mirror of
https://github.com/Security-Onion-Solutions/securityonion.git
synced 2026-05-09 04:42:40 +02:00
Compare commits
21 Commits
| Author | SHA1 | Date | |
|---|---|---|---|
| a3720219d8 | |||
| 385726b87c | |||
| ad960c2101 | |||
| 7f07c96a2f | |||
| 90bea975d0 | |||
| e8adea3022 | |||
| 71839bc87f | |||
| 7ac1e767ab | |||
| 2c4d833a5b | |||
| 41d3dd0aa5 | |||
| 6050ab6b21 | |||
| ae05251359 | |||
| f23158aed5 | |||
| b03b75315d | |||
| cbd98efaf4 | |||
| 1f7bf1fd88 | |||
| 179019b136 | |||
| ac022acbbe | |||
| 6bfe020c3b | |||
| 55a960bbc5 | |||
| 80f8fdc8d3 |
@@ -2,13 +2,11 @@ body:
|
||||
- type: markdown
|
||||
attributes:
|
||||
value: |
|
||||
⚠️ This category is solely for conversations related to Security Onion 2.4 ⚠️
|
||||
|
||||
If your organization needs more immediate, enterprise grade professional support, with one-on-one virtual meetings and screensharing, contact us via our website: https://securityonion.com/support
|
||||
- type: dropdown
|
||||
attributes:
|
||||
label: Version
|
||||
description: Which version of Security Onion 2.4.x are you asking about?
|
||||
description: Which version of Security Onion are you asking about?
|
||||
options:
|
||||
-
|
||||
- 2.4.10
|
||||
@@ -35,6 +33,7 @@ body:
|
||||
- 2.4.200
|
||||
- 2.4.201
|
||||
- 2.4.210
|
||||
- 3.0.0
|
||||
- Other (please provide detail below)
|
||||
validations:
|
||||
required: true
|
||||
|
||||
@@ -1,50 +1,58 @@
|
||||
## Security Onion 2.4
|
||||
<p align="center">
|
||||
<img src="https://securityonionsolutions.com/logo/logo-so-onion-dark.svg" width="400" alt="Security Onion Logo">
|
||||
</p>
|
||||
|
||||
Security Onion 2.4 is here!
|
||||
# Security Onion
|
||||
|
||||
## Screenshots
|
||||
Security Onion is a free and open Linux distribution for threat hunting, enterprise security monitoring, and log management. It includes a comprehensive suite of tools designed to work together to provide visibility into your network and host activity.
|
||||
|
||||
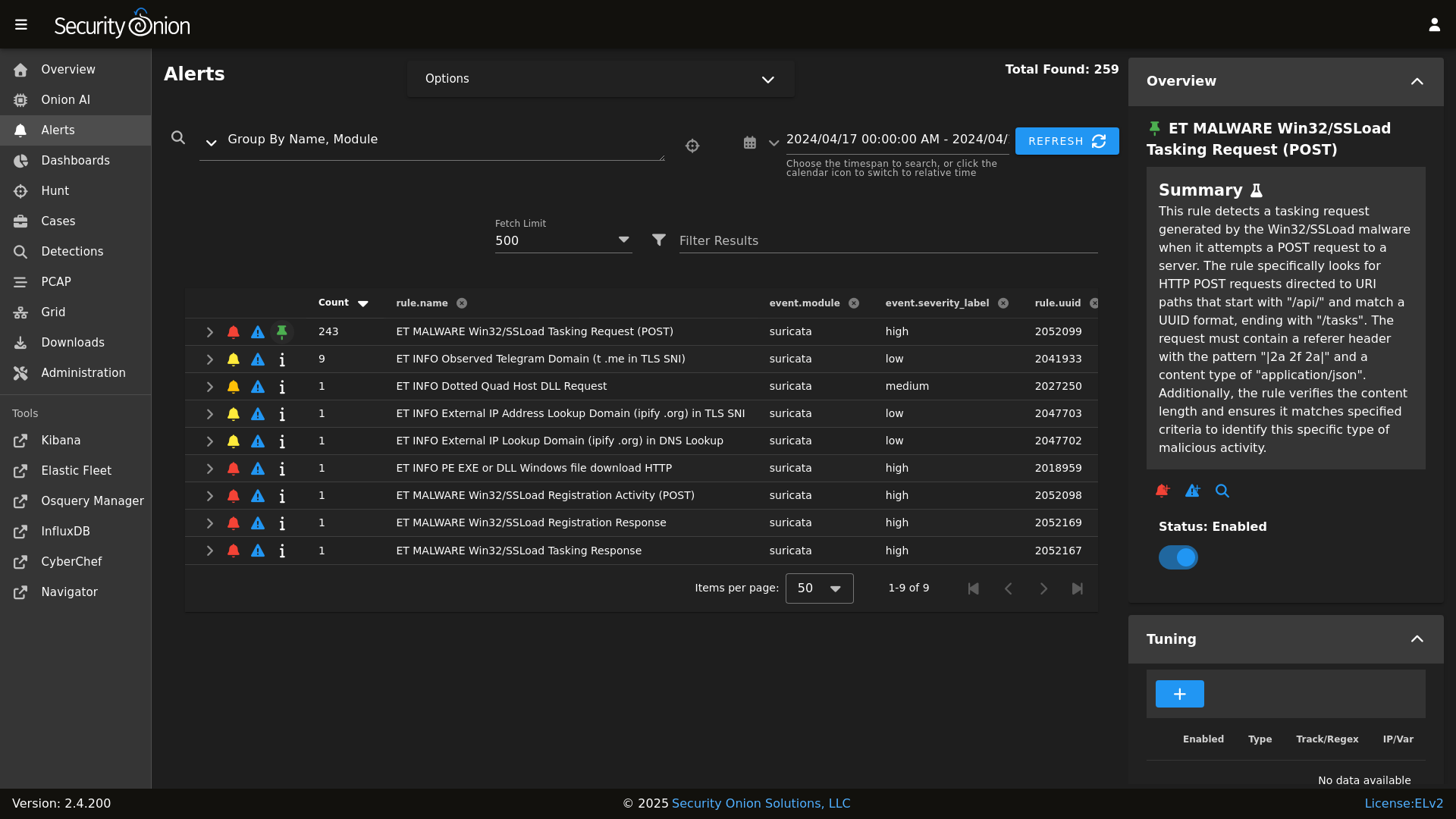
Alerts
|
||||
|
||||
## ✨ Features
|
||||
|
||||
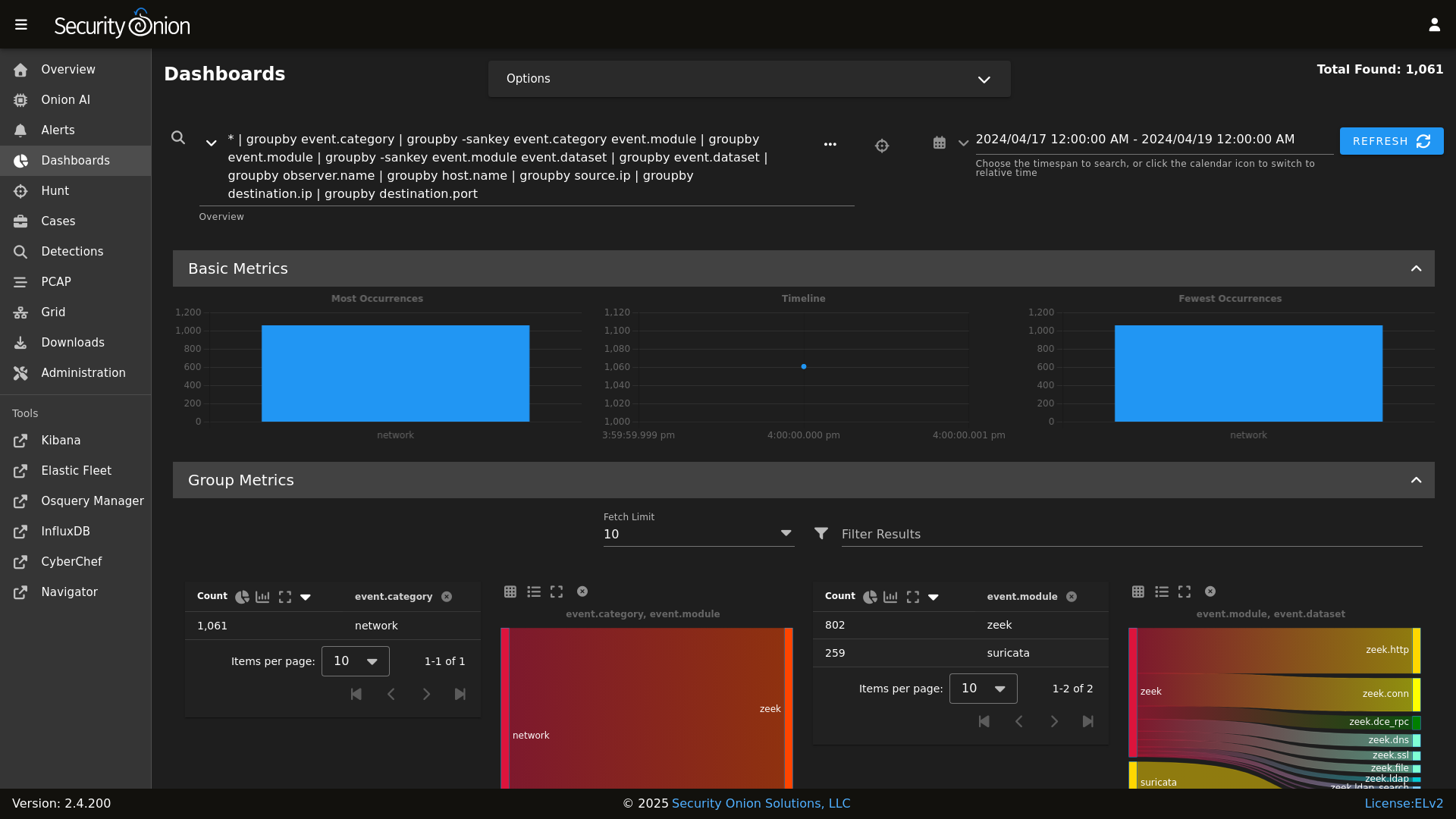
Dashboards
|
||||
|
||||
Security Onion includes everything you need to monitor your network and host systems:
|
||||
|
||||
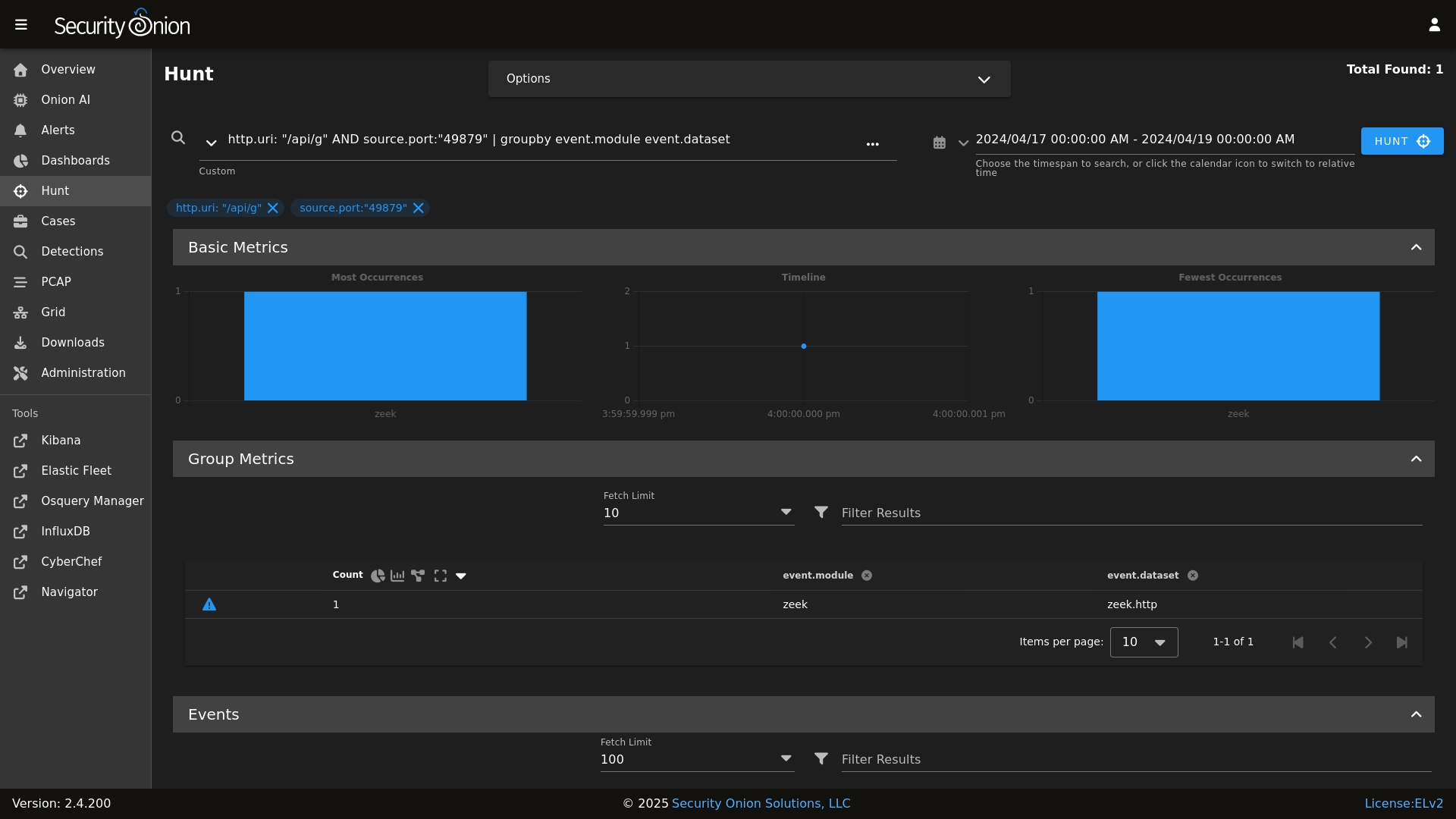
Hunt
|
||||
|
||||
* **Security Onion Console (SOC)**: A unified web interface for analyzing security events and managing your grid.
|
||||
* **Elastic Stack**: Powerful search backed by Elasticsearch.
|
||||
* **Intrusion Detection**: Network-based IDS with Suricata and host-based monitoring with Elastic Fleet.
|
||||
* **Network Metadata**: Detailed network metadata generated by Zeek or Suricata.
|
||||
* **Full Packet Capture**: Retain and analyze raw network traffic with Suricata PCAP.
|
||||
|
||||
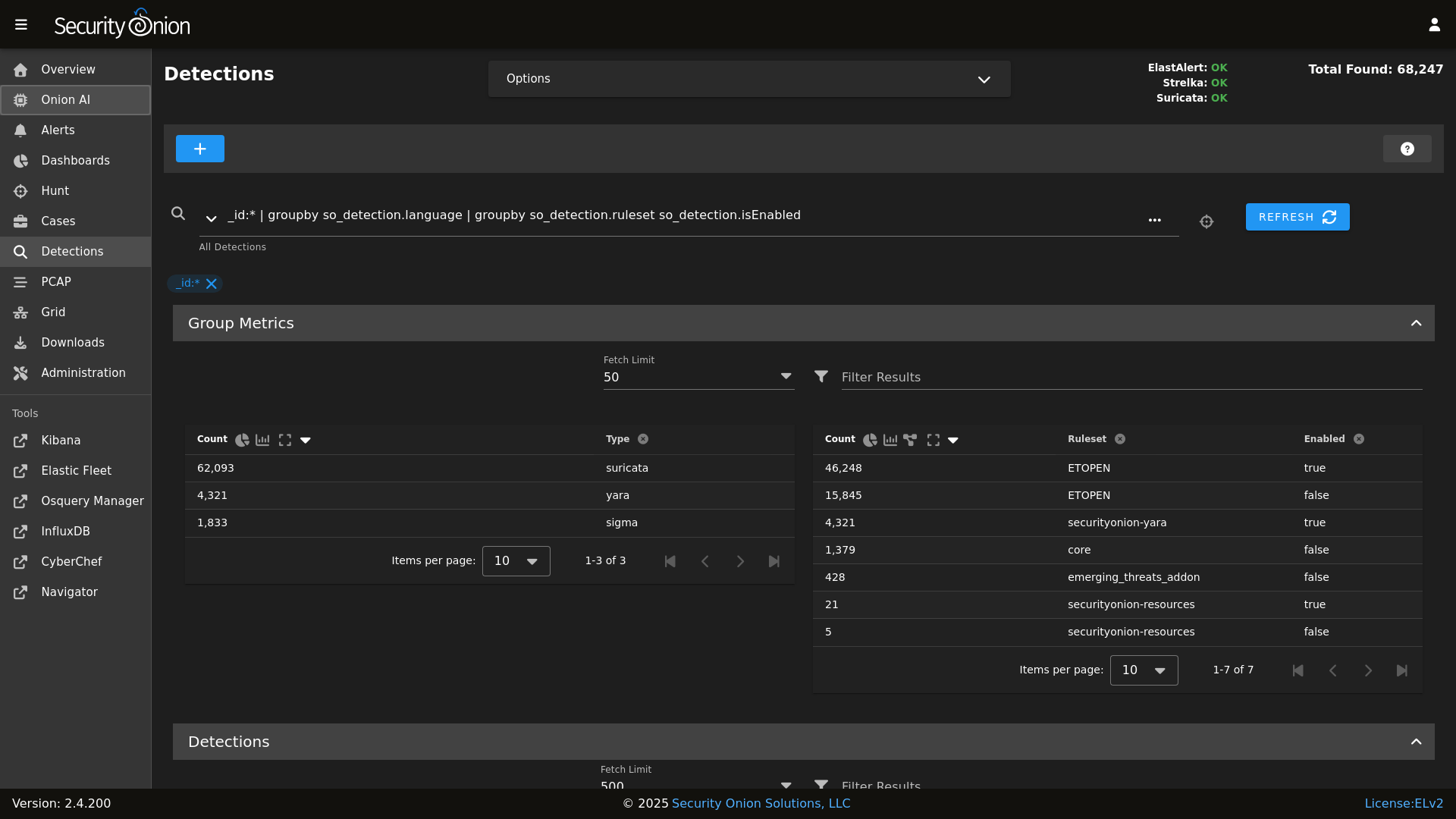
Detections
|
||||
|
||||
## ⭐ Security Onion Pro
|
||||
|
||||
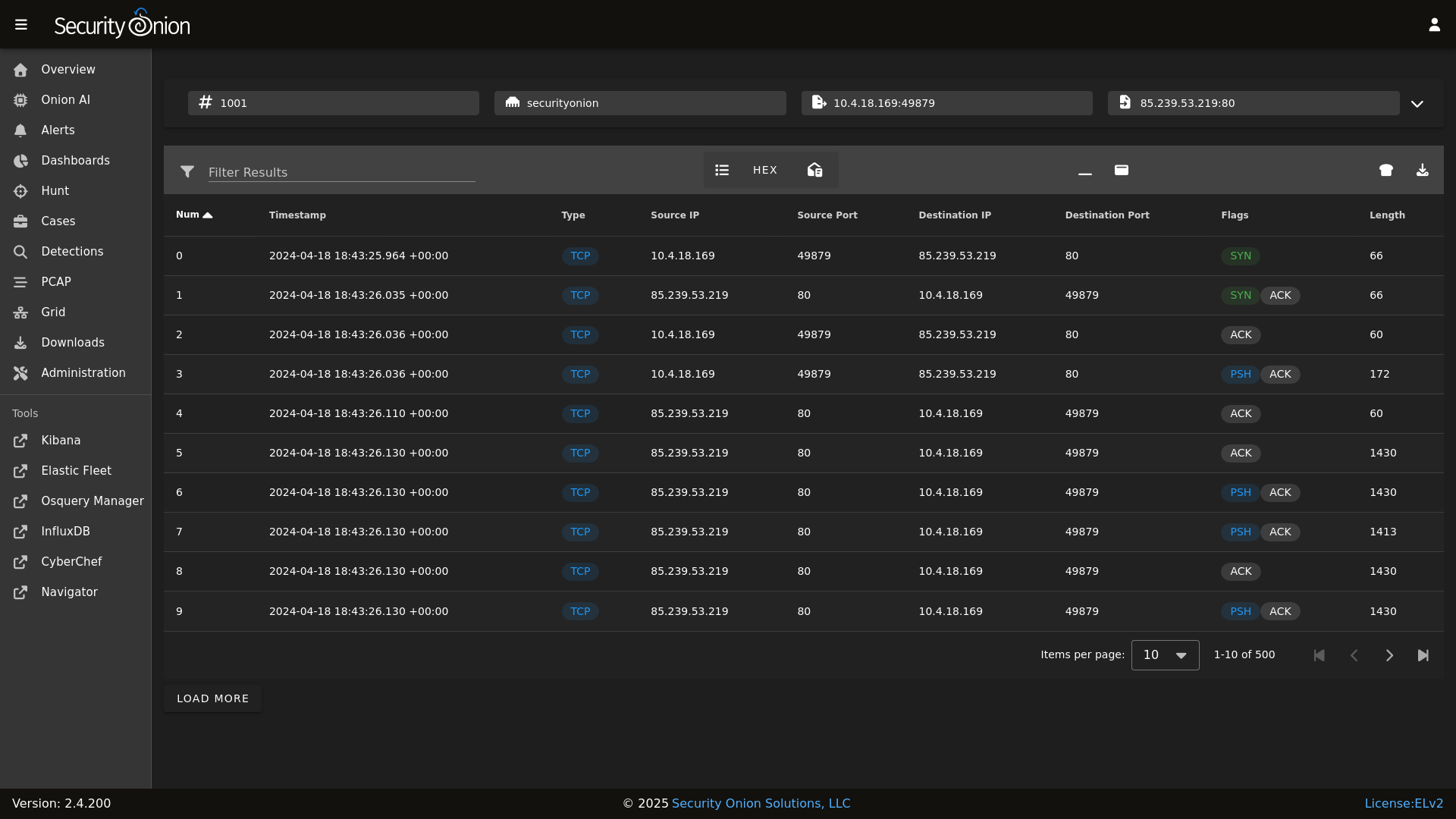
PCAP
|
||||
|
||||
For organizations and enterprises requiring advanced capabilities, **Security Onion Pro** offers additional features designed for scale and efficiency:
|
||||
|
||||
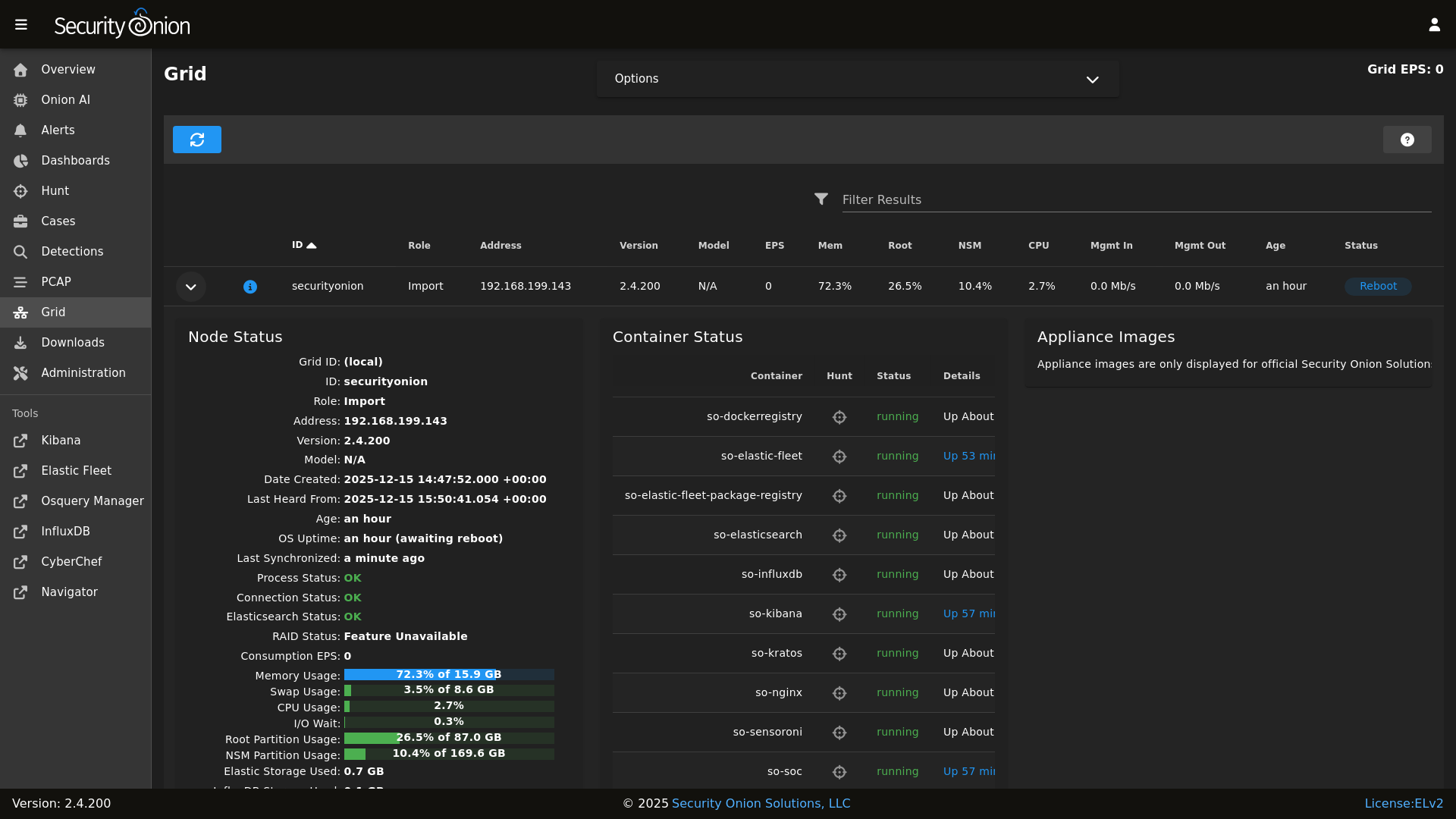
Grid
|
||||
|
||||
* **Onion AI**: Leverage powerful AI-driven insights to accelerate your analysis and investigations.
|
||||
* **Enterprise Features**: Enhanced tools and integrations tailored for enterprise-grade security operations.
|
||||
|
||||
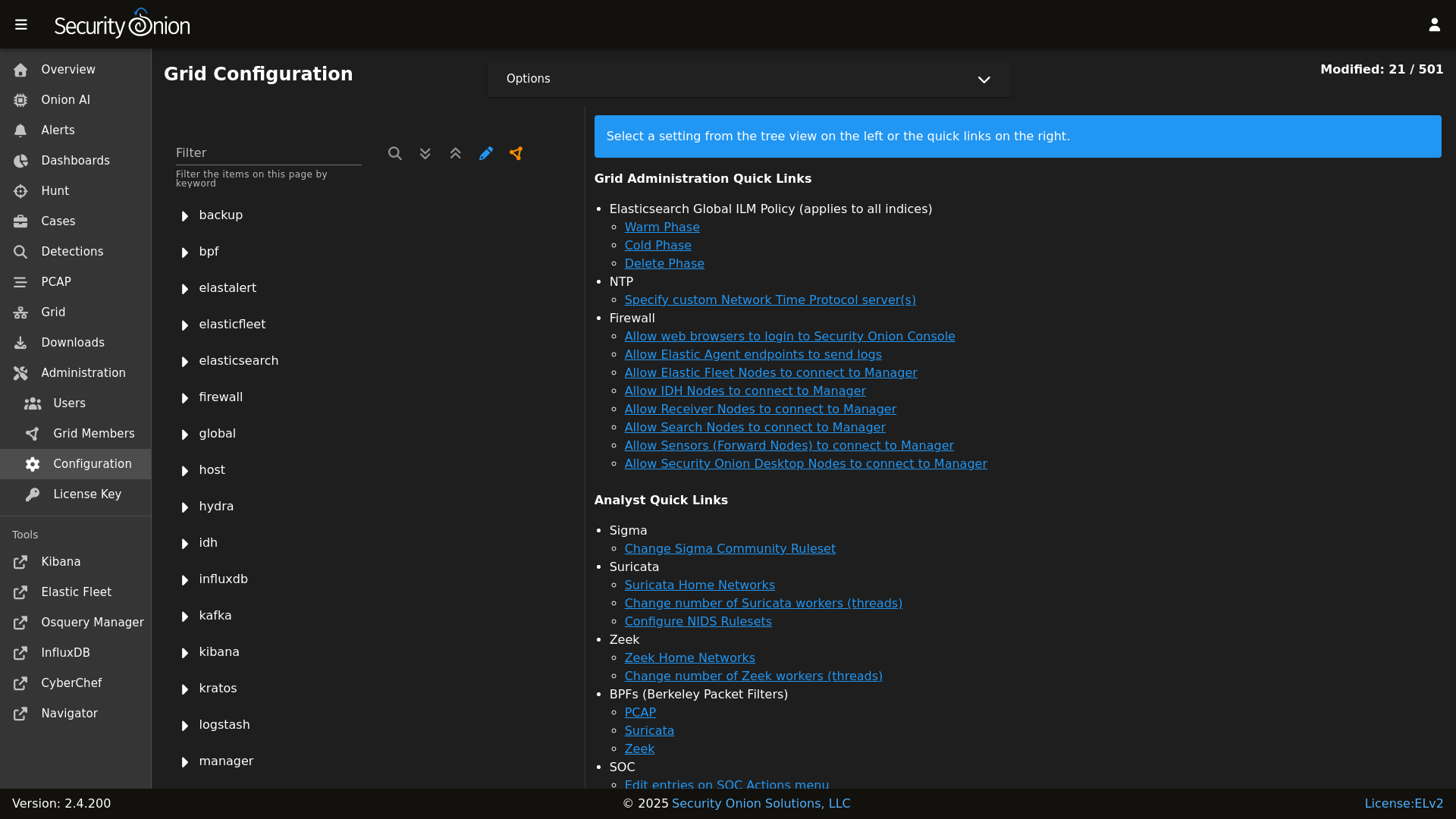
Config
|
||||
|
||||
For more information, visit the [Security Onion Pro](https://securityonionsolutions.com/pro) page.
|
||||
|
||||
### Release Notes
|
||||
## ☁️ Cloud Deployment
|
||||
|
||||
https://securityonion.net/docs/release-notes
|
||||
Security Onion is available and ready to deploy in the **AWS**, **Azure**, and **Google Cloud (GCP)** marketplaces.
|
||||
|
||||
### Requirements
|
||||
## 🚀 Getting Started
|
||||
|
||||
https://securityonion.net/docs/hardware
|
||||
| Goal | Resource |
|
||||
| :--- | :--- |
|
||||
| **Download** | [Security Onion ISO](https://securityonion.net/docs/download) |
|
||||
| **Requirements** | [Hardware Guide](https://securityonion.net/docs/hardware) |
|
||||
| **Install** | [Installation Instructions](https://securityonion.net/docs/installation) |
|
||||
| **What's New** | [Release Notes](https://securityonion.net/docs/release-notes) |
|
||||
|
||||
### Download
|
||||
## 📖 Documentation & Support
|
||||
|
||||
https://securityonion.net/docs/download
|
||||
For more detailed information, please visit our [Documentation](https://docs.securityonion.net).
|
||||
|
||||
### Installation
|
||||
* **FAQ**: [Frequently Asked Questions](https://securityonion.net/docs/faq)
|
||||
* **Community**: [Discussions & Support](https://securityonion.net/docs/community-support)
|
||||
* **Training**: [Official Training](https://securityonion.net/training)
|
||||
|
||||
https://securityonion.net/docs/installation
|
||||
## 🤝 Contributing
|
||||
|
||||
### FAQ
|
||||
We welcome contributions! Please see our [CONTRIBUTING.md](CONTRIBUTING.md) for guidelines on how to get involved.
|
||||
|
||||
https://securityonion.net/docs/faq
|
||||
## 🛡️ License
|
||||
|
||||
### Feedback
|
||||
Security Onion is licensed under the terms of the license found in the [LICENSE](LICENSE) file.
|
||||
|
||||
https://securityonion.net/docs/community-support
|
||||
---
|
||||
*Built with 🧅 by Security Onion Solutions.*
|
||||
|
||||
@@ -4,6 +4,7 @@
|
||||
|
||||
| Version | Supported |
|
||||
| ------- | ------------------ |
|
||||
| 3.x | :white_check_mark: |
|
||||
| 2.4.x | :white_check_mark: |
|
||||
| 2.3.x | :x: |
|
||||
| 16.04.x | :x: |
|
||||
|
||||
@@ -87,8 +87,6 @@ base:
|
||||
- zeek.adv_zeek
|
||||
- bpf.soc_bpf
|
||||
- bpf.adv_bpf
|
||||
- pcap.soc_pcap
|
||||
- pcap.adv_pcap
|
||||
- suricata.soc_suricata
|
||||
- suricata.adv_suricata
|
||||
- minions.{{ grains.id }}
|
||||
@@ -134,8 +132,6 @@ base:
|
||||
- zeek.adv_zeek
|
||||
- bpf.soc_bpf
|
||||
- bpf.adv_bpf
|
||||
- pcap.soc_pcap
|
||||
- pcap.adv_pcap
|
||||
- suricata.soc_suricata
|
||||
- suricata.adv_suricata
|
||||
- minions.{{ grains.id }}
|
||||
@@ -185,8 +181,6 @@ base:
|
||||
- zeek.adv_zeek
|
||||
- bpf.soc_bpf
|
||||
- bpf.adv_bpf
|
||||
- pcap.soc_pcap
|
||||
- pcap.adv_pcap
|
||||
- suricata.soc_suricata
|
||||
- suricata.adv_suricata
|
||||
- minions.{{ grains.id }}
|
||||
@@ -209,8 +203,6 @@ base:
|
||||
- zeek.adv_zeek
|
||||
- bpf.soc_bpf
|
||||
- bpf.adv_bpf
|
||||
- pcap.soc_pcap
|
||||
- pcap.adv_pcap
|
||||
- suricata.soc_suricata
|
||||
- suricata.adv_suricata
|
||||
- strelka.soc_strelka
|
||||
@@ -297,8 +289,6 @@ base:
|
||||
- zeek.adv_zeek
|
||||
- bpf.soc_bpf
|
||||
- bpf.adv_bpf
|
||||
- pcap.soc_pcap
|
||||
- pcap.adv_pcap
|
||||
- suricata.soc_suricata
|
||||
- suricata.adv_suricata
|
||||
- strelka.soc_strelka
|
||||
|
||||
@@ -38,7 +38,6 @@
|
||||
] %}
|
||||
|
||||
{% set sensor_states = [
|
||||
'pcap',
|
||||
'suricata',
|
||||
'healthcheck',
|
||||
'tcpreplay',
|
||||
|
||||
@@ -1,21 +1,15 @@
|
||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
{% set PCAP_BPF_STATUS = 0 %}
|
||||
{% set STENO_BPF_COMPILED = "" %}
|
||||
|
||||
{% if GLOBALS.pcap_engine == "TRANSITION" %}
|
||||
{% set PCAPBPF = ["ip and host 255.255.255.1 and port 1"] %}
|
||||
{% else %}
|
||||
{% import_yaml 'bpf/defaults.yaml' as BPFDEFAULTS %}
|
||||
{% set BPFMERGED = salt['pillar.get']('bpf', BPFDEFAULTS.bpf, merge=True) %}
|
||||
{% import 'bpf/macros.jinja' as MACROS %}
|
||||
{{ MACROS.remove_comments(BPFMERGED, 'pcap') }}
|
||||
{% set PCAPBPF = BPFMERGED.pcap %}
|
||||
{% endif %}
|
||||
|
||||
{% if PCAPBPF %}
|
||||
{% set PCAP_BPF_CALC = salt['cmd.script']('salt://common/tools/sbin/so-bpf-compile', GLOBALS.sensor.interface + ' ' + PCAPBPF|join(" "),cwd='/root') %}
|
||||
{% if PCAP_BPF_CALC['retcode'] == 0 %}
|
||||
{% set PCAP_BPF_STATUS = 1 %}
|
||||
{% set STENO_BPF_COMPILED = ",\\\"--filter=" + PCAP_BPF_CALC['stdout'] + "\\\"" %}
|
||||
{% endif %}
|
||||
{% endif %}
|
||||
|
||||
@@ -3,8 +3,6 @@
|
||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||
# Elastic License 2.0.
|
||||
|
||||
{% if '2.4' in salt['cp.get_file_str']('/etc/soversion') %}
|
||||
|
||||
{% import_yaml '/opt/so/saltstack/local/pillar/global/soc_global.sls' as SOC_GLOBAL %}
|
||||
{% if SOC_GLOBAL.global.airgap %}
|
||||
{% set UPDATE_DIR='/tmp/soagupdate/SecurityOnion' %}
|
||||
@@ -120,23 +118,3 @@ copy_bootstrap-salt_sbin:
|
||||
- source: {{UPDATE_DIR}}/salt/salt/scripts/bootstrap-salt.sh
|
||||
- force: True
|
||||
- preserve: True
|
||||
|
||||
{# this is added in 2.4.120 to remove salt repo files pointing to saltproject.io to accomodate the move to broadcom and new bootstrap-salt script #}
|
||||
{% if salt['pkg.version_cmp'](SOVERSION, '2.4.120') == -1 %}
|
||||
{% set saltrepofile = '/etc/yum.repos.d/salt.repo' %}
|
||||
{% if grains.os_family == 'Debian' %}
|
||||
{% set saltrepofile = '/etc/apt/sources.list.d/salt.list' %}
|
||||
{% endif %}
|
||||
remove_saltproject_io_repo_manager:
|
||||
file.absent:
|
||||
- name: {{ saltrepofile }}
|
||||
{% endif %}
|
||||
|
||||
{% else %}
|
||||
fix_23_soup_sbin:
|
||||
cmd.run:
|
||||
- name: curl -s -f -o /usr/sbin/soup https://raw.githubusercontent.com/Security-Onion-Solutions/securityonion/2.3/main/salt/common/tools/sbin/soup
|
||||
fix_23_soup_salt:
|
||||
cmd.run:
|
||||
- name: curl -s -f -o /opt/so/saltstack/defalt/salt/common/tools/sbin/soup https://raw.githubusercontent.com/Security-Onion-Solutions/securityonion/2.3/main/salt/common/tools/sbin/soup
|
||||
{% endif %}
|
||||
|
||||
@@ -16,7 +16,7 @@
|
||||
|
||||
if [ "$#" -lt 2 ]; then
|
||||
cat 1>&2 <<EOF
|
||||
$0 compiles a BPF expression to be passed to stenotype to apply a socket filter.
|
||||
$0 compiles a BPF expression to be passed to PCAP to apply a socket filter.
|
||||
Its first argument is the interface (link type is required) and all other arguments
|
||||
are passed to TCPDump.
|
||||
|
||||
|
||||
@@ -333,8 +333,8 @@ get_elastic_agent_vars() {
|
||||
|
||||
if [ -f "$defaultsfile" ]; then
|
||||
ELASTIC_AGENT_TARBALL_VERSION=$(egrep " +version: " $defaultsfile | awk -F: '{print $2}' | tr -d '[:space:]')
|
||||
ELASTIC_AGENT_URL="https://repo.securityonion.net/file/so-repo/prod/2.4/elasticagent/elastic-agent_SO-$ELASTIC_AGENT_TARBALL_VERSION.tar.gz"
|
||||
ELASTIC_AGENT_MD5_URL="https://repo.securityonion.net/file/so-repo/prod/2.4/elasticagent/elastic-agent_SO-$ELASTIC_AGENT_TARBALL_VERSION.md5"
|
||||
ELASTIC_AGENT_URL="https://repo.securityonion.net/file/so-repo/prod/3/elasticagent/elastic-agent_SO-$ELASTIC_AGENT_TARBALL_VERSION.tar.gz"
|
||||
ELASTIC_AGENT_MD5_URL="https://repo.securityonion.net/file/so-repo/prod/3/elasticagent/elastic-agent_SO-$ELASTIC_AGENT_TARBALL_VERSION.md5"
|
||||
ELASTIC_AGENT_FILE="/nsm/elastic-fleet/artifacts/elastic-agent_SO-$ELASTIC_AGENT_TARBALL_VERSION.tar.gz"
|
||||
ELASTIC_AGENT_MD5="/nsm/elastic-fleet/artifacts/elastic-agent_SO-$ELASTIC_AGENT_TARBALL_VERSION.md5"
|
||||
ELASTIC_AGENT_EXPANSION_DIR=/nsm/elastic-fleet/artifacts/beats/elastic-agent
|
||||
|
||||
@@ -32,7 +32,6 @@ container_list() {
|
||||
"so-nginx"
|
||||
"so-pcaptools"
|
||||
"so-soc"
|
||||
"so-steno"
|
||||
"so-suricata"
|
||||
"so-telegraf"
|
||||
"so-zeek"
|
||||
@@ -58,7 +57,6 @@ container_list() {
|
||||
"so-pcaptools"
|
||||
"so-redis"
|
||||
"so-soc"
|
||||
"so-steno"
|
||||
"so-strelka-backend"
|
||||
"so-strelka-manager"
|
||||
"so-suricata"
|
||||
@@ -71,7 +69,6 @@ container_list() {
|
||||
"so-logstash"
|
||||
"so-nginx"
|
||||
"so-redis"
|
||||
"so-steno"
|
||||
"so-suricata"
|
||||
"so-soc"
|
||||
"so-telegraf"
|
||||
|
||||
@@ -179,7 +179,6 @@ if [[ $EXCLUDE_KNOWN_ERRORS == 'Y' ]]; then
|
||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|salt-minion-check" # bug in early 2.4 place Jinja script in non-jinja salt dir causing cron output errors
|
||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|monitoring.metrics" # known issue with elastic agent casting the field incorrectly if an integer value shows up before a float
|
||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|repodownload.conf" # known issue with reposync on pre-2.4.20
|
||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|missing versions record" # stenographer corrupt index
|
||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|soc.field." # known ingest type collisions issue with earlier versions of SO
|
||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|error parsing signature" # Malformed Suricata rule, from upstream provider
|
||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|sticky buffer has no matches" # Non-critical Suricata error
|
||||
|
||||
@@ -55,19 +55,22 @@ if [ $SKIP -ne 1 ]; then
|
||||
fi
|
||||
|
||||
delete_pcap() {
|
||||
PCAP_DATA="/nsm/pcap/"
|
||||
[ -d $PCAP_DATA ] && so-pcap-stop && rm -rf $PCAP_DATA/* && so-pcap-start
|
||||
PCAP_DATA="/nsm/suripcap/"
|
||||
[ -d $PCAP_DATA ] && rm -rf $PCAP_DATA/*
|
||||
}
|
||||
delete_suricata() {
|
||||
SURI_LOG="/nsm/suricata/"
|
||||
[ -d $SURI_LOG ] && so-suricata-stop && rm -rf $SURI_LOG/* && so-suricata-start
|
||||
[ -d $SURI_LOG ] && rm -rf $SURI_LOG/*
|
||||
}
|
||||
delete_zeek() {
|
||||
ZEEK_LOG="/nsm/zeek/logs/"
|
||||
[ -d $ZEEK_LOG ] && so-zeek-stop && rm -rf $ZEEK_LOG/* && so-zeek-start
|
||||
}
|
||||
|
||||
so-suricata-stop
|
||||
delete_pcap
|
||||
delete_suricata
|
||||
delete_zeek
|
||||
so-suricata-start
|
||||
|
||||
|
||||
|
||||
@@ -23,7 +23,6 @@ if [ $# -ge 1 ]; then
|
||||
fi
|
||||
|
||||
case $1 in
|
||||
"steno") docker stop so-steno && docker rm so-steno && salt-call state.apply pcap queue=True;;
|
||||
"elastic-fleet") docker stop so-elastic-fleet && docker rm so-elastic-fleet && salt-call state.apply elasticfleet queue=True;;
|
||||
*) docker stop so-$1 ; docker rm so-$1 ; salt-call state.apply $1 queue=True;;
|
||||
esac
|
||||
|
||||
@@ -72,7 +72,7 @@ clean() {
|
||||
done
|
||||
fi
|
||||
|
||||
## Clean up extracted pcaps from Steno
|
||||
## Clean up extracted pcaps
|
||||
PCAPS='/nsm/pcapout'
|
||||
OLDEST_PCAP=$(find $PCAPS -type f -printf '%T+ %p\n' | sort -n | head -n 1)
|
||||
if [ -z "$OLDEST_PCAP" -o "$OLDEST_PCAP" == ".." -o "$OLDEST_PCAP" == "." ]; then
|
||||
|
||||
@@ -23,7 +23,6 @@ if [ $# -ge 1 ]; then
|
||||
|
||||
case $1 in
|
||||
"all") salt-call state.highstate queue=True;;
|
||||
"steno") if docker ps | grep -q so-$1; then printf "\n$1 is already running!\n\n"; else docker rm so-$1 >/dev/null 2>&1 ; salt-call state.apply pcap queue=True; fi ;;
|
||||
"elastic-fleet") if docker ps | grep -q so-$1; then printf "\n$1 is already running!\n\n"; else docker rm so-$1 >/dev/null 2>&1 ; salt-call state.apply elasticfleet queue=True; fi ;;
|
||||
*) if docker ps | grep -E -q '^so-$1$'; then printf "\n$1 is already running\n\n"; else docker rm so-$1 >/dev/null 2>&1 ; salt-call state.apply $1 queue=True; fi ;;
|
||||
esac
|
||||
|
||||
@@ -174,11 +174,6 @@ docker:
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
'so-steno':
|
||||
final_octet: 99
|
||||
custom_bind_mounts: []
|
||||
extra_hosts: []
|
||||
extra_env: []
|
||||
'so-suricata':
|
||||
final_octet: 99
|
||||
custom_bind_mounts: []
|
||||
|
||||
@@ -62,7 +62,6 @@ docker:
|
||||
so-idh: *dockerOptions
|
||||
so-elastic-agent: *dockerOptions
|
||||
so-telegraf: *dockerOptions
|
||||
so-steno: *dockerOptions
|
||||
so-suricata:
|
||||
final_octet:
|
||||
description: Last octet of the container IP address.
|
||||
|
||||
@@ -1,3 +1,3 @@
|
||||
global:
|
||||
pcapengine: STENO
|
||||
pcapengine: SURICATA
|
||||
pipeline: REDIS
|
||||
@@ -18,13 +18,11 @@ global:
|
||||
regexFailureMessage: You must enter either ZEEK or SURICATA.
|
||||
global: True
|
||||
pcapengine:
|
||||
description: Which engine to use for generating pcap. Options are STENO, SURICATA or TRANSITION.
|
||||
regex: ^(STENO|SURICATA|TRANSITION)$
|
||||
description: Which engine to use for generating pcap. Currently only SURICATA is supported.
|
||||
regex: ^(SURICATA)$
|
||||
options:
|
||||
- STENO
|
||||
- SURICATA
|
||||
- TRANSITION
|
||||
regexFailureMessage: You must enter either STENO, SURICATA or TRANSITION.
|
||||
regexFailureMessage: You must enter either SURICATA.
|
||||
global: True
|
||||
ids:
|
||||
description: Which IDS engine to use. Currently only Suricata is supported.
|
||||
|
||||
@@ -1,27 +0,0 @@
|
||||
[{
|
||||
"apiVersion": "influxdata.com/v2alpha1",
|
||||
"kind": "CheckThreshold",
|
||||
"metadata": {
|
||||
"name": "steno-packet-loss"
|
||||
},
|
||||
"spec": {
|
||||
"description": "Triggers when the average percent of packet loss is above the defined threshold. To tune this alert, modify the value for the appropriate alert level.",
|
||||
"every": "1m",
|
||||
"name": "Stenographer Packet Loss",
|
||||
"query": "from(bucket: \"telegraf/so_short_term\")\n |\u003e range(start: v.timeRangeStart, stop: v.timeRangeStop)\n |\u003e filter(fn: (r) =\u003e r[\"_measurement\"] == \"stenodrop\")\n |\u003e filter(fn: (r) =\u003e r[\"_field\"] == \"drop\")\n |\u003e aggregateWindow(every: 1m, fn: mean, createEmpty: false)\n |\u003e yield(name: \"mean\")",
|
||||
"status": "active",
|
||||
"statusMessageTemplate": "Stenographer Packet Loss on node ${r.host} has reached the ${ r._level } threshold. The current packet loss is ${ r.drop }%.",
|
||||
"thresholds": [
|
||||
{
|
||||
"level": "CRIT",
|
||||
"type": "greater",
|
||||
"value": 5
|
||||
},
|
||||
{
|
||||
"level": "WARN",
|
||||
"type": "greater",
|
||||
"value": 3
|
||||
}
|
||||
]
|
||||
}
|
||||
}]
|
||||
File diff suppressed because one or more lines are too long
@@ -180,16 +180,6 @@ logrotate:
|
||||
- extension .log
|
||||
- dateext
|
||||
- dateyesterday
|
||||
/opt/so/log/stenographer/*_x_log:
|
||||
- daily
|
||||
- rotate 14
|
||||
- missingok
|
||||
- copytruncate
|
||||
- compress
|
||||
- create
|
||||
- extension .log
|
||||
- dateext
|
||||
- dateyesterday
|
||||
/opt/so/log/salt/so-salt-minion-check:
|
||||
- daily
|
||||
- rotate 14
|
||||
|
||||
@@ -112,13 +112,6 @@ logrotate:
|
||||
multiline: True
|
||||
global: True
|
||||
forcedType: "[]string"
|
||||
"/opt/so/log/stenographer/*_x_log":
|
||||
description: List of logrotate options for this file.
|
||||
title: /opt/so/log/stenographer/*.log
|
||||
advanced: True
|
||||
multiline: True
|
||||
global: True
|
||||
forcedType: "[]string"
|
||||
"/opt/so/log/salt/so-salt-minion-check":
|
||||
description: List of logrotate options for this file.
|
||||
title: /opt/so/log/salt/so-salt-minion-check
|
||||
|
||||
@@ -1,2 +1,2 @@
|
||||
https://repo.securityonion.net/file/so-repo/prod/2.4/oracle/9
|
||||
https://repo-alt.securityonion.net/prod/2.4/oracle/9
|
||||
https://repo.securityonion.net/file/so-repo/prod/3/oracle/9
|
||||
https://repo-alt.securityonion.net/prod/3/oracle/9
|
||||
@@ -143,7 +143,7 @@ show_usage() {
|
||||
echo " -v Show verbose output (files changed/added/deleted)"
|
||||
echo " -vv Show very verbose output (includes file diffs)"
|
||||
echo " --test Test mode - show what would change without making changes"
|
||||
echo " branch Git branch to checkout (default: 2.4/main)"
|
||||
echo " branch Git branch to checkout (default: 3/main)"
|
||||
echo ""
|
||||
echo "Examples:"
|
||||
echo " $0 # Normal operation"
|
||||
@@ -193,7 +193,7 @@ done
|
||||
|
||||
# Set default branch if not provided
|
||||
if [ -z "$BRANCH" ]; then
|
||||
BRANCH=2.4/main
|
||||
BRANCH=3/main
|
||||
fi
|
||||
|
||||
got_root
|
||||
|
||||
@@ -1,184 +0,0 @@
|
||||
#!/bin/bash
|
||||
|
||||
# Copyright Security Onion Solutions LLC and/or licensed to Security Onion Solutions LLC under one
|
||||
# or more contributor license agreements. Licensed under the Elastic License 2.0 as shown at
|
||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||
# Elastic License 2.0.
|
||||
|
||||
|
||||
. /usr/sbin/so-common
|
||||
|
||||
UPDATE_URL=https://raw.githubusercontent.com/Security-Onion-Solutions/securityonion/refs/heads/3/main/VERSION
|
||||
|
||||
# Check if already running version 3
|
||||
CURRENT_VERSION=$(cat /etc/soversion 2>/dev/null)
|
||||
if [[ "$CURRENT_VERSION" =~ ^3\. ]]; then
|
||||
echo ""
|
||||
echo "========================================================================="
|
||||
echo " Already Running Security Onion 3"
|
||||
echo "========================================================================="
|
||||
echo ""
|
||||
echo " This system is already running Security Onion $CURRENT_VERSION."
|
||||
echo " Use 'soup' to update within the 3.x release line."
|
||||
echo ""
|
||||
exit 0
|
||||
fi
|
||||
|
||||
echo ""
|
||||
echo "Checking PCAP settings."
|
||||
echo ""
|
||||
|
||||
# Check pcapengine setting - must be SURICATA before upgrading to version 3
|
||||
PCAP_ENGINE=$(lookup_pillar "pcapengine")
|
||||
|
||||
PCAP_DELETED=false
|
||||
|
||||
prompt_delete_pcap() {
|
||||
read -rp " Would you like to delete all remaining Stenographer PCAP data? (y/N): " DELETE_PCAP
|
||||
if [[ "$DELETE_PCAP" =~ ^[Yy]$ ]]; then
|
||||
echo ""
|
||||
echo " WARNING: This will permanently delete all Stenographer PCAP data"
|
||||
echo " on all nodes. This action cannot be undone."
|
||||
echo ""
|
||||
read -rp " Are you sure? (y/N): " CONFIRM_DELETE
|
||||
if [[ "$CONFIRM_DELETE" =~ ^[Yy]$ ]]; then
|
||||
echo ""
|
||||
echo " Deleting Stenographer PCAP data on all nodes..."
|
||||
salt '*' cmd.run "rm -rf /nsm/pcap/* && rm -rf /nsm/pcapindex/*"
|
||||
echo " Done."
|
||||
PCAP_DELETED=true
|
||||
else
|
||||
echo ""
|
||||
echo " Delete cancelled."
|
||||
fi
|
||||
fi
|
||||
}
|
||||
|
||||
pcapengine_not_changed() {
|
||||
echo ""
|
||||
echo " PCAP engine must be set to SURICATA before upgrading to Security Onion 3."
|
||||
echo " You can change this in SOC by navigating to:"
|
||||
echo " Configuration -> global -> pcapengine"
|
||||
}
|
||||
|
||||
prompt_change_engine() {
|
||||
local current_engine=$1
|
||||
echo ""
|
||||
read -rp " Would you like to change the PCAP engine to SURICATA now? (y/N): " CHANGE_ENGINE
|
||||
if [[ "$CHANGE_ENGINE" =~ ^[Yy]$ ]]; then
|
||||
if [[ "$PCAP_DELETED" != "true" ]]; then
|
||||
echo ""
|
||||
echo " WARNING: Stenographer PCAP data was not deleted. If you proceed,"
|
||||
echo " this data will no longer be accessible through SOC and will never"
|
||||
echo " be automatically deleted. You will need to manually remove it later."
|
||||
echo ""
|
||||
read -rp " Continue with changing pcapengine to SURICATA? (y/N): " CONFIRM_CHANGE
|
||||
if [[ ! "$CONFIRM_CHANGE" =~ ^[Yy]$ ]]; then
|
||||
pcapengine_not_changed
|
||||
return 1
|
||||
fi
|
||||
fi
|
||||
echo ""
|
||||
echo " Updating PCAP engine to SURICATA..."
|
||||
so-yaml.py replace /opt/so/saltstack/local/pillar/global/soc_global.sls global.pcapengine SURICATA
|
||||
echo " Done."
|
||||
return 0
|
||||
else
|
||||
pcapengine_not_changed
|
||||
return 1
|
||||
fi
|
||||
}
|
||||
|
||||
case "$PCAP_ENGINE" in
|
||||
SURICATA)
|
||||
echo "PCAP engine settings OK."
|
||||
;;
|
||||
TRANSITION|STENO)
|
||||
echo ""
|
||||
echo "========================================================================="
|
||||
echo " PCAP Engine Check Failed"
|
||||
echo "========================================================================="
|
||||
echo ""
|
||||
echo " Your PCAP engine is currently set to $PCAP_ENGINE."
|
||||
echo ""
|
||||
echo " Before upgrading to Security Onion 3, Stenographer PCAP data must be"
|
||||
echo " removed and the PCAP engine must be set to SURICATA."
|
||||
echo ""
|
||||
echo " To check remaining Stenographer PCAP usage, run:"
|
||||
echo " salt '*' cmd.run 'du -sh /nsm/pcap'"
|
||||
echo ""
|
||||
|
||||
prompt_delete_pcap
|
||||
if ! prompt_change_engine "$PCAP_ENGINE"; then
|
||||
echo ""
|
||||
exit 1
|
||||
fi
|
||||
;;
|
||||
*)
|
||||
echo ""
|
||||
echo "========================================================================="
|
||||
echo " PCAP Engine Check Failed"
|
||||
echo "========================================================================="
|
||||
echo ""
|
||||
echo " Unable to determine the PCAP engine setting (got: '$PCAP_ENGINE')."
|
||||
echo " Please ensure the PCAP engine is set to SURICATA."
|
||||
echo " In SOC, navigate to Configuration -> global -> pcapengine"
|
||||
echo " and change the value to SURICATA."
|
||||
echo ""
|
||||
exit 1
|
||||
;;
|
||||
esac
|
||||
|
||||
echo ""
|
||||
echo "Checking Versions."
|
||||
echo ""
|
||||
|
||||
# Check if Security Onion 3 has been released
|
||||
VERSION=$(curl -sSf "$UPDATE_URL" 2>/dev/null)
|
||||
|
||||
if [[ -z "$VERSION" ]]; then
|
||||
echo ""
|
||||
echo "========================================================================="
|
||||
echo " Unable to Check Version"
|
||||
echo "========================================================================="
|
||||
echo ""
|
||||
echo " Could not retrieve version information from:"
|
||||
echo " $UPDATE_URL"
|
||||
echo ""
|
||||
echo " Please check your network connection and try again."
|
||||
echo ""
|
||||
exit 1
|
||||
fi
|
||||
|
||||
if [[ "$VERSION" == "UNRELEASED" ]]; then
|
||||
echo ""
|
||||
echo "========================================================================="
|
||||
echo " Security Onion 3 Not Available"
|
||||
echo "========================================================================="
|
||||
echo ""
|
||||
echo " Security Onion 3 has not been released yet."
|
||||
echo ""
|
||||
echo " Please check back later or visit https://securityonion.net for updates."
|
||||
echo ""
|
||||
exit 1
|
||||
fi
|
||||
|
||||
# Validate version format (e.g., 3.0.2)
|
||||
if [[ ! "$VERSION" =~ ^[0-9]+\.[0-9]+\.[0-9]+$ ]]; then
|
||||
echo ""
|
||||
echo "========================================================================="
|
||||
echo " Invalid Version"
|
||||
echo "========================================================================="
|
||||
echo ""
|
||||
echo " Received unexpected version format: '$VERSION'"
|
||||
echo ""
|
||||
echo " Please check back later or visit https://securityonion.net for updates."
|
||||
echo ""
|
||||
exit 1
|
||||
fi
|
||||
|
||||
echo "Security Onion 3 ($VERSION) is available. Upgrading..."
|
||||
echo ""
|
||||
|
||||
# All checks passed - proceed with upgrade
|
||||
BRANCH=3/main soup
|
||||
@@ -3,6 +3,7 @@ nginx:
|
||||
external_suricata: False
|
||||
ssl:
|
||||
replace_cert: False
|
||||
alt_names: []
|
||||
config:
|
||||
throttle_login_burst: 12
|
||||
throttle_login_rate: 20
|
||||
|
||||
@@ -60,6 +60,8 @@ http {
|
||||
{%- endif %}
|
||||
|
||||
{%- if GLOBALS.is_manager %}
|
||||
{%- set all_names = [GLOBALS.hostname, GLOBALS.url_base] + NGINXMERGED.ssl.alt_names %}
|
||||
{%- set full_server_name = all_names | unique | join(' ') %}
|
||||
|
||||
server {
|
||||
listen 80 default_server;
|
||||
@@ -69,7 +71,7 @@ http {
|
||||
|
||||
server {
|
||||
listen 8443;
|
||||
server_name {{ GLOBALS.url_base }};
|
||||
server_name {{ full_server_name }};
|
||||
root /opt/socore/html;
|
||||
location /artifacts/ {
|
||||
try_files $uri =206;
|
||||
@@ -112,7 +114,7 @@ http {
|
||||
|
||||
server {
|
||||
listen 7788;
|
||||
server_name {{ GLOBALS.url_base }};
|
||||
server_name {{ full_server_name }};
|
||||
root /nsm/rules;
|
||||
location / {
|
||||
allow all;
|
||||
@@ -128,7 +130,7 @@ http {
|
||||
server {
|
||||
listen 7789 ssl;
|
||||
http2 on;
|
||||
server_name {{ GLOBALS.url_base }};
|
||||
server_name {{ full_server_name }};
|
||||
root /surirules;
|
||||
|
||||
add_header Content-Security-Policy "default-src 'self' 'unsafe-inline' 'unsafe-eval' https: data: blob: wss:; frame-ancestors 'self'";
|
||||
@@ -161,7 +163,7 @@ http {
|
||||
server {
|
||||
listen 443 ssl;
|
||||
http2 on;
|
||||
server_name {{ GLOBALS.url_base }};
|
||||
server_name {{ full_server_name }};
|
||||
root /opt/socore/html;
|
||||
index index.html;
|
||||
|
||||
|
||||
@@ -30,6 +30,12 @@ nginx:
|
||||
advanced: True
|
||||
global: True
|
||||
helpLink: nginx.html
|
||||
alt_names:
|
||||
description: Provide a list of alternate names to allow remote systems the ability to refer to the SOC API as another hostname.
|
||||
global: True
|
||||
forcedType: '[]string'
|
||||
multiline: True
|
||||
helpLink: nginx.html
|
||||
config:
|
||||
throttle_login_burst:
|
||||
description: Number of login requests that can burst without triggering request throttling. Higher values allow more repeated login attempts. Values greater than zero are required in order to provide a usable login flow.
|
||||
|
||||
+12
-1
@@ -49,6 +49,17 @@ managerssl_key:
|
||||
- docker_container: so-nginx
|
||||
|
||||
# Create a cert for the reverse proxy
|
||||
{% set san_list = [GLOBALS.hostname, GLOBALS.node_ip, GLOBALS.url_base] + NGINXMERGED.ssl.alt_names %}
|
||||
{% set unique_san_list = san_list | unique %}
|
||||
{% set managerssl_san_list = [] %}
|
||||
{% for item in unique_san_list %}
|
||||
{% if item | ipaddr %}
|
||||
{% do managerssl_san_list.append("IP:" + item) %}
|
||||
{% else %}
|
||||
{% do managerssl_san_list.append("DNS:" + item) %}
|
||||
{% endif %}
|
||||
{% endfor %}
|
||||
{% set managerssl_san = managerssl_san_list | join(', ') %}
|
||||
managerssl_crt:
|
||||
x509.certificate_managed:
|
||||
- name: /etc/pki/managerssl.crt
|
||||
@@ -56,7 +67,7 @@ managerssl_crt:
|
||||
- signing_policy: managerssl
|
||||
- private_key: /etc/pki/managerssl.key
|
||||
- CN: {{ GLOBALS.hostname }}
|
||||
- subjectAltName: "DNS:{{ GLOBALS.hostname }}, IP:{{ GLOBALS.node_ip }}, DNS:{{ GLOBALS.url_base }}"
|
||||
- subjectAltName: {{ managerssl_san }}
|
||||
- days_remaining: 7
|
||||
- days_valid: 820
|
||||
- backup: True
|
||||
|
||||
@@ -1,22 +0,0 @@
|
||||
# Copyright Security Onion Solutions LLC and/or licensed to Security Onion Solutions LLC under one
|
||||
# or more contributor license agreements. Licensed under the Elastic License 2.0 as shown at
|
||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||
# Elastic License 2.0.
|
||||
|
||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
||||
{% if sls.split('.')[0] in allowed_states or sls in allowed_states%}
|
||||
|
||||
stenoca:
|
||||
file.directory:
|
||||
- name: /opt/so/conf/steno/certs
|
||||
- user: 941
|
||||
- group: 939
|
||||
- makedirs: True
|
||||
|
||||
{% else %}
|
||||
|
||||
{{sls}}_state_not_allowed:
|
||||
test.fail_without_changes:
|
||||
- name: {{sls}}_state_not_allowed
|
||||
|
||||
{% endif %}
|
||||
@@ -1,13 +0,0 @@
|
||||
{# Copyright Security Onion Solutions LLC and/or licensed to Security Onion Solutions LLC under one
|
||||
or more contributor license agreements. Licensed under the Elastic License 2.0 as shown at
|
||||
https://securityonion.net/license; you may not use this file except in compliance with the
|
||||
Elastic License 2.0. #}
|
||||
|
||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
{% import_yaml 'pcap/defaults.yaml' as PCAPDEFAULTS %}
|
||||
{% set PCAPMERGED = salt['pillar.get']('pcap', PCAPDEFAULTS.pcap, merge=True) %}
|
||||
|
||||
{# disable stenographer if the pcap engine is set to SURICATA #}
|
||||
{% if GLOBALS.pcap_engine == "SURICATA" %}
|
||||
{% do PCAPMERGED.update({'enabled': False}) %}
|
||||
{% endif %}
|
||||
@@ -1,87 +0,0 @@
|
||||
# Copyright Security Onion Solutions LLC and/or licensed to Security Onion Solutions LLC under one
|
||||
# or more contributor license agreements. Licensed under the Elastic License 2.0 as shown at
|
||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||
# Elastic License 2.0.
|
||||
|
||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
||||
{% if sls.split('.')[0] in allowed_states %}
|
||||
|
||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
{% from "pcap/config.map.jinja" import PCAPMERGED %}
|
||||
{% from 'bpf/pcap.map.jinja' import PCAPBPF, PCAP_BPF_STATUS, PCAP_BPF_CALC, STENO_BPF_COMPILED %}
|
||||
|
||||
# PCAP Section
|
||||
stenographergroup:
|
||||
group.present:
|
||||
- name: stenographer
|
||||
- gid: 941
|
||||
|
||||
stenographer:
|
||||
user.present:
|
||||
- uid: 941
|
||||
- gid: 941
|
||||
- home: /opt/so/conf/steno
|
||||
|
||||
stenoconfdir:
|
||||
file.directory:
|
||||
- name: /opt/so/conf/steno
|
||||
- user: 941
|
||||
- group: 939
|
||||
- makedirs: True
|
||||
|
||||
pcap_sbin:
|
||||
file.recurse:
|
||||
- name: /usr/sbin
|
||||
- source: salt://pcap/tools/sbin
|
||||
- user: 939
|
||||
- group: 939
|
||||
- file_mode: 755
|
||||
|
||||
{% if PCAPBPF and not PCAP_BPF_STATUS %}
|
||||
stenoPCAPbpfcompilationfailure:
|
||||
test.configurable_test_state:
|
||||
- changes: False
|
||||
- result: False
|
||||
- comment: "BPF Syntax Error - Discarding Specified BPF. Error: {{ PCAP_BPF_CALC['stderr'] }}"
|
||||
{% endif %}
|
||||
|
||||
stenoconf:
|
||||
file.managed:
|
||||
- name: /opt/so/conf/steno/config
|
||||
- source: salt://pcap/files/config.jinja
|
||||
- user: stenographer
|
||||
- group: stenographer
|
||||
- mode: 644
|
||||
- template: jinja
|
||||
- defaults:
|
||||
PCAPMERGED: {{ PCAPMERGED }}
|
||||
STENO_BPF_COMPILED: "{{ STENO_BPF_COMPILED }}"
|
||||
|
||||
pcaptmpdir:
|
||||
file.directory:
|
||||
- name: /nsm/pcaptmp
|
||||
- user: 941
|
||||
- group: 941
|
||||
- makedirs: True
|
||||
|
||||
pcapindexdir:
|
||||
file.directory:
|
||||
- name: /nsm/pcapindex
|
||||
- user: 941
|
||||
- group: 941
|
||||
- makedirs: True
|
||||
|
||||
stenolog:
|
||||
file.directory:
|
||||
- name: /opt/so/log/stenographer
|
||||
- user: 941
|
||||
- group: 941
|
||||
- makedirs: True
|
||||
|
||||
{% else %}
|
||||
|
||||
{{sls}}_state_not_allowed:
|
||||
test.fail_without_changes:
|
||||
- name: {{sls}}_state_not_allowed
|
||||
|
||||
{% endif %}
|
||||
@@ -1,11 +0,0 @@
|
||||
pcap:
|
||||
enabled: False
|
||||
config:
|
||||
maxdirectoryfiles: 30000
|
||||
diskfreepercentage: 10
|
||||
blocks: 2048
|
||||
preallocate_file_mb: 4096
|
||||
aiops: 128
|
||||
pin_to_cpu: False
|
||||
cpus_to_pin_to: []
|
||||
disks: []
|
||||
@@ -1,27 +0,0 @@
|
||||
# Copyright Security Onion Solutions LLC and/or licensed to Security Onion Solutions LLC under one
|
||||
# or more contributor license agreements. Licensed under the Elastic License 2.0 as shown at
|
||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||
# Elastic License 2.0.
|
||||
|
||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
||||
{% if sls.split('.')[0] in allowed_states %}
|
||||
|
||||
include:
|
||||
- pcap.sostatus
|
||||
|
||||
so-steno:
|
||||
docker_container.absent:
|
||||
- force: True
|
||||
|
||||
so-steno_so-status.disabled:
|
||||
file.comment:
|
||||
- name: /opt/so/conf/so-status/so-status.conf
|
||||
- regex: ^so-steno$
|
||||
|
||||
{% else %}
|
||||
|
||||
{{sls}}_state_not_allowed:
|
||||
test.fail_without_changes:
|
||||
- name: {{sls}}_state_not_allowed
|
||||
|
||||
{% endif %}
|
||||
@@ -1,63 +0,0 @@
|
||||
# Copyright Security Onion Solutions LLC and/or licensed to Security Onion Solutions LLC under one
|
||||
# or more contributor license agreements. Licensed under the Elastic License 2.0 as shown at
|
||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||
# Elastic License 2.0.
|
||||
|
||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
||||
{% if sls.split('.')[0] in allowed_states %}
|
||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
{% from 'docker/docker.map.jinja' import DOCKER %}
|
||||
|
||||
|
||||
include:
|
||||
- pcap.ca
|
||||
- pcap.config
|
||||
- pcap.sostatus
|
||||
|
||||
so-steno:
|
||||
docker_container.running:
|
||||
- image: {{ GLOBALS.registry_host }}:5000/{{ GLOBALS.image_repo }}/so-steno:{{ GLOBALS.so_version }}
|
||||
- start: True
|
||||
- network_mode: host
|
||||
- privileged: True
|
||||
- binds:
|
||||
- /opt/so/conf/steno/certs:/etc/stenographer/certs:rw
|
||||
- /opt/so/conf/steno/config:/etc/stenographer/config:rw
|
||||
- /nsm/pcap:/nsm/pcap:rw
|
||||
- /nsm/pcapindex:/nsm/pcapindex:rw
|
||||
- /nsm/pcaptmp:/tmp:rw
|
||||
- /opt/so/log/stenographer:/var/log/stenographer:rw
|
||||
{% if DOCKER.containers['so-steno'].custom_bind_mounts %}
|
||||
{% for BIND in DOCKER.containers['so-steno'].custom_bind_mounts %}
|
||||
- {{ BIND }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
{% if DOCKER.containers['so-steno'].extra_hosts %}
|
||||
- extra_hosts:
|
||||
{% for XTRAHOST in DOCKER.containers['so-steno'].extra_hosts %}
|
||||
- {{ XTRAHOST }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
{% if DOCKER.containers['so-steno'].extra_env %}
|
||||
- environment:
|
||||
{% for XTRAENV in DOCKER.containers['so-steno'].extra_env %}
|
||||
- {{ XTRAENV }}
|
||||
{% endfor %}
|
||||
{% endif %}
|
||||
- watch:
|
||||
- file: stenoconf
|
||||
- require:
|
||||
- file: stenoconf
|
||||
|
||||
delete_so-steno_so-status.disabled:
|
||||
file.uncomment:
|
||||
- name: /opt/so/conf/so-status/so-status.conf
|
||||
- regex: ^so-steno$
|
||||
|
||||
{% else %}
|
||||
|
||||
{{sls}}_state_not_allowed:
|
||||
test.fail_without_changes:
|
||||
- name: {{sls}}_state_not_allowed
|
||||
|
||||
{% endif %}
|
||||
@@ -1,11 +0,0 @@
|
||||
{
|
||||
"Threads": [
|
||||
{ "PacketsDirectory": "/nsm/pcap", "IndexDirectory": "/nsm/pcapindex", "MaxDirectoryFiles": {{ PCAPMERGED.config.maxdirectoryfiles }}, "DiskFreePercentage": {{ PCAPMERGED.config.diskfreepercentage }} }
|
||||
]
|
||||
, "StenotypePath": "/usr/bin/stenotype"
|
||||
, "Interface": "{{ pillar.sensor.interface }}"
|
||||
, "Port": 1234
|
||||
, "Host": "127.0.0.1"
|
||||
, "Flags": ["-v", "--blocks={{ PCAPMERGED.config.blocks }}", "--preallocate_file_mb={{ PCAPMERGED.config.preallocate_file_mb }}", "--aiops={{ PCAPMERGED.config.aiops }}", "--uid=stenographer", "--gid=stenographer"{{ STENO_BPF_COMPILED }}]
|
||||
, "CertPath": "/etc/stenographer/certs"
|
||||
}
|
||||
@@ -1,41 +0,0 @@
|
||||
# Copyright Security Onion Solutions LLC and/or licensed to Security Onion Solutions LLC under one
|
||||
# or more contributor license agreements. Licensed under the Elastic License 2.0 as shown at
|
||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||
# Elastic License 2.0.
|
||||
|
||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||
{% from 'pcap/config.map.jinja' import PCAPMERGED %}
|
||||
|
||||
include:
|
||||
{% if PCAPMERGED.enabled and GLOBALS.role != 'so-import'%}
|
||||
- pcap.enabled
|
||||
{% elif GLOBALS.role == 'so-import' %}
|
||||
- pcap.config
|
||||
- pcap.disabled
|
||||
{% else %}
|
||||
- pcap.disabled
|
||||
{% endif %}
|
||||
|
||||
# This directory needs to exist regardless of whether STENO is enabled or not, in order for
|
||||
# Sensoroni to be able to look at old steno PCAP data
|
||||
|
||||
# if stenographer has never run as the pcap engine no 941 user is created, so we use socore as a placeholder.
|
||||
# /nsm/pcap is empty until stenographer is used as pcap engine
|
||||
{% set pcap_id = 941 %}
|
||||
{% set user_list = salt['user.list_users']() %}
|
||||
{% if GLOBALS.pcap_engine == "SURICATA" and 'stenographer' not in user_list %}
|
||||
{% set pcap_id = 939 %}
|
||||
{% endif %}
|
||||
pcapdir:
|
||||
file.directory:
|
||||
- name: /nsm/pcap
|
||||
- user: {{ pcap_id }}
|
||||
- group: {{ pcap_id }}
|
||||
- makedirs: True
|
||||
|
||||
pcapoutdir:
|
||||
file.directory:
|
||||
- name: /nsm/pcapout
|
||||
- user: 939
|
||||
- group: 939
|
||||
- makedirs: True
|
||||
@@ -1,35 +0,0 @@
|
||||
pcap:
|
||||
enabled:
|
||||
description: Enables or disables the Stenographer packet recording process. This process may already be disabled if Suricata is being used as the packet capture process.
|
||||
helpLink: stenographer.html
|
||||
config:
|
||||
maxdirectoryfiles:
|
||||
description: By default, Stenographer limits the number of files in the pcap directory to 30000 to avoid limitations with the ext3 filesystem. However, if you're using the ext4 or xfs filesystems, then it is safe to increase this value. So if you have a large amount of storage and find that you only have 3 weeks worth of PCAP on disk while still having plenty of free space, then you may want to increase this default setting.
|
||||
helpLink: stenographer.html
|
||||
diskfreepercentage:
|
||||
description: Stenographer will purge old PCAP on a regular basis to keep the disk free percentage at this level. If you have a distributed deployment with dedicated Sensor nodes, then the default value of 10 should be reasonable since Stenographer should be the main consumer of disk space in the /nsm partition. However, if you have systems that run both Stenographer and Elasticsearch at the same time (like eval and standalone installations), then you’ll want to make sure that this value is no lower than 21 so that you avoid Elasticsearch hitting its watermark setting at 80% disk usage. If you have an older standalone installation, then you may need to manually change this value to 21.
|
||||
helpLink: stenographer.html
|
||||
blocks:
|
||||
description: The number of 1MB packet blocks used by Stenographer and AF_PACKET to store packets in memory, per thread. You shouldn't need to change this.
|
||||
advanced: True
|
||||
helpLink: stenographer.html
|
||||
preallocate_file_mb:
|
||||
description: File size to pre-allocate for individual Stenographer PCAP files. You shouldn't need to change this.
|
||||
advanced: True
|
||||
helpLink: stenographer.html
|
||||
aiops:
|
||||
description: The max number of async writes to allow for Stenographer at once.
|
||||
advanced: True
|
||||
helpLink: stenographer.html
|
||||
pin_to_cpu:
|
||||
description: Enable CPU pinning for Stenographer PCAP.
|
||||
advanced: True
|
||||
helpLink: stenographer.html
|
||||
cpus_to_pin_to:
|
||||
description: CPU to pin Stenographer PCAP to. Currently only a single CPU is supported.
|
||||
advanced: True
|
||||
helpLink: stenographer.html
|
||||
disks:
|
||||
description: List of disks to use for Stenographer PCAP. This is currently not used.
|
||||
advanced: True
|
||||
helpLink: stenographer.html
|
||||
@@ -1,21 +0,0 @@
|
||||
# Copyright Security Onion Solutions LLC and/or licensed to Security Onion Solutions LLC under one
|
||||
# or more contributor license agreements. Licensed under the Elastic License 2.0 as shown at
|
||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||
# Elastic License 2.0.
|
||||
|
||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
||||
{% if sls.split('.')[0] in allowed_states %}
|
||||
|
||||
append_so-steno_so-status.conf:
|
||||
file.append:
|
||||
- name: /opt/so/conf/so-status/so-status.conf
|
||||
- text: so-steno
|
||||
- unless: grep -q so-steno /opt/so/conf/so-status/so-status.conf
|
||||
|
||||
{% else %}
|
||||
|
||||
{{sls}}_state_not_allowed:
|
||||
test.fail_without_changes:
|
||||
- name: {{sls}}_state_not_allowed
|
||||
|
||||
{% endif %}
|
||||
@@ -1,18 +0,0 @@
|
||||
#!/bin/bash
|
||||
#
|
||||
# Copyright Security Onion Solutions LLC and/or licensed to Security Onion Solutions LLC under one
|
||||
# or more contributor license agreements. Licensed under the Elastic License 2.0 as shown at
|
||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||
# Elastic License 2.0.
|
||||
|
||||
|
||||
|
||||
if [ $# -lt 2 ]; then
|
||||
echo "Usage: $0 <steno-query> Output-Filename"
|
||||
exit 1
|
||||
fi
|
||||
|
||||
docker exec -t so-sensoroni scripts/stenoquery.sh "$1" -w /nsm/pcapout/$2.pcap
|
||||
|
||||
echo ""
|
||||
echo "If successful, the output was written to: /nsm/pcapout/$2.pcap"
|
||||
@@ -1,12 +0,0 @@
|
||||
#!/bin/bash
|
||||
#
|
||||
# Copyright Security Onion Solutions LLC and/or licensed to Security Onion Solutions LLC under one
|
||||
# or more contributor license agreements. Licensed under the Elastic License 2.0 as shown at
|
||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||
# Elastic License 2.0.
|
||||
|
||||
|
||||
|
||||
. /usr/sbin/so-common
|
||||
|
||||
/usr/sbin/so-restart steno $1
|
||||
@@ -1,12 +0,0 @@
|
||||
#!/bin/bash
|
||||
#
|
||||
# Copyright Security Onion Solutions LLC and/or licensed to Security Onion Solutions LLC under one
|
||||
# or more contributor license agreements. Licensed under the Elastic License 2.0 as shown at
|
||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||
# Elastic License 2.0.
|
||||
|
||||
|
||||
|
||||
. /usr/sbin/so-common
|
||||
|
||||
/usr/sbin/so-start steno $1
|
||||
@@ -1,12 +0,0 @@
|
||||
#!/bin/bash
|
||||
#
|
||||
# Copyright Security Onion Solutions LLC and/or licensed to Security Onion Solutions LLC under one
|
||||
# or more contributor license agreements. Licensed under the Elastic License 2.0 as shown at
|
||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||
# Elastic License 2.0.
|
||||
|
||||
|
||||
|
||||
. /usr/sbin/so-common
|
||||
|
||||
/usr/sbin/so-stop steno $1
|
||||
@@ -22,18 +22,6 @@ include:
|
||||
{% endif %}
|
||||
|
||||
{% if INSTALLEDSALTVERSION|string != SALTVERSION|string %}
|
||||
|
||||
{# this is added in 2.4.120 to remove salt repo files pointing to saltproject.io to accomodate the move to broadcom and new bootstrap-salt script #}
|
||||
{% if salt['pkg.version_cmp'](GLOBALS.so_version, '2.4.120') == -1 %}
|
||||
{% set saltrepofile = '/etc/yum.repos.d/salt.repo' %}
|
||||
{% if grains.os_family == 'Debian' %}
|
||||
{% set saltrepofile = '/etc/apt/sources.list.d/salt.list' %}
|
||||
{% endif %}
|
||||
remove_saltproject_io_repo_minion:
|
||||
file.absent:
|
||||
- name: {{ saltrepofile }}
|
||||
{% endif %}
|
||||
|
||||
unhold_salt_packages:
|
||||
pkg.unheld:
|
||||
- pkgs:
|
||||
|
||||
@@ -8,9 +8,6 @@
|
||||
|
||||
|
||||
include:
|
||||
{% if GLOBALS.is_sensor or GLOBALS.role == 'so-import' %}
|
||||
- pcap.ca
|
||||
{% endif %}
|
||||
- sensoroni.config
|
||||
- sensoroni.sostatus
|
||||
|
||||
@@ -19,10 +16,6 @@ so-sensoroni:
|
||||
- image: {{ GLOBALS.registry_host }}:5000/{{ GLOBALS.image_repo }}/so-soc:{{ GLOBALS.so_version }}
|
||||
- network_mode: host
|
||||
- binds:
|
||||
{% if GLOBALS.is_sensor or GLOBALS.role == 'so-import' %}
|
||||
- /opt/so/conf/steno/certs:/etc/stenographer/certs:rw
|
||||
{% endif %}
|
||||
- /nsm/pcap:/nsm/pcap:rw
|
||||
- /nsm/import:/nsm/import:rw
|
||||
- /nsm/pcapout:/nsm/pcapout:rw
|
||||
- /opt/so/conf/sensoroni/sensoroni.json:/opt/sensoroni/sensoroni.json:ro
|
||||
|
||||
@@ -14,7 +14,7 @@ An API key or User Credentials is necessary for utilizing Elasticsearch.
|
||||
|
||||
In SOC, navigate to `Administration`, toggle `Show all configurable settings, including advanced settings.`, and navigate to `sensoroni` -> `analyzers` -> `elasticsearch`.
|
||||
|
||||

|
||||

|
||||
|
||||
|
||||
The following configuration options are available for:
|
||||
|
||||
@@ -6,7 +6,7 @@ Submit a base64-encoded EML file to Sublime Platform for analysis.
|
||||
## Configuration Requirements
|
||||
In SOC, navigate to `Administration`, toggle `Show all configurable settings, including advanced settings.`, and navigate to `sensoroni` -> `analyzers` -> `sublime_platform`.
|
||||
|
||||

|
||||

|
||||
|
||||
|
||||
The following configuration options are available for:
|
||||
|
||||
@@ -32,11 +32,6 @@
|
||||
"apiKey": "{{ GLOBALS.sensoroni_key }}"
|
||||
{% if GLOBALS.is_sensor %}
|
||||
},
|
||||
"stenoquery": {
|
||||
"executablePath": "/opt/sensoroni/scripts/stenoquery.sh",
|
||||
"pcapInputPath": "/nsm/pcap",
|
||||
"pcapOutputPath": "/nsm/pcapout"
|
||||
},
|
||||
"suriquery": {
|
||||
"pcapInputPath": "/nsm/suripcap",
|
||||
"pcapOutputPath": "/nsm/pcapout",
|
||||
|
||||
@@ -10,7 +10,7 @@
|
||||
{% from 'suricata/map.jinja' import SURICATAMERGED %}
|
||||
{% from 'bpf/suricata.map.jinja' import SURICATABPF, SURICATA_BPF_STATUS, SURICATA_BPF_CALC %}
|
||||
|
||||
{% if GLOBALS.pcap_engine in ["SURICATA", "TRANSITION"] %}
|
||||
{% if GLOBALS.pcap_engine in ["SURICATA"] %}
|
||||
{% from 'bpf/pcap.map.jinja' import PCAPBPF, PCAP_BPF_STATUS, PCAP_BPF_CALC %}
|
||||
# BPF compilation and configuration
|
||||
{% if PCAPBPF and not PCAP_BPF_STATUS %}
|
||||
|
||||
@@ -9,7 +9,7 @@
|
||||
{% set surimeta_filestore_index = [] %}
|
||||
|
||||
{# before we change outputs back to list, enable pcap-log if suricata is the pcapengine #}
|
||||
{% if GLOBALS.pcap_engine in ["SURICATA", "TRANSITION"] %}
|
||||
{% if GLOBALS.pcap_engine in ["SURICATA"] %}
|
||||
|
||||
{% from 'bpf/pcap.map.jinja' import PCAPBPF, PCAP_BPF_STATUS %}
|
||||
{% if PCAPBPF and PCAP_BPF_STATUS %}
|
||||
|
||||
@@ -2,7 +2,7 @@
|
||||
{% from 'suricata/map.jinja' import SURICATAMERGED %}
|
||||
|
||||
# This directory needs to exist regardless of whether SURIPCAP is enabled or not, in order for
|
||||
# Sensoroni to be able to look at old Suricata PCAP data
|
||||
# Sensoroni to mount it
|
||||
suripcapdir:
|
||||
file.directory:
|
||||
- name: /nsm/suripcap
|
||||
@@ -11,7 +11,14 @@ suripcapdir:
|
||||
- mode: 775
|
||||
- makedirs: True
|
||||
|
||||
{% if GLOBALS.pcap_engine in ["SURICATA", "TRANSITION"] %}
|
||||
pcapoutdir:
|
||||
file.directory:
|
||||
- name: /nsm/pcapout
|
||||
- user: 939
|
||||
- group: 939
|
||||
- makedirs: True
|
||||
|
||||
{% if GLOBALS.pcap_engine in ["SURICATA"] %}
|
||||
|
||||
{# there should only be 1 interface in af-packet so we can just reference the first list item #}
|
||||
{% for i in range(1, SURICATAMERGED.config['af-packet'][0].threads + 1) %}
|
||||
|
||||
@@ -31,8 +31,9 @@ mkdir -p /tmp/nids-testing/output
|
||||
chown suricata:socore /tmp/nids-testing/output
|
||||
mkdir -p /tmp/nids-testing/rules
|
||||
|
||||
cp /opt/so/conf/suricata/rules/all.rules /tmp/nids-testing/rules/all.rules
|
||||
cat $TESTRULE >> /tmp/nids-testing/rules/all.rules
|
||||
cp /opt/so/rules/suricata/all-rulesets.rules /tmp/nids-testing/rules/all-rulesets.rules
|
||||
cat $TESTRULE >> /tmp/nids-testing/rules/all-rulesets.rules
|
||||
|
||||
|
||||
echo "==== Begin Suricata Output ==="
|
||||
|
||||
|
||||
@@ -19,7 +19,6 @@ telegraf:
|
||||
- os.sh
|
||||
- raid.sh
|
||||
- sostatus.sh
|
||||
- stenoloss.sh
|
||||
- suriloss.sh
|
||||
- surirules.sh
|
||||
- zeekcaptureloss.sh
|
||||
@@ -35,7 +34,6 @@ telegraf:
|
||||
- raid.sh
|
||||
- redis.sh
|
||||
- sostatus.sh
|
||||
- stenoloss.sh
|
||||
- suriloss.sh
|
||||
- surirules.sh
|
||||
- zeekcaptureloss.sh
|
||||
@@ -81,7 +79,6 @@ telegraf:
|
||||
- os.sh
|
||||
- raid.sh
|
||||
- sostatus.sh
|
||||
- stenoloss.sh
|
||||
- suriloss.sh
|
||||
- surirules.sh
|
||||
- zeekcaptureloss.sh
|
||||
@@ -96,7 +93,6 @@ telegraf:
|
||||
- raid.sh
|
||||
- redis.sh
|
||||
- sostatus.sh
|
||||
- stenoloss.sh
|
||||
- suriloss.sh
|
||||
- surirules.sh
|
||||
- zeekcaptureloss.sh
|
||||
|
||||
@@ -47,7 +47,6 @@ so-telegraf:
|
||||
- /etc/pki/telegraf.crt:/etc/telegraf/telegraf.crt:ro
|
||||
- /etc/pki/telegraf.key:/etc/telegraf/telegraf.key:ro
|
||||
- /opt/so/conf/telegraf/scripts:/scripts:ro
|
||||
- /opt/so/log/stenographer:/var/log/stenographer:ro
|
||||
- /opt/so/log/suricata:/var/log/suricata:ro
|
||||
- /opt/so/log/raid:/var/log/raid:ro
|
||||
- /opt/so/log/sostatus:/var/log/sostatus:ro
|
||||
|
||||
@@ -14,13 +14,6 @@
|
||||
{% do TELEGRAFMERGED.scripts[GLOBALS.role.split('-')[1]].remove('zeekloss.sh') %}
|
||||
{% do TELEGRAFMERGED.scripts[GLOBALS.role.split('-')[1]].remove('zeekcaptureloss.sh') %}
|
||||
{% endif %}
|
||||
|
||||
{% from 'pcap/config.map.jinja' import PCAPMERGED %}
|
||||
{# PCAPMERGED.enabled is set false in soc ui or if suricata is the pcap engine #}
|
||||
{% if not PCAPMERGED.enabled %}
|
||||
{% do TELEGRAFMERGED.scripts[GLOBALS.role.split('-')[1]].remove('stenoloss.sh') %}
|
||||
{% endif %}
|
||||
|
||||
{% endif %}
|
||||
|
||||
{% if GLOBALS.pipeline != 'REDIS' %}
|
||||
|
||||
@@ -5,11 +5,7 @@
|
||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||
# Elastic License 2.0.
|
||||
|
||||
{%- if GLOBALS.pcap_engine in ["SURICATA", "TRANSITION"] %}
|
||||
PCAPLOC=/host/nsm/suripcap
|
||||
{%- else %}
|
||||
PCAPLOC=/host/nsm/pcap
|
||||
{%- endif %}
|
||||
|
||||
# if this script isn't already running
|
||||
if [[ ! "`pidof -x $(basename $0) -o %PPID`" ]]; then
|
||||
|
||||
@@ -1,39 +0,0 @@
|
||||
#!/bin/bash
|
||||
#
|
||||
# Copyright Security Onion Solutions LLC and/or licensed to Security Onion Solutions LLC under one
|
||||
# or more contributor license agreements. Licensed under the Elastic License 2.0 as shown at
|
||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||
# Elastic License 2.0.
|
||||
|
||||
|
||||
|
||||
# if this script isn't already running
|
||||
if [[ ! "`pidof -x $(basename $0) -o %PPID`" ]]; then
|
||||
|
||||
CHECKIT=$(grep "Thread 0 stats" /var/log/stenographer/stenographer.log |tac |head -2|wc -l)
|
||||
STENOGREP=$(grep "Thread 0 stats" /var/log/stenographer/stenographer.log |tac |head -2)
|
||||
|
||||
declare RESULT=($STENOGREP)
|
||||
|
||||
CURRENT_PACKETS=$(echo ${RESULT[9]} | awk -F'=' '{print $2 }')
|
||||
CURRENT_DROPS=$(echo ${RESULT[12]} | awk -F'=' '{print $2 }')
|
||||
PREVIOUS_PACKETS=$(echo ${RESULT[23]} | awk -F'=' '{print $2 }')
|
||||
PREVIOUS_DROPS=$(echo ${RESULT[26]} | awk -F'=' '{print $2 }')
|
||||
|
||||
DROPPED=$((CURRENT_DROPS - PREVIOUS_DROPS))
|
||||
TOTAL_CURRENT=$((CURRENT_PACKETS + CURRENT_DROPS))
|
||||
TOTAL_PAST=$((PREVIOUS_PACKETS + PREVIOUS_DROPS))
|
||||
TOTAL=$((TOTAL_CURRENT - TOTAL_PAST))
|
||||
|
||||
if [ $CHECKIT == 2 ]; then
|
||||
if [ $DROPPED == 0 ]; then
|
||||
echo "stenodrop drop=$DROPPED"
|
||||
else
|
||||
LOSS=$(echo "4 k $DROPPED $TOTAL / 100 * p" | dc)
|
||||
echo "stenodrop drop=$LOSS"
|
||||
fi
|
||||
fi
|
||||
|
||||
fi
|
||||
|
||||
exit 0
|
||||
@@ -47,7 +47,7 @@ telegraf_key_perms:
|
||||
- group: 939
|
||||
|
||||
{% if not GLOBALS.is_manager %}
|
||||
{# Prior to 2.4.220, minions used influxdb.crt and key for telegraf #}
|
||||
{# Prior to 2.4.210, minions used influxdb.crt and key for telegraf #}
|
||||
remove_influxdb.crt:
|
||||
file.absent:
|
||||
- name: /etc/pki/influxdb.crt
|
||||
|
||||
@@ -78,7 +78,6 @@ base:
|
||||
- elasticsearch
|
||||
- elastic-fleet-package-registry
|
||||
- kibana
|
||||
- pcap
|
||||
- suricata
|
||||
- zeek
|
||||
- strelka
|
||||
@@ -108,7 +107,6 @@ base:
|
||||
- redis
|
||||
- elastic-fleet-package-registry
|
||||
- kibana
|
||||
- pcap
|
||||
- suricata
|
||||
- zeek
|
||||
- strelka
|
||||
@@ -192,7 +190,6 @@ base:
|
||||
- sensoroni
|
||||
- telegraf
|
||||
- firewall
|
||||
- pcap
|
||||
- elasticsearch
|
||||
- elastic-fleet-package-registry
|
||||
- kibana
|
||||
@@ -220,7 +217,6 @@ base:
|
||||
- telegraf
|
||||
- firewall
|
||||
- nginx
|
||||
- pcap
|
||||
- suricata
|
||||
- healthcheck
|
||||
- zeek
|
||||
@@ -240,7 +236,6 @@ base:
|
||||
- redis
|
||||
- curator.disabled
|
||||
- strelka
|
||||
- pcap
|
||||
- suricata
|
||||
- zeek
|
||||
- elasticfleet.install_agent_grid
|
||||
|
||||
+7
-10
@@ -1382,9 +1382,7 @@ create_global() {
|
||||
echo " registry_host: '$HOSTNAME'" >> $global_pillar_file
|
||||
echo " endgamehost: '$ENDGAMEHOST'" >> $global_pillar_file
|
||||
|
||||
if [[ $is_standalone || $is_eval ]]; then
|
||||
echo " pcapengine: SURICATA" >> $global_pillar_file
|
||||
fi
|
||||
echo " pcapengine: SURICATA" >> $global_pillar_file
|
||||
}
|
||||
|
||||
create_sensoroni_pillar() {
|
||||
@@ -1446,7 +1444,7 @@ make_some_dirs() {
|
||||
mkdir -p $local_salt_dir/salt/firewall/portgroups
|
||||
mkdir -p $local_salt_dir/salt/firewall/ports
|
||||
|
||||
for THEDIR in bpf pcap elasticsearch ntp firewall redis backup influxdb strelka sensoroni soc docker zeek suricata nginx telegraf logstash soc manager kratos hydra idh elastalert stig global kafka versionlock hypervisor vm; do
|
||||
for THEDIR in bpf elasticsearch ntp firewall redis backup influxdb strelka sensoroni soc docker zeek suricata nginx telegraf logstash soc manager kratos hydra idh elastalert stig global kafka versionlock hypervisor vm; do
|
||||
mkdir -p $local_salt_dir/pillar/$THEDIR
|
||||
touch $local_salt_dir/pillar/$THEDIR/adv_$THEDIR.sls
|
||||
touch $local_salt_dir/pillar/$THEDIR/soc_$THEDIR.sls
|
||||
@@ -1600,7 +1598,6 @@ reserve_group_ids() {
|
||||
logCmd "groupadd -g 940 suricata"
|
||||
logCmd "groupadd -g 948 elastic-agent-pr"
|
||||
logCmd "groupadd -g 949 elastic-agent"
|
||||
logCmd "groupadd -g 941 stenographer"
|
||||
logCmd "groupadd -g 947 elastic-fleet"
|
||||
logCmd "groupadd -g 960 kafka"
|
||||
}
|
||||
@@ -1798,8 +1795,8 @@ securityonion_repo() {
|
||||
if ! $is_desktop_grid; then
|
||||
gpg_rpm_import
|
||||
if [[ ! $is_airgap ]]; then
|
||||
echo "https://repo.securityonion.net/file/so-repo/prod/2.4/oracle/9" > /etc/yum/mirror.txt
|
||||
echo "https://so-repo-east.s3.us-east-005.backblazeb2.com/prod/2.4/oracle/9" >> /etc/yum/mirror.txt
|
||||
echo "https://repo.securityonion.net/file/so-repo/prod/3/oracle/9" > /etc/yum/mirror.txt
|
||||
echo "https://so-repo-east.s3.us-east-005.backblazeb2.com/prod/3/oracle/9" >> /etc/yum/mirror.txt
|
||||
echo "[main]" > /etc/yum.repos.d/securityonion.repo
|
||||
echo "gpgcheck=1" >> /etc/yum.repos.d/securityonion.repo
|
||||
echo "installonly_limit=3" >> /etc/yum.repos.d/securityonion.repo
|
||||
@@ -1857,8 +1854,8 @@ repo_sync_local() {
|
||||
info "Adding Repo Download Configuration"
|
||||
mkdir -p /nsm/repo
|
||||
mkdir -p /opt/so/conf/reposync/cache
|
||||
echo "https://repo.securityonion.net/file/so-repo/prod/2.4/oracle/9" > /opt/so/conf/reposync/mirror.txt
|
||||
echo "https://repo-alt.securityonion.net/prod/2.4/oracle/9" >> /opt/so/conf/reposync/mirror.txt
|
||||
echo "https://repo.securityonion.net/file/so-repo/prod/3/oracle/9" > /opt/so/conf/reposync/mirror.txt
|
||||
echo "https://repo-alt.securityonion.net/prod/3/oracle/9" >> /opt/so/conf/reposync/mirror.txt
|
||||
echo "[main]" > /opt/so/conf/reposync/repodownload.conf
|
||||
echo "gpgcheck=1" >> /opt/so/conf/reposync/repodownload.conf
|
||||
echo "installonly_limit=3" >> /opt/so/conf/reposync/repodownload.conf
|
||||
@@ -1895,7 +1892,7 @@ repo_sync_local() {
|
||||
logCmd "dnf -y install epel-release"
|
||||
fi
|
||||
dnf install -y yum-utils device-mapper-persistent-data lvm2
|
||||
curl -fsSL https://repo.securityonion.net/file/so-repo/prod/2.4/so/so.repo | tee /etc/yum.repos.d/so.repo
|
||||
curl -fsSL https://repo.securityonion.net/file/so-repo/prod/3/so/so.repo | tee /etc/yum.repos.d/so.repo
|
||||
rpm --import https://packages.broadcom.com/artifactory/api/security/keypair/SaltProjectKey/public
|
||||
dnf config-manager --add-repo https://download.docker.com/linux/centos/docker-ce.repo
|
||||
curl -fsSL "https://github.com/saltstack/salt-install-guide/releases/latest/download/salt.repo" | tee /etc/yum.repos.d/salt.repo
|
||||
|
||||
Reference in New Issue
Block a user