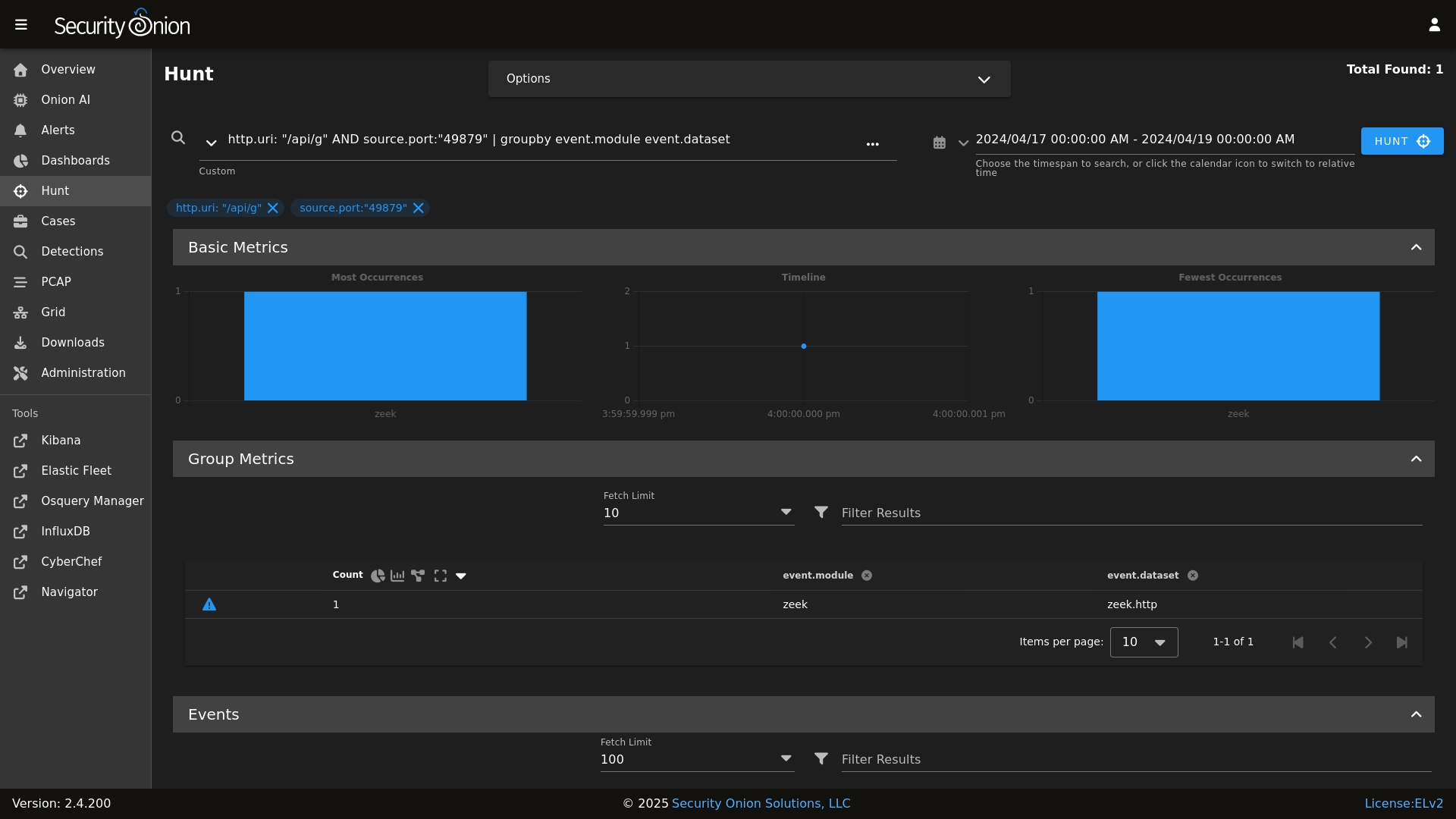
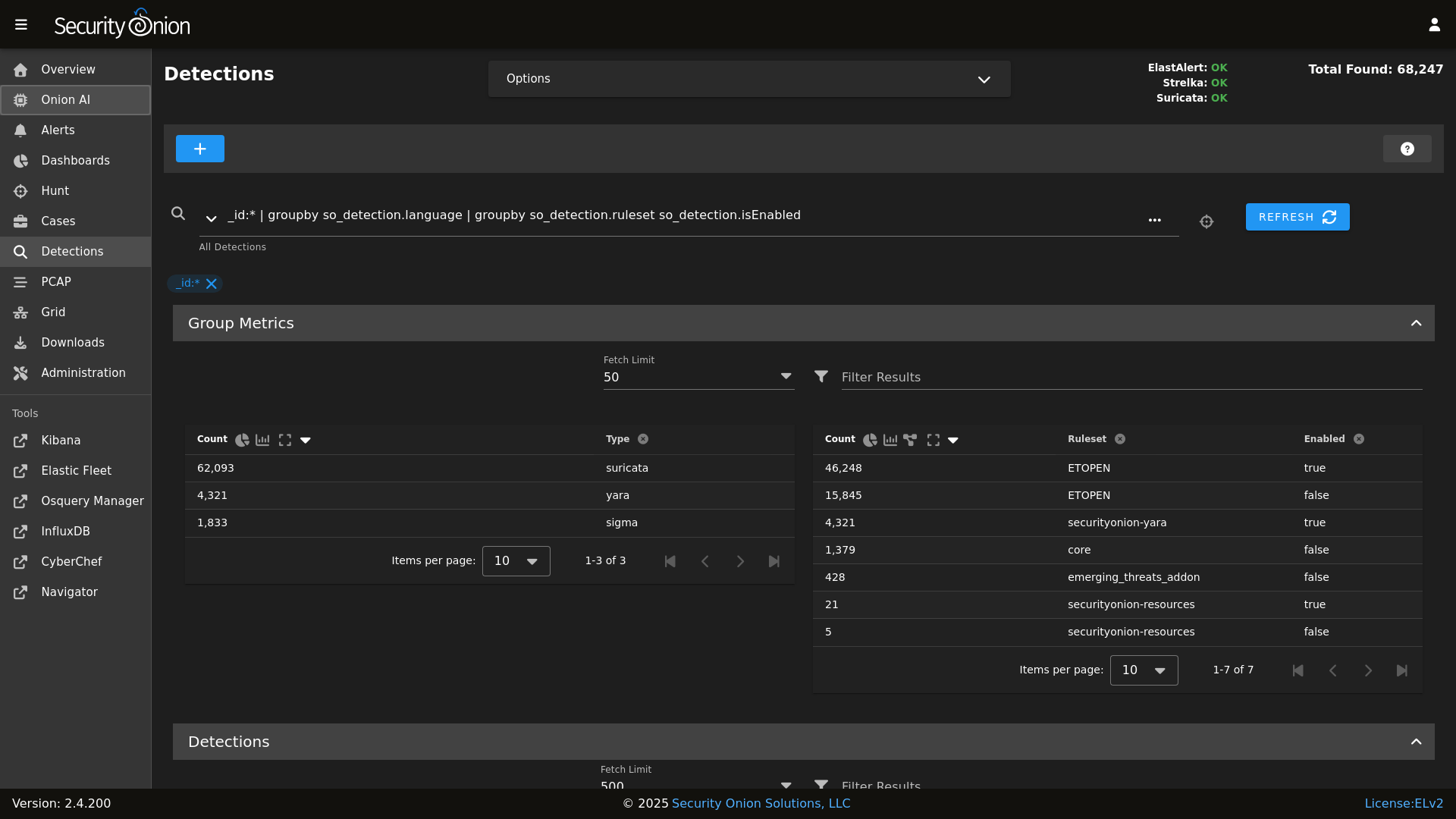
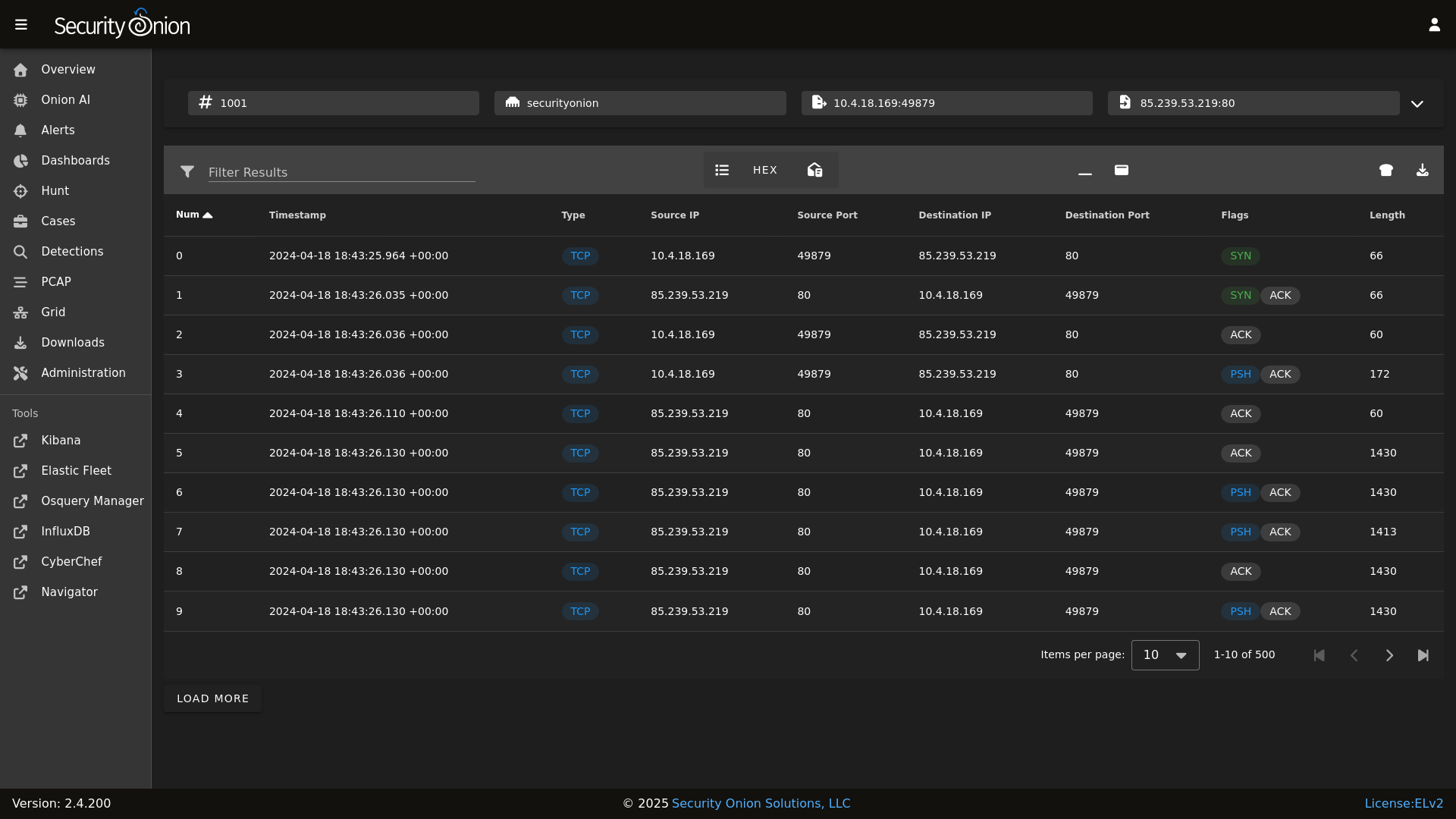
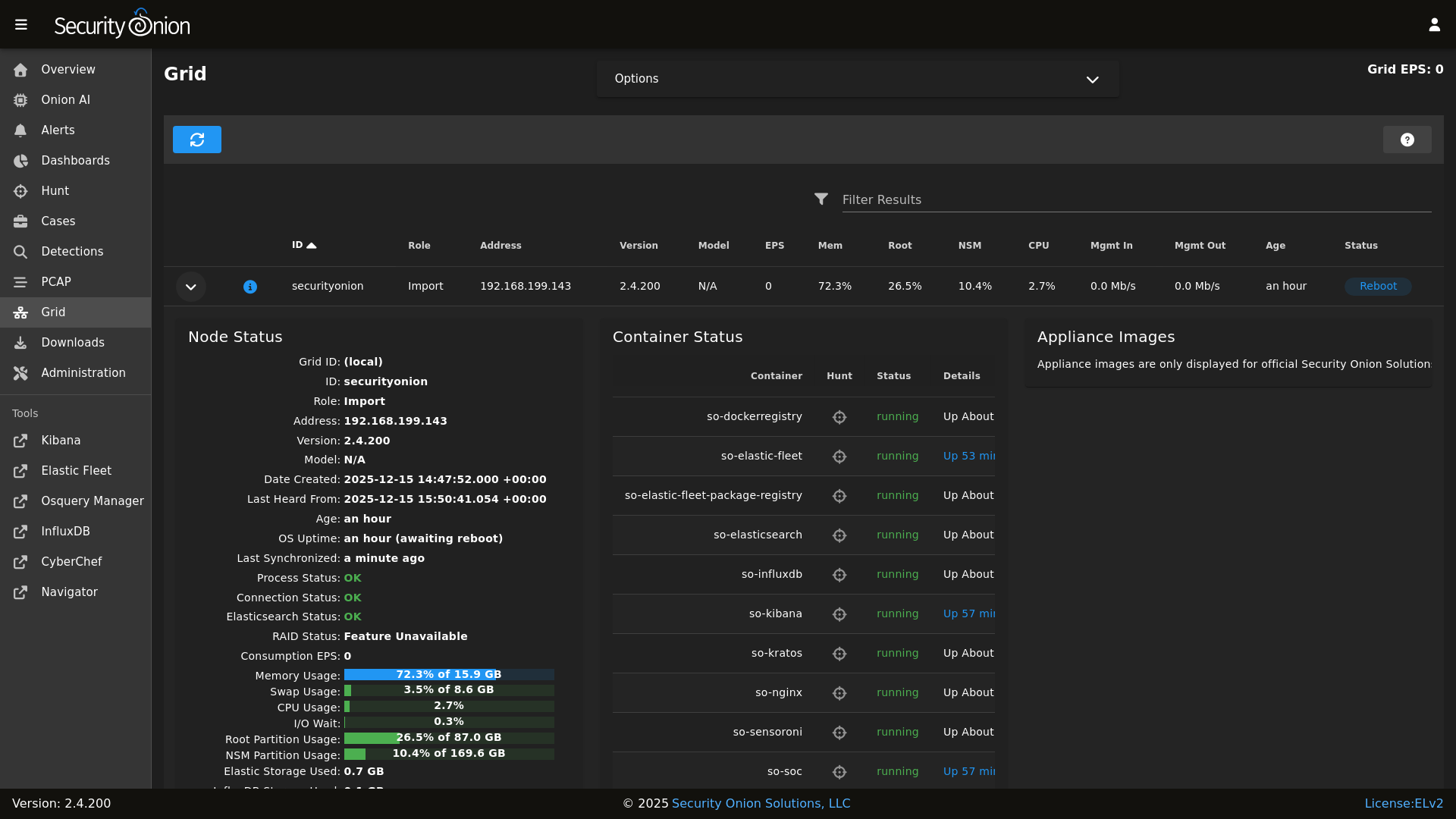
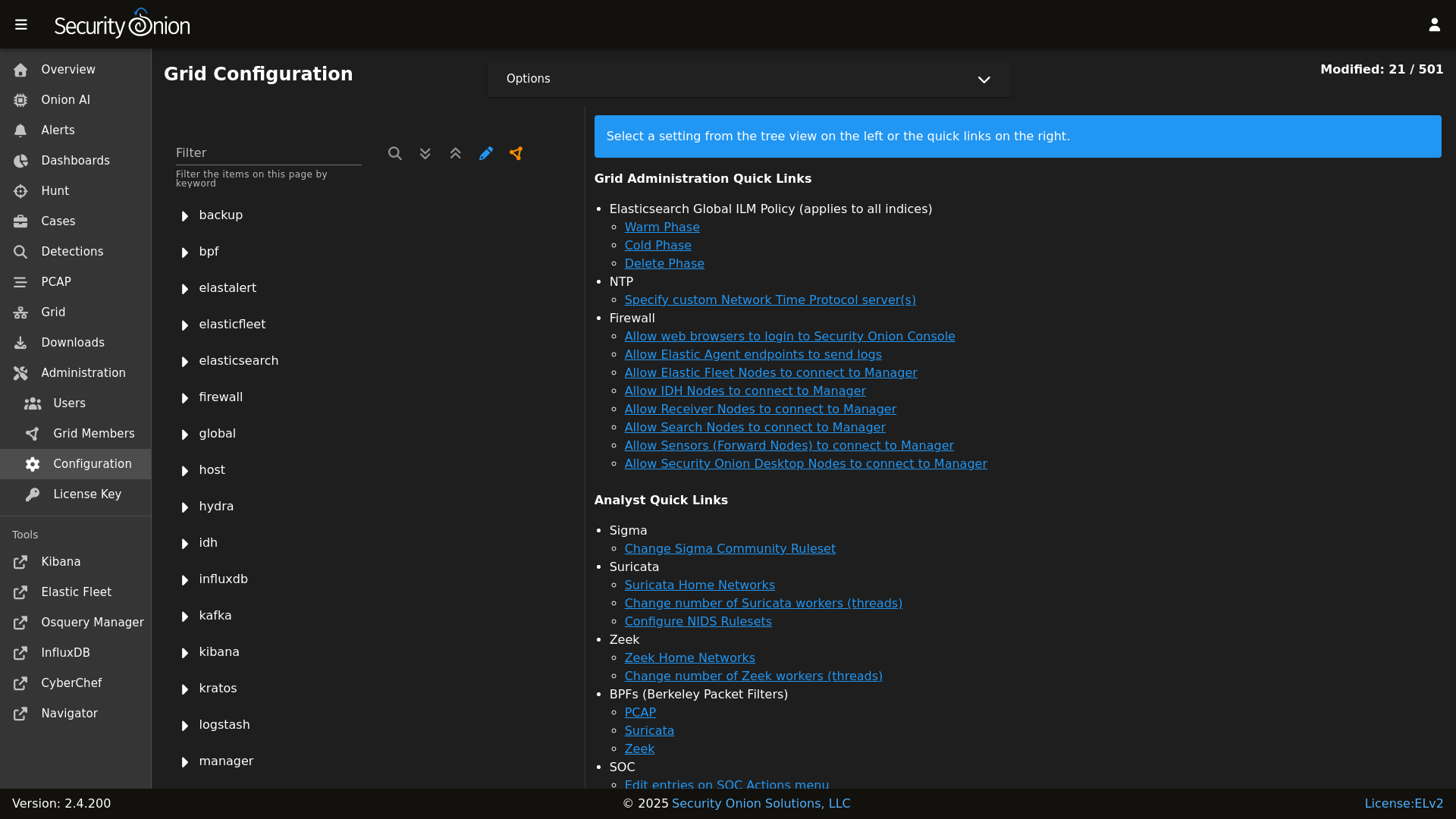
## Screenshots
|
||||
|
||||
## ✨ Features
|
||||
Alerts
|
||||
|
||||
|
||||
Security Onion includes everything you need to monitor your network and host systems:
|
||||
Dashboards
|
||||
|
||||
|
||||
* **Security Onion Console (SOC)**: A unified web interface for analyzing security events and managing your grid.
|
||||
* **Elastic Stack**: Powerful search backed by Elasticsearch.
|
||||
* **Intrusion Detection**: Network-based IDS with Suricata and host-based monitoring with Elastic Fleet.
|
||||
* **Network Metadata**: Detailed network metadata generated by Zeek or Suricata.
|
||||
* **Full Packet Capture**: Retain and analyze raw network traffic with Suricata PCAP.
|
||||
Hunt
|
||||
|
||||
|
||||
## ⭐ Security Onion Pro
|
||||
Detections
|
||||
|
||||
|
||||
For organizations and enterprises requiring advanced capabilities, **Security Onion Pro** offers additional features designed for scale and efficiency:
|
||||
PCAP
|
||||
|
||||
|
||||
* **Onion AI**: Leverage powerful AI-driven insights to accelerate your analysis and investigations.
|
||||
* **Enterprise Features**: Enhanced tools and integrations tailored for enterprise-grade security operations.
|
||||
Grid
|
||||
|
||||
|
||||
For more information, visit the [Security Onion Pro](https://securityonionsolutions.com/pro) page.
|
||||
Config
|
||||
|
||||
|
||||
## ☁️ Cloud Deployment
|
||||
### Release Notes
|
||||
|
||||
Security Onion is available and ready to deploy in the **AWS**, **Azure**, and **Google Cloud (GCP)** marketplaces.
|
||||
https://securityonion.net/docs/release-notes
|
||||
|
||||
## 🚀 Getting Started
|
||||
### Requirements
|
||||
|
||||
| Goal | Resource |
|
||||
| :--- | :--- |
|
||||
| **Download** | [Security Onion ISO](https://securityonion.net/docs/download) |
|
||||
| **Requirements** | [Hardware Guide](https://securityonion.net/docs/hardware) |
|
||||
| **Install** | [Installation Instructions](https://securityonion.net/docs/installation) |
|
||||
| **What's New** | [Release Notes](https://securityonion.net/docs/release-notes) |
|
||||
https://securityonion.net/docs/hardware
|
||||
|
||||
## 📖 Documentation & Support
|
||||
### Download
|
||||
|
||||
For more detailed information, please visit our [Documentation](https://docs.securityonion.net).
|
||||
https://securityonion.net/docs/download
|
||||
|
||||
* **FAQ**: [Frequently Asked Questions](https://securityonion.net/docs/faq)
|
||||
* **Community**: [Discussions & Support](https://securityonion.net/docs/community-support)
|
||||
* **Training**: [Official Training](https://securityonion.net/training)
|
||||
### Installation
|
||||
|
||||
## 🤝 Contributing
|
||||
https://securityonion.net/docs/installation
|
||||
|
||||
We welcome contributions! Please see our [CONTRIBUTING.md](CONTRIBUTING.md) for guidelines on how to get involved.
|
||||
### FAQ
|
||||
|
||||
## 🛡️ License
|
||||
https://securityonion.net/docs/faq
|
||||
|
||||
Security Onion is licensed under the terms of the license found in the [LICENSE](LICENSE) file.
|
||||
### Feedback
|
||||
|
||||
---
|
||||
*Built with 🧅 by Security Onion Solutions.*
|
||||
https://securityonion.net/docs/community-support
|
||||
|
||||
@@ -4,7 +4,6 @@
|
||||
|
||||
| Version | Supported |
|
||||
| ------- | ------------------ |
|
||||
| 3.x | :white_check_mark: |
|
||||
| 2.4.x | :white_check_mark: |
|
||||
| 2.3.x | :x: |
|
||||
| 16.04.x | :x: |
|
||||
|
||||
@@ -3,6 +3,8 @@
|
||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||
# Elastic License 2.0.
|
||||
|
||||
{% if '2.4' in salt['cp.get_file_str']('/etc/soversion') %}
|
||||
|
||||
{% import_yaml '/opt/so/saltstack/local/pillar/global/soc_global.sls' as SOC_GLOBAL %}
|
||||
{% if SOC_GLOBAL.global.airgap %}
|
||||
{% set UPDATE_DIR='/tmp/soagupdate/SecurityOnion' %}
|
||||
@@ -118,3 +120,23 @@ copy_bootstrap-salt_sbin:
|
||||
- source: {{UPDATE_DIR}}/salt/salt/scripts/bootstrap-salt.sh
|
||||
- force: True
|
||||
- preserve: True
|
||||
|
||||
{# this is added in 2.4.120 to remove salt repo files pointing to saltproject.io to accomodate the move to broadcom and new bootstrap-salt script #}
|
||||
{% if salt['pkg.version_cmp'](SOVERSION, '2.4.120') == -1 %}
|
||||
{% set saltrepofile = '/etc/yum.repos.d/salt.repo' %}
|
||||
{% if grains.os_family == 'Debian' %}
|
||||
{% set saltrepofile = '/etc/apt/sources.list.d/salt.list' %}
|
||||
{% endif %}
|
||||
remove_saltproject_io_repo_manager:
|
||||
file.absent:
|
||||
- name: {{ saltrepofile }}
|
||||
{% endif %}
|
||||
|
||||
{% else %}
|
||||
fix_23_soup_sbin:
|
||||
cmd.run:
|
||||
- name: curl -s -f -o /usr/sbin/soup https://raw.githubusercontent.com/Security-Onion-Solutions/securityonion/2.3/main/salt/common/tools/sbin/soup
|
||||
fix_23_soup_salt:
|
||||
cmd.run:
|
||||
- name: curl -s -f -o /opt/so/saltstack/defalt/salt/common/tools/sbin/soup https://raw.githubusercontent.com/Security-Onion-Solutions/securityonion/2.3/main/salt/common/tools/sbin/soup
|
||||
{% endif %}
|
||||
|
||||
@@ -333,8 +333,8 @@ get_elastic_agent_vars() {
|
||||
|
||||
if [ -f "$defaultsfile" ]; then
|
||||
ELASTIC_AGENT_TARBALL_VERSION=$(egrep " +version: " $defaultsfile | awk -F: '{print $2}' | tr -d '[:space:]')
|
||||
ELASTIC_AGENT_URL="https://repo.securityonion.net/file/so-repo/prod/3/elasticagent/elastic-agent_SO-$ELASTIC_AGENT_TARBALL_VERSION.tar.gz"
|
||||
ELASTIC_AGENT_MD5_URL="https://repo.securityonion.net/file/so-repo/prod/3/elasticagent/elastic-agent_SO-$ELASTIC_AGENT_TARBALL_VERSION.md5"
|
||||
ELASTIC_AGENT_URL="https://repo.securityonion.net/file/so-repo/prod/2.4/elasticagent/elastic-agent_SO-$ELASTIC_AGENT_TARBALL_VERSION.tar.gz"
|
||||
ELASTIC_AGENT_MD5_URL="https://repo.securityonion.net/file/so-repo/prod/2.4/elasticagent/elastic-agent_SO-$ELASTIC_AGENT_TARBALL_VERSION.md5"
|
||||
ELASTIC_AGENT_FILE="/nsm/elastic-fleet/artifacts/elastic-agent_SO-$ELASTIC_AGENT_TARBALL_VERSION.tar.gz"
|
||||
ELASTIC_AGENT_MD5="/nsm/elastic-fleet/artifacts/elastic-agent_SO-$ELASTIC_AGENT_TARBALL_VERSION.md5"
|
||||
ELASTIC_AGENT_EXPANSION_DIR=/nsm/elastic-fleet/artifacts/beats/elastic-agent
|
||||
|
||||
@@ -10,7 +10,7 @@
|
||||
|
||||
vm.max_map_count:
|
||||
sysctl.present:
|
||||
- value: 262144
|
||||
- value: {{ ELASTICSEARCHMERGED.vm.max_map_count }}
|
||||
|
||||
# Add ES Group
|
||||
elasticsearchgroup:
|
||||
|
||||
@@ -2,6 +2,8 @@ elasticsearch:
|
||||
enabled: false
|
||||
version: 9.0.8
|
||||
index_clean: true
|
||||
vm:
|
||||
max_map_count: 1048576
|
||||
config:
|
||||
action:
|
||||
destructive_requires_name: true
|
||||
|
||||
@@ -15,6 +15,11 @@ elasticsearch:
|
||||
description: Determines if indices should be considered for deletion by available disk space in the cluster. Otherwise, indices will only be deleted by the age defined in the ILM settings. This setting only applies to EVAL, STANDALONE, and HEAVY NODE installations. Other installations can only use ILM settings.
|
||||
forcedType: bool
|
||||
helpLink: elasticsearch.html
|
||||
vm:
|
||||
max_map_count:
|
||||
description: The maximum number of memory map areas a process may use. Elasticsearch uses a mmapfs directory by default to store its indices. The default operating system limits on mmap counts could be too low, which may result in out of memory exceptions.
|
||||
forcedType: int
|
||||
helpLink: elasticsearch.html
|
||||
retention:
|
||||
retention_pct:
|
||||
decription: Total percentage of space used by Elasticsearch for multi node clusters
|
||||
|
||||
@@ -1,2 +1,2 @@
|
||||
https://repo.securityonion.net/file/so-repo/prod/3/oracle/9
|
||||
https://repo-alt.securityonion.net/prod/3/oracle/9
|
||||
https://repo.securityonion.net/file/so-repo/prod/2.4/oracle/9
|
||||
https://repo-alt.securityonion.net/prod/2.4/oracle/9
|
||||
@@ -143,7 +143,7 @@ show_usage() {
|
||||
echo " -v Show verbose output (files changed/added/deleted)"
|
||||
echo " -vv Show very verbose output (includes file diffs)"
|
||||
echo " --test Test mode - show what would change without making changes"
|
||||
echo " branch Git branch to checkout (default: 3/main)"
|
||||
echo " branch Git branch to checkout (default: 2.4/main)"
|
||||
echo ""
|
||||
echo "Examples:"
|
||||
echo " $0 # Normal operation"
|
||||
@@ -193,7 +193,7 @@ done
|
||||
|
||||
# Set default branch if not provided
|
||||
if [ -z "$BRANCH" ]; then
|
||||
BRANCH=3/main
|
||||
BRANCH=2.4/main
|
||||
fi
|
||||
|
||||
got_root
|
||||
|
||||
184
salt/manager/tools/sbin/soupto3
Executable file
184
salt/manager/tools/sbin/soupto3
Executable file
@@ -0,0 +1,184 @@
|
||||
#!/bin/bash
|
||||
|
||||
# Copyright Security Onion Solutions LLC and/or licensed to Security Onion Solutions LLC under one
|
||||
# or more contributor license agreements. Licensed under the Elastic License 2.0 as shown at
|
||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||
# Elastic License 2.0.
|
||||
|
||||
|
||||
. /usr/sbin/so-common
|
||||
|
||||
UPDATE_URL=https://raw.githubusercontent.com/Security-Onion-Solutions/securityonion/refs/heads/3/main/VERSION
|
||||
|
||||
# Check if already running version 3
|
||||
CURRENT_VERSION=$(cat /etc/soversion 2>/dev/null)
|
||||
if [[ "$CURRENT_VERSION" =~ ^3\. ]]; then
|
||||
echo ""
|
||||
echo "========================================================================="
|
||||
echo " Already Running Security Onion 3"
|
||||
echo "========================================================================="
|
||||
echo ""
|
||||
echo " This system is already running Security Onion $CURRENT_VERSION."
|
||||
echo " Use 'soup' to update within the 3.x release line."
|
||||
echo ""
|
||||
exit 0
|
||||
fi
|
||||
|
||||
echo ""
|
||||
echo "Checking PCAP settings."
|
||||
echo ""
|
||||
|
||||
# Check pcapengine setting - must be SURICATA before upgrading to version 3
|
||||
PCAP_ENGINE=$(lookup_pillar "pcapengine")
|
||||
|
||||
PCAP_DELETED=false
|
||||
|
||||
prompt_delete_pcap() {
|
||||
read -rp " Would you like to delete all remaining Stenographer PCAP data? (y/N): " DELETE_PCAP
|
||||
if [[ "$DELETE_PCAP" =~ ^[Yy]$ ]]; then
|
||||
echo ""
|
||||
echo " WARNING: This will permanently delete all Stenographer PCAP data"
|
||||
echo " on all nodes. This action cannot be undone."
|
||||
echo ""
|
||||
read -rp " Are you sure? (y/N): " CONFIRM_DELETE
|
||||
if [[ "$CONFIRM_DELETE" =~ ^[Yy]$ ]]; then
|
||||
echo ""
|
||||
echo " Deleting Stenographer PCAP data on all nodes..."
|
||||
salt '*' cmd.run "rm -rf /nsm/pcap/* && rm -rf /nsm/pcapindex/*"
|
||||
echo " Done."
|
||||
PCAP_DELETED=true
|
||||
else
|
||||
echo ""
|
||||
echo " Delete cancelled."
|
||||
fi
|
||||
fi
|
||||
}
|
||||
|
||||
pcapengine_not_changed() {
|
||||
echo ""
|
||||
echo " PCAP engine must be set to SURICATA before upgrading to Security Onion 3."
|
||||
echo " You can change this in SOC by navigating to:"
|
||||
echo " Configuration -> global -> pcapengine"
|
||||
}
|
||||
|
||||
prompt_change_engine() {
|
||||
local current_engine=$1
|
||||
echo ""
|
||||
read -rp " Would you like to change the PCAP engine to SURICATA now? (y/N): " CHANGE_ENGINE
|
||||
if [[ "$CHANGE_ENGINE" =~ ^[Yy]$ ]]; then
|
||||
if [[ "$PCAP_DELETED" != "true" ]]; then
|
||||
echo ""
|
||||
echo " WARNING: Stenographer PCAP data was not deleted. If you proceed,"
|
||||
echo " this data will no longer be accessible through SOC and will never"
|
||||
echo " be automatically deleted. You will need to manually remove it later."
|
||||
echo ""
|
||||
read -rp " Continue with changing pcapengine to SURICATA? (y/N): " CONFIRM_CHANGE
|
||||
if [[ ! "$CONFIRM_CHANGE" =~ ^[Yy]$ ]]; then
|
||||
pcapengine_not_changed
|
||||
return 1
|
||||
fi
|
||||
fi
|
||||
echo ""
|
||||
echo " Updating PCAP engine to SURICATA..."
|
||||
so-yaml.py replace /opt/so/saltstack/local/pillar/global/soc_global.sls global.pcapengine SURICATA
|
||||
echo " Done."
|
||||
return 0
|
||||
else
|
||||
pcapengine_not_changed
|
||||
return 1
|
||||
fi
|
||||
}
|
||||
|
||||
case "$PCAP_ENGINE" in
|
||||
SURICATA)
|
||||
echo "PCAP engine settings OK."
|
||||
;;
|
||||
TRANSITION|STENO)
|
||||
echo ""
|
||||
echo "========================================================================="
|
||||
echo " PCAP Engine Check Failed"
|
||||
echo "========================================================================="
|
||||
echo ""
|
||||
echo " Your PCAP engine is currently set to $PCAP_ENGINE."
|
||||
echo ""
|
||||
echo " Before upgrading to Security Onion 3, Stenographer PCAP data must be"
|
||||
echo " removed and the PCAP engine must be set to SURICATA."
|
||||
echo ""
|
||||
echo " To check remaining Stenographer PCAP usage, run:"
|
||||
echo " salt '*' cmd.run 'du -sh /nsm/pcap'"
|
||||
echo ""
|
||||
|
||||
prompt_delete_pcap
|
||||
if ! prompt_change_engine "$PCAP_ENGINE"; then
|
||||
echo ""
|
||||
exit 1
|
||||
fi
|
||||
;;
|
||||
*)
|
||||
echo ""
|
||||
echo "========================================================================="
|
||||
echo " PCAP Engine Check Failed"
|
||||
echo "========================================================================="
|
||||
echo ""
|
||||
echo " Unable to determine the PCAP engine setting (got: '$PCAP_ENGINE')."
|
||||
echo " Please ensure the PCAP engine is set to SURICATA."
|
||||
echo " In SOC, navigate to Configuration -> global -> pcapengine"
|
||||
echo " and change the value to SURICATA."
|
||||
echo ""
|
||||
exit 1
|
||||
;;
|
||||
esac
|
||||
|
||||
echo ""
|
||||
echo "Checking Versions."
|
||||
echo ""
|
||||
|
||||
# Check if Security Onion 3 has been released
|
||||
VERSION=$(curl -sSf "$UPDATE_URL" 2>/dev/null)
|
||||
|
||||
if [[ -z "$VERSION" ]]; then
|
||||
echo ""
|
||||
echo "========================================================================="
|
||||
echo " Unable to Check Version"
|
||||
echo "========================================================================="
|
||||
echo ""
|
||||
echo " Could not retrieve version information from:"
|
||||
echo " $UPDATE_URL"
|
||||
echo ""
|
||||
echo " Please check your network connection and try again."
|
||||
echo ""
|
||||
exit 1
|
||||
fi
|
||||
|
||||
if [[ "$VERSION" == "UNRELEASED" ]]; then
|
||||
echo ""
|
||||
echo "========================================================================="
|
||||
echo " Security Onion 3 Not Available"
|
||||
echo "========================================================================="
|
||||
echo ""
|
||||
echo " Security Onion 3 has not been released yet."
|
||||
echo ""
|
||||
echo " Please check back later or visit https://securityonion.net for updates."
|
||||
echo ""
|
||||
exit 1
|
||||
fi
|
||||
|
||||
# Validate version format (e.g., 3.0.2)
|
||||
if [[ ! "$VERSION" =~ ^[0-9]+\.[0-9]+\.[0-9]+$ ]]; then
|
||||
echo ""
|
||||
echo "========================================================================="
|
||||
echo " Invalid Version"
|
||||
echo "========================================================================="
|
||||
echo ""
|
||||
echo " Received unexpected version format: '$VERSION'"
|
||||
echo ""
|
||||
echo " Please check back later or visit https://securityonion.net for updates."
|
||||
echo ""
|
||||
exit 1
|
||||
fi
|
||||
|
||||
echo "Security Onion 3 ($VERSION) is available. Upgrading..."
|
||||
echo ""
|
||||
|
||||
# All checks passed - proceed with upgrade
|
||||
BRANCH=3/main soup
|
||||
@@ -3,7 +3,6 @@ nginx:
|
||||
external_suricata: False
|
||||
ssl:
|
||||
replace_cert: False
|
||||
alt_names: []
|
||||
config:
|
||||
throttle_login_burst: 12
|
||||
throttle_login_rate: 20
|
||||
|
||||
@@ -60,8 +60,6 @@ http {
|
||||
{%- endif %}
|
||||
|
||||
{%- if GLOBALS.is_manager %}
|
||||
{%- set all_names = [GLOBALS.hostname, GLOBALS.url_base] + NGINXMERGED.ssl.alt_names %}
|
||||
{%- set full_server_name = all_names | unique | join(' ') %}
|
||||
|
||||
server {
|
||||
listen 80 default_server;
|
||||
@@ -71,7 +69,7 @@ http {
|
||||
|
||||
server {
|
||||
listen 8443;
|
||||
server_name {{ full_server_name }};
|
||||
server_name {{ GLOBALS.url_base }};
|
||||
root /opt/socore/html;
|
||||
location /artifacts/ {
|
||||
try_files $uri =206;
|
||||
@@ -114,7 +112,7 @@ http {
|
||||
|
||||
server {
|
||||
listen 7788;
|
||||
server_name {{ full_server_name }};
|
||||
server_name {{ GLOBALS.url_base }};
|
||||
root /nsm/rules;
|
||||
location / {
|
||||
allow all;
|
||||
@@ -130,7 +128,7 @@ http {
|
||||
server {
|
||||
listen 7789 ssl;
|
||||
http2 on;
|
||||
server_name {{ full_server_name }};
|
||||
server_name {{ GLOBALS.url_base }};
|
||||
root /surirules;
|
||||
|
||||
add_header Content-Security-Policy "default-src 'self' 'unsafe-inline' 'unsafe-eval' https: data: blob: wss:; frame-ancestors 'self'";
|
||||
@@ -163,7 +161,7 @@ http {
|
||||
server {
|
||||
listen 443 ssl;
|
||||
http2 on;
|
||||
server_name {{ full_server_name }};
|
||||
server_name {{ GLOBALS.url_base }};
|
||||
root /opt/socore/html;
|
||||
index index.html;
|
||||
|
||||
|
||||
@@ -30,12 +30,6 @@ nginx:
|
||||
advanced: True
|
||||
global: True
|
||||
helpLink: nginx.html
|
||||
alt_names:
|
||||
description: Provide a list of alternate names to allow remote systems the ability to refer to the SOC API as another hostname.
|
||||
global: True
|
||||
forcedType: '[]string'
|
||||
multiline: True
|
||||
helpLink: nginx.html
|
||||
config:
|
||||
throttle_login_burst:
|
||||
description: Number of login requests that can burst without triggering request throttling. Higher values allow more repeated login attempts. Values greater than zero are required in order to provide a usable login flow.
|
||||
|
||||
@@ -49,17 +49,6 @@ managerssl_key:
|
||||
- docker_container: so-nginx
|
||||
|
||||
# Create a cert for the reverse proxy
|
||||
{% set san_list = [GLOBALS.hostname, GLOBALS.node_ip, GLOBALS.url_base] + NGINXMERGED.ssl.alt_names %}
|
||||
{% set unique_san_list = san_list | unique %}
|
||||
{% set managerssl_san_list = [] %}
|
||||
{% for item in unique_san_list %}
|
||||
{% if item | ipaddr %}
|
||||
{% do managerssl_san_list.append("IP:" + item) %}
|
||||
{% else %}
|
||||
{% do managerssl_san_list.append("DNS:" + item) %}
|
||||
{% endif %}
|
||||
{% endfor %}
|
||||
{% set managerssl_san = managerssl_san_list | join(', ') %}
|
||||
managerssl_crt:
|
||||
x509.certificate_managed:
|
||||
- name: /etc/pki/managerssl.crt
|
||||
@@ -67,7 +56,7 @@ managerssl_crt:
|
||||
- signing_policy: managerssl
|
||||
- private_key: /etc/pki/managerssl.key
|
||||
- CN: {{ GLOBALS.hostname }}
|
||||
- subjectAltName: {{ managerssl_san }}
|
||||
- subjectAltName: "DNS:{{ GLOBALS.hostname }}, IP:{{ GLOBALS.node_ip }}, DNS:{{ GLOBALS.url_base }}"
|
||||
- days_remaining: 7
|
||||
- days_valid: 820
|
||||
- backup: True
|
||||
|
||||
@@ -22,6 +22,18 @@ include:
|
||||
{% endif %}
|
||||
|
||||
{% if INSTALLEDSALTVERSION|string != SALTVERSION|string %}
|
||||
|
||||
{# this is added in 2.4.120 to remove salt repo files pointing to saltproject.io to accomodate the move to broadcom and new bootstrap-salt script #}
|
||||
{% if salt['pkg.version_cmp'](GLOBALS.so_version, '2.4.120') == -1 %}
|
||||
{% set saltrepofile = '/etc/yum.repos.d/salt.repo' %}
|
||||
{% if grains.os_family == 'Debian' %}
|
||||
{% set saltrepofile = '/etc/apt/sources.list.d/salt.list' %}
|
||||
{% endif %}
|
||||
remove_saltproject_io_repo_minion:
|
||||
file.absent:
|
||||
- name: {{ saltrepofile }}
|
||||
{% endif %}
|
||||
|
||||
unhold_salt_packages:
|
||||
pkg.unheld:
|
||||
- pkgs:
|
||||
|
||||
@@ -14,7 +14,7 @@ An API key or User Credentials is necessary for utilizing Elasticsearch.
|
||||
|
||||
In SOC, navigate to `Administration`, toggle `Show all configurable settings, including advanced settings.`, and navigate to `sensoroni` -> `analyzers` -> `elasticsearch`.
|
||||
|
||||

|
||||

|
||||
|
||||
|
||||
The following configuration options are available for:
|
||||
|
||||
@@ -6,7 +6,7 @@ Submit a base64-encoded EML file to Sublime Platform for analysis.
|
||||
## Configuration Requirements
|
||||
In SOC, navigate to `Administration`, toggle `Show all configurable settings, including advanced settings.`, and navigate to `sensoroni` -> `analyzers` -> `sublime_platform`.
|
||||
|
||||

|
||||

|
||||
|
||||
|
||||
The following configuration options are available for:
|
||||
|
||||
@@ -47,7 +47,7 @@ telegraf_key_perms:
|
||||
- group: 939
|
||||
|
||||
{% if not GLOBALS.is_manager %}
|
||||
{# Prior to 2.4.210, minions used influxdb.crt and key for telegraf #}
|
||||
{# Prior to 2.4.220, minions used influxdb.crt and key for telegraf #}
|
||||
remove_influxdb.crt:
|
||||
file.absent:
|
||||
- name: /etc/pki/influxdb.crt
|
||||
|
||||
@@ -1798,8 +1798,8 @@ securityonion_repo() {
|
||||
if ! $is_desktop_grid; then
|
||||
gpg_rpm_import
|
||||
if [[ ! $is_airgap ]]; then
|
||||
echo "https://repo.securityonion.net/file/so-repo/prod/3/oracle/9" > /etc/yum/mirror.txt
|
||||
echo "https://so-repo-east.s3.us-east-005.backblazeb2.com/prod/3/oracle/9" >> /etc/yum/mirror.txt
|
||||
echo "https://repo.securityonion.net/file/so-repo/prod/2.4/oracle/9" > /etc/yum/mirror.txt
|
||||
echo "https://so-repo-east.s3.us-east-005.backblazeb2.com/prod/2.4/oracle/9" >> /etc/yum/mirror.txt
|
||||
echo "[main]" > /etc/yum.repos.d/securityonion.repo
|
||||
echo "gpgcheck=1" >> /etc/yum.repos.d/securityonion.repo
|
||||
echo "installonly_limit=3" >> /etc/yum.repos.d/securityonion.repo
|
||||
@@ -1857,8 +1857,8 @@ repo_sync_local() {
|
||||
info "Adding Repo Download Configuration"
|
||||
mkdir -p /nsm/repo
|
||||
mkdir -p /opt/so/conf/reposync/cache
|
||||
echo "https://repo.securityonion.net/file/so-repo/prod/3/oracle/9" > /opt/so/conf/reposync/mirror.txt
|
||||
echo "https://repo-alt.securityonion.net/prod/3/oracle/9" >> /opt/so/conf/reposync/mirror.txt
|
||||
echo "https://repo.securityonion.net/file/so-repo/prod/2.4/oracle/9" > /opt/so/conf/reposync/mirror.txt
|
||||
echo "https://repo-alt.securityonion.net/prod/2.4/oracle/9" >> /opt/so/conf/reposync/mirror.txt
|
||||
echo "[main]" > /opt/so/conf/reposync/repodownload.conf
|
||||
echo "gpgcheck=1" >> /opt/so/conf/reposync/repodownload.conf
|
||||
echo "installonly_limit=3" >> /opt/so/conf/reposync/repodownload.conf
|
||||
@@ -1895,7 +1895,7 @@ repo_sync_local() {
|
||||
logCmd "dnf -y install epel-release"
|
||||
fi
|
||||
dnf install -y yum-utils device-mapper-persistent-data lvm2
|
||||
curl -fsSL https://repo.securityonion.net/file/so-repo/prod/3/so/so.repo | tee /etc/yum.repos.d/so.repo
|
||||
curl -fsSL https://repo.securityonion.net/file/so-repo/prod/2.4/so/so.repo | tee /etc/yum.repos.d/so.repo
|
||||
rpm --import https://packages.broadcom.com/artifactory/api/security/keypair/SaltProjectKey/public
|
||||
dnf config-manager --add-repo https://download.docker.com/linux/centos/docker-ce.repo
|
||||
curl -fsSL "https://github.com/saltstack/salt-install-guide/releases/latest/download/salt.repo" | tee /etc/yum.repos.d/salt.repo
|
||||
|
||||
Reference in New Issue
Block a user