mirror of
https://github.com/Security-Onion-Solutions/securityonion.git
synced 2026-03-24 13:32:37 +01:00
Compare commits
1 Commits
customulim
...
TOoSmOotH-
| Author | SHA1 | Date | |
|---|---|---|---|
|
|
cef71b41e2 |
9
.github/DISCUSSION_TEMPLATE/2-4.yml
vendored
9
.github/DISCUSSION_TEMPLATE/2-4.yml
vendored
@@ -2,11 +2,13 @@ body:
|
|||||||
- type: markdown
|
- type: markdown
|
||||||
attributes:
|
attributes:
|
||||||
value: |
|
value: |
|
||||||
|
⚠️ This category is solely for conversations related to Security Onion 2.4 ⚠️
|
||||||
|
|
||||||
If your organization needs more immediate, enterprise grade professional support, with one-on-one virtual meetings and screensharing, contact us via our website: https://securityonion.com/support
|
If your organization needs more immediate, enterprise grade professional support, with one-on-one virtual meetings and screensharing, contact us via our website: https://securityonion.com/support
|
||||||
- type: dropdown
|
- type: dropdown
|
||||||
attributes:
|
attributes:
|
||||||
label: Version
|
label: Version
|
||||||
description: Which version of Security Onion are you asking about?
|
description: Which version of Security Onion 2.4.x are you asking about?
|
||||||
options:
|
options:
|
||||||
-
|
-
|
||||||
- 2.4.10
|
- 2.4.10
|
||||||
@@ -31,9 +33,6 @@ body:
|
|||||||
- 2.4.180
|
- 2.4.180
|
||||||
- 2.4.190
|
- 2.4.190
|
||||||
- 2.4.200
|
- 2.4.200
|
||||||
- 2.4.201
|
|
||||||
- 2.4.210
|
|
||||||
- 2.4.211
|
|
||||||
- Other (please provide detail below)
|
- Other (please provide detail below)
|
||||||
validations:
|
validations:
|
||||||
required: true
|
required: true
|
||||||
@@ -95,7 +94,7 @@ body:
|
|||||||
attributes:
|
attributes:
|
||||||
label: Hardware Specs
|
label: Hardware Specs
|
||||||
description: >
|
description: >
|
||||||
Does your hardware meet or exceed the minimum requirements for your installation type as shown at https://securityonion.net/docs/hardware?
|
Does your hardware meet or exceed the minimum requirements for your installation type as shown at https://docs.securityonion.net/en/2.4/hardware.html?
|
||||||
options:
|
options:
|
||||||
-
|
-
|
||||||
- Meets minimum requirements
|
- Meets minimum requirements
|
||||||
|
|||||||
177
.github/DISCUSSION_TEMPLATE/3-0.yml
vendored
177
.github/DISCUSSION_TEMPLATE/3-0.yml
vendored
@@ -1,177 +0,0 @@
|
|||||||
body:
|
|
||||||
- type: markdown
|
|
||||||
attributes:
|
|
||||||
value: |
|
|
||||||
If your organization needs more immediate, enterprise grade professional support, with one-on-one virtual meetings and screensharing, contact us via our website: https://securityonion.com/support
|
|
||||||
- type: dropdown
|
|
||||||
attributes:
|
|
||||||
label: Version
|
|
||||||
description: Which version of Security Onion are you asking about?
|
|
||||||
options:
|
|
||||||
-
|
|
||||||
- 3.0.0
|
|
||||||
- Other (please provide detail below)
|
|
||||||
validations:
|
|
||||||
required: true
|
|
||||||
- type: dropdown
|
|
||||||
attributes:
|
|
||||||
label: Installation Method
|
|
||||||
description: How did you install Security Onion?
|
|
||||||
options:
|
|
||||||
-
|
|
||||||
- Security Onion ISO image
|
|
||||||
- Cloud image (Amazon, Azure, Google)
|
|
||||||
- Network installation on Oracle 9 (unsupported)
|
|
||||||
- Other (please provide detail below)
|
|
||||||
validations:
|
|
||||||
required: true
|
|
||||||
- type: dropdown
|
|
||||||
attributes:
|
|
||||||
label: Description
|
|
||||||
description: >
|
|
||||||
Is this discussion about installation, configuration, upgrading, or other?
|
|
||||||
options:
|
|
||||||
-
|
|
||||||
- installation
|
|
||||||
- configuration
|
|
||||||
- upgrading
|
|
||||||
- other (please provide detail below)
|
|
||||||
validations:
|
|
||||||
required: true
|
|
||||||
- type: dropdown
|
|
||||||
attributes:
|
|
||||||
label: Installation Type
|
|
||||||
description: >
|
|
||||||
When you installed, did you choose Import, Eval, Standalone, Distributed, or something else?
|
|
||||||
options:
|
|
||||||
-
|
|
||||||
- Import
|
|
||||||
- Eval
|
|
||||||
- Standalone
|
|
||||||
- Distributed
|
|
||||||
- other (please provide detail below)
|
|
||||||
validations:
|
|
||||||
required: true
|
|
||||||
- type: dropdown
|
|
||||||
attributes:
|
|
||||||
label: Location
|
|
||||||
description: >
|
|
||||||
Is this deployment in the cloud, on-prem with Internet access, or airgap?
|
|
||||||
options:
|
|
||||||
-
|
|
||||||
- cloud
|
|
||||||
- on-prem with Internet access
|
|
||||||
- airgap
|
|
||||||
- other (please provide detail below)
|
|
||||||
validations:
|
|
||||||
required: true
|
|
||||||
- type: dropdown
|
|
||||||
attributes:
|
|
||||||
label: Hardware Specs
|
|
||||||
description: >
|
|
||||||
Does your hardware meet or exceed the minimum requirements for your installation type as shown at https://securityonion.net/docs/hardware?
|
|
||||||
options:
|
|
||||||
-
|
|
||||||
- Meets minimum requirements
|
|
||||||
- Exceeds minimum requirements
|
|
||||||
- Does not meet minimum requirements
|
|
||||||
- other (please provide detail below)
|
|
||||||
validations:
|
|
||||||
required: true
|
|
||||||
- type: input
|
|
||||||
attributes:
|
|
||||||
label: CPU
|
|
||||||
description: How many CPU cores do you have?
|
|
||||||
validations:
|
|
||||||
required: true
|
|
||||||
- type: input
|
|
||||||
attributes:
|
|
||||||
label: RAM
|
|
||||||
description: How much RAM do you have?
|
|
||||||
validations:
|
|
||||||
required: true
|
|
||||||
- type: input
|
|
||||||
attributes:
|
|
||||||
label: Storage for /
|
|
||||||
description: How much storage do you have for the / partition?
|
|
||||||
validations:
|
|
||||||
required: true
|
|
||||||
- type: input
|
|
||||||
attributes:
|
|
||||||
label: Storage for /nsm
|
|
||||||
description: How much storage do you have for the /nsm partition?
|
|
||||||
validations:
|
|
||||||
required: true
|
|
||||||
- type: dropdown
|
|
||||||
attributes:
|
|
||||||
label: Network Traffic Collection
|
|
||||||
description: >
|
|
||||||
Are you collecting network traffic from a tap or span port?
|
|
||||||
options:
|
|
||||||
-
|
|
||||||
- tap
|
|
||||||
- span port
|
|
||||||
- other (please provide detail below)
|
|
||||||
validations:
|
|
||||||
required: true
|
|
||||||
- type: dropdown
|
|
||||||
attributes:
|
|
||||||
label: Network Traffic Speeds
|
|
||||||
description: >
|
|
||||||
How much network traffic are you monitoring?
|
|
||||||
options:
|
|
||||||
-
|
|
||||||
- Less than 1Gbps
|
|
||||||
- 1Gbps to 10Gbps
|
|
||||||
- more than 10Gbps
|
|
||||||
validations:
|
|
||||||
required: true
|
|
||||||
- type: dropdown
|
|
||||||
attributes:
|
|
||||||
label: Status
|
|
||||||
description: >
|
|
||||||
Does SOC Grid show all services on all nodes as running OK?
|
|
||||||
options:
|
|
||||||
-
|
|
||||||
- Yes, all services on all nodes are running OK
|
|
||||||
- No, one or more services are failed (please provide detail below)
|
|
||||||
validations:
|
|
||||||
required: true
|
|
||||||
- type: dropdown
|
|
||||||
attributes:
|
|
||||||
label: Salt Status
|
|
||||||
description: >
|
|
||||||
Do you get any failures when you run "sudo salt-call state.highstate"?
|
|
||||||
options:
|
|
||||||
-
|
|
||||||
- Yes, there are salt failures (please provide detail below)
|
|
||||||
- No, there are no failures
|
|
||||||
validations:
|
|
||||||
required: true
|
|
||||||
- type: dropdown
|
|
||||||
attributes:
|
|
||||||
label: Logs
|
|
||||||
description: >
|
|
||||||
Are there any additional clues in /opt/so/log/?
|
|
||||||
options:
|
|
||||||
-
|
|
||||||
- Yes, there are additional clues in /opt/so/log/ (please provide detail below)
|
|
||||||
- No, there are no additional clues
|
|
||||||
validations:
|
|
||||||
required: true
|
|
||||||
- type: textarea
|
|
||||||
attributes:
|
|
||||||
label: Detail
|
|
||||||
description: Please read our discussion guidelines at https://github.com/Security-Onion-Solutions/securityonion/discussions/1720 and then provide detailed information to help us help you.
|
|
||||||
placeholder: |-
|
|
||||||
STOP! Before typing, please read our discussion guidelines at https://github.com/Security-Onion-Solutions/securityonion/discussions/1720 in their entirety!
|
|
||||||
|
|
||||||
If your organization needs more immediate, enterprise grade professional support, with one-on-one virtual meetings and screensharing, contact us via our website: https://securityonion.com/support
|
|
||||||
validations:
|
|
||||||
required: true
|
|
||||||
- type: checkboxes
|
|
||||||
attributes:
|
|
||||||
label: Guidelines
|
|
||||||
options:
|
|
||||||
- label: I have read the discussion guidelines at https://github.com/Security-Onion-Solutions/securityonion/discussions/1720 and assert that I have followed the guidelines.
|
|
||||||
required: true
|
|
||||||
2
.github/workflows/pythontest.yml
vendored
2
.github/workflows/pythontest.yml
vendored
@@ -13,7 +13,7 @@ jobs:
|
|||||||
strategy:
|
strategy:
|
||||||
fail-fast: false
|
fail-fast: false
|
||||||
matrix:
|
matrix:
|
||||||
python-version: ["3.14"]
|
python-version: ["3.13"]
|
||||||
python-code-path: ["salt/sensoroni/files/analyzers", "salt/manager/tools/sbin"]
|
python-code-path: ["salt/sensoroni/files/analyzers", "salt/manager/tools/sbin"]
|
||||||
|
|
||||||
steps:
|
steps:
|
||||||
|
|||||||
@@ -1,17 +1,17 @@
|
|||||||
### 2.4.210-20260302 ISO image released on 2026/03/02
|
### 2.4.201-20260114 ISO image released on 2026/1/15
|
||||||
|
|
||||||
|
|
||||||
### Download and Verify
|
### Download and Verify
|
||||||
|
|
||||||
2.4.210-20260302 ISO image:
|
2.4.201-20260114 ISO image:
|
||||||
https://download.securityonion.net/file/securityonion/securityonion-2.4.210-20260302.iso
|
https://download.securityonion.net/file/securityonion/securityonion-2.4.201-20260114.iso
|
||||||
|
|
||||||
MD5: 575F316981891EBED2EE4E1F42A1F016
|
MD5: 20E926E433203798512EF46E590C89B9
|
||||||
SHA1: 600945E8823221CBC5F1C056084A71355308227E
|
SHA1: 779E4084A3E1A209B494493B8F5658508B6014FA
|
||||||
SHA256: A6AA6471125F07FA6E2796430E94BEAFDEF728E833E9728FDFA7106351EBC47E
|
SHA256: 3D10E7C885AEC5C5D4F4E50F9644FF9728E8C0A2E36EBB8C96B32569685A7C40
|
||||||
|
|
||||||
Signature for ISO image:
|
Signature for ISO image:
|
||||||
https://github.com/Security-Onion-Solutions/securityonion/raw/2.4/main/sigs/securityonion-2.4.210-20260302.iso.sig
|
https://github.com/Security-Onion-Solutions/securityonion/raw/2.4/main/sigs/securityonion-2.4.201-20260114.iso.sig
|
||||||
|
|
||||||
Signing key:
|
Signing key:
|
||||||
https://raw.githubusercontent.com/Security-Onion-Solutions/securityonion/2.4/main/KEYS
|
https://raw.githubusercontent.com/Security-Onion-Solutions/securityonion/2.4/main/KEYS
|
||||||
@@ -25,22 +25,22 @@ wget https://raw.githubusercontent.com/Security-Onion-Solutions/securityonion/2.
|
|||||||
|
|
||||||
Download the signature file for the ISO:
|
Download the signature file for the ISO:
|
||||||
```
|
```
|
||||||
wget https://github.com/Security-Onion-Solutions/securityonion/raw/2.4/main/sigs/securityonion-2.4.210-20260302.iso.sig
|
wget https://github.com/Security-Onion-Solutions/securityonion/raw/2.4/main/sigs/securityonion-2.4.201-20260114.iso.sig
|
||||||
```
|
```
|
||||||
|
|
||||||
Download the ISO image:
|
Download the ISO image:
|
||||||
```
|
```
|
||||||
wget https://download.securityonion.net/file/securityonion/securityonion-2.4.210-20260302.iso
|
wget https://download.securityonion.net/file/securityonion/securityonion-2.4.201-20260114.iso
|
||||||
```
|
```
|
||||||
|
|
||||||
Verify the downloaded ISO image using the signature file:
|
Verify the downloaded ISO image using the signature file:
|
||||||
```
|
```
|
||||||
gpg --verify securityonion-2.4.210-20260302.iso.sig securityonion-2.4.210-20260302.iso
|
gpg --verify securityonion-2.4.201-20260114.iso.sig securityonion-2.4.201-20260114.iso
|
||||||
```
|
```
|
||||||
|
|
||||||
The output should show "Good signature" and the Primary key fingerprint should match what's shown below:
|
The output should show "Good signature" and the Primary key fingerprint should match what's shown below:
|
||||||
```
|
```
|
||||||
gpg: Signature made Mon 02 Mar 2026 11:55:24 AM EST using RSA key ID FE507013
|
gpg: Signature made Wed 14 Jan 2026 05:23:39 PM EST using RSA key ID FE507013
|
||||||
gpg: Good signature from "Security Onion Solutions, LLC <info@securityonionsolutions.com>"
|
gpg: Good signature from "Security Onion Solutions, LLC <info@securityonionsolutions.com>"
|
||||||
gpg: WARNING: This key is not certified with a trusted signature!
|
gpg: WARNING: This key is not certified with a trusted signature!
|
||||||
gpg: There is no indication that the signature belongs to the owner.
|
gpg: There is no indication that the signature belongs to the owner.
|
||||||
@@ -50,4 +50,4 @@ Primary key fingerprint: C804 A93D 36BE 0C73 3EA1 9644 7C10 60B7 FE50 7013
|
|||||||
If it fails to verify, try downloading again. If it still fails to verify, try downloading from another computer or another network.
|
If it fails to verify, try downloading again. If it still fails to verify, try downloading from another computer or another network.
|
||||||
|
|
||||||
Once you've verified the ISO image, you're ready to proceed to our Installation guide:
|
Once you've verified the ISO image, you're ready to proceed to our Installation guide:
|
||||||
https://securityonion.net/docs/installation
|
https://docs.securityonion.net/en/2.4/installation.html
|
||||||
|
|||||||
66
README.md
66
README.md
@@ -1,58 +1,50 @@
|
|||||||
<p align="center">
|
## Security Onion 2.4
|
||||||
<img src="https://securityonionsolutions.com/logo/logo-so-onion-dark.svg" width="400" alt="Security Onion Logo">
|
|
||||||
</p>
|
|
||||||
|
|
||||||
# Security Onion
|
Security Onion 2.4 is here!
|
||||||
|
|
||||||
Security Onion is a free and open Linux distribution for threat hunting, enterprise security monitoring, and log management. It includes a comprehensive suite of tools designed to work together to provide visibility into your network and host activity.
|
## Screenshots
|
||||||
|
|
||||||
## ✨ Features
|
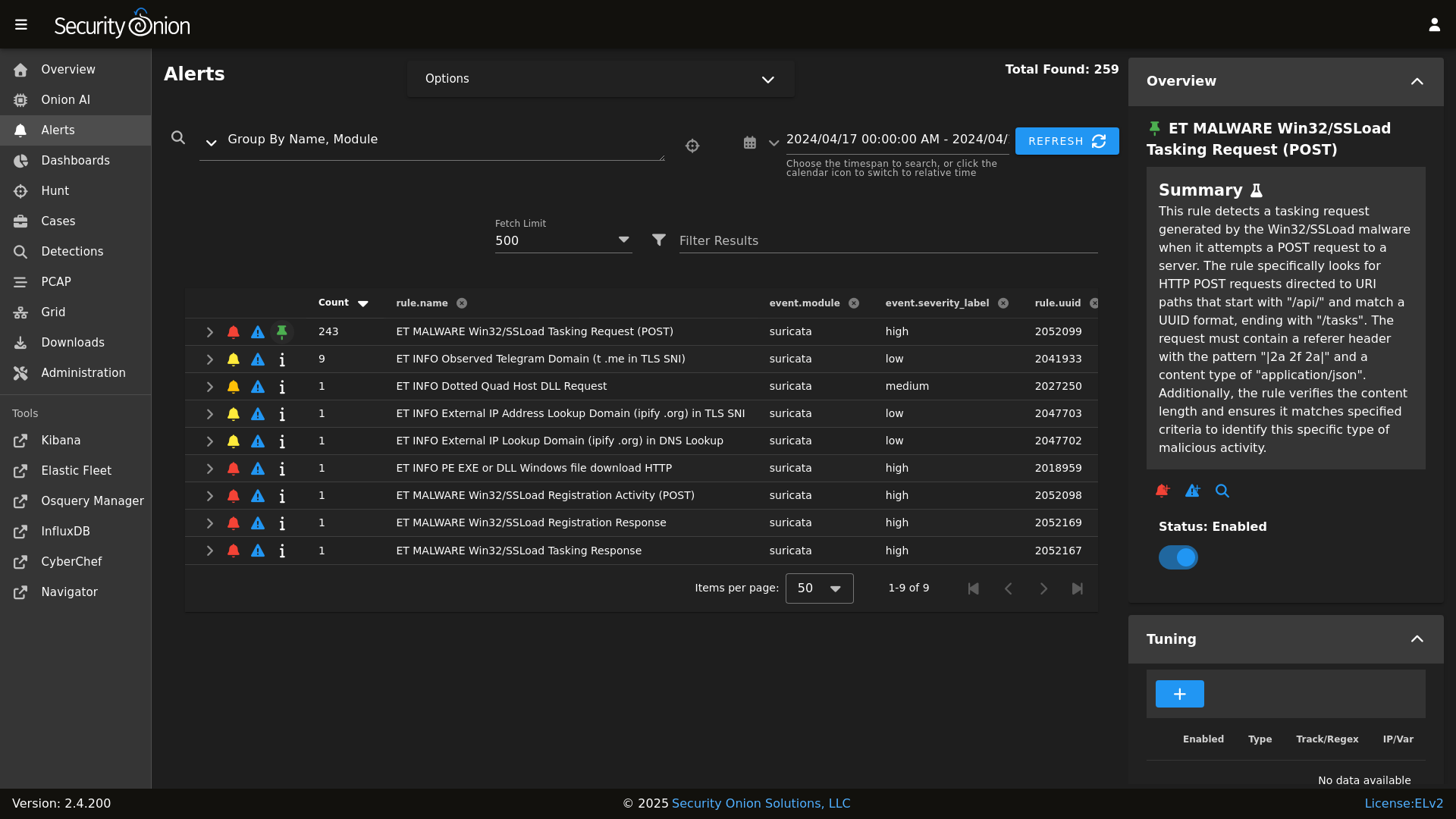
Alerts
|
||||||
|
|
||||||
|
|
||||||
Security Onion includes everything you need to monitor your network and host systems:
|
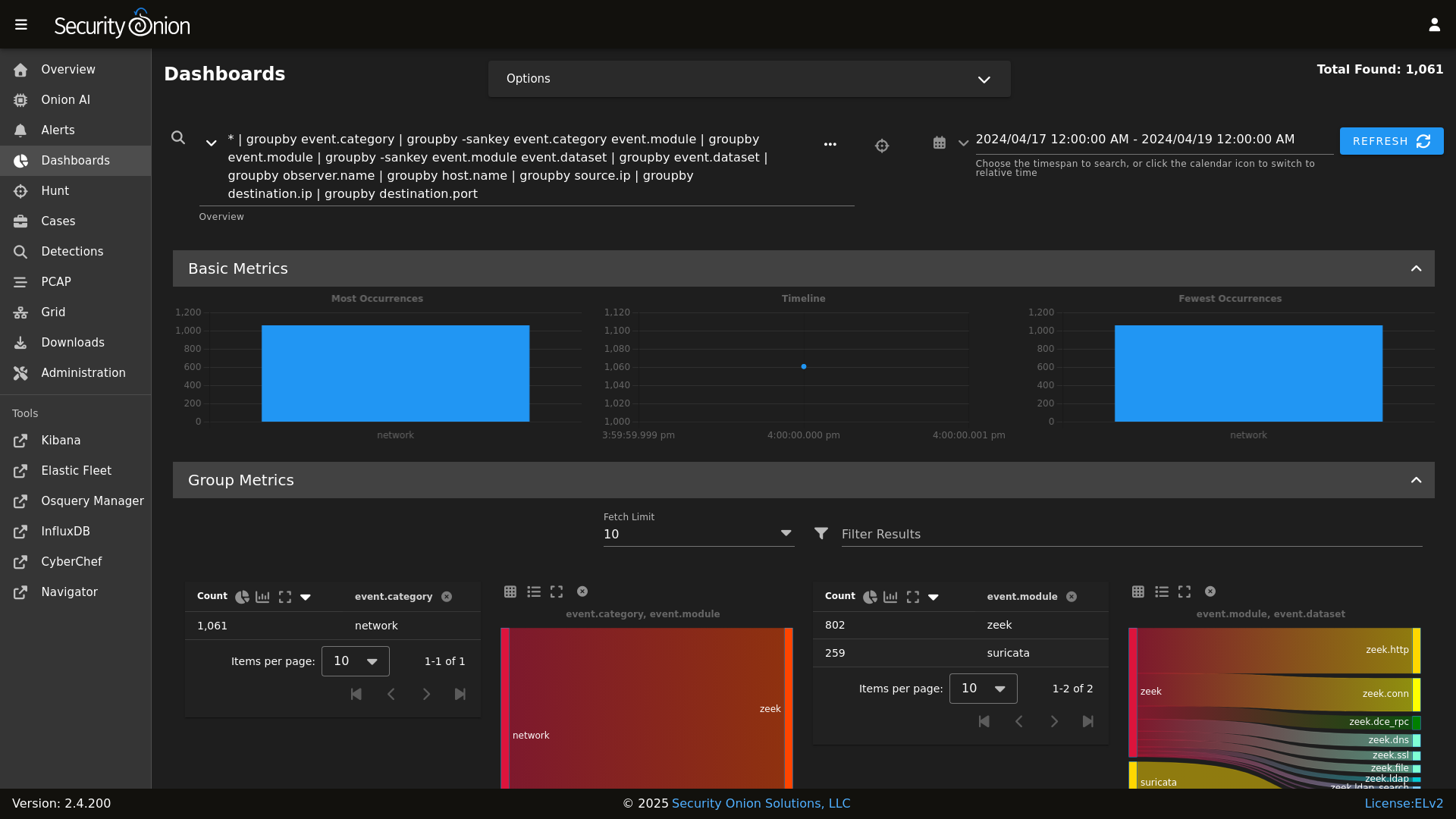
Dashboards
|
||||||
|
|
||||||
|
|
||||||
* **Security Onion Console (SOC)**: A unified web interface for analyzing security events and managing your grid.
|
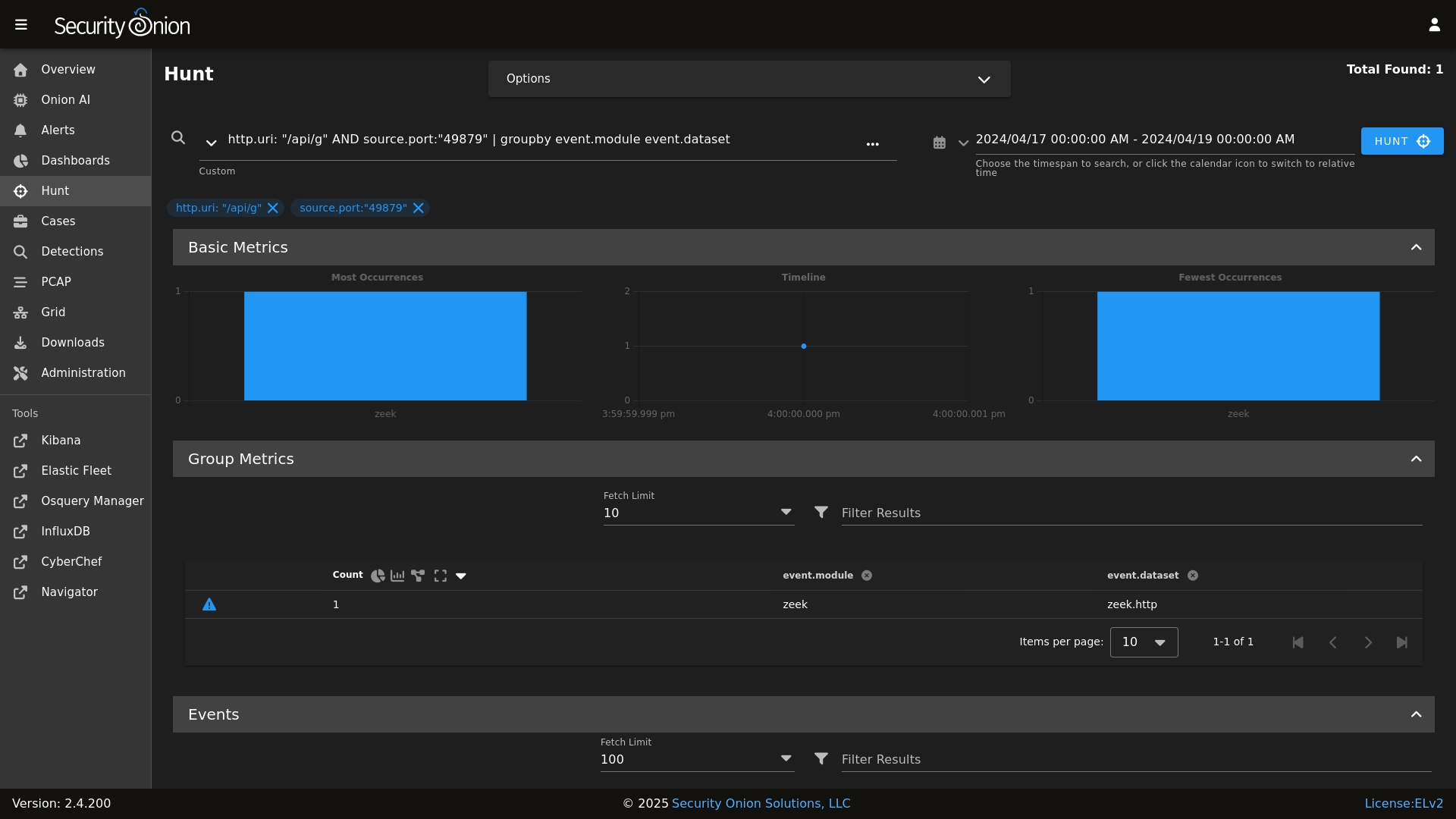
Hunt
|
||||||
* **Elastic Stack**: Powerful search backed by Elasticsearch.
|
|
||||||
* **Intrusion Detection**: Network-based IDS with Suricata and host-based monitoring with Elastic Fleet.
|
|
||||||
* **Network Metadata**: Detailed network metadata generated by Zeek or Suricata.
|
|
||||||
* **Full Packet Capture**: Retain and analyze raw network traffic with Suricata PCAP.
|
|
||||||
|
|
||||||
## ⭐ Security Onion Pro
|
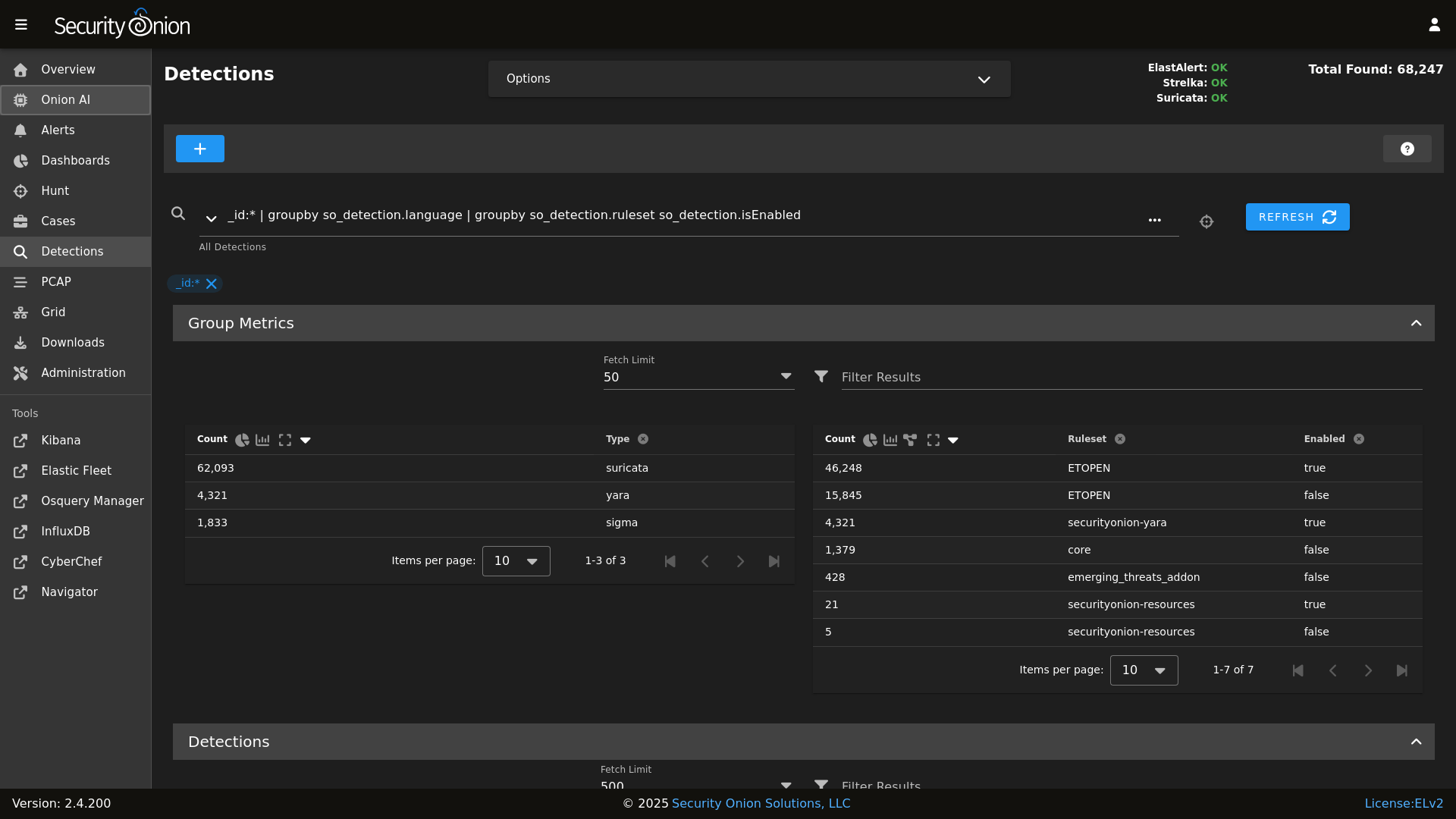
Detections
|
||||||
|
|
||||||
|
|
||||||
For organizations and enterprises requiring advanced capabilities, **Security Onion Pro** offers additional features designed for scale and efficiency:
|
PCAP
|
||||||
|
|
||||||
|
|
||||||
* **Onion AI**: Leverage powerful AI-driven insights to accelerate your analysis and investigations.
|
Grid
|
||||||
* **Enterprise Features**: Enhanced tools and integrations tailored for enterprise-grade security operations.
|
|
||||||
|
|
||||||
For more information, visit the [Security Onion Pro](https://securityonionsolutions.com/pro) page.
|
Config
|
||||||
|
|
||||||
|
|
||||||
## ☁️ Cloud Deployment
|
### Release Notes
|
||||||
|
|
||||||
Security Onion is available and ready to deploy in the **AWS**, **Azure**, and **Google Cloud (GCP)** marketplaces.
|
https://docs.securityonion.net/en/2.4/release-notes.html
|
||||||
|
|
||||||
## 🚀 Getting Started
|
### Requirements
|
||||||
|
|
||||||
| Goal | Resource |
|
https://docs.securityonion.net/en/2.4/hardware.html
|
||||||
| :--- | :--- |
|
|
||||||
| **Download** | [Security Onion ISO](https://securityonion.net/docs/download) |
|
|
||||||
| **Requirements** | [Hardware Guide](https://securityonion.net/docs/hardware) |
|
|
||||||
| **Install** | [Installation Instructions](https://securityonion.net/docs/installation) |
|
|
||||||
| **What's New** | [Release Notes](https://securityonion.net/docs/release-notes) |
|
|
||||||
|
|
||||||
## 📖 Documentation & Support
|
### Download
|
||||||
|
|
||||||
For more detailed information, please visit our [Documentation](https://docs.securityonion.net).
|
https://docs.securityonion.net/en/2.4/download.html
|
||||||
|
|
||||||
* **FAQ**: [Frequently Asked Questions](https://securityonion.net/docs/faq)
|
### Installation
|
||||||
* **Community**: [Discussions & Support](https://securityonion.net/docs/community-support)
|
|
||||||
* **Training**: [Official Training](https://securityonion.net/training)
|
|
||||||
|
|
||||||
## 🤝 Contributing
|
https://docs.securityonion.net/en/2.4/installation.html
|
||||||
|
|
||||||
We welcome contributions! Please see our [CONTRIBUTING.md](CONTRIBUTING.md) for guidelines on how to get involved.
|
### FAQ
|
||||||
|
|
||||||
## 🛡️ License
|
https://docs.securityonion.net/en/2.4/faq.html
|
||||||
|
|
||||||
Security Onion is licensed under the terms of the license found in the [LICENSE](LICENSE) file.
|
### Feedback
|
||||||
|
|
||||||
---
|
https://docs.securityonion.net/en/2.4/community-support.html
|
||||||
*Built with 🧅 by Security Onion Solutions.*
|
|
||||||
|
|||||||
@@ -4,7 +4,6 @@
|
|||||||
|
|
||||||
| Version | Supported |
|
| Version | Supported |
|
||||||
| ------- | ------------------ |
|
| ------- | ------------------ |
|
||||||
| 3.x | :white_check_mark: |
|
|
||||||
| 2.4.x | :white_check_mark: |
|
| 2.4.x | :white_check_mark: |
|
||||||
| 2.3.x | :x: |
|
| 2.3.x | :x: |
|
||||||
| 16.04.x | :x: |
|
| 16.04.x | :x: |
|
||||||
|
|||||||
@@ -1,2 +0,0 @@
|
|||||||
ca:
|
|
||||||
server:
|
|
||||||
@@ -1,6 +1,5 @@
|
|||||||
base:
|
base:
|
||||||
'*':
|
'*':
|
||||||
- ca
|
|
||||||
- global.soc_global
|
- global.soc_global
|
||||||
- global.adv_global
|
- global.adv_global
|
||||||
- docker.soc_docker
|
- docker.soc_docker
|
||||||
@@ -87,6 +86,8 @@ base:
|
|||||||
- zeek.adv_zeek
|
- zeek.adv_zeek
|
||||||
- bpf.soc_bpf
|
- bpf.soc_bpf
|
||||||
- bpf.adv_bpf
|
- bpf.adv_bpf
|
||||||
|
- pcap.soc_pcap
|
||||||
|
- pcap.adv_pcap
|
||||||
- suricata.soc_suricata
|
- suricata.soc_suricata
|
||||||
- suricata.adv_suricata
|
- suricata.adv_suricata
|
||||||
- minions.{{ grains.id }}
|
- minions.{{ grains.id }}
|
||||||
@@ -132,6 +133,8 @@ base:
|
|||||||
- zeek.adv_zeek
|
- zeek.adv_zeek
|
||||||
- bpf.soc_bpf
|
- bpf.soc_bpf
|
||||||
- bpf.adv_bpf
|
- bpf.adv_bpf
|
||||||
|
- pcap.soc_pcap
|
||||||
|
- pcap.adv_pcap
|
||||||
- suricata.soc_suricata
|
- suricata.soc_suricata
|
||||||
- suricata.adv_suricata
|
- suricata.adv_suricata
|
||||||
- minions.{{ grains.id }}
|
- minions.{{ grains.id }}
|
||||||
@@ -181,6 +184,8 @@ base:
|
|||||||
- zeek.adv_zeek
|
- zeek.adv_zeek
|
||||||
- bpf.soc_bpf
|
- bpf.soc_bpf
|
||||||
- bpf.adv_bpf
|
- bpf.adv_bpf
|
||||||
|
- pcap.soc_pcap
|
||||||
|
- pcap.adv_pcap
|
||||||
- suricata.soc_suricata
|
- suricata.soc_suricata
|
||||||
- suricata.adv_suricata
|
- suricata.adv_suricata
|
||||||
- minions.{{ grains.id }}
|
- minions.{{ grains.id }}
|
||||||
@@ -203,6 +208,8 @@ base:
|
|||||||
- zeek.adv_zeek
|
- zeek.adv_zeek
|
||||||
- bpf.soc_bpf
|
- bpf.soc_bpf
|
||||||
- bpf.adv_bpf
|
- bpf.adv_bpf
|
||||||
|
- pcap.soc_pcap
|
||||||
|
- pcap.adv_pcap
|
||||||
- suricata.soc_suricata
|
- suricata.soc_suricata
|
||||||
- suricata.adv_suricata
|
- suricata.adv_suricata
|
||||||
- strelka.soc_strelka
|
- strelka.soc_strelka
|
||||||
@@ -289,6 +296,8 @@ base:
|
|||||||
- zeek.adv_zeek
|
- zeek.adv_zeek
|
||||||
- bpf.soc_bpf
|
- bpf.soc_bpf
|
||||||
- bpf.adv_bpf
|
- bpf.adv_bpf
|
||||||
|
- pcap.soc_pcap
|
||||||
|
- pcap.adv_pcap
|
||||||
- suricata.soc_suricata
|
- suricata.soc_suricata
|
||||||
- suricata.adv_suricata
|
- suricata.adv_suricata
|
||||||
- strelka.soc_strelka
|
- strelka.soc_strelka
|
||||||
|
|||||||
@@ -1,14 +1,24 @@
|
|||||||
|
from os import path
|
||||||
import subprocess
|
import subprocess
|
||||||
|
|
||||||
def check():
|
def check():
|
||||||
|
|
||||||
|
osfam = __grains__['os_family']
|
||||||
retval = 'False'
|
retval = 'False'
|
||||||
|
|
||||||
cmd = 'needs-restarting -r > /dev/null 2>&1'
|
if osfam == 'Debian':
|
||||||
|
if path.exists('/var/run/reboot-required'):
|
||||||
|
retval = 'True'
|
||||||
|
|
||||||
try:
|
elif osfam == 'RedHat':
|
||||||
needs_restarting = subprocess.check_call(cmd, shell=True)
|
cmd = 'needs-restarting -r > /dev/null 2>&1'
|
||||||
except subprocess.CalledProcessError:
|
|
||||||
retval = 'True'
|
try:
|
||||||
|
needs_restarting = subprocess.check_call(cmd, shell=True)
|
||||||
|
except subprocess.CalledProcessError:
|
||||||
|
retval = 'True'
|
||||||
|
|
||||||
|
else:
|
||||||
|
retval = 'Unsupported OS: %s' % os
|
||||||
|
|
||||||
return retval
|
return retval
|
||||||
|
|||||||
@@ -15,7 +15,11 @@
|
|||||||
'salt.minion-check',
|
'salt.minion-check',
|
||||||
'sensoroni',
|
'sensoroni',
|
||||||
'salt.lasthighstate',
|
'salt.lasthighstate',
|
||||||
'salt.minion',
|
'salt.minion'
|
||||||
|
] %}
|
||||||
|
|
||||||
|
{% set ssl_states = [
|
||||||
|
'ssl',
|
||||||
'telegraf',
|
'telegraf',
|
||||||
'firewall',
|
'firewall',
|
||||||
'schedule',
|
'schedule',
|
||||||
@@ -24,7 +28,7 @@
|
|||||||
|
|
||||||
{% set manager_states = [
|
{% set manager_states = [
|
||||||
'salt.master',
|
'salt.master',
|
||||||
'ca.server',
|
'ca',
|
||||||
'registry',
|
'registry',
|
||||||
'manager',
|
'manager',
|
||||||
'nginx',
|
'nginx',
|
||||||
@@ -38,6 +42,7 @@
|
|||||||
] %}
|
] %}
|
||||||
|
|
||||||
{% set sensor_states = [
|
{% set sensor_states = [
|
||||||
|
'pcap',
|
||||||
'suricata',
|
'suricata',
|
||||||
'healthcheck',
|
'healthcheck',
|
||||||
'tcpreplay',
|
'tcpreplay',
|
||||||
@@ -70,24 +75,28 @@
|
|||||||
{# Map role-specific states #}
|
{# Map role-specific states #}
|
||||||
{% set role_states = {
|
{% set role_states = {
|
||||||
'so-eval': (
|
'so-eval': (
|
||||||
|
ssl_states +
|
||||||
manager_states +
|
manager_states +
|
||||||
sensor_states +
|
sensor_states +
|
||||||
elastic_stack_states | reject('equalto', 'logstash') | list +
|
elastic_stack_states | reject('equalto', 'logstash') | list
|
||||||
['logstash.ssl']
|
|
||||||
),
|
),
|
||||||
'so-heavynode': (
|
'so-heavynode': (
|
||||||
|
ssl_states +
|
||||||
sensor_states +
|
sensor_states +
|
||||||
['elasticagent', 'elasticsearch', 'logstash', 'redis', 'nginx']
|
['elasticagent', 'elasticsearch', 'logstash', 'redis', 'nginx']
|
||||||
),
|
),
|
||||||
'so-idh': (
|
'so-idh': (
|
||||||
|
ssl_states +
|
||||||
['idh']
|
['idh']
|
||||||
),
|
),
|
||||||
'so-import': (
|
'so-import': (
|
||||||
|
ssl_states +
|
||||||
manager_states +
|
manager_states +
|
||||||
sensor_states | reject('equalto', 'strelka') | reject('equalto', 'healthcheck') | list +
|
sensor_states | reject('equalto', 'strelka') | reject('equalto', 'healthcheck') | list +
|
||||||
['elasticsearch', 'elasticsearch.auth', 'kibana', 'kibana.secrets', 'logstash.ssl', 'strelka.manager']
|
['elasticsearch', 'elasticsearch.auth', 'kibana', 'kibana.secrets', 'strelka.manager']
|
||||||
),
|
),
|
||||||
'so-manager': (
|
'so-manager': (
|
||||||
|
ssl_states +
|
||||||
manager_states +
|
manager_states +
|
||||||
['salt.cloud', 'libvirt.packages', 'libvirt.ssh.users', 'strelka.manager'] +
|
['salt.cloud', 'libvirt.packages', 'libvirt.ssh.users', 'strelka.manager'] +
|
||||||
stig_states +
|
stig_states +
|
||||||
@@ -95,6 +104,7 @@
|
|||||||
elastic_stack_states
|
elastic_stack_states
|
||||||
),
|
),
|
||||||
'so-managerhype': (
|
'so-managerhype': (
|
||||||
|
ssl_states +
|
||||||
manager_states +
|
manager_states +
|
||||||
['salt.cloud', 'strelka.manager', 'hypervisor', 'libvirt'] +
|
['salt.cloud', 'strelka.manager', 'hypervisor', 'libvirt'] +
|
||||||
stig_states +
|
stig_states +
|
||||||
@@ -102,6 +112,7 @@
|
|||||||
elastic_stack_states
|
elastic_stack_states
|
||||||
),
|
),
|
||||||
'so-managersearch': (
|
'so-managersearch': (
|
||||||
|
ssl_states +
|
||||||
manager_states +
|
manager_states +
|
||||||
['salt.cloud', 'libvirt.packages', 'libvirt.ssh.users', 'strelka.manager'] +
|
['salt.cloud', 'libvirt.packages', 'libvirt.ssh.users', 'strelka.manager'] +
|
||||||
stig_states +
|
stig_states +
|
||||||
@@ -109,10 +120,12 @@
|
|||||||
elastic_stack_states
|
elastic_stack_states
|
||||||
),
|
),
|
||||||
'so-searchnode': (
|
'so-searchnode': (
|
||||||
|
ssl_states +
|
||||||
['kafka.ca', 'kafka.ssl', 'elasticsearch', 'logstash', 'nginx'] +
|
['kafka.ca', 'kafka.ssl', 'elasticsearch', 'logstash', 'nginx'] +
|
||||||
stig_states
|
stig_states
|
||||||
),
|
),
|
||||||
'so-standalone': (
|
'so-standalone': (
|
||||||
|
ssl_states +
|
||||||
manager_states +
|
manager_states +
|
||||||
['salt.cloud', 'libvirt.packages', 'libvirt.ssh.users'] +
|
['salt.cloud', 'libvirt.packages', 'libvirt.ssh.users'] +
|
||||||
sensor_states +
|
sensor_states +
|
||||||
@@ -121,24 +134,29 @@
|
|||||||
elastic_stack_states
|
elastic_stack_states
|
||||||
),
|
),
|
||||||
'so-sensor': (
|
'so-sensor': (
|
||||||
|
ssl_states +
|
||||||
sensor_states +
|
sensor_states +
|
||||||
['nginx'] +
|
['nginx'] +
|
||||||
stig_states
|
stig_states
|
||||||
),
|
),
|
||||||
'so-fleet': (
|
'so-fleet': (
|
||||||
|
ssl_states +
|
||||||
stig_states +
|
stig_states +
|
||||||
['logstash', 'nginx', 'healthcheck', 'elasticfleet']
|
['logstash', 'nginx', 'healthcheck', 'elasticfleet']
|
||||||
),
|
),
|
||||||
'so-receiver': (
|
'so-receiver': (
|
||||||
|
ssl_states +
|
||||||
kafka_states +
|
kafka_states +
|
||||||
stig_states +
|
stig_states +
|
||||||
['logstash', 'redis']
|
['logstash', 'redis']
|
||||||
),
|
),
|
||||||
'so-hypervisor': (
|
'so-hypervisor': (
|
||||||
|
ssl_states +
|
||||||
stig_states +
|
stig_states +
|
||||||
['hypervisor', 'libvirt']
|
['hypervisor', 'libvirt']
|
||||||
),
|
),
|
||||||
'so-desktop': (
|
'so-desktop': (
|
||||||
|
['ssl', 'docker_clean', 'telegraf'] +
|
||||||
stig_states
|
stig_states
|
||||||
)
|
)
|
||||||
} %}
|
} %}
|
||||||
|
|||||||
@@ -1,12 +1,10 @@
|
|||||||
{% macro remove_comments(bpfmerged, app) %}
|
{% macro remove_comments(bpfmerged, app) %}
|
||||||
|
|
||||||
{# remove comments from the bpf #}
|
{# remove comments from the bpf #}
|
||||||
{% set app_list = [] %}
|
|
||||||
{% for bpf in bpfmerged[app] %}
|
{% for bpf in bpfmerged[app] %}
|
||||||
{% if not bpf.strip().startswith('#') %}
|
{% if bpf.strip().startswith('#') %}
|
||||||
{% do app_list.append(bpf) %}
|
{% do bpfmerged[app].pop(loop.index0) %}
|
||||||
{% endif %}
|
{% endif %}
|
||||||
{% endfor %}
|
{% endfor %}
|
||||||
{% do bpfmerged.update({app: app_list}) %}
|
|
||||||
|
|
||||||
{% endmacro %}
|
{% endmacro %}
|
||||||
|
|||||||
@@ -1,15 +1,21 @@
|
|||||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||||
{% set PCAP_BPF_STATUS = 0 %}
|
{% set PCAP_BPF_STATUS = 0 %}
|
||||||
|
{% set STENO_BPF_COMPILED = "" %}
|
||||||
|
|
||||||
|
{% if GLOBALS.pcap_engine == "TRANSITION" %}
|
||||||
|
{% set PCAPBPF = ["ip and host 255.255.255.1 and port 1"] %}
|
||||||
|
{% else %}
|
||||||
{% import_yaml 'bpf/defaults.yaml' as BPFDEFAULTS %}
|
{% import_yaml 'bpf/defaults.yaml' as BPFDEFAULTS %}
|
||||||
{% set BPFMERGED = salt['pillar.get']('bpf', BPFDEFAULTS.bpf, merge=True) %}
|
{% set BPFMERGED = salt['pillar.get']('bpf', BPFDEFAULTS.bpf, merge=True) %}
|
||||||
{% import 'bpf/macros.jinja' as MACROS %}
|
{% import 'bpf/macros.jinja' as MACROS %}
|
||||||
{{ MACROS.remove_comments(BPFMERGED, 'pcap') }}
|
{{ MACROS.remove_comments(BPFMERGED, 'pcap') }}
|
||||||
{% set PCAPBPF = BPFMERGED.pcap %}
|
{% set PCAPBPF = BPFMERGED.pcap %}
|
||||||
|
{% endif %}
|
||||||
|
|
||||||
{% if PCAPBPF %}
|
{% if PCAPBPF %}
|
||||||
{% set PCAP_BPF_CALC = salt['cmd.script']('salt://common/tools/sbin/so-bpf-compile', GLOBALS.sensor.interface + ' ' + PCAPBPF|join(" "),cwd='/root') %}
|
{% set PCAP_BPF_CALC = salt['cmd.run_all']('/usr/sbin/so-bpf-compile ' ~ GLOBALS.sensor.interface ~ ' ' ~ PCAPBPF|join(" "), cwd='/root') %}
|
||||||
{% if PCAP_BPF_CALC['retcode'] == 0 %}
|
{% if PCAP_BPF_CALC['retcode'] == 0 %}
|
||||||
{% set PCAP_BPF_STATUS = 1 %}
|
{% set PCAP_BPF_STATUS = 1 %}
|
||||||
|
{% set STENO_BPF_COMPILED = ",\\\"--filter=" + PCAP_BPF_CALC['stdout'] + "\\\"" %}
|
||||||
{% endif %}
|
{% endif %}
|
||||||
{% endif %}
|
{% endif %}
|
||||||
|
|||||||
@@ -9,7 +9,7 @@
|
|||||||
{% set SURICATABPF = BPFMERGED.suricata %}
|
{% set SURICATABPF = BPFMERGED.suricata %}
|
||||||
|
|
||||||
{% if SURICATABPF %}
|
{% if SURICATABPF %}
|
||||||
{% set SURICATA_BPF_CALC = salt['cmd.script']('salt://common/tools/sbin/so-bpf-compile', GLOBALS.sensor.interface + ' ' + SURICATABPF|join(" "),cwd='/root') %}
|
{% set SURICATA_BPF_CALC = salt['cmd.run_all']('/usr/sbin/so-bpf-compile ' ~ GLOBALS.sensor.interface ~ ' ' ~ SURICATABPF|join(" "), cwd='/root') %}
|
||||||
{% if SURICATA_BPF_CALC['retcode'] == 0 %}
|
{% if SURICATA_BPF_CALC['retcode'] == 0 %}
|
||||||
{% set SURICATA_BPF_STATUS = 1 %}
|
{% set SURICATA_BPF_STATUS = 1 %}
|
||||||
{% endif %}
|
{% endif %}
|
||||||
|
|||||||
@@ -9,7 +9,7 @@
|
|||||||
{% set ZEEKBPF = BPFMERGED.zeek %}
|
{% set ZEEKBPF = BPFMERGED.zeek %}
|
||||||
|
|
||||||
{% if ZEEKBPF %}
|
{% if ZEEKBPF %}
|
||||||
{% set ZEEK_BPF_CALC = salt['cmd.script']('salt://common/tools/sbin/so-bpf-compile', GLOBALS.sensor.interface + ' ' + ZEEKBPF|join(" "),cwd='/root') %}
|
{% set ZEEK_BPF_CALC = salt['cmd.run_all']('/usr/sbin/so-bpf-compile ' ~ GLOBALS.sensor.interface ~ ' ' ~ ZEEKBPF|join(" "), cwd='/root') %}
|
||||||
{% if ZEEK_BPF_CALC['retcode'] == 0 %}
|
{% if ZEEK_BPF_CALC['retcode'] == 0 %}
|
||||||
{% set ZEEK_BPF_STATUS = 1 %}
|
{% set ZEEK_BPF_STATUS = 1 %}
|
||||||
{% endif %}
|
{% endif %}
|
||||||
|
|||||||
4
salt/ca/dirs.sls
Normal file
4
salt/ca/dirs.sls
Normal file
@@ -0,0 +1,4 @@
|
|||||||
|
pki_issued_certs:
|
||||||
|
file.directory:
|
||||||
|
- name: /etc/pki/issued_certs
|
||||||
|
- makedirs: True
|
||||||
@@ -3,10 +3,70 @@
|
|||||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||||
# Elastic License 2.0.
|
# Elastic License 2.0.
|
||||||
|
|
||||||
|
{% from 'allowed_states.map.jinja' import allowed_states %}
|
||||||
|
{% if sls in allowed_states %}
|
||||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||||
|
|
||||||
|
|
||||||
include:
|
include:
|
||||||
{% if GLOBALS.is_manager %}
|
- ca.dirs
|
||||||
- ca.server
|
|
||||||
|
/etc/salt/minion.d/signing_policies.conf:
|
||||||
|
file.managed:
|
||||||
|
- source: salt://ca/files/signing_policies.conf
|
||||||
|
|
||||||
|
pki_private_key:
|
||||||
|
x509.private_key_managed:
|
||||||
|
- name: /etc/pki/ca.key
|
||||||
|
- keysize: 4096
|
||||||
|
- passphrase:
|
||||||
|
- backup: True
|
||||||
|
{% if salt['file.file_exists']('/etc/pki/ca.key') -%}
|
||||||
|
- prereq:
|
||||||
|
- x509: /etc/pki/ca.crt
|
||||||
|
{%- endif %}
|
||||||
|
|
||||||
|
pki_public_ca_crt:
|
||||||
|
x509.certificate_managed:
|
||||||
|
- name: /etc/pki/ca.crt
|
||||||
|
- signing_private_key: /etc/pki/ca.key
|
||||||
|
- CN: {{ GLOBALS.manager }}
|
||||||
|
- C: US
|
||||||
|
- ST: Utah
|
||||||
|
- L: Salt Lake City
|
||||||
|
- basicConstraints: "critical CA:true"
|
||||||
|
- keyUsage: "critical cRLSign, keyCertSign"
|
||||||
|
- extendedkeyUsage: "serverAuth, clientAuth"
|
||||||
|
- subjectKeyIdentifier: hash
|
||||||
|
- authorityKeyIdentifier: keyid:always, issuer
|
||||||
|
- days_valid: 3650
|
||||||
|
- days_remaining: 0
|
||||||
|
- backup: True
|
||||||
|
- replace: False
|
||||||
|
- require:
|
||||||
|
- sls: ca.dirs
|
||||||
|
- timeout: 30
|
||||||
|
- retry:
|
||||||
|
attempts: 5
|
||||||
|
interval: 30
|
||||||
|
|
||||||
|
mine_update_ca_crt:
|
||||||
|
module.run:
|
||||||
|
- mine.update: []
|
||||||
|
- onchanges:
|
||||||
|
- x509: pki_public_ca_crt
|
||||||
|
|
||||||
|
cakeyperms:
|
||||||
|
file.managed:
|
||||||
|
- replace: False
|
||||||
|
- name: /etc/pki/ca.key
|
||||||
|
- mode: 640
|
||||||
|
- group: 939
|
||||||
|
|
||||||
|
{% else %}
|
||||||
|
|
||||||
|
{{sls}}_state_not_allowed:
|
||||||
|
test.fail_without_changes:
|
||||||
|
- name: {{sls}}_state_not_allowed
|
||||||
|
|
||||||
{% endif %}
|
{% endif %}
|
||||||
- ca.trustca
|
|
||||||
|
|||||||
@@ -1,3 +0,0 @@
|
|||||||
{% set CA = {
|
|
||||||
'server': pillar.ca.server
|
|
||||||
}%}
|
|
||||||
@@ -1,35 +1,7 @@
|
|||||||
# Copyright Security Onion Solutions LLC and/or licensed to Security Onion Solutions LLC under one
|
pki_private_key:
|
||||||
# or more contributor license agreements. Licensed under the Elastic License 2.0 as shown at
|
|
||||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
|
||||||
# Elastic License 2.0.
|
|
||||||
|
|
||||||
{% set setup_running = salt['cmd.retcode']('pgrep -x so-setup') == 0 %}
|
|
||||||
|
|
||||||
{% if setup_running%}
|
|
||||||
|
|
||||||
include:
|
|
||||||
- ssl.remove
|
|
||||||
|
|
||||||
remove_pki_private_key:
|
|
||||||
file.absent:
|
file.absent:
|
||||||
- name: /etc/pki/ca.key
|
- name: /etc/pki/ca.key
|
||||||
|
|
||||||
remove_pki_public_ca_crt:
|
pki_public_ca_crt:
|
||||||
file.absent:
|
file.absent:
|
||||||
- name: /etc/pki/ca.crt
|
- name: /etc/pki/ca.crt
|
||||||
|
|
||||||
remove_trusttheca:
|
|
||||||
file.absent:
|
|
||||||
- name: /etc/pki/tls/certs/intca.crt
|
|
||||||
|
|
||||||
remove_pki_public_ca_crt_symlink:
|
|
||||||
file.absent:
|
|
||||||
- name: /opt/so/saltstack/local/salt/ca/files/ca.crt
|
|
||||||
|
|
||||||
{% else %}
|
|
||||||
|
|
||||||
so-setup_not_running:
|
|
||||||
test.show_notification:
|
|
||||||
- text: "This state is reserved for usage during so-setup."
|
|
||||||
|
|
||||||
{% endif %}
|
|
||||||
|
|||||||
@@ -1,63 +0,0 @@
|
|||||||
# Copyright Security Onion Solutions LLC and/or licensed to Security Onion Solutions LLC under one
|
|
||||||
# or more contributor license agreements. Licensed under the Elastic License 2.0 as shown at
|
|
||||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
|
||||||
# Elastic License 2.0.
|
|
||||||
|
|
||||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
|
||||||
{% if sls in allowed_states %}
|
|
||||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
|
||||||
|
|
||||||
pki_private_key:
|
|
||||||
x509.private_key_managed:
|
|
||||||
- name: /etc/pki/ca.key
|
|
||||||
- keysize: 4096
|
|
||||||
- passphrase:
|
|
||||||
- backup: True
|
|
||||||
{% if salt['file.file_exists']('/etc/pki/ca.key') -%}
|
|
||||||
- prereq:
|
|
||||||
- x509: /etc/pki/ca.crt
|
|
||||||
{%- endif %}
|
|
||||||
|
|
||||||
pki_public_ca_crt:
|
|
||||||
x509.certificate_managed:
|
|
||||||
- name: /etc/pki/ca.crt
|
|
||||||
- signing_private_key: /etc/pki/ca.key
|
|
||||||
- CN: {{ GLOBALS.manager }}
|
|
||||||
- C: US
|
|
||||||
- ST: Utah
|
|
||||||
- L: Salt Lake City
|
|
||||||
- basicConstraints: "critical CA:true"
|
|
||||||
- keyUsage: "critical cRLSign, keyCertSign"
|
|
||||||
- extendedkeyUsage: "serverAuth, clientAuth"
|
|
||||||
- subjectKeyIdentifier: hash
|
|
||||||
- authorityKeyIdentifier: keyid:always, issuer
|
|
||||||
- days_valid: 3650
|
|
||||||
- days_remaining: 7
|
|
||||||
- backup: True
|
|
||||||
- replace: False
|
|
||||||
- timeout: 30
|
|
||||||
- retry:
|
|
||||||
attempts: 5
|
|
||||||
interval: 30
|
|
||||||
|
|
||||||
pki_public_ca_crt_symlink:
|
|
||||||
file.symlink:
|
|
||||||
- name: /opt/so/saltstack/local/salt/ca/files/ca.crt
|
|
||||||
- target: /etc/pki/ca.crt
|
|
||||||
- require:
|
|
||||||
- x509: pki_public_ca_crt
|
|
||||||
|
|
||||||
cakeyperms:
|
|
||||||
file.managed:
|
|
||||||
- replace: False
|
|
||||||
- name: /etc/pki/ca.key
|
|
||||||
- mode: 640
|
|
||||||
- group: 939
|
|
||||||
|
|
||||||
{% else %}
|
|
||||||
|
|
||||||
{{sls}}_state_not_allowed:
|
|
||||||
test.fail_without_changes:
|
|
||||||
- name: {{sls}}_state_not_allowed
|
|
||||||
|
|
||||||
{% endif %}
|
|
||||||
12
salt/common/files/daemon.json
Normal file
12
salt/common/files/daemon.json
Normal file
@@ -0,0 +1,12 @@
|
|||||||
|
{
|
||||||
|
"registry-mirrors": [
|
||||||
|
"https://:5000"
|
||||||
|
],
|
||||||
|
"bip": "172.17.0.1/24",
|
||||||
|
"default-address-pools": [
|
||||||
|
{
|
||||||
|
"base": "172.17.0.0/24",
|
||||||
|
"size": 24
|
||||||
|
}
|
||||||
|
]
|
||||||
|
}
|
||||||
@@ -20,6 +20,11 @@ kernel.printk:
|
|||||||
sysctl.present:
|
sysctl.present:
|
||||||
- value: "3 4 1 3"
|
- value: "3 4 1 3"
|
||||||
|
|
||||||
|
# Remove variables.txt from /tmp - This is temp
|
||||||
|
rmvariablesfile:
|
||||||
|
file.absent:
|
||||||
|
- name: /tmp/variables.txt
|
||||||
|
|
||||||
# Add socore Group
|
# Add socore Group
|
||||||
socoregroup:
|
socoregroup:
|
||||||
group.present:
|
group.present:
|
||||||
@@ -144,13 +149,35 @@ common_sbin_jinja:
|
|||||||
- so-import-pcap
|
- so-import-pcap
|
||||||
{% endif %}
|
{% endif %}
|
||||||
|
|
||||||
|
{% if GLOBALS.role == 'so-heavynode' %}
|
||||||
|
remove_so-pcap-import_heavynode:
|
||||||
|
file.absent:
|
||||||
|
- name: /usr/sbin/so-pcap-import
|
||||||
|
|
||||||
|
remove_so-import-pcap_heavynode:
|
||||||
|
file.absent:
|
||||||
|
- name: /usr/sbin/so-import-pcap
|
||||||
|
{% endif %}
|
||||||
|
|
||||||
|
{% if not GLOBALS.is_manager%}
|
||||||
|
# prior to 2.4.50 these scripts were in common/tools/sbin on the manager because of soup and distributed to non managers
|
||||||
|
# these two states remove the scripts from non manager nodes
|
||||||
|
remove_soup:
|
||||||
|
file.absent:
|
||||||
|
- name: /usr/sbin/soup
|
||||||
|
|
||||||
|
remove_so-firewall:
|
||||||
|
file.absent:
|
||||||
|
- name: /usr/sbin/so-firewall
|
||||||
|
{% endif %}
|
||||||
|
|
||||||
so-status_script:
|
so-status_script:
|
||||||
file.managed:
|
file.managed:
|
||||||
- name: /usr/sbin/so-status
|
- name: /usr/sbin/so-status
|
||||||
- source: salt://common/tools/sbin/so-status
|
- source: salt://common/tools/sbin/so-status
|
||||||
- mode: 755
|
- mode: 755
|
||||||
|
|
||||||
{% if GLOBALS.is_sensor %}
|
{% if GLOBALS.role in GLOBALS.sensor_roles %}
|
||||||
# Add sensor cleanup
|
# Add sensor cleanup
|
||||||
so-sensor-clean:
|
so-sensor-clean:
|
||||||
cron.present:
|
cron.present:
|
||||||
|
|||||||
@@ -1,5 +1,52 @@
|
|||||||
# we cannot import GLOBALS from vars/globals.map.jinja in this state since it is called in setup.virt.init
|
# we cannot import GLOBALS from vars/globals.map.jinja in this state since it is called in setup.virt.init
|
||||||
# since it is early in setup of a new VM, the pillars imported in GLOBALS are not yet defined
|
# since it is early in setup of a new VM, the pillars imported in GLOBALS are not yet defined
|
||||||
|
{% if grains.os_family == 'Debian' %}
|
||||||
|
commonpkgs:
|
||||||
|
pkg.installed:
|
||||||
|
- skip_suggestions: True
|
||||||
|
- pkgs:
|
||||||
|
- apache2-utils
|
||||||
|
- wget
|
||||||
|
- ntpdate
|
||||||
|
- jq
|
||||||
|
- curl
|
||||||
|
- ca-certificates
|
||||||
|
- software-properties-common
|
||||||
|
- apt-transport-https
|
||||||
|
- openssl
|
||||||
|
- netcat-openbsd
|
||||||
|
- sqlite3
|
||||||
|
- libssl-dev
|
||||||
|
- procps
|
||||||
|
- python3-dateutil
|
||||||
|
- python3-docker
|
||||||
|
- python3-packaging
|
||||||
|
- python3-lxml
|
||||||
|
- git
|
||||||
|
- rsync
|
||||||
|
- vim
|
||||||
|
- tar
|
||||||
|
- unzip
|
||||||
|
- bc
|
||||||
|
{% if grains.oscodename != 'focal' %}
|
||||||
|
- python3-rich
|
||||||
|
{% endif %}
|
||||||
|
|
||||||
|
{% if grains.oscodename == 'focal' %}
|
||||||
|
# since Ubuntu requires and internet connection we can use pip to install modules
|
||||||
|
python3-pip:
|
||||||
|
pkg.installed
|
||||||
|
|
||||||
|
python-rich:
|
||||||
|
pip.installed:
|
||||||
|
- name: rich
|
||||||
|
- target: /usr/local/lib/python3.8/dist-packages/
|
||||||
|
- require:
|
||||||
|
- pkg: python3-pip
|
||||||
|
{% endif %}
|
||||||
|
{% endif %}
|
||||||
|
|
||||||
|
{% if grains.os_family == 'RedHat' %}
|
||||||
|
|
||||||
remove_mariadb:
|
remove_mariadb:
|
||||||
pkg.removed:
|
pkg.removed:
|
||||||
@@ -37,3 +84,5 @@ commonpkgs:
|
|||||||
- unzip
|
- unzip
|
||||||
- wget
|
- wget
|
||||||
- yum-utils
|
- yum-utils
|
||||||
|
|
||||||
|
{% endif %}
|
||||||
|
|||||||
@@ -3,6 +3,8 @@
|
|||||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||||
# Elastic License 2.0.
|
# Elastic License 2.0.
|
||||||
|
|
||||||
|
{% if '2.4' in salt['cp.get_file_str']('/etc/soversion') %}
|
||||||
|
|
||||||
{% import_yaml '/opt/so/saltstack/local/pillar/global/soc_global.sls' as SOC_GLOBAL %}
|
{% import_yaml '/opt/so/saltstack/local/pillar/global/soc_global.sls' as SOC_GLOBAL %}
|
||||||
{% if SOC_GLOBAL.global.airgap %}
|
{% if SOC_GLOBAL.global.airgap %}
|
||||||
{% set UPDATE_DIR='/tmp/soagupdate/SecurityOnion' %}
|
{% set UPDATE_DIR='/tmp/soagupdate/SecurityOnion' %}
|
||||||
@@ -11,6 +13,14 @@
|
|||||||
{% endif %}
|
{% endif %}
|
||||||
{% set SOVERSION = salt['file.read']('/etc/soversion').strip() %}
|
{% set SOVERSION = salt['file.read']('/etc/soversion').strip() %}
|
||||||
|
|
||||||
|
remove_common_soup:
|
||||||
|
file.absent:
|
||||||
|
- name: /opt/so/saltstack/default/salt/common/tools/sbin/soup
|
||||||
|
|
||||||
|
remove_common_so-firewall:
|
||||||
|
file.absent:
|
||||||
|
- name: /opt/so/saltstack/default/salt/common/tools/sbin/so-firewall
|
||||||
|
|
||||||
# This section is used to put the scripts in place in the Salt file system
|
# This section is used to put the scripts in place in the Salt file system
|
||||||
# in case a state run tries to overwrite what we do in the next section.
|
# in case a state run tries to overwrite what we do in the next section.
|
||||||
copy_so-common_common_tools_sbin:
|
copy_so-common_common_tools_sbin:
|
||||||
@@ -110,3 +120,23 @@ copy_bootstrap-salt_sbin:
|
|||||||
- source: {{UPDATE_DIR}}/salt/salt/scripts/bootstrap-salt.sh
|
- source: {{UPDATE_DIR}}/salt/salt/scripts/bootstrap-salt.sh
|
||||||
- force: True
|
- force: True
|
||||||
- preserve: True
|
- preserve: True
|
||||||
|
|
||||||
|
{# this is added in 2.4.120 to remove salt repo files pointing to saltproject.io to accomodate the move to broadcom and new bootstrap-salt script #}
|
||||||
|
{% if salt['pkg.version_cmp'](SOVERSION, '2.4.120') == -1 %}
|
||||||
|
{% set saltrepofile = '/etc/yum.repos.d/salt.repo' %}
|
||||||
|
{% if grains.os_family == 'Debian' %}
|
||||||
|
{% set saltrepofile = '/etc/apt/sources.list.d/salt.list' %}
|
||||||
|
{% endif %}
|
||||||
|
remove_saltproject_io_repo_manager:
|
||||||
|
file.absent:
|
||||||
|
- name: {{ saltrepofile }}
|
||||||
|
{% endif %}
|
||||||
|
|
||||||
|
{% else %}
|
||||||
|
fix_23_soup_sbin:
|
||||||
|
cmd.run:
|
||||||
|
- name: curl -s -f -o /usr/sbin/soup https://raw.githubusercontent.com/Security-Onion-Solutions/securityonion/2.3/main/salt/common/tools/sbin/soup
|
||||||
|
fix_23_soup_salt:
|
||||||
|
cmd.run:
|
||||||
|
- name: curl -s -f -o /opt/so/saltstack/defalt/salt/common/tools/sbin/soup https://raw.githubusercontent.com/Security-Onion-Solutions/securityonion/2.3/main/salt/common/tools/sbin/soup
|
||||||
|
{% endif %}
|
||||||
|
|||||||
@@ -16,7 +16,7 @@
|
|||||||
|
|
||||||
if [ "$#" -lt 2 ]; then
|
if [ "$#" -lt 2 ]; then
|
||||||
cat 1>&2 <<EOF
|
cat 1>&2 <<EOF
|
||||||
$0 compiles a BPF expression to be passed to PCAP to apply a socket filter.
|
$0 compiles a BPF expression to be passed to stenotype to apply a socket filter.
|
||||||
Its first argument is the interface (link type is required) and all other arguments
|
Its first argument is the interface (link type is required) and all other arguments
|
||||||
are passed to TCPDump.
|
are passed to TCPDump.
|
||||||
|
|
||||||
|
|||||||
@@ -10,7 +10,7 @@
|
|||||||
cat << EOF
|
cat << EOF
|
||||||
|
|
||||||
so-checkin will run a full salt highstate to apply all salt states. If a highstate is already running, this request will be queued and so it may pause for a few minutes before you see any more output. For more information about so-checkin and salt, please see:
|
so-checkin will run a full salt highstate to apply all salt states. If a highstate is already running, this request will be queued and so it may pause for a few minutes before you see any more output. For more information about so-checkin and salt, please see:
|
||||||
https://securityonion.net/docs/salt
|
https://docs.securityonion.net/en/2.4/salt.html
|
||||||
|
|
||||||
EOF
|
EOF
|
||||||
|
|
||||||
|
|||||||
@@ -10,7 +10,7 @@
|
|||||||
# and since this same logic is required during installation, it's included in this file.
|
# and since this same logic is required during installation, it's included in this file.
|
||||||
|
|
||||||
DEFAULT_SALT_DIR=/opt/so/saltstack/default
|
DEFAULT_SALT_DIR=/opt/so/saltstack/default
|
||||||
DOC_BASE_URL="https://securityonion.net/docs"
|
DOC_BASE_URL="https://docs.securityonion.net/en/2.4"
|
||||||
|
|
||||||
if [ -z $NOROOT ]; then
|
if [ -z $NOROOT ]; then
|
||||||
# Check for prerequisites
|
# Check for prerequisites
|
||||||
@@ -333,8 +333,8 @@ get_elastic_agent_vars() {
|
|||||||
|
|
||||||
if [ -f "$defaultsfile" ]; then
|
if [ -f "$defaultsfile" ]; then
|
||||||
ELASTIC_AGENT_TARBALL_VERSION=$(egrep " +version: " $defaultsfile | awk -F: '{print $2}' | tr -d '[:space:]')
|
ELASTIC_AGENT_TARBALL_VERSION=$(egrep " +version: " $defaultsfile | awk -F: '{print $2}' | tr -d '[:space:]')
|
||||||
ELASTIC_AGENT_URL="https://repo.securityonion.net/file/so-repo/prod/3/elasticagent/elastic-agent_SO-$ELASTIC_AGENT_TARBALL_VERSION.tar.gz"
|
ELASTIC_AGENT_URL="https://repo.securityonion.net/file/so-repo/prod/2.4/elasticagent/elastic-agent_SO-$ELASTIC_AGENT_TARBALL_VERSION.tar.gz"
|
||||||
ELASTIC_AGENT_MD5_URL="https://repo.securityonion.net/file/so-repo/prod/3/elasticagent/elastic-agent_SO-$ELASTIC_AGENT_TARBALL_VERSION.md5"
|
ELASTIC_AGENT_MD5_URL="https://repo.securityonion.net/file/so-repo/prod/2.4/elasticagent/elastic-agent_SO-$ELASTIC_AGENT_TARBALL_VERSION.md5"
|
||||||
ELASTIC_AGENT_FILE="/nsm/elastic-fleet/artifacts/elastic-agent_SO-$ELASTIC_AGENT_TARBALL_VERSION.tar.gz"
|
ELASTIC_AGENT_FILE="/nsm/elastic-fleet/artifacts/elastic-agent_SO-$ELASTIC_AGENT_TARBALL_VERSION.tar.gz"
|
||||||
ELASTIC_AGENT_MD5="/nsm/elastic-fleet/artifacts/elastic-agent_SO-$ELASTIC_AGENT_TARBALL_VERSION.md5"
|
ELASTIC_AGENT_MD5="/nsm/elastic-fleet/artifacts/elastic-agent_SO-$ELASTIC_AGENT_TARBALL_VERSION.md5"
|
||||||
ELASTIC_AGENT_EXPANSION_DIR=/nsm/elastic-fleet/artifacts/beats/elastic-agent
|
ELASTIC_AGENT_EXPANSION_DIR=/nsm/elastic-fleet/artifacts/beats/elastic-agent
|
||||||
@@ -349,16 +349,21 @@ get_random_value() {
|
|||||||
}
|
}
|
||||||
|
|
||||||
gpg_rpm_import() {
|
gpg_rpm_import() {
|
||||||
if [[ "$WHATWOULDYOUSAYYAHDOHERE" == "setup" ]]; then
|
if [[ $is_oracle ]]; then
|
||||||
local RPMKEYSLOC="../salt/repo/client/files/$OS/keys"
|
if [[ "$WHATWOULDYOUSAYYAHDOHERE" == "setup" ]]; then
|
||||||
else
|
local RPMKEYSLOC="../salt/repo/client/files/$OS/keys"
|
||||||
local RPMKEYSLOC="$UPDATE_DIR/salt/repo/client/files/$OS/keys"
|
else
|
||||||
|
local RPMKEYSLOC="$UPDATE_DIR/salt/repo/client/files/$OS/keys"
|
||||||
|
fi
|
||||||
|
RPMKEYS=('RPM-GPG-KEY-oracle' 'RPM-GPG-KEY-EPEL-9' 'SALT-PROJECT-GPG-PUBKEY-2023.pub' 'docker.pub' 'securityonion.pub')
|
||||||
|
for RPMKEY in "${RPMKEYS[@]}"; do
|
||||||
|
rpm --import $RPMKEYSLOC/$RPMKEY
|
||||||
|
echo "Imported $RPMKEY"
|
||||||
|
done
|
||||||
|
elif [[ $is_rpm ]]; then
|
||||||
|
echo "Importing the security onion GPG key"
|
||||||
|
rpm --import ../salt/repo/client/files/oracle/keys/securityonion.pub
|
||||||
fi
|
fi
|
||||||
RPMKEYS=('RPM-GPG-KEY-oracle' 'RPM-GPG-KEY-EPEL-9' 'SALT-PROJECT-GPG-PUBKEY-2023.pub' 'docker.pub' 'securityonion.pub')
|
|
||||||
for RPMKEY in "${RPMKEYS[@]}"; do
|
|
||||||
rpm --import $RPMKEYSLOC/$RPMKEY
|
|
||||||
echo "Imported $RPMKEY"
|
|
||||||
done
|
|
||||||
}
|
}
|
||||||
|
|
||||||
header() {
|
header() {
|
||||||
@@ -399,25 +404,6 @@ is_single_node_grid() {
|
|||||||
grep "role: so-" /etc/salt/grains | grep -E "eval|standalone|import" &> /dev/null
|
grep "role: so-" /etc/salt/grains | grep -E "eval|standalone|import" &> /dev/null
|
||||||
}
|
}
|
||||||
|
|
||||||
initialize_elasticsearch_indices() {
|
|
||||||
local index_names=$1
|
|
||||||
local default_entry=${2:-'{"@timestamp":"0"}'}
|
|
||||||
|
|
||||||
for idx in $index_names; do
|
|
||||||
if ! so-elasticsearch-query "$idx" --fail --retry 3 --retry-delay 30 >/dev/null 2>&1; then
|
|
||||||
echo "Index does not already exist. Initializing $idx index."
|
|
||||||
|
|
||||||
if retry 3 10 "so-elasticsearch-query "$idx/_doc" -d '$default_entry' -XPOST --fail 2>/dev/null" '"successful":1'; then
|
|
||||||
echo "Successfully initialized $idx index."
|
|
||||||
else
|
|
||||||
echo "Failed to initialize $idx index after 3 attempts."
|
|
||||||
fi
|
|
||||||
else
|
|
||||||
echo "Index $idx already exists. No action needed."
|
|
||||||
fi
|
|
||||||
done
|
|
||||||
}
|
|
||||||
|
|
||||||
lookup_bond_interfaces() {
|
lookup_bond_interfaces() {
|
||||||
cat /proc/net/bonding/bond0 | grep "Slave Interface:" | sed -e "s/Slave Interface: //g"
|
cat /proc/net/bonding/bond0 | grep "Slave Interface:" | sed -e "s/Slave Interface: //g"
|
||||||
}
|
}
|
||||||
@@ -568,39 +554,21 @@ run_check_net_err() {
|
|||||||
}
|
}
|
||||||
|
|
||||||
wait_for_salt_minion() {
|
wait_for_salt_minion() {
|
||||||
local minion="$1"
|
local minion="$1"
|
||||||
local max_wait="${2:-30}"
|
local timeout="${2:-5}"
|
||||||
local interval="${3:-2}"
|
local logfile="${3:-'/dev/stdout'}"
|
||||||
local logfile="${4:-'/dev/stdout'}"
|
retry 60 5 "journalctl -u salt-minion.service | grep 'Minion is ready to receive requests'" >> "$logfile" 2>&1 || fail
|
||||||
local elapsed=0
|
local attempt=0
|
||||||
|
# each attempts would take about 15 seconds
|
||||||
echo "$(date '+%a %d %b %Y %H:%M:%S.%6N') - Waiting for salt-minion '$minion' to be ready..."
|
local maxAttempts=20
|
||||||
|
until check_salt_minion_status "$minion" "$timeout" "$logfile"; do
|
||||||
while [ $elapsed -lt $max_wait ]; do
|
attempt=$((attempt+1))
|
||||||
# Check if service is running
|
if [[ $attempt -eq $maxAttempts ]]; then
|
||||||
echo "$(date '+%a %d %b %Y %H:%M:%S.%6N') - Check if salt-minion service is running"
|
return 1
|
||||||
if ! systemctl is-active --quiet salt-minion; then
|
fi
|
||||||
echo "$(date '+%a %d %b %Y %H:%M:%S.%6N') - salt-minion service not running (elapsed: ${elapsed}s)"
|
sleep 10
|
||||||
sleep $interval
|
done
|
||||||
elapsed=$((elapsed + interval))
|
return 0
|
||||||
continue
|
|
||||||
fi
|
|
||||||
echo "$(date '+%a %d %b %Y %H:%M:%S.%6N') - salt-minion service is running"
|
|
||||||
|
|
||||||
# Check if minion responds to ping
|
|
||||||
echo "$(date '+%a %d %b %Y %H:%M:%S.%6N') - Check if $minion responds to ping"
|
|
||||||
if salt "$minion" test.ping --timeout=3 --out=json 2>> "$logfile" | grep -q "true"; then
|
|
||||||
echo "$(date '+%a %d %b %Y %H:%M:%S.%6N') - salt-minion '$minion' is connected and ready!"
|
|
||||||
return 0
|
|
||||||
fi
|
|
||||||
|
|
||||||
echo "$(date '+%a %d %b %Y %H:%M:%S.%6N') - Waiting... (${elapsed}s / ${max_wait}s)"
|
|
||||||
sleep $interval
|
|
||||||
elapsed=$((elapsed + interval))
|
|
||||||
done
|
|
||||||
|
|
||||||
echo "$(date '+%a %d %b %Y %H:%M:%S.%6N') - ERROR: salt-minion '$minion' not ready after $max_wait seconds"
|
|
||||||
return 1
|
|
||||||
}
|
}
|
||||||
|
|
||||||
salt_minion_count() {
|
salt_minion_count() {
|
||||||
@@ -610,19 +578,69 @@ salt_minion_count() {
|
|||||||
}
|
}
|
||||||
|
|
||||||
set_os() {
|
set_os() {
|
||||||
if [ -f /etc/redhat-release ] && grep -q "Red Hat Enterprise Linux release 9" /etc/redhat-release && [ -f /etc/oracle-release ]; then
|
if [ -f /etc/redhat-release ]; then
|
||||||
OS=oracle
|
if grep -q "Rocky Linux release 9" /etc/redhat-release; then
|
||||||
OSVER=9
|
OS=rocky
|
||||||
is_oracle=true
|
OSVER=9
|
||||||
is_rpm=true
|
is_rocky=true
|
||||||
|
is_rpm=true
|
||||||
|
elif grep -q "CentOS Stream release 9" /etc/redhat-release; then
|
||||||
|
OS=centos
|
||||||
|
OSVER=9
|
||||||
|
is_centos=true
|
||||||
|
is_rpm=true
|
||||||
|
elif grep -q "AlmaLinux release 9" /etc/redhat-release; then
|
||||||
|
OS=alma
|
||||||
|
OSVER=9
|
||||||
|
is_alma=true
|
||||||
|
is_rpm=true
|
||||||
|
elif grep -q "Red Hat Enterprise Linux release 9" /etc/redhat-release; then
|
||||||
|
if [ -f /etc/oracle-release ]; then
|
||||||
|
OS=oracle
|
||||||
|
OSVER=9
|
||||||
|
is_oracle=true
|
||||||
|
is_rpm=true
|
||||||
|
else
|
||||||
|
OS=rhel
|
||||||
|
OSVER=9
|
||||||
|
is_rhel=true
|
||||||
|
is_rpm=true
|
||||||
|
fi
|
||||||
|
fi
|
||||||
|
cron_service_name="crond"
|
||||||
|
elif [ -f /etc/os-release ]; then
|
||||||
|
if grep -q "UBUNTU_CODENAME=focal" /etc/os-release; then
|
||||||
|
OSVER=focal
|
||||||
|
UBVER=20.04
|
||||||
|
OS=ubuntu
|
||||||
|
is_ubuntu=true
|
||||||
|
is_deb=true
|
||||||
|
elif grep -q "UBUNTU_CODENAME=jammy" /etc/os-release; then
|
||||||
|
OSVER=jammy
|
||||||
|
UBVER=22.04
|
||||||
|
OS=ubuntu
|
||||||
|
is_ubuntu=true
|
||||||
|
is_deb=true
|
||||||
|
elif grep -q "VERSION_CODENAME=bookworm" /etc/os-release; then
|
||||||
|
OSVER=bookworm
|
||||||
|
DEBVER=12
|
||||||
|
is_debian=true
|
||||||
|
OS=debian
|
||||||
|
is_deb=true
|
||||||
|
fi
|
||||||
|
cron_service_name="cron"
|
||||||
fi
|
fi
|
||||||
cron_service_name="crond"
|
|
||||||
}
|
}
|
||||||
|
|
||||||
set_minionid() {
|
set_minionid() {
|
||||||
MINIONID=$(lookup_grain id)
|
MINIONID=$(lookup_grain id)
|
||||||
}
|
}
|
||||||
|
|
||||||
|
set_palette() {
|
||||||
|
if [[ $is_deb ]]; then
|
||||||
|
update-alternatives --set newt-palette /etc/newt/palette.original
|
||||||
|
fi
|
||||||
|
}
|
||||||
|
|
||||||
set_version() {
|
set_version() {
|
||||||
CURRENTVERSION=0.0.0
|
CURRENTVERSION=0.0.0
|
||||||
|
|||||||
@@ -32,6 +32,7 @@ container_list() {
|
|||||||
"so-nginx"
|
"so-nginx"
|
||||||
"so-pcaptools"
|
"so-pcaptools"
|
||||||
"so-soc"
|
"so-soc"
|
||||||
|
"so-steno"
|
||||||
"so-suricata"
|
"so-suricata"
|
||||||
"so-telegraf"
|
"so-telegraf"
|
||||||
"so-zeek"
|
"so-zeek"
|
||||||
@@ -57,6 +58,7 @@ container_list() {
|
|||||||
"so-pcaptools"
|
"so-pcaptools"
|
||||||
"so-redis"
|
"so-redis"
|
||||||
"so-soc"
|
"so-soc"
|
||||||
|
"so-steno"
|
||||||
"so-strelka-backend"
|
"so-strelka-backend"
|
||||||
"so-strelka-manager"
|
"so-strelka-manager"
|
||||||
"so-suricata"
|
"so-suricata"
|
||||||
@@ -69,6 +71,7 @@ container_list() {
|
|||||||
"so-logstash"
|
"so-logstash"
|
||||||
"so-nginx"
|
"so-nginx"
|
||||||
"so-redis"
|
"so-redis"
|
||||||
|
"so-steno"
|
||||||
"so-suricata"
|
"so-suricata"
|
||||||
"so-soc"
|
"so-soc"
|
||||||
"so-telegraf"
|
"so-telegraf"
|
||||||
|
|||||||
@@ -129,8 +129,6 @@ if [[ $EXCLUDE_STARTUP_ERRORS == 'Y' ]]; then
|
|||||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|responded with status-code 503" # telegraf getting 503 from ES during startup
|
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|responded with status-code 503" # telegraf getting 503 from ES during startup
|
||||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|process_cluster_event_timeout_exception" # logstash waiting for elasticsearch to start
|
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|process_cluster_event_timeout_exception" # logstash waiting for elasticsearch to start
|
||||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|not configured for GeoIP" # SO does not bundle the maxminddb with Zeek
|
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|not configured for GeoIP" # SO does not bundle the maxminddb with Zeek
|
||||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|HTTP 404: Not Found" # Salt loops until Kratos returns 200, during startup Kratos may not be ready
|
|
||||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|Cancelling deferred write event maybeFenceReplicas because the event queue is now closed" # Kafka controller log during shutdown/restart
|
|
||||||
fi
|
fi
|
||||||
|
|
||||||
if [[ $EXCLUDE_FALSE_POSITIVE_ERRORS == 'Y' ]]; then
|
if [[ $EXCLUDE_FALSE_POSITIVE_ERRORS == 'Y' ]]; then
|
||||||
@@ -161,9 +159,7 @@ if [[ $EXCLUDE_FALSE_POSITIVE_ERRORS == 'Y' ]]; then
|
|||||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|adding ingest pipeline" # false positive (elasticsearch ingest pipeline names contain 'error')
|
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|adding ingest pipeline" # false positive (elasticsearch ingest pipeline names contain 'error')
|
||||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|updating index template" # false positive (elasticsearch index or template names contain 'error')
|
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|updating index template" # false positive (elasticsearch index or template names contain 'error')
|
||||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|updating component template" # false positive (elasticsearch index or template names contain 'error')
|
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|updating component template" # false positive (elasticsearch index or template names contain 'error')
|
||||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|upgrading component template" # false positive (elasticsearch index or template names contain 'error')
|
|
||||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|upgrading composable template" # false positive (elasticsearch composable template names contain 'error')
|
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|upgrading composable template" # false positive (elasticsearch composable template names contain 'error')
|
||||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|Error while parsing document for index \[.ds-logs-kratos-so-.*object mapping for \[file\]" # false positive (mapping error occuring BEFORE kratos index has rolled over in 2.4.210)
|
|
||||||
fi
|
fi
|
||||||
|
|
||||||
if [[ $EXCLUDE_KNOWN_ERRORS == 'Y' ]]; then
|
if [[ $EXCLUDE_KNOWN_ERRORS == 'Y' ]]; then
|
||||||
@@ -179,6 +175,7 @@ if [[ $EXCLUDE_KNOWN_ERRORS == 'Y' ]]; then
|
|||||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|salt-minion-check" # bug in early 2.4 place Jinja script in non-jinja salt dir causing cron output errors
|
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|salt-minion-check" # bug in early 2.4 place Jinja script in non-jinja salt dir causing cron output errors
|
||||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|monitoring.metrics" # known issue with elastic agent casting the field incorrectly if an integer value shows up before a float
|
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|monitoring.metrics" # known issue with elastic agent casting the field incorrectly if an integer value shows up before a float
|
||||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|repodownload.conf" # known issue with reposync on pre-2.4.20
|
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|repodownload.conf" # known issue with reposync on pre-2.4.20
|
||||||
|
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|missing versions record" # stenographer corrupt index
|
||||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|soc.field." # known ingest type collisions issue with earlier versions of SO
|
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|soc.field." # known ingest type collisions issue with earlier versions of SO
|
||||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|error parsing signature" # Malformed Suricata rule, from upstream provider
|
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|error parsing signature" # Malformed Suricata rule, from upstream provider
|
||||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|sticky buffer has no matches" # Non-critical Suricata error
|
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|sticky buffer has no matches" # Non-critical Suricata error
|
||||||
@@ -226,8 +223,6 @@ if [[ $EXCLUDE_KNOWN_ERRORS == 'Y' ]]; then
|
|||||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|from NIC checksum offloading" # zeek reporter.log
|
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|from NIC checksum offloading" # zeek reporter.log
|
||||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|marked for removal" # docker container getting recycled
|
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|marked for removal" # docker container getting recycled
|
||||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|tcp 127.0.0.1:6791: bind: address already in use" # so-elastic-fleet agent restarting. Seen starting w/ 8.18.8 https://github.com/elastic/kibana/issues/201459
|
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|tcp 127.0.0.1:6791: bind: address already in use" # so-elastic-fleet agent restarting. Seen starting w/ 8.18.8 https://github.com/elastic/kibana/issues/201459
|
||||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|TransformTask\] \[logs-(tychon|aws_billing|microsoft_defender_endpoint).*user so_kibana lacks the required permissions \[logs-\1" # Known issue with 3 integrations using kibana_system role vs creating unique api creds with proper permissions.
|
|
||||||
EXCLUDED_ERRORS="$EXCLUDED_ERRORS|manifest unknown" # appears in so-dockerregistry log for so-tcpreplay following docker upgrade to 29.2.1-1
|
|
||||||
fi
|
fi
|
||||||
|
|
||||||
RESULT=0
|
RESULT=0
|
||||||
|
|||||||
@@ -55,22 +55,19 @@ if [ $SKIP -ne 1 ]; then
|
|||||||
fi
|
fi
|
||||||
|
|
||||||
delete_pcap() {
|
delete_pcap() {
|
||||||
PCAP_DATA="/nsm/suripcap/"
|
PCAP_DATA="/nsm/pcap/"
|
||||||
[ -d $PCAP_DATA ] && rm -rf $PCAP_DATA/*
|
[ -d $PCAP_DATA ] && so-pcap-stop && rm -rf $PCAP_DATA/* && so-pcap-start
|
||||||
}
|
}
|
||||||
delete_suricata() {
|
delete_suricata() {
|
||||||
SURI_LOG="/nsm/suricata/"
|
SURI_LOG="/nsm/suricata/"
|
||||||
[ -d $SURI_LOG ] && rm -rf $SURI_LOG/*
|
[ -d $SURI_LOG ] && so-suricata-stop && rm -rf $SURI_LOG/* && so-suricata-start
|
||||||
}
|
}
|
||||||
delete_zeek() {
|
delete_zeek() {
|
||||||
ZEEK_LOG="/nsm/zeek/logs/"
|
ZEEK_LOG="/nsm/zeek/logs/"
|
||||||
[ -d $ZEEK_LOG ] && so-zeek-stop && rm -rf $ZEEK_LOG/* && so-zeek-start
|
[ -d $ZEEK_LOG ] && so-zeek-stop && rm -rf $ZEEK_LOG/* && so-zeek-start
|
||||||
}
|
}
|
||||||
|
|
||||||
so-suricata-stop
|
|
||||||
delete_pcap
|
delete_pcap
|
||||||
delete_suricata
|
delete_suricata
|
||||||
delete_zeek
|
delete_zeek
|
||||||
so-suricata-start
|
|
||||||
|
|
||||||
|
|
||||||
|
|||||||
@@ -23,6 +23,7 @@ if [ $# -ge 1 ]; then
|
|||||||
fi
|
fi
|
||||||
|
|
||||||
case $1 in
|
case $1 in
|
||||||
|
"steno") docker stop so-steno && docker rm so-steno && salt-call state.apply pcap queue=True;;
|
||||||
"elastic-fleet") docker stop so-elastic-fleet && docker rm so-elastic-fleet && salt-call state.apply elasticfleet queue=True;;
|
"elastic-fleet") docker stop so-elastic-fleet && docker rm so-elastic-fleet && salt-call state.apply elasticfleet queue=True;;
|
||||||
*) docker stop so-$1 ; docker rm so-$1 ; salt-call state.apply $1 queue=True;;
|
*) docker stop so-$1 ; docker rm so-$1 ; salt-call state.apply $1 queue=True;;
|
||||||
esac
|
esac
|
||||||
|
|||||||
@@ -72,7 +72,7 @@ clean() {
|
|||||||
done
|
done
|
||||||
fi
|
fi
|
||||||
|
|
||||||
## Clean up extracted pcaps
|
## Clean up extracted pcaps from Steno
|
||||||
PCAPS='/nsm/pcapout'
|
PCAPS='/nsm/pcapout'
|
||||||
OLDEST_PCAP=$(find $PCAPS -type f -printf '%T+ %p\n' | sort -n | head -n 1)
|
OLDEST_PCAP=$(find $PCAPS -type f -printf '%T+ %p\n' | sort -n | head -n 1)
|
||||||
if [ -z "$OLDEST_PCAP" -o "$OLDEST_PCAP" == ".." -o "$OLDEST_PCAP" == "." ]; then
|
if [ -z "$OLDEST_PCAP" -o "$OLDEST_PCAP" == ".." -o "$OLDEST_PCAP" == "." ]; then
|
||||||
|
|||||||
@@ -23,6 +23,7 @@ if [ $# -ge 1 ]; then
|
|||||||
|
|
||||||
case $1 in
|
case $1 in
|
||||||
"all") salt-call state.highstate queue=True;;
|
"all") salt-call state.highstate queue=True;;
|
||||||
|
"steno") if docker ps | grep -q so-$1; then printf "\n$1 is already running!\n\n"; else docker rm so-$1 >/dev/null 2>&1 ; salt-call state.apply pcap queue=True; fi ;;
|
||||||
"elastic-fleet") if docker ps | grep -q so-$1; then printf "\n$1 is already running!\n\n"; else docker rm so-$1 >/dev/null 2>&1 ; salt-call state.apply elasticfleet queue=True; fi ;;
|
"elastic-fleet") if docker ps | grep -q so-$1; then printf "\n$1 is already running!\n\n"; else docker rm so-$1 >/dev/null 2>&1 ; salt-call state.apply elasticfleet queue=True; fi ;;
|
||||||
*) if docker ps | grep -E -q '^so-$1$'; then printf "\n$1 is already running\n\n"; else docker rm so-$1 >/dev/null 2>&1 ; salt-call state.apply $1 queue=True; fi ;;
|
*) if docker ps | grep -E -q '^so-$1$'; then printf "\n$1 is already running\n\n"; else docker rm so-$1 >/dev/null 2>&1 ; salt-call state.apply $1 queue=True; fi ;;
|
||||||
esac
|
esac
|
||||||
|
|||||||
@@ -6,7 +6,7 @@
|
|||||||
# Elastic License 2.0.
|
# Elastic License 2.0.
|
||||||
|
|
||||||
source /usr/sbin/so-common
|
source /usr/sbin/so-common
|
||||||
doc_desktop_url="$DOC_BASE_URL/desktop"
|
doc_desktop_url="$DOC_BASE_URL/desktop.html"
|
||||||
|
|
||||||
{# we only want the script to install the desktop if it is OEL -#}
|
{# we only want the script to install the desktop if it is OEL -#}
|
||||||
{% if grains.os == 'OEL' -%}
|
{% if grains.os == 'OEL' -%}
|
||||||
|
|||||||
34
salt/curator/disabled.sls
Normal file
34
salt/curator/disabled.sls
Normal file
@@ -0,0 +1,34 @@
|
|||||||
|
# Copyright Security Onion Solutions LLC and/or licensed to Security Onion Solutions LLC under one
|
||||||
|
# or more contributor license agreements. Licensed under the Elastic License 2.0 as shown at
|
||||||
|
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||||
|
# Elastic License 2.0.
|
||||||
|
|
||||||
|
so-curator:
|
||||||
|
docker_container.absent:
|
||||||
|
- force: True
|
||||||
|
|
||||||
|
so-curator_so-status.disabled:
|
||||||
|
file.line:
|
||||||
|
- name: /opt/so/conf/so-status/so-status.conf
|
||||||
|
- match: ^so-curator$
|
||||||
|
- mode: delete
|
||||||
|
|
||||||
|
so-curator-cluster-close:
|
||||||
|
cron.absent:
|
||||||
|
- identifier: so-curator-cluster-close
|
||||||
|
|
||||||
|
so-curator-cluster-delete:
|
||||||
|
cron.absent:
|
||||||
|
- identifier: so-curator-cluster-delete
|
||||||
|
|
||||||
|
delete_curator_configuration:
|
||||||
|
file.absent:
|
||||||
|
- name: /opt/so/conf/curator
|
||||||
|
- recurse: True
|
||||||
|
|
||||||
|
{% set files = salt.file.find(path='/usr/sbin', name='so-curator*') %}
|
||||||
|
{% if files|length > 0 %}
|
||||||
|
delete_curator_scripts:
|
||||||
|
file.absent:
|
||||||
|
- names: {{files|yaml}}
|
||||||
|
{% endif %}
|
||||||
@@ -3,16 +3,29 @@
|
|||||||
{# we only want this state to run it is CentOS #}
|
{# we only want this state to run it is CentOS #}
|
||||||
{% if GLOBALS.os == 'OEL' %}
|
{% if GLOBALS.os == 'OEL' %}
|
||||||
|
|
||||||
|
{% set global_ca_text = [] %}
|
||||||
|
{% set global_ca_server = [] %}
|
||||||
|
{% set manager = GLOBALS.manager %}
|
||||||
|
{% set x509dict = salt['mine.get'](manager | lower~'*', 'x509.get_pem_entries') %}
|
||||||
|
{% for host in x509dict %}
|
||||||
|
{% if host.split('_')|last in ['manager', 'managersearch', 'standalone', 'import', 'eval'] %}
|
||||||
|
{% do global_ca_text.append(x509dict[host].get('/etc/pki/ca.crt')|replace('\n', '')) %}
|
||||||
|
{% do global_ca_server.append(host) %}
|
||||||
|
{% endif %}
|
||||||
|
{% endfor %}
|
||||||
|
{% set trusttheca_text = global_ca_text[0] %}
|
||||||
|
{% set ca_server = global_ca_server[0] %}
|
||||||
|
|
||||||
trusted_ca:
|
trusted_ca:
|
||||||
file.managed:
|
x509.pem_managed:
|
||||||
- name: /etc/pki/ca-trust/source/anchors/ca.crt
|
- name: /etc/pki/ca-trust/source/anchors/ca.crt
|
||||||
- source: salt://ca/files/ca.crt
|
- text: {{ trusttheca_text }}
|
||||||
|
|
||||||
update_ca_certs:
|
update_ca_certs:
|
||||||
cmd.run:
|
cmd.run:
|
||||||
- name: update-ca-trust
|
- name: update-ca-trust
|
||||||
- onchanges:
|
- onchanges:
|
||||||
- file: trusted_ca
|
- x509: trusted_ca
|
||||||
|
|
||||||
{% else %}
|
{% else %}
|
||||||
|
|
||||||
|
|||||||
@@ -1,10 +1,6 @@
|
|||||||
docker:
|
docker:
|
||||||
range: '172.17.1.0/24'
|
range: '172.17.1.0/24'
|
||||||
gateway: '172.17.1.1'
|
gateway: '172.17.1.1'
|
||||||
ulimits:
|
|
||||||
- name: nofile
|
|
||||||
soft: 1048576
|
|
||||||
hard: 1048576
|
|
||||||
containers:
|
containers:
|
||||||
'so-dockerregistry':
|
'so-dockerregistry':
|
||||||
final_octet: 20
|
final_octet: 20
|
||||||
@@ -13,7 +9,6 @@ docker:
|
|||||||
custom_bind_mounts: []
|
custom_bind_mounts: []
|
||||||
extra_hosts: []
|
extra_hosts: []
|
||||||
extra_env: []
|
extra_env: []
|
||||||
ulimits: []
|
|
||||||
'so-elastic-fleet':
|
'so-elastic-fleet':
|
||||||
final_octet: 21
|
final_octet: 21
|
||||||
port_bindings:
|
port_bindings:
|
||||||
@@ -21,7 +16,6 @@ docker:
|
|||||||
custom_bind_mounts: []
|
custom_bind_mounts: []
|
||||||
extra_hosts: []
|
extra_hosts: []
|
||||||
extra_env: []
|
extra_env: []
|
||||||
ulimits: []
|
|
||||||
'so-elasticsearch':
|
'so-elasticsearch':
|
||||||
final_octet: 22
|
final_octet: 22
|
||||||
port_bindings:
|
port_bindings:
|
||||||
@@ -30,16 +24,6 @@ docker:
|
|||||||
custom_bind_mounts: []
|
custom_bind_mounts: []
|
||||||
extra_hosts: []
|
extra_hosts: []
|
||||||
extra_env: []
|
extra_env: []
|
||||||
ulimits:
|
|
||||||
- name: memlock
|
|
||||||
soft: -1
|
|
||||||
hard: -1
|
|
||||||
- name: nofile
|
|
||||||
soft: 65536
|
|
||||||
hard: 65536
|
|
||||||
- name: nproc
|
|
||||||
soft: 4096
|
|
||||||
hard: 4096
|
|
||||||
'so-influxdb':
|
'so-influxdb':
|
||||||
final_octet: 26
|
final_octet: 26
|
||||||
port_bindings:
|
port_bindings:
|
||||||
@@ -47,7 +31,6 @@ docker:
|
|||||||
custom_bind_mounts: []
|
custom_bind_mounts: []
|
||||||
extra_hosts: []
|
extra_hosts: []
|
||||||
extra_env: []
|
extra_env: []
|
||||||
ulimits: []
|
|
||||||
'so-kibana':
|
'so-kibana':
|
||||||
final_octet: 27
|
final_octet: 27
|
||||||
port_bindings:
|
port_bindings:
|
||||||
@@ -55,7 +38,6 @@ docker:
|
|||||||
custom_bind_mounts: []
|
custom_bind_mounts: []
|
||||||
extra_hosts: []
|
extra_hosts: []
|
||||||
extra_env: []
|
extra_env: []
|
||||||
ulimits: []
|
|
||||||
'so-kratos':
|
'so-kratos':
|
||||||
final_octet: 28
|
final_octet: 28
|
||||||
port_bindings:
|
port_bindings:
|
||||||
@@ -64,7 +46,6 @@ docker:
|
|||||||
custom_bind_mounts: []
|
custom_bind_mounts: []
|
||||||
extra_hosts: []
|
extra_hosts: []
|
||||||
extra_env: []
|
extra_env: []
|
||||||
ulimits: []
|
|
||||||
'so-hydra':
|
'so-hydra':
|
||||||
final_octet: 30
|
final_octet: 30
|
||||||
port_bindings:
|
port_bindings:
|
||||||
@@ -73,7 +54,6 @@ docker:
|
|||||||
custom_bind_mounts: []
|
custom_bind_mounts: []
|
||||||
extra_hosts: []
|
extra_hosts: []
|
||||||
extra_env: []
|
extra_env: []
|
||||||
ulimits: []
|
|
||||||
'so-logstash':
|
'so-logstash':
|
||||||
final_octet: 29
|
final_octet: 29
|
||||||
port_bindings:
|
port_bindings:
|
||||||
@@ -90,7 +70,6 @@ docker:
|
|||||||
custom_bind_mounts: []
|
custom_bind_mounts: []
|
||||||
extra_hosts: []
|
extra_hosts: []
|
||||||
extra_env: []
|
extra_env: []
|
||||||
ulimits: []
|
|
||||||
'so-nginx':
|
'so-nginx':
|
||||||
final_octet: 31
|
final_octet: 31
|
||||||
port_bindings:
|
port_bindings:
|
||||||
@@ -102,7 +81,6 @@ docker:
|
|||||||
custom_bind_mounts: []
|
custom_bind_mounts: []
|
||||||
extra_hosts: []
|
extra_hosts: []
|
||||||
extra_env: []
|
extra_env: []
|
||||||
ulimits: []
|
|
||||||
'so-nginx-fleet-node':
|
'so-nginx-fleet-node':
|
||||||
final_octet: 31
|
final_octet: 31
|
||||||
port_bindings:
|
port_bindings:
|
||||||
@@ -110,7 +88,6 @@ docker:
|
|||||||
custom_bind_mounts: []
|
custom_bind_mounts: []
|
||||||
extra_hosts: []
|
extra_hosts: []
|
||||||
extra_env: []
|
extra_env: []
|
||||||
ulimits: []
|
|
||||||
'so-redis':
|
'so-redis':
|
||||||
final_octet: 33
|
final_octet: 33
|
||||||
port_bindings:
|
port_bindings:
|
||||||
@@ -119,13 +96,11 @@ docker:
|
|||||||
custom_bind_mounts: []
|
custom_bind_mounts: []
|
||||||
extra_hosts: []
|
extra_hosts: []
|
||||||
extra_env: []
|
extra_env: []
|
||||||
ulimits: []
|
|
||||||
'so-sensoroni':
|
'so-sensoroni':
|
||||||
final_octet: 99
|
final_octet: 99
|
||||||
custom_bind_mounts: []
|
custom_bind_mounts: []
|
||||||
extra_hosts: []
|
extra_hosts: []
|
||||||
extra_env: []
|
extra_env: []
|
||||||
ulimits: []
|
|
||||||
'so-soc':
|
'so-soc':
|
||||||
final_octet: 34
|
final_octet: 34
|
||||||
port_bindings:
|
port_bindings:
|
||||||
@@ -133,19 +108,16 @@ docker:
|
|||||||
custom_bind_mounts: []
|
custom_bind_mounts: []
|
||||||
extra_hosts: []
|
extra_hosts: []
|
||||||
extra_env: []
|
extra_env: []
|
||||||
ulimits: []
|
|
||||||
'so-strelka-backend':
|
'so-strelka-backend':
|
||||||
final_octet: 36
|
final_octet: 36
|
||||||
custom_bind_mounts: []
|
custom_bind_mounts: []
|
||||||
extra_hosts: []
|
extra_hosts: []
|
||||||
extra_env: []
|
extra_env: []
|
||||||
ulimits: []
|
|
||||||
'so-strelka-filestream':
|
'so-strelka-filestream':
|
||||||
final_octet: 37
|
final_octet: 37
|
||||||
custom_bind_mounts: []
|
custom_bind_mounts: []
|
||||||
extra_hosts: []
|
extra_hosts: []
|
||||||
extra_env: []
|
extra_env: []
|
||||||
ulimits: []
|
|
||||||
'so-strelka-frontend':
|
'so-strelka-frontend':
|
||||||
final_octet: 38
|
final_octet: 38
|
||||||
port_bindings:
|
port_bindings:
|
||||||
@@ -153,13 +125,11 @@ docker:
|
|||||||
custom_bind_mounts: []
|
custom_bind_mounts: []
|
||||||
extra_hosts: []
|
extra_hosts: []
|
||||||
extra_env: []
|
extra_env: []
|
||||||
ulimits: []
|
|
||||||
'so-strelka-manager':
|
'so-strelka-manager':
|
||||||
final_octet: 39
|
final_octet: 39
|
||||||
custom_bind_mounts: []
|
custom_bind_mounts: []
|
||||||
extra_hosts: []
|
extra_hosts: []
|
||||||
extra_env: []
|
extra_env: []
|
||||||
ulimits: []
|
|
||||||
'so-strelka-gatekeeper':
|
'so-strelka-gatekeeper':
|
||||||
final_octet: 40
|
final_octet: 40
|
||||||
port_bindings:
|
port_bindings:
|
||||||
@@ -167,7 +137,6 @@ docker:
|
|||||||
custom_bind_mounts: []
|
custom_bind_mounts: []
|
||||||
extra_hosts: []
|
extra_hosts: []
|
||||||
extra_env: []
|
extra_env: []
|
||||||
ulimits: []
|
|
||||||
'so-strelka-coordinator':
|
'so-strelka-coordinator':
|
||||||
final_octet: 41
|
final_octet: 41
|
||||||
port_bindings:
|
port_bindings:
|
||||||
@@ -175,13 +144,11 @@ docker:
|
|||||||
custom_bind_mounts: []
|
custom_bind_mounts: []
|
||||||
extra_hosts: []
|
extra_hosts: []
|
||||||
extra_env: []
|
extra_env: []
|
||||||
ulimits: []
|
|
||||||
'so-elastalert':
|
'so-elastalert':
|
||||||
final_octet: 42
|
final_octet: 42
|
||||||
custom_bind_mounts: []
|
custom_bind_mounts: []
|
||||||
extra_hosts: []
|
extra_hosts: []
|
||||||
extra_env: []
|
extra_env: []
|
||||||
ulimits: []
|
|
||||||
'so-elastic-fleet-package-registry':
|
'so-elastic-fleet-package-registry':
|
||||||
final_octet: 44
|
final_octet: 44
|
||||||
port_bindings:
|
port_bindings:
|
||||||
@@ -189,13 +156,11 @@ docker:
|
|||||||
custom_bind_mounts: []
|
custom_bind_mounts: []
|
||||||
extra_hosts: []
|
extra_hosts: []
|
||||||
extra_env: []
|
extra_env: []
|
||||||
ulimits: []
|
|
||||||
'so-idh':
|
'so-idh':
|
||||||
final_octet: 45
|
final_octet: 45
|
||||||
custom_bind_mounts: []
|
custom_bind_mounts: []
|
||||||
extra_hosts: []
|
extra_hosts: []
|
||||||
extra_env: []
|
extra_env: []
|
||||||
ulimits: []
|
|
||||||
'so-elastic-agent':
|
'so-elastic-agent':
|
||||||
final_octet: 46
|
final_octet: 46
|
||||||
port_bindings:
|
port_bindings:
|
||||||
@@ -204,34 +169,28 @@ docker:
|
|||||||
custom_bind_mounts: []
|
custom_bind_mounts: []
|
||||||
extra_hosts: []
|
extra_hosts: []
|
||||||
extra_env: []
|
extra_env: []
|
||||||
ulimits: []
|
|
||||||
'so-telegraf':
|
'so-telegraf':
|
||||||
final_octet: 99
|
final_octet: 99
|
||||||
custom_bind_mounts: []
|
custom_bind_mounts: []
|
||||||
extra_hosts: []
|
extra_hosts: []
|
||||||
extra_env: []
|
extra_env: []
|
||||||
ulimits: []
|
'so-steno':
|
||||||
|
final_octet: 99
|
||||||
|
custom_bind_mounts: []
|
||||||
|
extra_hosts: []
|
||||||
|
extra_env: []
|
||||||
'so-suricata':
|
'so-suricata':
|
||||||
final_octet: 99
|
final_octet: 99
|
||||||
custom_bind_mounts: []
|
custom_bind_mounts: []
|
||||||
extra_hosts: []
|
extra_hosts: []
|
||||||
extra_env: []
|
extra_env: []
|
||||||
ulimits:
|
ulimits:
|
||||||
- name: memlock
|
- memlock=524288000
|
||||||
soft: 524288000
|
|
||||||
hard: 524288000
|
|
||||||
'so-zeek':
|
'so-zeek':
|
||||||
final_octet: 99
|
final_octet: 99
|
||||||
custom_bind_mounts: []
|
custom_bind_mounts: []
|
||||||
extra_hosts: []
|
extra_hosts: []
|
||||||
extra_env: []
|
extra_env: []
|
||||||
ulimits:
|
|
||||||
- name: core
|
|
||||||
soft: 0
|
|
||||||
hard: 0
|
|
||||||
- name: nofile
|
|
||||||
soft: 1048576
|
|
||||||
hard: 1048576
|
|
||||||
'so-kafka':
|
'so-kafka':
|
||||||
final_octet: 88
|
final_octet: 88
|
||||||
port_bindings:
|
port_bindings:
|
||||||
@@ -242,4 +201,3 @@ docker:
|
|||||||
custom_bind_mounts: []
|
custom_bind_mounts: []
|
||||||
extra_hosts: []
|
extra_hosts: []
|
||||||
extra_env: []
|
extra_env: []
|
||||||
ulimits: []
|
|
||||||
|
|||||||
@@ -1,8 +1,8 @@
|
|||||||
{% import_yaml 'docker/defaults.yaml' as DOCKERDEFAULTS %}
|
{% import_yaml 'docker/defaults.yaml' as DOCKERDEFAULTS %}
|
||||||
{% set DOCKERMERGED = salt['pillar.get']('docker', DOCKERDEFAULTS.docker, merge=True) %}
|
{% set DOCKER = salt['pillar.get']('docker', DOCKERDEFAULTS.docker, merge=True) %}
|
||||||
{% set RANGESPLIT = DOCKERMERGED.range.split('.') %}
|
{% set RANGESPLIT = DOCKER.range.split('.') %}
|
||||||
{% set FIRSTTHREE = RANGESPLIT[0] ~ '.' ~ RANGESPLIT[1] ~ '.' ~ RANGESPLIT[2] ~ '.' %}
|
{% set FIRSTTHREE = RANGESPLIT[0] ~ '.' ~ RANGESPLIT[1] ~ '.' ~ RANGESPLIT[2] ~ '.' %}
|
||||||
|
|
||||||
{% for container, vals in DOCKERMERGED.containers.items() %}
|
{% for container, vals in DOCKER.containers.items() %}
|
||||||
{% do DOCKERMERGED.containers[container].update({'ip': FIRSTTHREE ~ DOCKERMERGED.containers[container].final_octet}) %}
|
{% do DOCKER.containers[container].update({'ip': FIRSTTHREE ~ DOCKER.containers[container].final_octet}) %}
|
||||||
{% endfor %}
|
{% endfor %}
|
||||||
|
|||||||
@@ -1,24 +0,0 @@
|
|||||||
{% from 'docker/docker.map.jinja' import DOCKERMERGED -%}
|
|
||||||
{
|
|
||||||
"registry-mirrors": [
|
|
||||||
"https://:5000"
|
|
||||||
],
|
|
||||||
"bip": "172.17.0.1/24",
|
|
||||||
"default-address-pools": [
|
|
||||||
{
|
|
||||||
"base": "172.17.0.0/24",
|
|
||||||
"size": 24
|
|
||||||
}
|
|
||||||
]
|
|
||||||
{%- if DOCKERMERGED.ulimits %},
|
|
||||||
"default-ulimits": {
|
|
||||||
{%- for ULIMIT in DOCKERMERGED.ulimits %}
|
|
||||||
"{{ ULIMIT.name }}": {
|
|
||||||
"Name": "{{ ULIMIT.name }}",
|
|
||||||
"Soft": {{ ULIMIT.soft }},
|
|
||||||
"Hard": {{ ULIMIT.hard }}
|
|
||||||
}{{ "," if not loop.last else "" }}
|
|
||||||
{%- endfor %}
|
|
||||||
}
|
|
||||||
{%- endif %}
|
|
||||||
}
|
|
||||||
@@ -3,27 +3,61 @@
|
|||||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
# https://securityonion.net/license; you may not use this file except in compliance with the
|
||||||
# Elastic License 2.0.
|
# Elastic License 2.0.
|
||||||
|
|
||||||
{% from 'docker/docker.map.jinja' import DOCKERMERGED %}
|
{% from 'docker/docker.map.jinja' import DOCKER %}
|
||||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||||
|
|
||||||
# docker service requires the ca.crt
|
# include ssl since docker service requires the intca
|
||||||
include:
|
include:
|
||||||
- ca
|
- ssl
|
||||||
|
|
||||||
dockergroup:
|
dockergroup:
|
||||||
group.present:
|
group.present:
|
||||||
- name: docker
|
- name: docker
|
||||||
- gid: 920
|
- gid: 920
|
||||||
|
|
||||||
|
{% if GLOBALS.os_family == 'Debian' %}
|
||||||
|
{% if grains.oscodename == 'bookworm' %}
|
||||||
dockerheldpackages:
|
dockerheldpackages:
|
||||||
pkg.installed:
|
pkg.installed:
|
||||||
- pkgs:
|
- pkgs:
|
||||||
- containerd.io: 2.2.1-1.el9
|
- containerd.io: 1.7.21-1
|
||||||
- docker-ce: 3:29.2.1-1.el9
|
- docker-ce: 5:27.2.0-1~debian.12~bookworm
|
||||||
- docker-ce-cli: 1:29.2.1-1.el9
|
- docker-ce-cli: 5:27.2.0-1~debian.12~bookworm
|
||||||
- docker-ce-rootless-extras: 29.2.1-1.el9
|
- docker-ce-rootless-extras: 5:27.2.0-1~debian.12~bookworm
|
||||||
- hold: True
|
- hold: True
|
||||||
- update_holds: True
|
- update_holds: True
|
||||||
|
{% elif grains.oscodename == 'jammy' %}
|
||||||
|
dockerheldpackages:
|
||||||
|
pkg.installed:
|
||||||
|
- pkgs:
|
||||||
|
- containerd.io: 1.7.21-1
|
||||||
|
- docker-ce: 5:27.2.0-1~ubuntu.22.04~jammy
|
||||||
|
- docker-ce-cli: 5:27.2.0-1~ubuntu.22.04~jammy
|
||||||
|
- docker-ce-rootless-extras: 5:27.2.0-1~ubuntu.22.04~jammy
|
||||||
|
- hold: True
|
||||||
|
- update_holds: True
|
||||||
|
{% else %}
|
||||||
|
dockerheldpackages:
|
||||||
|
pkg.installed:
|
||||||
|
- pkgs:
|
||||||
|
- containerd.io: 1.7.21-1
|
||||||
|
- docker-ce: 5:27.2.0-1~ubuntu.20.04~focal
|
||||||
|
- docker-ce-cli: 5:27.2.0-1~ubuntu.20.04~focal
|
||||||
|
- docker-ce-rootless-extras: 5:27.2.0-1~ubuntu.20.04~focal
|
||||||
|
- hold: True
|
||||||
|
- update_holds: True
|
||||||
|
{% endif %}
|
||||||
|
{% else %}
|
||||||
|
dockerheldpackages:
|
||||||
|
pkg.installed:
|
||||||
|
- pkgs:
|
||||||
|
- containerd.io: 1.7.21-3.1.el9
|
||||||
|
- docker-ce: 3:27.2.0-1.el9
|
||||||
|
- docker-ce-cli: 1:27.2.0-1.el9
|
||||||
|
- docker-ce-rootless-extras: 27.2.0-1.el9
|
||||||
|
- hold: True
|
||||||
|
- update_holds: True
|
||||||
|
{% endif %}
|
||||||
|
|
||||||
#disable docker from managing iptables
|
#disable docker from managing iptables
|
||||||
iptables_disabled:
|
iptables_disabled:
|
||||||
@@ -41,9 +75,10 @@ dockeretc:
|
|||||||
file.directory:
|
file.directory:
|
||||||
- name: /etc/docker
|
- name: /etc/docker
|
||||||
|
|
||||||
|
# Manager daemon.json
|
||||||
docker_daemon:
|
docker_daemon:
|
||||||
file.managed:
|
file.managed:
|
||||||
- source: salt://docker/files/daemon.json.jinja
|
- source: salt://common/files/daemon.json
|
||||||
- name: /etc/docker/daemon.json
|
- name: /etc/docker/daemon.json
|
||||||
- template: jinja
|
- template: jinja
|
||||||
|
|
||||||
@@ -54,9 +89,10 @@ docker_running:
|
|||||||
- enable: True
|
- enable: True
|
||||||
- watch:
|
- watch:
|
||||||
- file: docker_daemon
|
- file: docker_daemon
|
||||||
|
- x509: trusttheca
|
||||||
- require:
|
- require:
|
||||||
- file: docker_daemon
|
- file: docker_daemon
|
||||||
- file: trusttheca
|
- x509: trusttheca
|
||||||
|
|
||||||
|
|
||||||
# Reserve OS ports for Docker proxy in case boot settings are not already applied/present
|
# Reserve OS ports for Docker proxy in case boot settings are not already applied/present
|
||||||
@@ -74,12 +110,12 @@ dockerreserveports:
|
|||||||
sos_docker_net:
|
sos_docker_net:
|
||||||
docker_network.present:
|
docker_network.present:
|
||||||
- name: sobridge
|
- name: sobridge
|
||||||
- subnet: {{ DOCKERMERGED.range }}
|
- subnet: {{ DOCKER.range }}
|
||||||
- gateway: {{ DOCKERMERGED.gateway }}
|
- gateway: {{ DOCKER.gateway }}
|
||||||
- options:
|
- options:
|
||||||
com.docker.network.bridge.name: 'sobridge'
|
com.docker.network.bridge.name: 'sobridge'
|
||||||
com.docker.network.driver.mtu: '1500'
|
com.docker.network.driver.mtu: '1500'
|
||||||
com.docker.network.bridge.enable_ip_masquerade: 'true'
|
com.docker.network.bridge.enable_ip_masquerade: 'true'
|
||||||
com.docker.network.bridge.enable_icc: 'true'
|
com.docker.network.bridge.enable_icc: 'true'
|
||||||
com.docker.network.bridge.host_binding_ipv4: '0.0.0.0'
|
com.docker.network.bridge.host_binding_ipv4: '0.0.0.0'
|
||||||
- unless: ip l | grep sobridge
|
- unless: 'docker network ls | grep sobridge'
|
||||||
|
|||||||
@@ -7,25 +7,6 @@ docker:
|
|||||||
description: Default docker IP range for containers.
|
description: Default docker IP range for containers.
|
||||||
helpLink: docker.html
|
helpLink: docker.html
|
||||||
advanced: True
|
advanced: True
|
||||||
ulimits:
|
|
||||||
description: |
|
|
||||||
Default ulimit settings applied to all containers via the Docker daemon. Each entry specifies a resource name (e.g. nofile, memlock, core, nproc) with soft and hard limits. Individual container ulimits override these defaults. Valid resource names include: cpu, fsize, data, stack, core, rss, nproc, nofile, memlock, as, locks, sigpending, msgqueue, nice, rtprio, rttime.
|
|
||||||
forcedType: "[]{}"
|
|
||||||
syntax: json
|
|
||||||
advanced: True
|
|
||||||
helpLink: docker.html
|
|
||||||
uiElements:
|
|
||||||
- field: name
|
|
||||||
label: Resource Name
|
|
||||||
required: True
|
|
||||||
regex: ^(cpu|fsize|data|stack|core|rss|nproc|nofile|memlock|as|locks|sigpending|msgqueue|nice|rtprio|rttime)$
|
|
||||||
regexFailureMessage: You must enter a valid ulimit name (cpu, fsize, data, stack, core, rss, nproc, nofile, memlock, as, locks, sigpending, msgqueue, nice, rtprio, rttime).
|
|
||||||
- field: soft
|
|
||||||
label: Soft Limit
|
|
||||||
forcedType: int
|
|
||||||
- field: hard
|
|
||||||
label: Hard Limit
|
|
||||||
forcedType: int
|
|
||||||
containers:
|
containers:
|
||||||
so-dockerregistry: &dockerOptions
|
so-dockerregistry: &dockerOptions
|
||||||
final_octet:
|
final_octet:
|
||||||
@@ -58,25 +39,6 @@ docker:
|
|||||||
helpLink: docker.html
|
helpLink: docker.html
|
||||||
multiline: True
|
multiline: True
|
||||||
forcedType: "[]string"
|
forcedType: "[]string"
|
||||||
ulimits:
|
|
||||||
description: |
|
|
||||||
Ulimit settings for the container. Each entry specifies a resource name (e.g. nofile, memlock, core, nproc) with optional soft and hard limits. Valid resource names include: cpu, fsize, data, stack, core, rss, nproc, nofile, memlock, as, locks, sigpending, msgqueue, nice, rtprio, rttime.
|
|
||||||
advanced: True
|
|
||||||
helpLink: docker.html
|
|
||||||
forcedType: "[]{}"
|
|
||||||
syntax: json
|
|
||||||
uiElements:
|
|
||||||
- field: name
|
|
||||||
label: Resource Name
|
|
||||||
required: True
|
|
||||||
regex: ^(cpu|fsize|data|stack|core|rss|nproc|nofile|memlock|as|locks|sigpending|msgqueue|nice|rtprio|rttime)$
|
|
||||||
regexFailureMessage: You must enter a valid ulimit name (cpu, fsize, data, stack, core, rss, nproc, nofile, memlock, as, locks, sigpending, msgqueue, nice, rtprio, rttime).
|
|
||||||
- field: soft
|
|
||||||
label: Soft Limit
|
|
||||||
forcedType: int
|
|
||||||
- field: hard
|
|
||||||
label: Hard Limit
|
|
||||||
forcedType: int
|
|
||||||
so-elastic-fleet: *dockerOptions
|
so-elastic-fleet: *dockerOptions
|
||||||
so-elasticsearch: *dockerOptions
|
so-elasticsearch: *dockerOptions
|
||||||
so-influxdb: *dockerOptions
|
so-influxdb: *dockerOptions
|
||||||
@@ -100,6 +62,43 @@ docker:
|
|||||||
so-idh: *dockerOptions
|
so-idh: *dockerOptions
|
||||||
so-elastic-agent: *dockerOptions
|
so-elastic-agent: *dockerOptions
|
||||||
so-telegraf: *dockerOptions
|
so-telegraf: *dockerOptions
|
||||||
so-suricata: *dockerOptions
|
so-steno: *dockerOptions
|
||||||
|
so-suricata:
|
||||||
|
final_octet:
|
||||||
|
description: Last octet of the container IP address.
|
||||||
|
helpLink: docker.html
|
||||||
|
readonly: True
|
||||||
|
advanced: True
|
||||||
|
global: True
|
||||||
|
port_bindings:
|
||||||
|
description: List of port bindings for the container.
|
||||||
|
helpLink: docker.html
|
||||||
|
advanced: True
|
||||||
|
multiline: True
|
||||||
|
forcedType: "[]string"
|
||||||
|
custom_bind_mounts:
|
||||||
|
description: List of custom local volume bindings.
|
||||||
|
advanced: True
|
||||||
|
helpLink: docker.html
|
||||||
|
multiline: True
|
||||||
|
forcedType: "[]string"
|
||||||
|
extra_hosts:
|
||||||
|
description: List of additional host entries for the container.
|
||||||
|
advanced: True
|
||||||
|
helpLink: docker.html
|
||||||
|
multiline: True
|
||||||
|
forcedType: "[]string"
|
||||||
|
extra_env:
|
||||||
|
description: List of additional ENV entries for the container.
|
||||||
|
advanced: True
|
||||||
|
helpLink: docker.html
|
||||||
|
multiline: True
|
||||||
|
forcedType: "[]string"
|
||||||
|
ulimits:
|
||||||
|
description: Ulimits for the container, in bytes.
|
||||||
|
advanced: True
|
||||||
|
helpLink: docker.html
|
||||||
|
multiline: True
|
||||||
|
forcedType: "[]string"
|
||||||
so-zeek: *dockerOptions
|
so-zeek: *dockerOptions
|
||||||
so-kafka: *dockerOptions
|
so-kafka: *dockerOptions
|
||||||
|
|||||||
@@ -6,7 +6,7 @@
|
|||||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
{% from 'allowed_states.map.jinja' import allowed_states %}
|
||||||
{% if sls.split('.')[0] in allowed_states %}
|
{% if sls.split('.')[0] in allowed_states %}
|
||||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||||
{% from 'docker/docker.map.jinja' import DOCKERMERGED %}
|
{% from 'docker/docker.map.jinja' import DOCKER %}
|
||||||
|
|
||||||
include:
|
include:
|
||||||
- elastalert.config
|
- elastalert.config
|
||||||
@@ -24,7 +24,7 @@ so-elastalert:
|
|||||||
- user: so-elastalert
|
- user: so-elastalert
|
||||||
- networks:
|
- networks:
|
||||||
- sobridge:
|
- sobridge:
|
||||||
- ipv4_address: {{ DOCKERMERGED.containers['so-elastalert'].ip }}
|
- ipv4_address: {{ DOCKER.containers['so-elastalert'].ip }}
|
||||||
- detach: True
|
- detach: True
|
||||||
- binds:
|
- binds:
|
||||||
- /opt/so/rules/elastalert:/opt/elastalert/rules/:ro
|
- /opt/so/rules/elastalert:/opt/elastalert/rules/:ro
|
||||||
@@ -33,30 +33,24 @@ so-elastalert:
|
|||||||
- /opt/so/conf/elastalert/predefined/:/opt/elastalert/predefined/:ro
|
- /opt/so/conf/elastalert/predefined/:/opt/elastalert/predefined/:ro
|
||||||
- /opt/so/conf/elastalert/custom/:/opt/elastalert/custom/:ro
|
- /opt/so/conf/elastalert/custom/:/opt/elastalert/custom/:ro
|
||||||
- /opt/so/conf/elastalert/elastalert_config.yaml:/opt/elastalert/config.yaml:ro
|
- /opt/so/conf/elastalert/elastalert_config.yaml:/opt/elastalert/config.yaml:ro
|
||||||
{% if DOCKERMERGED.containers['so-elastalert'].custom_bind_mounts %}
|
{% if DOCKER.containers['so-elastalert'].custom_bind_mounts %}
|
||||||
{% for BIND in DOCKERMERGED.containers['so-elastalert'].custom_bind_mounts %}
|
{% for BIND in DOCKER.containers['so-elastalert'].custom_bind_mounts %}
|
||||||
- {{ BIND }}
|
- {{ BIND }}
|
||||||
{% endfor %}
|
{% endfor %}
|
||||||
{% endif %}
|
{% endif %}
|
||||||
- extra_hosts:
|
- extra_hosts:
|
||||||
- {{ GLOBALS.manager }}:{{ GLOBALS.manager_ip }}
|
- {{ GLOBALS.manager }}:{{ GLOBALS.manager_ip }}
|
||||||
{% if DOCKERMERGED.containers['so-elastalert'].extra_hosts %}
|
{% if DOCKER.containers['so-elastalert'].extra_hosts %}
|
||||||
{% for XTRAHOST in DOCKERMERGED.containers['so-elastalert'].extra_hosts %}
|
{% for XTRAHOST in DOCKER.containers['so-elastalert'].extra_hosts %}
|
||||||
- {{ XTRAHOST }}
|
- {{ XTRAHOST }}
|
||||||
{% endfor %}
|
{% endfor %}
|
||||||
{% endif %}
|
{% endif %}
|
||||||
{% if DOCKERMERGED.containers['so-elastalert'].extra_env %}
|
{% if DOCKER.containers['so-elastalert'].extra_env %}
|
||||||
- environment:
|
- environment:
|
||||||
{% for XTRAENV in DOCKERMERGED.containers['so-elastalert'].extra_env %}
|
{% for XTRAENV in DOCKER.containers['so-elastalert'].extra_env %}
|
||||||
- {{ XTRAENV }}
|
- {{ XTRAENV }}
|
||||||
{% endfor %}
|
{% endfor %}
|
||||||
{% endif %}
|
{% endif %}
|
||||||
{% if DOCKERMERGED.containers['so-elastalert'].ulimits %}
|
|
||||||
- ulimits:
|
|
||||||
{% for ULIMIT in DOCKERMERGED.containers['so-elastalert'].ulimits %}
|
|
||||||
- {{ ULIMIT.name }}={{ ULIMIT.soft }}:{{ ULIMIT.hard }}
|
|
||||||
{% endfor %}
|
|
||||||
{% endif %}
|
|
||||||
- require:
|
- require:
|
||||||
- cmd: wait_for_elasticsearch
|
- cmd: wait_for_elasticsearch
|
||||||
- file: elastarules
|
- file: elastarules
|
||||||
@@ -66,7 +60,7 @@ so-elastalert:
|
|||||||
- watch:
|
- watch:
|
||||||
- file: elastaconf
|
- file: elastaconf
|
||||||
- onlyif:
|
- onlyif:
|
||||||
- "so-elasticsearch-query / | jq -r '.version.number[0:1]' | grep -q 9" {# only run this state if elasticsearch is version 9 #}
|
- "so-elasticsearch-query / | jq -r '.version.number[0:1]' | grep -q 8" {# only run this state if elasticsearch is version 8 #}
|
||||||
|
|
||||||
delete_so-elastalert_so-status.disabled:
|
delete_so-elastalert_so-status.disabled:
|
||||||
file.uncomment:
|
file.uncomment:
|
||||||
|
|||||||
1
salt/elastalert/files/custom/placeholder
Normal file
1
salt/elastalert/files/custom/placeholder
Normal file
@@ -0,0 +1 @@
|
|||||||
|
THIS IS A PLACEHOLDER FILE
|
||||||
@@ -6,7 +6,7 @@
|
|||||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
{% from 'allowed_states.map.jinja' import allowed_states %}
|
||||||
{% if sls.split('.')[0] in allowed_states %}
|
{% if sls.split('.')[0] in allowed_states %}
|
||||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||||
{% from 'docker/docker.map.jinja' import DOCKERMERGED %}
|
{% from 'docker/docker.map.jinja' import DOCKER %}
|
||||||
|
|
||||||
include:
|
include:
|
||||||
- elastic-fleet-package-registry.config
|
- elastic-fleet-package-registry.config
|
||||||
@@ -21,36 +21,30 @@ so-elastic-fleet-package-registry:
|
|||||||
- user: 948
|
- user: 948
|
||||||
- networks:
|
- networks:
|
||||||
- sobridge:
|
- sobridge:
|
||||||
- ipv4_address: {{ DOCKERMERGED.containers['so-elastic-fleet-package-registry'].ip }}
|
- ipv4_address: {{ DOCKER.containers['so-elastic-fleet-package-registry'].ip }}
|
||||||
- extra_hosts:
|
- extra_hosts:
|
||||||
- {{ GLOBALS.hostname }}:{{ GLOBALS.node_ip }}
|
- {{ GLOBALS.hostname }}:{{ GLOBALS.node_ip }}
|
||||||
{% if DOCKERMERGED.containers['so-elastic-fleet-package-registry'].extra_hosts %}
|
{% if DOCKER.containers['so-elastic-fleet-package-registry'].extra_hosts %}
|
||||||
{% for XTRAHOST in DOCKERMERGED.containers['so-elastic-fleet-package-registry'].extra_hosts %}
|
{% for XTRAHOST in DOCKER.containers['so-elastic-fleet-package-registry'].extra_hosts %}
|
||||||
- {{ XTRAHOST }}
|
- {{ XTRAHOST }}
|
||||||
{% endfor %}
|
{% endfor %}
|
||||||
{% endif %}
|
{% endif %}
|
||||||
- port_bindings:
|
- port_bindings:
|
||||||
{% for BINDING in DOCKERMERGED.containers['so-elastic-fleet-package-registry'].port_bindings %}
|
{% for BINDING in DOCKER.containers['so-elastic-fleet-package-registry'].port_bindings %}
|
||||||
- {{ BINDING }}
|
- {{ BINDING }}
|
||||||
{% endfor %}
|
{% endfor %}
|
||||||
{% if DOCKERMERGED.containers['so-elastic-fleet-package-registry'].custom_bind_mounts %}
|
{% if DOCKER.containers['so-elastic-fleet-package-registry'].custom_bind_mounts %}
|
||||||
- binds:
|
- binds:
|
||||||
{% for BIND in DOCKERMERGED.containers['so-elastic-fleet-package-registry'].custom_bind_mounts %}
|
{% for BIND in DOCKER.containers['so-elastic-fleet-package-registry'].custom_bind_mounts %}
|
||||||
- {{ BIND }}
|
- {{ BIND }}
|
||||||
{% endfor %}
|
{% endfor %}
|
||||||
{% endif %}
|
{% endif %}
|
||||||
{% if DOCKERMERGED.containers['so-elastic-fleet-package-registry'].extra_env %}
|
{% if DOCKER.containers['so-elastic-fleet-package-registry'].extra_env %}
|
||||||
- environment:
|
- environment:
|
||||||
{% for XTRAENV in DOCKERMERGED.containers['so-elastic-fleet-package-registry'].extra_env %}
|
{% for XTRAENV in DOCKER.containers['so-elastic-fleet-package-registry'].extra_env %}
|
||||||
- {{ XTRAENV }}
|
- {{ XTRAENV }}
|
||||||
{% endfor %}
|
{% endfor %}
|
||||||
{% endif %}
|
{% endif %}
|
||||||
{% if DOCKERMERGED.containers['so-elastic-fleet-package-registry'].ulimits %}
|
|
||||||
- ulimits:
|
|
||||||
{% for ULIMIT in DOCKERMERGED.containers['so-elastic-fleet-package-registry'].ulimits %}
|
|
||||||
- {{ ULIMIT.name }}={{ ULIMIT.soft }}:{{ ULIMIT.hard }}
|
|
||||||
{% endfor %}
|
|
||||||
{% endif %}
|
|
||||||
delete_so-elastic-fleet-package-registry_so-status.disabled:
|
delete_so-elastic-fleet-package-registry_so-status.disabled:
|
||||||
file.uncomment:
|
file.uncomment:
|
||||||
- name: /opt/so/conf/so-status/so-status.conf
|
- name: /opt/so/conf/so-status/so-status.conf
|
||||||
|
|||||||
@@ -6,10 +6,9 @@
|
|||||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
{% from 'allowed_states.map.jinja' import allowed_states %}
|
||||||
{% if sls.split('.')[0] in allowed_states %}
|
{% if sls.split('.')[0] in allowed_states %}
|
||||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||||
{% from 'docker/docker.map.jinja' import DOCKERMERGED %}
|
{% from 'docker/docker.map.jinja' import DOCKER %}
|
||||||
|
|
||||||
include:
|
include:
|
||||||
- ca
|
|
||||||
- elasticagent.config
|
- elasticagent.config
|
||||||
- elasticagent.sostatus
|
- elasticagent.sostatus
|
||||||
|
|
||||||
@@ -22,17 +21,17 @@ so-elastic-agent:
|
|||||||
- user: 949
|
- user: 949
|
||||||
- networks:
|
- networks:
|
||||||
- sobridge:
|
- sobridge:
|
||||||
- ipv4_address: {{ DOCKERMERGED.containers['so-elastic-agent'].ip }}
|
- ipv4_address: {{ DOCKER.containers['so-elastic-agent'].ip }}
|
||||||
- extra_hosts:
|
- extra_hosts:
|
||||||
- {{ GLOBALS.manager }}:{{ GLOBALS.manager_ip }}
|
- {{ GLOBALS.manager }}:{{ GLOBALS.manager_ip }}
|
||||||
- {{ GLOBALS.hostname }}:{{ GLOBALS.node_ip }}
|
- {{ GLOBALS.hostname }}:{{ GLOBALS.node_ip }}
|
||||||
{% if DOCKERMERGED.containers['so-elastic-agent'].extra_hosts %}
|
{% if DOCKER.containers['so-elastic-agent'].extra_hosts %}
|
||||||
{% for XTRAHOST in DOCKERMERGED.containers['so-elastic-agent'].extra_hosts %}
|
{% for XTRAHOST in DOCKER.containers['so-elastic-agent'].extra_hosts %}
|
||||||
- {{ XTRAHOST }}
|
- {{ XTRAHOST }}
|
||||||
{% endfor %}
|
{% endfor %}
|
||||||
{% endif %}
|
{% endif %}
|
||||||
- port_bindings:
|
- port_bindings:
|
||||||
{% for BINDING in DOCKERMERGED.containers['so-elastic-agent'].port_bindings %}
|
{% for BINDING in DOCKER.containers['so-elastic-agent'].port_bindings %}
|
||||||
- {{ BINDING }}
|
- {{ BINDING }}
|
||||||
{% endfor %}
|
{% endfor %}
|
||||||
- binds:
|
- binds:
|
||||||
@@ -41,31 +40,23 @@ so-elastic-agent:
|
|||||||
- /etc/pki/tls/certs/intca.crt:/etc/pki/tls/certs/intca.crt:ro
|
- /etc/pki/tls/certs/intca.crt:/etc/pki/tls/certs/intca.crt:ro
|
||||||
- /nsm:/nsm:ro
|
- /nsm:/nsm:ro
|
||||||
- /opt/so/log:/opt/so/log:ro
|
- /opt/so/log:/opt/so/log:ro
|
||||||
{% if DOCKERMERGED.containers['so-elastic-agent'].custom_bind_mounts %}
|
{% if DOCKER.containers['so-elastic-agent'].custom_bind_mounts %}
|
||||||
{% for BIND in DOCKERMERGED.containers['so-elastic-agent'].custom_bind_mounts %}
|
{% for BIND in DOCKER.containers['so-elastic-agent'].custom_bind_mounts %}
|
||||||
- {{ BIND }}
|
- {{ BIND }}
|
||||||
{% endfor %}
|
{% endfor %}
|
||||||
{% endif %}
|
{% endif %}
|
||||||
- environment:
|
- environment:
|
||||||
- FLEET_CA=/etc/pki/tls/certs/intca.crt
|
- FLEET_CA=/etc/pki/tls/certs/intca.crt
|
||||||
- LOGS_PATH=logs
|
- LOGS_PATH=logs
|
||||||
{% if DOCKERMERGED.containers['so-elastic-agent'].extra_env %}
|
{% if DOCKER.containers['so-elastic-agent'].extra_env %}
|
||||||
{% for XTRAENV in DOCKERMERGED.containers['so-elastic-agent'].extra_env %}
|
{% for XTRAENV in DOCKER.containers['so-elastic-agent'].extra_env %}
|
||||||
- {{ XTRAENV }}
|
- {{ XTRAENV }}
|
||||||
{% endfor %}
|
{% endfor %}
|
||||||
{% endif %}
|
{% endif %}
|
||||||
{% if DOCKERMERGED.containers['so-elastic-agent'].ulimits %}
|
|
||||||
- ulimits:
|
|
||||||
{% for ULIMIT in DOCKERMERGED.containers['so-elastic-agent'].ulimits %}
|
|
||||||
- {{ ULIMIT.name }}={{ ULIMIT.soft }}:{{ ULIMIT.hard }}
|
|
||||||
{% endfor %}
|
|
||||||
{% endif %}
|
|
||||||
- require:
|
- require:
|
||||||
- file: create-elastic-agent-config
|
- file: create-elastic-agent-config
|
||||||
- file: trusttheca
|
|
||||||
- watch:
|
- watch:
|
||||||
- file: create-elastic-agent-config
|
- file: create-elastic-agent-config
|
||||||
- file: trusttheca
|
|
||||||
|
|
||||||
delete_so-elastic-agent_so-status.disabled:
|
delete_so-elastic-agent_so-status.disabled:
|
||||||
file.uncomment:
|
file.uncomment:
|
||||||
|
|||||||
@@ -3,7 +3,7 @@
|
|||||||
{%- set ES_PASS = salt['pillar.get']('elasticsearch:auth:users:so_elastic_user:pass', '') %}
|
{%- set ES_PASS = salt['pillar.get']('elasticsearch:auth:users:so_elastic_user:pass', '') %}
|
||||||
|
|
||||||
id: aea1ba80-1065-11ee-a369-97538913b6a9
|
id: aea1ba80-1065-11ee-a369-97538913b6a9
|
||||||
revision: 4
|
revision: 1
|
||||||
outputs:
|
outputs:
|
||||||
default:
|
default:
|
||||||
type: elasticsearch
|
type: elasticsearch
|
||||||
@@ -22,133 +22,242 @@ agent:
|
|||||||
metrics: false
|
metrics: false
|
||||||
features: {}
|
features: {}
|
||||||
inputs:
|
inputs:
|
||||||
- id: filestream-filestream-85820eb0-25ef-11f0-a18d-1b26f69b8310
|
- id: logfile-logs-fefef78c-422f-4cfa-8abf-4cd1b9428f62
|
||||||
name: import-suricata-logs
|
name: import-evtx-logs
|
||||||
revision: 3
|
revision: 2
|
||||||
type: filestream
|
type: logfile
|
||||||
use_output: default
|
use_output: default
|
||||||
meta:
|
meta:
|
||||||
package:
|
package:
|
||||||
name: filestream
|
name: log
|
||||||
version:
|
version:
|
||||||
data_stream:
|
data_stream:
|
||||||
namespace: so
|
namespace: so
|
||||||
package_policy_id: 85820eb0-25ef-11f0-a18d-1b26f69b8310
|
package_policy_id: fefef78c-422f-4cfa-8abf-4cd1b9428f62
|
||||||
streams:
|
streams:
|
||||||
- id: filestream-filestream.generic-85820eb0-25ef-11f0-a18d-1b26f69b8310
|
- id: logfile-log.log-fefef78c-422f-4cfa-8abf-4cd1b9428f62
|
||||||
data_stream:
|
data_stream:
|
||||||
dataset: import
|
dataset: import
|
||||||
paths:
|
paths:
|
||||||
- /nsm/import/*/suricata/eve*.json
|
- /nsm/import/*/evtx/*.json
|
||||||
pipeline: suricata.common
|
|
||||||
prospector.scanner.recursive_glob: true
|
|
||||||
prospector.scanner.exclude_files:
|
|
||||||
- \.gz$
|
|
||||||
ignore_older: 72h
|
|
||||||
clean_inactive: -1
|
|
||||||
parsers: null
|
|
||||||
processors:
|
|
||||||
- add_fields:
|
|
||||||
target: event
|
|
||||||
fields:
|
|
||||||
category: network
|
|
||||||
module: suricata
|
|
||||||
imported: true
|
|
||||||
- dissect:
|
|
||||||
tokenizer: /nsm/import/%{import.id}/suricata/%{import.file}
|
|
||||||
field: log.file.path
|
|
||||||
target_prefix: ''
|
|
||||||
file_identity.native: null
|
|
||||||
prospector.scanner.fingerprint.enabled: false
|
|
||||||
- id: filestream-filestream-86b4e960-25ef-11f0-a18d-1b26f69b8310
|
|
||||||
name: import-zeek-logs
|
|
||||||
revision: 3
|
|
||||||
type: filestream
|
|
||||||
use_output: default
|
|
||||||
meta:
|
|
||||||
package:
|
|
||||||
name: filestream
|
|
||||||
version:
|
|
||||||
data_stream:
|
|
||||||
namespace: so
|
|
||||||
package_policy_id: 86b4e960-25ef-11f0-a18d-1b26f69b8310
|
|
||||||
streams:
|
|
||||||
- id: filestream-filestream.generic-86b4e960-25ef-11f0-a18d-1b26f69b8310
|
|
||||||
data_stream:
|
|
||||||
dataset: import
|
|
||||||
paths:
|
|
||||||
- /nsm/import/*/zeek/logs/*.log
|
|
||||||
prospector.scanner.recursive_glob: true
|
|
||||||
prospector.scanner.exclude_files:
|
|
||||||
- >-
|
|
||||||
(broker|capture_loss|cluster|conn-summary|console|ecat_arp_info|known_certs|known_hosts|known_services|loaded_scripts|ntp|ocsp|packet_filter|reporter|stats|stderr|stdout).log$
|
|
||||||
clean_inactive: -1
|
|
||||||
parsers: null
|
|
||||||
processors:
|
processors:
|
||||||
- dissect:
|
- dissect:
|
||||||
tokenizer: /nsm/import/%{import.id}/zeek/logs/%{import.file}
|
|
||||||
field: log.file.path
|
field: log.file.path
|
||||||
|
tokenizer: '/nsm/import/%{import.id}/evtx/%{import.file}'
|
||||||
target_prefix: ''
|
target_prefix: ''
|
||||||
- script:
|
|
||||||
lang: javascript
|
|
||||||
source: |
|
|
||||||
function process(event) {
|
|
||||||
var pl = event.Get("import.file").slice(0,-4);
|
|
||||||
event.Put("@metadata.pipeline", "zeek." + pl);
|
|
||||||
}
|
|
||||||
- add_fields:
|
|
||||||
target: event
|
|
||||||
fields:
|
|
||||||
category: network
|
|
||||||
module: zeek
|
|
||||||
imported: true
|
|
||||||
- add_tags:
|
|
||||||
tags: ics
|
|
||||||
when:
|
|
||||||
regexp:
|
|
||||||
import.file: >-
|
|
||||||
^bacnet*|^bsap*|^cip*|^cotp*|^dnp3*|^ecat*|^enip*|^modbus*|^opcua*|^profinet*|^s7comm*
|
|
||||||
file_identity.native: null
|
|
||||||
prospector.scanner.fingerprint.enabled: false
|
|
||||||
- id: filestream-filestream-91741240-25ef-11f0-a18d-1b26f69b8310
|
|
||||||
name: soc-sensoroni-logs
|
|
||||||
revision: 3
|
|
||||||
type: filestream
|
|
||||||
use_output: default
|
|
||||||
meta:
|
|
||||||
package:
|
|
||||||
name: filestream
|
|
||||||
version:
|
|
||||||
data_stream:
|
|
||||||
namespace: so
|
|
||||||
package_policy_id: 91741240-25ef-11f0-a18d-1b26f69b8310
|
|
||||||
streams:
|
|
||||||
- id: filestream-filestream.generic-91741240-25ef-11f0-a18d-1b26f69b8310
|
|
||||||
data_stream:
|
|
||||||
dataset: soc
|
|
||||||
paths:
|
|
||||||
- /opt/so/log/sensoroni/sensoroni.log
|
|
||||||
pipeline: common
|
|
||||||
prospector.scanner.recursive_glob: true
|
|
||||||
prospector.scanner.exclude_files:
|
|
||||||
- \.gz$
|
|
||||||
clean_inactive: -1
|
|
||||||
parsers: null
|
|
||||||
processors:
|
|
||||||
- decode_json_fields:
|
- decode_json_fields:
|
||||||
fields:
|
fields:
|
||||||
- message
|
- message
|
||||||
target: sensoroni
|
target: ''
|
||||||
|
- drop_fields:
|
||||||
|
ignore_missing: true
|
||||||
|
fields:
|
||||||
|
- host
|
||||||
|
- add_fields:
|
||||||
|
fields:
|
||||||
|
dataset: system.security
|
||||||
|
type: logs
|
||||||
|
namespace: default
|
||||||
|
target: data_stream
|
||||||
|
- add_fields:
|
||||||
|
fields:
|
||||||
|
dataset: system.security
|
||||||
|
module: system
|
||||||
|
imported: true
|
||||||
|
target: event
|
||||||
|
- then:
|
||||||
|
- add_fields:
|
||||||
|
fields:
|
||||||
|
dataset: windows.sysmon_operational
|
||||||
|
target: data_stream
|
||||||
|
- add_fields:
|
||||||
|
fields:
|
||||||
|
dataset: windows.sysmon_operational
|
||||||
|
module: windows
|
||||||
|
imported: true
|
||||||
|
target: event
|
||||||
|
if:
|
||||||
|
equals:
|
||||||
|
winlog.channel: Microsoft-Windows-Sysmon/Operational
|
||||||
|
- then:
|
||||||
|
- add_fields:
|
||||||
|
fields:
|
||||||
|
dataset: system.application
|
||||||
|
target: data_stream
|
||||||
|
- add_fields:
|
||||||
|
fields:
|
||||||
|
dataset: system.application
|
||||||
|
target: event
|
||||||
|
if:
|
||||||
|
equals:
|
||||||
|
winlog.channel: Application
|
||||||
|
- then:
|
||||||
|
- add_fields:
|
||||||
|
fields:
|
||||||
|
dataset: system.system
|
||||||
|
target: data_stream
|
||||||
|
- add_fields:
|
||||||
|
fields:
|
||||||
|
dataset: system.system
|
||||||
|
target: event
|
||||||
|
if:
|
||||||
|
equals:
|
||||||
|
winlog.channel: System
|
||||||
|
- then:
|
||||||
|
- add_fields:
|
||||||
|
fields:
|
||||||
|
dataset: windows.powershell_operational
|
||||||
|
target: data_stream
|
||||||
|
- add_fields:
|
||||||
|
fields:
|
||||||
|
dataset: windows.powershell_operational
|
||||||
|
module: windows
|
||||||
|
target: event
|
||||||
|
if:
|
||||||
|
equals:
|
||||||
|
winlog.channel: Microsoft-Windows-PowerShell/Operational
|
||||||
|
tags:
|
||||||
|
- import
|
||||||
|
- id: logfile-redis-fc98c947-7d17-4861-a318-7ad075f6d1b0
|
||||||
|
name: redis-logs
|
||||||
|
revision: 2
|
||||||
|
type: logfile
|
||||||
|
use_output: default
|
||||||
|
meta:
|
||||||
|
package:
|
||||||
|
name: redis
|
||||||
|
version:
|
||||||
|
data_stream:
|
||||||
|
namespace: default
|
||||||
|
package_policy_id: fc98c947-7d17-4861-a318-7ad075f6d1b0
|
||||||
|
streams:
|
||||||
|
- id: logfile-redis.log-fc98c947-7d17-4861-a318-7ad075f6d1b0
|
||||||
|
data_stream:
|
||||||
|
dataset: redis.log
|
||||||
|
type: logs
|
||||||
|
exclude_files:
|
||||||
|
- .gz$
|
||||||
|
paths:
|
||||||
|
- /opt/so/log/redis/redis.log
|
||||||
|
tags:
|
||||||
|
- redis-log
|
||||||
|
exclude_lines:
|
||||||
|
- '^\s+[\-`(''.|_]'
|
||||||
|
- id: logfile-logs-3b56803d-5ade-4c93-b25e-9b37182f66b8
|
||||||
|
name: import-suricata-logs
|
||||||
|
revision: 2
|
||||||
|
type: logfile
|
||||||
|
use_output: default
|
||||||
|
meta:
|
||||||
|
package:
|
||||||
|
name: log
|
||||||
|
version:
|
||||||
|
data_stream:
|
||||||
|
namespace: so
|
||||||
|
package_policy_id: 3b56803d-5ade-4c93-b25e-9b37182f66b8
|
||||||
|
streams:
|
||||||
|
- id: logfile-log.log-3b56803d-5ade-4c93-b25e-9b37182f66b8
|
||||||
|
data_stream:
|
||||||
|
dataset: import
|
||||||
|
pipeline: suricata.common
|
||||||
|
paths:
|
||||||
|
- /nsm/import/*/suricata/eve*.json
|
||||||
|
processors:
|
||||||
|
- add_fields:
|
||||||
|
fields:
|
||||||
|
module: suricata
|
||||||
|
imported: true
|
||||||
|
category: network
|
||||||
|
target: event
|
||||||
|
- dissect:
|
||||||
|
field: log.file.path
|
||||||
|
tokenizer: '/nsm/import/%{import.id}/suricata/%{import.file}'
|
||||||
|
target_prefix: ''
|
||||||
|
- id: logfile-logs-c327e1a3-1ebe-449c-a8eb-f6f35032e69d
|
||||||
|
name: soc-server-logs
|
||||||
|
revision: 2
|
||||||
|
type: logfile
|
||||||
|
use_output: default
|
||||||
|
meta:
|
||||||
|
package:
|
||||||
|
name: log
|
||||||
|
version:
|
||||||
|
data_stream:
|
||||||
|
namespace: so
|
||||||
|
package_policy_id: c327e1a3-1ebe-449c-a8eb-f6f35032e69d
|
||||||
|
streams:
|
||||||
|
- id: logfile-log.log-c327e1a3-1ebe-449c-a8eb-f6f35032e69d
|
||||||
|
data_stream:
|
||||||
|
dataset: soc
|
||||||
|
pipeline: common
|
||||||
|
paths:
|
||||||
|
- /opt/so/log/soc/sensoroni-server.log
|
||||||
|
processors:
|
||||||
|
- decode_json_fields:
|
||||||
|
add_error_key: true
|
||||||
process_array: true
|
process_array: true
|
||||||
max_depth: 2
|
max_depth: 2
|
||||||
add_error_key: true
|
|
||||||
- add_fields:
|
|
||||||
target: event
|
|
||||||
fields:
|
fields:
|
||||||
|
- message
|
||||||
|
target: soc
|
||||||
|
- add_fields:
|
||||||
|
fields:
|
||||||
|
module: soc
|
||||||
|
dataset_temp: server
|
||||||
category: host
|
category: host
|
||||||
|
target: event
|
||||||
|
- rename:
|
||||||
|
ignore_missing: true
|
||||||
|
fields:
|
||||||
|
- from: soc.fields.sourceIp
|
||||||
|
to: source.ip
|
||||||
|
- from: soc.fields.status
|
||||||
|
to: http.response.status_code
|
||||||
|
- from: soc.fields.method
|
||||||
|
to: http.request.method
|
||||||
|
- from: soc.fields.path
|
||||||
|
to: url.path
|
||||||
|
- from: soc.message
|
||||||
|
to: event.action
|
||||||
|
- from: soc.level
|
||||||
|
to: log.level
|
||||||
|
tags:
|
||||||
|
- so-soc
|
||||||
|
- id: logfile-logs-906e0d4c-9ec3-4c6a-bef6-e347ec9fd073
|
||||||
|
name: soc-sensoroni-logs
|
||||||
|
revision: 2
|
||||||
|
type: logfile
|
||||||
|
use_output: default
|
||||||
|
meta:
|
||||||
|
package:
|
||||||
|
name: log
|
||||||
|
version:
|
||||||
|
data_stream:
|
||||||
|
namespace: so
|
||||||
|
package_policy_id: 906e0d4c-9ec3-4c6a-bef6-e347ec9fd073
|
||||||
|
streams:
|
||||||
|
- id: logfile-log.log-906e0d4c-9ec3-4c6a-bef6-e347ec9fd073
|
||||||
|
data_stream:
|
||||||
|
dataset: soc
|
||||||
|
pipeline: common
|
||||||
|
paths:
|
||||||
|
- /opt/so/log/sensoroni/sensoroni.log
|
||||||
|
processors:
|
||||||
|
- decode_json_fields:
|
||||||
|
add_error_key: true
|
||||||
|
process_array: true
|
||||||
|
max_depth: 2
|
||||||
|
fields:
|
||||||
|
- message
|
||||||
|
target: sensoroni
|
||||||
|
- add_fields:
|
||||||
|
fields:
|
||||||
module: soc
|
module: soc
|
||||||
dataset_temp: sensoroni
|
dataset_temp: sensoroni
|
||||||
|
category: host
|
||||||
|
target: event
|
||||||
- rename:
|
- rename:
|
||||||
|
ignore_missing: true
|
||||||
fields:
|
fields:
|
||||||
- from: sensoroni.fields.sourceIp
|
- from: sensoroni.fields.sourceIp
|
||||||
to: source.ip
|
to: source.ip
|
||||||
@@ -162,100 +271,141 @@ inputs:
|
|||||||
to: event.action
|
to: event.action
|
||||||
- from: sensoroni.level
|
- from: sensoroni.level
|
||||||
to: log.level
|
to: log.level
|
||||||
ignore_missing: true
|
- id: logfile-logs-df0d7f2c-221f-433b-b18b-d1cf83250515
|
||||||
file_identity.native: null
|
name: soc-salt-relay-logs
|
||||||
prospector.scanner.fingerprint.enabled: false
|
revision: 2
|
||||||
- id: filestream-filestream-976e3900-25ef-11f0-a18d-1b26f69b8310
|
type: logfile
|
||||||
name: suricata-logs
|
|
||||||
revision: 3
|
|
||||||
type: filestream
|
|
||||||
use_output: default
|
use_output: default
|
||||||
meta:
|
meta:
|
||||||
package:
|
package:
|
||||||
name: filestream
|
name: log
|
||||||
version:
|
version:
|
||||||
data_stream:
|
data_stream:
|
||||||
namespace: so
|
namespace: so
|
||||||
package_policy_id: 976e3900-25ef-11f0-a18d-1b26f69b8310
|
package_policy_id: df0d7f2c-221f-433b-b18b-d1cf83250515
|
||||||
streams:
|
streams:
|
||||||
- id: filestream-filestream.generic-976e3900-25ef-11f0-a18d-1b26f69b8310
|
- id: logfile-log.log-df0d7f2c-221f-433b-b18b-d1cf83250515
|
||||||
|
data_stream:
|
||||||
|
dataset: soc
|
||||||
|
pipeline: common
|
||||||
|
paths:
|
||||||
|
- /opt/so/log/soc/salt-relay.log
|
||||||
|
processors:
|
||||||
|
- dissect:
|
||||||
|
field: message
|
||||||
|
tokenizer: '%{soc.ts} | %{event.action}'
|
||||||
|
target_prefix: ''
|
||||||
|
- add_fields:
|
||||||
|
fields:
|
||||||
|
module: soc
|
||||||
|
dataset_temp: salt_relay
|
||||||
|
category: host
|
||||||
|
target: event
|
||||||
|
tags:
|
||||||
|
- so-soc
|
||||||
|
- id: logfile-logs-74bd2366-fe52-493c-bddc-843a017fc4d0
|
||||||
|
name: soc-auth-sync-logs
|
||||||
|
revision: 2
|
||||||
|
type: logfile
|
||||||
|
use_output: default
|
||||||
|
meta:
|
||||||
|
package:
|
||||||
|
name: log
|
||||||
|
version:
|
||||||
|
data_stream:
|
||||||
|
namespace: so
|
||||||
|
package_policy_id: 74bd2366-fe52-493c-bddc-843a017fc4d0
|
||||||
|
streams:
|
||||||
|
- id: logfile-log.log-74bd2366-fe52-493c-bddc-843a017fc4d0
|
||||||
|
data_stream:
|
||||||
|
dataset: soc
|
||||||
|
pipeline: common
|
||||||
|
paths:
|
||||||
|
- /opt/so/log/soc/sync.log
|
||||||
|
processors:
|
||||||
|
- dissect:
|
||||||
|
field: message
|
||||||
|
tokenizer: '%{event.action}'
|
||||||
|
target_prefix: ''
|
||||||
|
- add_fields:
|
||||||
|
fields:
|
||||||
|
module: soc
|
||||||
|
dataset_temp: auth_sync
|
||||||
|
category: host
|
||||||
|
target: event
|
||||||
|
tags:
|
||||||
|
- so-soc
|
||||||
|
- id: logfile-logs-d151d9bf-ff2a-4529-9520-c99244bc0253
|
||||||
|
name: suricata-logs
|
||||||
|
revision: 2
|
||||||
|
type: logfile
|
||||||
|
use_output: default
|
||||||
|
meta:
|
||||||
|
package:
|
||||||
|
name: log
|
||||||
|
version:
|
||||||
|
data_stream:
|
||||||
|
namespace: so
|
||||||
|
package_policy_id: d151d9bf-ff2a-4529-9520-c99244bc0253
|
||||||
|
streams:
|
||||||
|
- id: logfile-log.log-d151d9bf-ff2a-4529-9520-c99244bc0253
|
||||||
data_stream:
|
data_stream:
|
||||||
dataset: suricata
|
dataset: suricata
|
||||||
|
pipeline: suricata.common
|
||||||
paths:
|
paths:
|
||||||
- /nsm/suricata/eve*.json
|
- /nsm/suricata/eve*.json
|
||||||
pipeline: suricata.common
|
|
||||||
prospector.scanner.recursive_glob: true
|
|
||||||
prospector.scanner.exclude_files:
|
|
||||||
- \.gz$
|
|
||||||
clean_inactive: -1
|
|
||||||
parsers: null
|
|
||||||
processors:
|
processors:
|
||||||
- add_fields:
|
- add_fields:
|
||||||
target: event
|
|
||||||
fields:
|
fields:
|
||||||
category: network
|
|
||||||
module: suricata
|
module: suricata
|
||||||
file_identity.native: null
|
category: network
|
||||||
prospector.scanner.fingerprint.enabled: false
|
target: event
|
||||||
- id: filestream-filestream-95091fe0-25ef-11f0-a18d-1b26f69b8310
|
- id: logfile-logs-31f94d05-ae75-40ee-b9c5-0e0356eff327
|
||||||
name: strelka-logs
|
name: strelka-logs
|
||||||
revision: 3
|
revision: 2
|
||||||
type: filestream
|
type: logfile
|
||||||
use_output: default
|
use_output: default
|
||||||
meta:
|
meta:
|
||||||
package:
|
package:
|
||||||
name: filestream
|
name: log
|
||||||
version:
|
version:
|
||||||
data_stream:
|
data_stream:
|
||||||
namespace: so
|
namespace: so
|
||||||
package_policy_id: 95091fe0-25ef-11f0-a18d-1b26f69b8310
|
package_policy_id: 31f94d05-ae75-40ee-b9c5-0e0356eff327
|
||||||
streams:
|
streams:
|
||||||
- id: filestream-filestream.generic-95091fe0-25ef-11f0-a18d-1b26f69b8310
|
- id: logfile-log.log-31f94d05-ae75-40ee-b9c5-0e0356eff327
|
||||||
data_stream:
|
data_stream:
|
||||||
dataset: strelka
|
dataset: strelka
|
||||||
|
pipeline: strelka.file
|
||||||
paths:
|
paths:
|
||||||
- /nsm/strelka/log/strelka.log
|
- /nsm/strelka/log/strelka.log
|
||||||
pipeline: strelka.file
|
|
||||||
prospector.scanner.recursive_glob: true
|
|
||||||
prospector.scanner.exclude_files:
|
|
||||||
- \.gz$
|
|
||||||
clean_inactive: -1
|
|
||||||
parsers: null
|
|
||||||
processors:
|
processors:
|
||||||
- add_fields:
|
- add_fields:
|
||||||
target: event
|
|
||||||
fields:
|
fields:
|
||||||
category: file
|
|
||||||
module: strelka
|
module: strelka
|
||||||
file_identity.native: null
|
category: file
|
||||||
prospector.scanner.fingerprint.enabled: false
|
target: event
|
||||||
- id: filestream-filestream-9f309ca0-25ef-11f0-a18d-1b26f69b8310
|
- id: logfile-logs-6197fe84-9b58-4d9b-8464-3d517f28808d
|
||||||
name: zeek-logs
|
name: zeek-logs
|
||||||
revision: 2
|
revision: 1
|
||||||
type: filestream
|
type: logfile
|
||||||
use_output: default
|
use_output: default
|
||||||
meta:
|
meta:
|
||||||
package:
|
package:
|
||||||
name: filestream
|
name: log
|
||||||
version:
|
version:
|
||||||
data_stream:
|
data_stream:
|
||||||
namespace: so
|
namespace: so
|
||||||
package_policy_id: 9f309ca0-25ef-11f0-a18d-1b26f69b8310
|
package_policy_id: 6197fe84-9b58-4d9b-8464-3d517f28808d
|
||||||
streams:
|
streams:
|
||||||
- id: filestream-filestream.generic-9f309ca0-25ef-11f0-a18d-1b26f69b8310
|
- id: logfile-log.log-6197fe84-9b58-4d9b-8464-3d517f28808d
|
||||||
data_stream:
|
data_stream:
|
||||||
dataset: zeek
|
dataset: zeek
|
||||||
paths:
|
paths:
|
||||||
- /nsm/zeek/logs/current/*.log
|
- /nsm/zeek/logs/current/*.log
|
||||||
prospector.scanner.recursive_glob: true
|
|
||||||
prospector.scanner.exclude_files:
|
|
||||||
- >-
|
|
||||||
(broker|capture_loss|cluster|conn-summary|console|ecat_arp_info|known_certs|known_hosts|known_services|loaded_scripts|ntp|ocsp|packet_filter|reporter|stats|stderr|stdout).log$
|
|
||||||
clean_inactive: -1
|
|
||||||
parsers: null
|
|
||||||
processors:
|
processors:
|
||||||
- dissect:
|
- dissect:
|
||||||
tokenizer: /nsm/zeek/logs/current/%{pipeline}.log
|
tokenizer: '/nsm/zeek/logs/current/%{pipeline}.log'
|
||||||
field: log.file.path
|
field: log.file.path
|
||||||
trim_chars: .log
|
trim_chars: .log
|
||||||
target_prefix: ''
|
target_prefix: ''
|
||||||
@@ -277,17 +427,18 @@ inputs:
|
|||||||
regexp:
|
regexp:
|
||||||
pipeline: >-
|
pipeline: >-
|
||||||
^bacnet*|^bsap*|^cip*|^cotp*|^dnp3*|^ecat*|^enip*|^modbus*|^opcua*|^profinet*|^s7comm*
|
^bacnet*|^bsap*|^cip*|^cotp*|^dnp3*|^ecat*|^enip*|^modbus*|^opcua*|^profinet*|^s7comm*
|
||||||
file_identity.native: null
|
exclude_files:
|
||||||
prospector.scanner.fingerprint.enabled: false
|
- >-
|
||||||
|
broker|capture_loss|cluster|ecat_arp_info|known_hosts|known_services|loaded_scripts|ntp|ocsp|packet_filter|reporter|stats|stderr|stdout.log$
|
||||||
- id: udp-udp-35051de0-46a5-11ee-8d5d-9f98c8182f60
|
- id: udp-udp-35051de0-46a5-11ee-8d5d-9f98c8182f60
|
||||||
name: syslog-udp-514
|
name: syslog-udp-514
|
||||||
revision: 4
|
revision: 3
|
||||||
type: udp
|
type: udp
|
||||||
use_output: default
|
use_output: default
|
||||||
meta:
|
meta:
|
||||||
package:
|
package:
|
||||||
name: udp
|
name: udp
|
||||||
version:
|
version: 1.10.0
|
||||||
data_stream:
|
data_stream:
|
||||||
namespace: so
|
namespace: so
|
||||||
package_policy_id: 35051de0-46a5-11ee-8d5d-9f98c8182f60
|
package_policy_id: 35051de0-46a5-11ee-8d5d-9f98c8182f60
|
||||||
@@ -307,13 +458,13 @@ inputs:
|
|||||||
- syslog
|
- syslog
|
||||||
- id: tcp-tcp-33d37bb0-46a5-11ee-8d5d-9f98c8182f60
|
- id: tcp-tcp-33d37bb0-46a5-11ee-8d5d-9f98c8182f60
|
||||||
name: syslog-tcp-514
|
name: syslog-tcp-514
|
||||||
revision: 4
|
revision: 3
|
||||||
type: tcp
|
type: tcp
|
||||||
use_output: default
|
use_output: default
|
||||||
meta:
|
meta:
|
||||||
package:
|
package:
|
||||||
name: tcp
|
name: tcp
|
||||||
version:
|
version: 1.10.0
|
||||||
data_stream:
|
data_stream:
|
||||||
namespace: so
|
namespace: so
|
||||||
package_policy_id: 33d37bb0-46a5-11ee-8d5d-9f98c8182f60
|
package_policy_id: 33d37bb0-46a5-11ee-8d5d-9f98c8182f60
|
||||||
|
|||||||
@@ -11,7 +11,6 @@
|
|||||||
|
|
||||||
include:
|
include:
|
||||||
- elasticfleet.artifact_registry
|
- elasticfleet.artifact_registry
|
||||||
- elasticfleet.ssl
|
|
||||||
|
|
||||||
# Add EA Group
|
# Add EA Group
|
||||||
elasticfleetgroup:
|
elasticfleetgroup:
|
||||||
@@ -96,9 +95,6 @@ soresourcesrepoclone:
|
|||||||
- rev: 'main'
|
- rev: 'main'
|
||||||
- depth: 1
|
- depth: 1
|
||||||
- force_reset: True
|
- force_reset: True
|
||||||
- retry:
|
|
||||||
attempts: 3
|
|
||||||
interval: 10
|
|
||||||
{% endif %}
|
{% endif %}
|
||||||
|
|
||||||
elasticdefendconfdir:
|
elasticdefendconfdir:
|
||||||
|
|||||||
@@ -6,17 +6,16 @@
|
|||||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
{% from 'allowed_states.map.jinja' import allowed_states %}
|
||||||
{% if sls.split('.')[0] in allowed_states %}
|
{% if sls.split('.')[0] in allowed_states %}
|
||||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||||
{% from 'docker/docker.map.jinja' import DOCKERMERGED %}
|
{% from 'docker/docker.map.jinja' import DOCKER %}
|
||||||
{% from 'elasticfleet/map.jinja' import ELASTICFLEETMERGED %}
|
{% from 'elasticfleet/map.jinja' import ELASTICFLEETMERGED %}
|
||||||
|
|
||||||
{# This value is generated during node install and stored in minion pillar #}
|
{# This value is generated during node install and stored in minion pillar #}
|
||||||
{% set SERVICETOKEN = salt['pillar.get']('elasticfleet:config:server:es_token','') %}
|
{% set SERVICETOKEN = salt['pillar.get']('elasticfleet:config:server:es_token','') %}
|
||||||
|
|
||||||
include:
|
include:
|
||||||
- ca
|
|
||||||
- logstash.ssl
|
|
||||||
- elasticfleet.config
|
- elasticfleet.config
|
||||||
- elasticfleet.sostatus
|
- elasticfleet.sostatus
|
||||||
|
- ssl
|
||||||
|
|
||||||
{% if grains.role not in ['so-fleet'] %}
|
{% if grains.role not in ['so-fleet'] %}
|
||||||
# Wait for Elasticsearch to be ready - no reason to try running Elastic Fleet server if ES is not ready
|
# Wait for Elasticsearch to be ready - no reason to try running Elastic Fleet server if ES is not ready
|
||||||
@@ -94,17 +93,17 @@ so-elastic-fleet:
|
|||||||
- user: 947
|
- user: 947
|
||||||
- networks:
|
- networks:
|
||||||
- sobridge:
|
- sobridge:
|
||||||
- ipv4_address: {{ DOCKERMERGED.containers['so-elastic-fleet'].ip }}
|
- ipv4_address: {{ DOCKER.containers['so-elastic-fleet'].ip }}
|
||||||
- extra_hosts:
|
- extra_hosts:
|
||||||
- {{ GLOBALS.manager }}:{{ GLOBALS.manager_ip }}
|
- {{ GLOBALS.manager }}:{{ GLOBALS.manager_ip }}
|
||||||
- {{ GLOBALS.hostname }}:{{ GLOBALS.node_ip }}
|
- {{ GLOBALS.hostname }}:{{ GLOBALS.node_ip }}
|
||||||
{% if DOCKERMERGED.containers['so-elastic-fleet'].extra_hosts %}
|
{% if DOCKER.containers['so-elastic-fleet'].extra_hosts %}
|
||||||
{% for XTRAHOST in DOCKERMERGED.containers['so-elastic-fleet'].extra_hosts %}
|
{% for XTRAHOST in DOCKER.containers['so-elastic-fleet'].extra_hosts %}
|
||||||
- {{ XTRAHOST }}
|
- {{ XTRAHOST }}
|
||||||
{% endfor %}
|
{% endfor %}
|
||||||
{% endif %}
|
{% endif %}
|
||||||
- port_bindings:
|
- port_bindings:
|
||||||
{% for BINDING in DOCKERMERGED.containers['so-elastic-fleet'].port_bindings %}
|
{% for BINDING in DOCKER.containers['so-elastic-fleet'].port_bindings %}
|
||||||
- {{ BINDING }}
|
- {{ BINDING }}
|
||||||
{% endfor %}
|
{% endfor %}
|
||||||
- binds:
|
- binds:
|
||||||
@@ -112,8 +111,8 @@ so-elastic-fleet:
|
|||||||
- /etc/pki/elasticfleet-server.key:/etc/pki/elasticfleet-server.key:ro
|
- /etc/pki/elasticfleet-server.key:/etc/pki/elasticfleet-server.key:ro
|
||||||
- /etc/pki/tls/certs/intca.crt:/etc/pki/tls/certs/intca.crt:ro
|
- /etc/pki/tls/certs/intca.crt:/etc/pki/tls/certs/intca.crt:ro
|
||||||
- /opt/so/log/elasticfleet:/usr/share/elastic-agent/logs
|
- /opt/so/log/elasticfleet:/usr/share/elastic-agent/logs
|
||||||
{% if DOCKERMERGED.containers['so-elastic-fleet'].custom_bind_mounts %}
|
{% if DOCKER.containers['so-elastic-fleet'].custom_bind_mounts %}
|
||||||
{% for BIND in DOCKERMERGED.containers['so-elastic-fleet'].custom_bind_mounts %}
|
{% for BIND in DOCKER.containers['so-elastic-fleet'].custom_bind_mounts %}
|
||||||
- {{ BIND }}
|
- {{ BIND }}
|
||||||
{% endfor %}
|
{% endfor %}
|
||||||
{% endif %}
|
{% endif %}
|
||||||
@@ -128,23 +127,12 @@ so-elastic-fleet:
|
|||||||
- FLEET_CA=/etc/pki/tls/certs/intca.crt
|
- FLEET_CA=/etc/pki/tls/certs/intca.crt
|
||||||
- FLEET_SERVER_ELASTICSEARCH_CA=/etc/pki/tls/certs/intca.crt
|
- FLEET_SERVER_ELASTICSEARCH_CA=/etc/pki/tls/certs/intca.crt
|
||||||
- LOGS_PATH=logs
|
- LOGS_PATH=logs
|
||||||
{% if DOCKERMERGED.containers['so-elastic-fleet'].extra_env %}
|
{% if DOCKER.containers['so-elastic-fleet'].extra_env %}
|
||||||
{% for XTRAENV in DOCKERMERGED.containers['so-elastic-fleet'].extra_env %}
|
{% for XTRAENV in DOCKER.containers['so-elastic-fleet'].extra_env %}
|
||||||
- {{ XTRAENV }}
|
- {{ XTRAENV }}
|
||||||
{% endfor %}
|
{% endfor %}
|
||||||
{% endif %}
|
{% endif %}
|
||||||
{% if DOCKERMERGED.containers['so-elastic-fleet'].ulimits %}
|
|
||||||
- ulimits:
|
|
||||||
{% for ULIMIT in DOCKERMERGED.containers['so-elastic-fleet'].ulimits %}
|
|
||||||
- {{ ULIMIT.name }}={{ ULIMIT.soft }}:{{ ULIMIT.hard }}
|
|
||||||
{% endfor %}
|
|
||||||
{% endif %}
|
|
||||||
- watch:
|
- watch:
|
||||||
- file: trusttheca
|
|
||||||
- x509: etc_elasticfleet_key
|
|
||||||
- x509: etc_elasticfleet_crt
|
|
||||||
- require:
|
|
||||||
- file: trusttheca
|
|
||||||
- x509: etc_elasticfleet_key
|
- x509: etc_elasticfleet_key
|
||||||
- x509: etc_elasticfleet_crt
|
- x509: etc_elasticfleet_crt
|
||||||
{% endif %}
|
{% endif %}
|
||||||
|
|||||||
@@ -2,7 +2,7 @@
|
|||||||
{%- raw -%}
|
{%- raw -%}
|
||||||
{
|
{
|
||||||
"package": {
|
"package": {
|
||||||
"name": "filestream",
|
"name": "log",
|
||||||
"version": ""
|
"version": ""
|
||||||
},
|
},
|
||||||
"name": "import-zeek-logs",
|
"name": "import-zeek-logs",
|
||||||
@@ -10,31 +10,19 @@
|
|||||||
"description": "Zeek Import logs",
|
"description": "Zeek Import logs",
|
||||||
"policy_id": "so-grid-nodes_general",
|
"policy_id": "so-grid-nodes_general",
|
||||||
"inputs": {
|
"inputs": {
|
||||||
"filestream-filestream": {
|
"logs-logfile": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"streams": {
|
"streams": {
|
||||||
"filestream.generic": {
|
"log.logs": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"vars": {
|
"vars": {
|
||||||
"paths": [
|
"paths": [
|
||||||
"/nsm/import/*/zeek/logs/*.log"
|
"/nsm/import/*/zeek/logs/*.log"
|
||||||
],
|
],
|
||||||
"data_stream.dataset": "import",
|
"data_stream.dataset": "import",
|
||||||
"pipeline": "",
|
|
||||||
"parsers": "#- ndjson:\n# target: \"\"\n# message_key: msg\n#- multiline:\n# type: count\n# count_lines: 3\n",
|
|
||||||
"exclude_files": ["({%- endraw -%}{{ ELASTICFLEETMERGED.logging.zeek.excluded | join('|') }}{%- raw -%})(\\..+)?\\.log$"],
|
|
||||||
"include_files": [],
|
|
||||||
"processors": "- dissect:\n tokenizer: \"/nsm/import/%{import.id}/zeek/logs/%{import.file}\"\n field: \"log.file.path\"\n target_prefix: \"\"\n- script:\n lang: javascript\n source: >\n function process(event) {\n var pl = event.Get(\"import.file\").slice(0,-4);\n event.Put(\"@metadata.pipeline\", \"zeek.\" + pl);\n }\n- add_fields:\n target: event\n fields:\n category: network\n module: zeek\n imported: true\n- add_tags:\n tags: \"ics\"\n when:\n regexp:\n import.file: \"^bacnet*|^bsap*|^cip*|^cotp*|^dnp3*|^ecat*|^enip*|^modbus*|^opcua*|^profinet*|^s7comm*\"",
|
|
||||||
"tags": [],
|
"tags": [],
|
||||||
"recursive_glob": true,
|
"processors": "- dissect:\n tokenizer: \"/nsm/import/%{import.id}/zeek/logs/%{import.file}\"\n field: \"log.file.path\"\n target_prefix: \"\"\n- script:\n lang: javascript\n source: >\n function process(event) {\n var pl = event.Get(\"import.file\").slice(0,-4);\n event.Put(\"@metadata.pipeline\", \"zeek.\" + pl);\n }\n- add_fields:\n target: event\n fields:\n category: network\n module: zeek\n imported: true\n- add_tags:\n tags: \"ics\"\n when:\n regexp:\n import.file: \"^bacnet*|^bsap*|^cip*|^cotp*|^dnp3*|^ecat*|^enip*|^modbus*|^opcua*|^profinet*|^s7comm*\"",
|
||||||
"clean_inactive": -1,
|
"custom": "exclude_files: [\"{%- endraw -%}{{ ELASTICFLEETMERGED.logging.zeek.excluded | join('|') }}{%- raw -%}.log$\"]\n"
|
||||||
"harvester_limit": 0,
|
|
||||||
"fingerprint": false,
|
|
||||||
"fingerprint_offset": 0,
|
|
||||||
"fingerprint_length": "64",
|
|
||||||
"file_identity_native": true,
|
|
||||||
"exclude_lines": [],
|
|
||||||
"include_lines": []
|
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
|
|||||||
@@ -11,51 +11,36 @@
|
|||||||
{%- endif -%}
|
{%- endif -%}
|
||||||
{
|
{
|
||||||
"package": {
|
"package": {
|
||||||
"name": "filestream",
|
"name": "log",
|
||||||
"version": ""
|
"version": ""
|
||||||
},
|
},
|
||||||
"name": "kratos-logs",
|
"name": "kratos-logs",
|
||||||
|
"namespace": "so",
|
||||||
"description": "Kratos logs",
|
"description": "Kratos logs",
|
||||||
"policy_id": "so-grid-nodes_general",
|
"policy_id": "so-grid-nodes_general",
|
||||||
"namespace": "so",
|
|
||||||
"inputs": {
|
"inputs": {
|
||||||
"filestream-filestream": {
|
"logs-logfile": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"streams": {
|
"streams": {
|
||||||
"filestream.generic": {
|
"log.logs": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"vars": {
|
"vars": {
|
||||||
"paths": [
|
"paths": [
|
||||||
"/opt/so/log/kratos/kratos.log"
|
"/opt/so/log/kratos/kratos.log"
|
||||||
],
|
],
|
||||||
"data_stream.dataset": "kratos",
|
"data_stream.dataset": "kratos",
|
||||||
"pipeline": "kratos",
|
"tags": ["so-kratos"],
|
||||||
"parsers": "#- ndjson:\n# target: \"\"\n# message_key: msg\n#- multiline:\n# type: count\n# count_lines: 3\n",
|
|
||||||
"exclude_files": [
|
|
||||||
"\\.gz$"
|
|
||||||
],
|
|
||||||
"include_files": [],
|
|
||||||
{%- if valid_identities -%}
|
{%- if valid_identities -%}
|
||||||
"processors": "- decode_json_fields:\n fields: [\"message\"]\n target: \"\"\n add_error_key: true\n- add_fields:\n target: event\n fields:\n category: iam\n module: kratos\n- if:\n has_fields:\n - identity_id\n then:{% for id, email in identities %}\n - if:\n equals:\n identity_id: \"{{ id }}\"\n then:\n - add_fields:\n target: ''\n fields:\n user.name: \"{{ email }}\"{% endfor %}",
|
"processors": "- decode_json_fields:\n fields: [\"message\"]\n target: \"\"\n add_error_key: true\n- add_fields:\n target: event\n fields:\n category: iam\n module: kratos\n- if:\n has_fields:\n - identity_id\n then:{% for id, email in identities %}\n - if:\n equals:\n identity_id: \"{{ id }}\"\n then:\n - add_fields:\n target: ''\n fields:\n user.name: \"{{ email }}\"{% endfor %}",
|
||||||
{%- else -%}
|
{%- else -%}
|
||||||
"processors": "- decode_json_fields:\n fields: [\"message\"]\n target: \"\"\n add_error_key: true\n- add_fields:\n target: event\n fields:\n category: iam\n module: kratos",
|
"processors": "- decode_json_fields:\n fields: [\"message\"]\n target: \"\"\n add_error_key: true\n- add_fields:\n target: event\n fields:\n category: iam\n module: kratos",
|
||||||
{%- endif -%}
|
{%- endif -%}
|
||||||
"tags": [
|
"custom": "pipeline: kratos"
|
||||||
"so-kratos"
|
|
||||||
],
|
|
||||||
"recursive_glob": true,
|
|
||||||
"clean_inactive": -1,
|
|
||||||
"harvester_limit": 0,
|
|
||||||
"fingerprint": false,
|
|
||||||
"fingerprint_offset": 0,
|
|
||||||
"fingerprint_length": "64",
|
|
||||||
"file_identity_native": true,
|
|
||||||
"exclude_lines": [],
|
|
||||||
"include_lines": []
|
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
},
|
},
|
||||||
"force": true
|
"force": true
|
||||||
}
|
}
|
||||||
|
|
||||||
|
|||||||
@@ -2,38 +2,28 @@
|
|||||||
{%- raw -%}
|
{%- raw -%}
|
||||||
{
|
{
|
||||||
"package": {
|
"package": {
|
||||||
"name": "filestream",
|
"name": "log",
|
||||||
"version": ""
|
"version": ""
|
||||||
},
|
},
|
||||||
|
"id": "zeek-logs",
|
||||||
"name": "zeek-logs",
|
"name": "zeek-logs",
|
||||||
"namespace": "so",
|
"namespace": "so",
|
||||||
"description": "Zeek logs",
|
"description": "Zeek logs",
|
||||||
"policy_id": "so-grid-nodes_general",
|
"policy_id": "so-grid-nodes_general",
|
||||||
"inputs": {
|
"inputs": {
|
||||||
"filestream-filestream": {
|
"logs-logfile": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"streams": {
|
"streams": {
|
||||||
"filestream.generic": {
|
"log.logs": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"vars": {
|
"vars": {
|
||||||
"paths": [
|
"paths": [
|
||||||
"/nsm/zeek/logs/current/*.log"
|
"/nsm/zeek/logs/current/*.log"
|
||||||
],
|
],
|
||||||
"data_stream.dataset": "zeek",
|
"data_stream.dataset": "zeek",
|
||||||
"parsers": "#- ndjson:\n# target: \"\"\n# message_key: msg\n#- multiline:\n# type: count\n# count_lines: 3\n",
|
|
||||||
"exclude_files": ["({%- endraw -%}{{ ELASTICFLEETMERGED.logging.zeek.excluded | join('|') }}{%- raw -%})(\\..+)?\\.log$"],
|
|
||||||
"include_files": [],
|
|
||||||
"processors": "- dissect:\n tokenizer: \"/nsm/zeek/logs/current/%{pipeline}.log\"\n field: \"log.file.path\"\n trim_chars: \".log\"\n target_prefix: \"\"\n- script:\n lang: javascript\n source: >\n function process(event) {\n var pl = event.Get(\"pipeline\");\n event.Put(\"@metadata.pipeline\", \"zeek.\" + pl);\n }\n- add_fields:\n target: event\n fields:\n category: network\n module: zeek\n- add_tags:\n tags: \"ics\"\n when:\n regexp:\n pipeline: \"^bacnet*|^bsap*|^cip*|^cotp*|^dnp3*|^ecat*|^enip*|^modbus*|^opcua*|^profinet*|^s7comm*\"",
|
|
||||||
"tags": [],
|
"tags": [],
|
||||||
"recursive_glob": true,
|
"processors": "- dissect:\n tokenizer: \"/nsm/zeek/logs/current/%{pipeline}.log\"\n field: \"log.file.path\"\n trim_chars: \".log\"\n target_prefix: \"\"\n- script:\n lang: javascript\n source: >\n function process(event) {\n var pl = event.Get(\"pipeline\");\n event.Put(\"@metadata.pipeline\", \"zeek.\" + pl);\n }\n- add_fields:\n target: event\n fields:\n category: network\n module: zeek\n- add_tags:\n tags: \"ics\"\n when:\n regexp:\n pipeline: \"^bacnet*|^bsap*|^cip*|^cotp*|^dnp3*|^ecat*|^enip*|^modbus*|^opcua*|^profinet*|^s7comm*\"",
|
||||||
"clean_inactive": -1,
|
"custom": "exclude_files: [\"{%- endraw -%}{{ ELASTICFLEETMERGED.logging.zeek.excluded | join('|') }}{%- raw -%}.log$\"]\n"
|
||||||
"harvester_limit": 0,
|
|
||||||
"fingerprint": false,
|
|
||||||
"fingerprint_offset": 0,
|
|
||||||
"fingerprint_length": "64",
|
|
||||||
"file_identity_native": true,
|
|
||||||
"exclude_lines": [],
|
|
||||||
"include_lines": []
|
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
@@ -41,4 +31,4 @@
|
|||||||
},
|
},
|
||||||
"force": true
|
"force": true
|
||||||
}
|
}
|
||||||
{%- endraw -%}
|
{%- endraw -%}
|
||||||
|
|||||||
@@ -5,7 +5,7 @@
|
|||||||
"package": {
|
"package": {
|
||||||
"name": "endpoint",
|
"name": "endpoint",
|
||||||
"title": "Elastic Defend",
|
"title": "Elastic Defend",
|
||||||
"version": "9.0.2",
|
"version": "8.18.1",
|
||||||
"requires_root": true
|
"requires_root": true
|
||||||
},
|
},
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
|
|||||||
@@ -1,43 +1,26 @@
|
|||||||
{
|
{
|
||||||
"package": {
|
"package": {
|
||||||
"name": "filestream",
|
"name": "log",
|
||||||
"version": ""
|
"version": ""
|
||||||
},
|
},
|
||||||
"name": "hydra-logs",
|
"name": "hydra-logs",
|
||||||
|
"namespace": "so",
|
||||||
"description": "Hydra logs",
|
"description": "Hydra logs",
|
||||||
"policy_id": "so-grid-nodes_general",
|
"policy_id": "so-grid-nodes_general",
|
||||||
"namespace": "so",
|
|
||||||
"inputs": {
|
"inputs": {
|
||||||
"filestream-filestream": {
|
"logs-logfile": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"streams": {
|
"streams": {
|
||||||
"filestream.generic": {
|
"log.logs": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"vars": {
|
"vars": {
|
||||||
"paths": [
|
"paths": [
|
||||||
"/opt/so/log/hydra/hydra.log"
|
"/opt/so/log/hydra/hydra.log"
|
||||||
],
|
],
|
||||||
"data_stream.dataset": "hydra",
|
"data_stream.dataset": "hydra",
|
||||||
"pipeline": "hydra",
|
"tags": ["so-hydra"],
|
||||||
"parsers": "#- ndjson:\n# target: \"\"\n# message_key: msg\n#- multiline:\n# type: count\n# count_lines: 3\n",
|
"processors": "- decode_json_fields:\n fields: [\"message\"]\n target: \"\"\n add_error_key: true \n- add_fields:\n target: event\n fields:\n category: iam\n module: hydra",
|
||||||
"exclude_files": [
|
"custom": "pipeline: hydra"
|
||||||
"\\.gz$"
|
|
||||||
],
|
|
||||||
"include_files": [],
|
|
||||||
"processors": "- decode_json_fields:\n fields: [\"message\"]\n target: \"\"\n add_error_key: true\n- add_fields:\n target: event\n fields:\n category: iam\n module: hydra",
|
|
||||||
"tags": [
|
|
||||||
"so-hydra"
|
|
||||||
],
|
|
||||||
"recursive_glob": true,
|
|
||||||
"ignore_older": "72h",
|
|
||||||
"clean_inactive": -1,
|
|
||||||
"harvester_limit": 0,
|
|
||||||
"fingerprint": false,
|
|
||||||
"fingerprint_offset": 0,
|
|
||||||
"fingerprint_length": "64",
|
|
||||||
"file_identity_native": true,
|
|
||||||
"exclude_lines": [],
|
|
||||||
"include_lines": []
|
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
@@ -45,5 +28,3 @@
|
|||||||
},
|
},
|
||||||
"force": true
|
"force": true
|
||||||
}
|
}
|
||||||
|
|
||||||
|
|
||||||
|
|||||||
@@ -1,44 +1,30 @@
|
|||||||
{
|
{
|
||||||
"package": {
|
"package": {
|
||||||
"name": "filestream",
|
"name": "log",
|
||||||
"version": ""
|
"version": ""
|
||||||
},
|
},
|
||||||
"name": "idh-logs",
|
"name": "idh-logs",
|
||||||
|
"namespace": "so",
|
||||||
"description": "IDH integration",
|
"description": "IDH integration",
|
||||||
"policy_id": "so-grid-nodes_general",
|
"policy_id": "so-grid-nodes_general",
|
||||||
"namespace": "so",
|
|
||||||
"inputs": {
|
"inputs": {
|
||||||
"filestream-filestream": {
|
"logs-logfile": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"streams": {
|
"streams": {
|
||||||
"filestream.generic": {
|
"log.logs": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"vars": {
|
"vars": {
|
||||||
"paths": [
|
"paths": [
|
||||||
"/nsm/idh/opencanary.log"
|
"/nsm/idh/opencanary.log"
|
||||||
],
|
],
|
||||||
"data_stream.dataset": "idh",
|
"data_stream.dataset": "idh",
|
||||||
"pipeline": "common",
|
|
||||||
"parsers": "#- ndjson:\n# target: \"\"\n# message_key: msg\n#- multiline:\n# type: count\n# count_lines: 3\n",
|
|
||||||
"exclude_files": [
|
|
||||||
"\\.gz$"
|
|
||||||
],
|
|
||||||
"include_files": [],
|
|
||||||
"processors": "\n- decode_json_fields:\n fields: [\"message\"]\n target: \"\"\n add_error_key: true\n- convert:\n fields:\n - {from: \"logtype\", to: \"event.code\", type: \"string\"}\n- drop_fields:\n when:\n equals:\n event.code: \"1001\"\n fields: [\"src_host\", \"src_port\", \"dst_host\", \"dst_port\" ]\n ignore_missing: true\n- rename:\n fields:\n - from: \"src_host\"\n to: \"source.ip\"\n - from: \"src_port\"\n to: \"source.port\"\n - from: \"dst_host\"\n to: \"destination.host\"\n - from: \"dst_port\"\n to: \"destination.port\"\n ignore_missing: true\n- drop_fields:\n fields: '[\"prospector\", \"input\", \"offset\", \"beat\"]'\n- add_fields:\n target: event\n fields:\n category: host\n module: opencanary",
|
|
||||||
"tags": [],
|
"tags": [],
|
||||||
"recursive_glob": true,
|
"processors": "\n- decode_json_fields:\n fields: [\"message\"]\n target: \"\"\n add_error_key: true\n- convert:\n fields:\n - {from: \"logtype\", to: \"event.code\", type: \"string\"}\n- drop_fields:\n when:\n equals:\n event.code: \"1001\"\n fields: [\"src_host\", \"src_port\", \"dst_host\", \"dst_port\" ]\n ignore_missing: true\n- rename:\n fields:\n - from: \"src_host\"\n to: \"source.ip\"\n - from: \"src_port\"\n to: \"source.port\"\n - from: \"dst_host\"\n to: \"destination.host\"\n - from: \"dst_port\"\n to: \"destination.port\"\n ignore_missing: true\n- drop_fields:\n fields: '[\"prospector\", \"input\", \"offset\", \"beat\"]'\n- add_fields:\n target: event\n fields:\n category: host\n module: opencanary",
|
||||||
"clean_inactive": -1,
|
"custom": "pipeline: common"
|
||||||
"harvester_limit": 0,
|
|
||||||
"fingerprint": false,
|
|
||||||
"fingerprint_offset": 0,
|
|
||||||
"fingerprint_length": "64",
|
|
||||||
"file_identity_native": true,
|
|
||||||
"exclude_lines": [],
|
|
||||||
"include_lines": []
|
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
},
|
},
|
||||||
"force": true
|
"force": true
|
||||||
}
|
}
|
||||||
|
|||||||
@@ -1,46 +1,33 @@
|
|||||||
{
|
{
|
||||||
"package": {
|
"package": {
|
||||||
"name": "filestream",
|
"name": "log",
|
||||||
"version": ""
|
"version": ""
|
||||||
},
|
},
|
||||||
"name": "import-evtx-logs",
|
"name": "import-evtx-logs",
|
||||||
|
"namespace": "so",
|
||||||
"description": "Import Windows EVTX logs",
|
"description": "Import Windows EVTX logs",
|
||||||
"policy_id": "so-grid-nodes_general",
|
"policy_id": "so-grid-nodes_general",
|
||||||
"namespace": "so",
|
"vars": {},
|
||||||
"inputs": {
|
"inputs": {
|
||||||
"filestream-filestream": {
|
"logs-logfile": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"streams": {
|
"streams": {
|
||||||
"filestream.generic": {
|
"log.logs": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"vars": {
|
"vars": {
|
||||||
"paths": [
|
"paths": [
|
||||||
"/nsm/import/*/evtx/*.json"
|
"/nsm/import/*/evtx/*.json"
|
||||||
],
|
],
|
||||||
"data_stream.dataset": "import",
|
"data_stream.dataset": "import",
|
||||||
"parsers": "#- ndjson:\n# target: \"\"\n# message_key: msg\n#- multiline:\n# type: count\n# count_lines: 3\n",
|
"custom": "",
|
||||||
"exclude_files": [
|
|
||||||
"\\.gz$"
|
|
||||||
],
|
|
||||||
"include_files": [],
|
|
||||||
"processors": "- dissect:\n tokenizer: \"/nsm/import/%{import.id}/evtx/%{import.file}\"\n field: \"log.file.path\"\n target_prefix: \"\"\n- decode_json_fields:\n fields: [\"message\"]\n target: \"\"\n- drop_fields:\n fields: [\"host\"]\n ignore_missing: true\n- add_fields:\n target: data_stream\n fields:\n type: logs\n dataset: system.security\n- add_fields:\n target: event\n fields:\n dataset: system.security\n module: system\n imported: true\n- add_fields:\n target: \"@metadata\"\n fields:\n pipeline: logs-system.security-2.6.1\n- if:\n equals:\n winlog.channel: 'Microsoft-Windows-Sysmon/Operational'\n then: \n - add_fields:\n target: data_stream\n fields:\n dataset: windows.sysmon_operational\n - add_fields:\n target: event\n fields:\n dataset: windows.sysmon_operational\n module: windows\n imported: true\n - add_fields:\n target: \"@metadata\"\n fields:\n pipeline: logs-windows.sysmon_operational-3.1.2\n- if:\n equals:\n winlog.channel: 'Application'\n then: \n - add_fields:\n target: data_stream\n fields:\n dataset: system.application\n - add_fields:\n target: event\n fields:\n dataset: system.application\n - add_fields:\n target: \"@metadata\"\n fields:\n pipeline: logs-system.application-2.6.1\n- if:\n equals:\n winlog.channel: 'System'\n then: \n - add_fields:\n target: data_stream\n fields:\n dataset: system.system\n - add_fields:\n target: event\n fields:\n dataset: system.system\n - add_fields:\n target: \"@metadata\"\n fields:\n pipeline: logs-system.system-2.6.1\n \n- if:\n equals:\n winlog.channel: 'Microsoft-Windows-PowerShell/Operational'\n then: \n - add_fields:\n target: data_stream\n fields:\n dataset: windows.powershell_operational\n - add_fields:\n target: event\n fields:\n dataset: windows.powershell_operational\n module: windows\n - add_fields:\n target: \"@metadata\"\n fields:\n pipeline: logs-windows.powershell_operational-3.1.2\n- add_fields:\n target: data_stream\n fields:\n dataset: import",
|
"processors": "- dissect:\n tokenizer: \"/nsm/import/%{import.id}/evtx/%{import.file}\"\n field: \"log.file.path\"\n target_prefix: \"\"\n- decode_json_fields:\n fields: [\"message\"]\n target: \"\"\n- drop_fields:\n fields: [\"host\"]\n ignore_missing: true\n- add_fields:\n target: data_stream\n fields:\n type: logs\n dataset: system.security\n- add_fields:\n target: event\n fields:\n dataset: system.security\n module: system\n imported: true\n- add_fields:\n target: \"@metadata\"\n fields:\n pipeline: logs-system.security-2.6.1\n- if:\n equals:\n winlog.channel: 'Microsoft-Windows-Sysmon/Operational'\n then: \n - add_fields:\n target: data_stream\n fields:\n dataset: windows.sysmon_operational\n - add_fields:\n target: event\n fields:\n dataset: windows.sysmon_operational\n module: windows\n imported: true\n - add_fields:\n target: \"@metadata\"\n fields:\n pipeline: logs-windows.sysmon_operational-3.1.2\n- if:\n equals:\n winlog.channel: 'Application'\n then: \n - add_fields:\n target: data_stream\n fields:\n dataset: system.application\n - add_fields:\n target: event\n fields:\n dataset: system.application\n - add_fields:\n target: \"@metadata\"\n fields:\n pipeline: logs-system.application-2.6.1\n- if:\n equals:\n winlog.channel: 'System'\n then: \n - add_fields:\n target: data_stream\n fields:\n dataset: system.system\n - add_fields:\n target: event\n fields:\n dataset: system.system\n - add_fields:\n target: \"@metadata\"\n fields:\n pipeline: logs-system.system-2.6.1\n \n- if:\n equals:\n winlog.channel: 'Microsoft-Windows-PowerShell/Operational'\n then: \n - add_fields:\n target: data_stream\n fields:\n dataset: windows.powershell_operational\n - add_fields:\n target: event\n fields:\n dataset: windows.powershell_operational\n module: windows\n - add_fields:\n target: \"@metadata\"\n fields:\n pipeline: logs-windows.powershell_operational-3.1.2\n- add_fields:\n target: data_stream\n fields:\n dataset: import",
|
||||||
"tags": [
|
"tags": [
|
||||||
"import"
|
"import"
|
||||||
],
|
]
|
||||||
"recursive_glob": true,
|
|
||||||
"ignore_older": "72h",
|
|
||||||
"clean_inactive": -1,
|
|
||||||
"harvester_limit": 0,
|
|
||||||
"fingerprint": false,
|
|
||||||
"fingerprint_offset": 0,
|
|
||||||
"fingerprint_length": "64",
|
|
||||||
"file_identity_native": true,
|
|
||||||
"exclude_lines": [],
|
|
||||||
"include_lines": []
|
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
},
|
},
|
||||||
"force": true
|
"force": true
|
||||||
}
|
}
|
||||||
|
|||||||
@@ -1,45 +1,30 @@
|
|||||||
{
|
{
|
||||||
"package": {
|
"package": {
|
||||||
"name": "filestream",
|
"name": "log",
|
||||||
"version": ""
|
"version": ""
|
||||||
},
|
},
|
||||||
"name": "import-suricata-logs",
|
"name": "import-suricata-logs",
|
||||||
|
"namespace": "so",
|
||||||
"description": "Import Suricata logs",
|
"description": "Import Suricata logs",
|
||||||
"policy_id": "so-grid-nodes_general",
|
"policy_id": "so-grid-nodes_general",
|
||||||
"namespace": "so",
|
|
||||||
"inputs": {
|
"inputs": {
|
||||||
"filestream-filestream": {
|
"logs-logfile": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"streams": {
|
"streams": {
|
||||||
"filestream.generic": {
|
"log.logs": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"vars": {
|
"vars": {
|
||||||
"paths": [
|
"paths": [
|
||||||
"/nsm/import/*/suricata/eve*.json"
|
"/nsm/import/*/suricata/eve*.json"
|
||||||
],
|
],
|
||||||
"data_stream.dataset": "import",
|
"data_stream.dataset": "import",
|
||||||
"pipeline": "suricata.common",
|
|
||||||
"parsers": "#- ndjson:\n# target: \"\"\n# message_key: msg\n#- multiline:\n# type: count\n# count_lines: 3\n",
|
|
||||||
"exclude_files": [
|
|
||||||
"\\.gz$"
|
|
||||||
],
|
|
||||||
"include_files": [],
|
|
||||||
"processors": "- add_fields:\n target: event\n fields:\n category: network\n module: suricata\n imported: true\n- dissect:\n tokenizer: \"/nsm/import/%{import.id}/suricata/%{import.file}\"\n field: \"log.file.path\"\n target_prefix: \"\"\n",
|
|
||||||
"tags": [],
|
"tags": [],
|
||||||
"recursive_glob": true,
|
"processors": "- add_fields:\n target: event\n fields:\n category: network\n module: suricata\n imported: true\n- dissect:\n tokenizer: \"/nsm/import/%{import.id}/suricata/%{import.file}\"\n field: \"log.file.path\"\n target_prefix: \"\"",
|
||||||
"ignore_older": "72h",
|
"custom": "pipeline: suricata.common"
|
||||||
"clean_inactive": -1,
|
|
||||||
"harvester_limit": 0,
|
|
||||||
"fingerprint": false,
|
|
||||||
"fingerprint_offset": 0,
|
|
||||||
"fingerprint_length": "64",
|
|
||||||
"file_identity_native": true,
|
|
||||||
"exclude_lines": [],
|
|
||||||
"include_lines": []
|
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
},
|
},
|
||||||
"force": true
|
"force": true
|
||||||
}
|
}
|
||||||
|
|||||||
@@ -15,7 +15,7 @@
|
|||||||
"enabled": true,
|
"enabled": true,
|
||||||
"vars": {
|
"vars": {
|
||||||
"paths": [
|
"paths": [
|
||||||
"/opt/so/log/redis/redis-server.log"
|
"/opt/so/log/redis/redis.log"
|
||||||
],
|
],
|
||||||
"tags": [
|
"tags": [
|
||||||
"redis-log"
|
"redis-log"
|
||||||
|
|||||||
@@ -1,17 +1,18 @@
|
|||||||
{
|
{
|
||||||
"package": {
|
"package": {
|
||||||
"name": "filestream",
|
"name": "log",
|
||||||
"version": ""
|
"version": ""
|
||||||
},
|
},
|
||||||
"name": "rita-logs",
|
"name": "rita-logs",
|
||||||
|
"namespace": "so",
|
||||||
"description": "RITA Logs",
|
"description": "RITA Logs",
|
||||||
"policy_id": "so-grid-nodes_general",
|
"policy_id": "so-grid-nodes_general",
|
||||||
"namespace": "so",
|
"vars": {},
|
||||||
"inputs": {
|
"inputs": {
|
||||||
"filestream-filestream": {
|
"logs-logfile": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"streams": {
|
"streams": {
|
||||||
"filestream.generic": {
|
"log.logs": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"vars": {
|
"vars": {
|
||||||
"paths": [
|
"paths": [
|
||||||
@@ -19,28 +20,15 @@
|
|||||||
"/nsm/rita/exploded-dns.csv",
|
"/nsm/rita/exploded-dns.csv",
|
||||||
"/nsm/rita/long-connections.csv"
|
"/nsm/rita/long-connections.csv"
|
||||||
],
|
],
|
||||||
"data_stream.dataset": "rita",
|
"exclude_files": [],
|
||||||
"parsers": "#- ndjson:\n# target: \"\"\n# message_key: msg\n#- multiline:\n# type: count\n# count_lines: 3\n",
|
|
||||||
"exclude_files": [
|
|
||||||
"\\.gz$"
|
|
||||||
],
|
|
||||||
"include_files": [],
|
|
||||||
"processors": "- dissect:\n tokenizer: \"/nsm/rita/%{pipeline}.csv\"\n field: \"log.file.path\"\n trim_chars: \".csv\"\n target_prefix: \"\"\n- script:\n lang: javascript\n source: >\n function process(event) {\n var pl = event.Get(\"pipeline\").split(\"-\");\n if (pl.length > 1) {\n pl = pl[1];\n }\n else {\n pl = pl[0];\n }\n event.Put(\"@metadata.pipeline\", \"rita.\" + pl);\n }\n- add_fields:\n target: event\n fields:\n category: network\n module: rita",
|
|
||||||
"tags": [],
|
|
||||||
"recursive_glob": true,
|
|
||||||
"ignore_older": "72h",
|
"ignore_older": "72h",
|
||||||
"clean_inactive": -1,
|
"data_stream.dataset": "rita",
|
||||||
"harvester_limit": 0,
|
"tags": [],
|
||||||
"fingerprint": false,
|
"processors": "- dissect:\n tokenizer: \"/nsm/rita/%{pipeline}.csv\"\n field: \"log.file.path\"\n trim_chars: \".csv\"\n target_prefix: \"\"\n- script:\n lang: javascript\n source: >\n function process(event) {\n var pl = event.Get(\"pipeline\").split(\"-\");\n if (pl.length > 1) {\n pl = pl[1];\n }\n else {\n pl = pl[0];\n }\n event.Put(\"@metadata.pipeline\", \"rita.\" + pl);\n }\n- add_fields:\n target: event\n fields:\n category: network\n module: rita",
|
||||||
"fingerprint_offset": 0,
|
"custom": "exclude_lines: ['^Score', '^Source', '^Domain', '^No results']"
|
||||||
"fingerprint_length": "64",
|
|
||||||
"file_identity_native": true,
|
|
||||||
"exclude_lines": [],
|
|
||||||
"include_lines": []
|
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
},
|
}
|
||||||
"force": true
|
|
||||||
}
|
}
|
||||||
|
|||||||
@@ -1,41 +1,29 @@
|
|||||||
{
|
{
|
||||||
"package": {
|
"package": {
|
||||||
"name": "filestream",
|
"name": "log",
|
||||||
"version": ""
|
"version": ""
|
||||||
},
|
},
|
||||||
"name": "so-ip-mappings",
|
"name": "so-ip-mappings",
|
||||||
|
"namespace": "so",
|
||||||
"description": "IP Description mappings",
|
"description": "IP Description mappings",
|
||||||
"policy_id": "so-grid-nodes_general",
|
"policy_id": "so-grid-nodes_general",
|
||||||
"namespace": "so",
|
"vars": {},
|
||||||
"inputs": {
|
"inputs": {
|
||||||
"filestream-filestream": {
|
"logs-logfile": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"streams": {
|
"streams": {
|
||||||
"filestream.generic": {
|
"log.logs": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"vars": {
|
"vars": {
|
||||||
"paths": [
|
"paths": [
|
||||||
"/nsm/custom-mappings/ip-descriptions.csv"
|
"/nsm/custom-mappings/ip-descriptions.csv"
|
||||||
],
|
],
|
||||||
"data_stream.dataset": "hostnamemappings",
|
"data_stream.dataset": "hostnamemappings",
|
||||||
"parsers": "#- ndjson:\n# target: \"\"\n# message_key: msg\n#- multiline:\n# type: count\n# count_lines: 3\n",
|
|
||||||
"exclude_files": [
|
|
||||||
"\\.gz$"
|
|
||||||
],
|
|
||||||
"include_files": [],
|
|
||||||
"processors": "- decode_csv_fields:\n fields:\n message: decoded.csv\n separator: \",\"\n ignore_missing: false\n overwrite_keys: true\n trim_leading_space: true\n fail_on_error: true\n\n- extract_array:\n field: decoded.csv\n mappings:\n so.ip_address: '0'\n so.description: '1'\n\n- script:\n lang: javascript\n source: >\n function process(event) {\n var ip = event.Get('so.ip_address');\n var validIpRegex = /^((25[0-5]|2[0-4]\\d|1\\d{2}|[1-9]?\\d)\\.){3}(25[0-5]|2[0-4]\\d|1\\d{2}|[1-9]?\\d)$/\n if (!validIpRegex.test(ip)) {\n event.Cancel();\n }\n }\n- fingerprint:\n fields: [\"so.ip_address\"]\n target_field: \"@metadata._id\"\n",
|
|
||||||
"tags": [
|
"tags": [
|
||||||
"so-ip-mappings"
|
"so-ip-mappings"
|
||||||
],
|
],
|
||||||
"recursive_glob": true,
|
"processors": "- decode_csv_fields:\n fields:\n message: decoded.csv\n separator: \",\"\n ignore_missing: false\n overwrite_keys: true\n trim_leading_space: true\n fail_on_error: true\n\n- extract_array:\n field: decoded.csv\n mappings:\n so.ip_address: '0'\n so.description: '1'\n\n- script:\n lang: javascript\n source: >\n function process(event) {\n var ip = event.Get('so.ip_address');\n var validIpRegex = /^((25[0-5]|2[0-4]\\d|1\\d{2}|[1-9]?\\d)\\.){3}(25[0-5]|2[0-4]\\d|1\\d{2}|[1-9]?\\d)$/\n if (!validIpRegex.test(ip)) {\n event.Cancel();\n }\n }\n- fingerprint:\n fields: [\"so.ip_address\"]\n target_field: \"@metadata._id\"\n",
|
||||||
"clean_inactive": -1,
|
"custom": ""
|
||||||
"harvester_limit": 0,
|
|
||||||
"fingerprint": false,
|
|
||||||
"fingerprint_offset": 0,
|
|
||||||
"fingerprint_length": "64",
|
|
||||||
"file_identity_native": true,
|
|
||||||
"exclude_lines": [],
|
|
||||||
"include_lines": []
|
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
@@ -43,3 +31,5 @@
|
|||||||
},
|
},
|
||||||
"force": true
|
"force": true
|
||||||
}
|
}
|
||||||
|
|
||||||
|
|
||||||
|
|||||||
@@ -1,44 +1,30 @@
|
|||||||
{
|
{
|
||||||
"package": {
|
"package": {
|
||||||
"name": "filestream",
|
"name": "log",
|
||||||
"version": ""
|
"version": ""
|
||||||
},
|
},
|
||||||
"name": "soc-auth-sync-logs",
|
"name": "soc-auth-sync-logs",
|
||||||
|
"namespace": "so",
|
||||||
"description": "Security Onion - Elastic Auth Sync - Logs",
|
"description": "Security Onion - Elastic Auth Sync - Logs",
|
||||||
"policy_id": "so-grid-nodes_general",
|
"policy_id": "so-grid-nodes_general",
|
||||||
"namespace": "so",
|
|
||||||
"inputs": {
|
"inputs": {
|
||||||
"filestream-filestream": {
|
"logs-logfile": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"streams": {
|
"streams": {
|
||||||
"filestream.generic": {
|
"log.logs": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"vars": {
|
"vars": {
|
||||||
"paths": [
|
"paths": [
|
||||||
"/opt/so/log/soc/sync.log"
|
"/opt/so/log/soc/sync.log"
|
||||||
],
|
],
|
||||||
"data_stream.dataset": "soc",
|
"data_stream.dataset": "soc",
|
||||||
"pipeline": "common",
|
"tags": ["so-soc"],
|
||||||
"parsers": "#- ndjson:\n# target: \"\"\n# message_key: msg\n#- multiline:\n# type: count\n# count_lines: 3\n",
|
|
||||||
"exclude_files": [
|
|
||||||
"\\.gz$"
|
|
||||||
],
|
|
||||||
"include_files": [],
|
|
||||||
"processors": "- dissect:\n tokenizer: \"%{event.action}\"\n field: \"message\"\n target_prefix: \"\"\n- add_fields:\n target: event\n fields:\n category: host\n module: soc\n dataset_temp: auth_sync",
|
"processors": "- dissect:\n tokenizer: \"%{event.action}\"\n field: \"message\"\n target_prefix: \"\"\n- add_fields:\n target: event\n fields:\n category: host\n module: soc\n dataset_temp: auth_sync",
|
||||||
"tags": [],
|
"custom": "pipeline: common"
|
||||||
"recursive_glob": true,
|
|
||||||
"clean_inactive": -1,
|
|
||||||
"harvester_limit": 0,
|
|
||||||
"fingerprint": false,
|
|
||||||
"fingerprint_offset": 0,
|
|
||||||
"fingerprint_length": "64",
|
|
||||||
"file_identity_native": true,
|
|
||||||
"exclude_lines": [],
|
|
||||||
"include_lines": []
|
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
},
|
},
|
||||||
"force": true
|
"force": true
|
||||||
}
|
}
|
||||||
|
|||||||
@@ -1,48 +1,35 @@
|
|||||||
{
|
{
|
||||||
|
"policy_id": "so-grid-nodes_general",
|
||||||
"package": {
|
"package": {
|
||||||
"name": "filestream",
|
"name": "log",
|
||||||
"version": ""
|
"version": ""
|
||||||
},
|
},
|
||||||
"name": "soc-detections-logs",
|
"name": "soc-detections-logs",
|
||||||
"description": "Security Onion Console - Detections Logs",
|
"description": "Security Onion Console - Detections Logs",
|
||||||
"policy_id": "so-grid-nodes_general",
|
|
||||||
"namespace": "so",
|
"namespace": "so",
|
||||||
"inputs": {
|
"inputs": {
|
||||||
"filestream-filestream": {
|
"logs-logfile": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"streams": {
|
"streams": {
|
||||||
"filestream.generic": {
|
"log.logs": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"vars": {
|
"vars": {
|
||||||
"paths": [
|
"paths": [
|
||||||
"/opt/so/log/soc/detections_runtime-status_sigma.log",
|
"/opt/so/log/soc/detections_runtime-status_sigma.log",
|
||||||
"/opt/so/log/soc/detections_runtime-status_yara.log"
|
"/opt/so/log/soc/detections_runtime-status_yara.log"
|
||||||
],
|
],
|
||||||
|
"exclude_files": [],
|
||||||
|
"ignore_older": "72h",
|
||||||
"data_stream.dataset": "soc",
|
"data_stream.dataset": "soc",
|
||||||
"pipeline": "common",
|
|
||||||
"parsers": "#- ndjson:\n# target: \"\"\n# message_key: msg\n#- multiline:\n# type: count\n# count_lines: 3\n",
|
|
||||||
"exclude_files": [
|
|
||||||
"\\.gz$"
|
|
||||||
],
|
|
||||||
"include_files": [],
|
|
||||||
"processors": "- decode_json_fields:\n fields: [\"message\"]\n target: \"soc\"\n process_array: true\n max_depth: 2\n add_error_key: true \n- add_fields:\n target: event\n fields:\n category: host\n module: soc\n dataset_temp: detections\n- rename:\n fields:\n - from: \"soc.fields.sourceIp\"\n to: \"source.ip\"\n - from: \"soc.fields.status\"\n to: \"http.response.status_code\"\n - from: \"soc.fields.method\"\n to: \"http.request.method\"\n - from: \"soc.fields.path\"\n to: \"url.path\"\n - from: \"soc.message\"\n to: \"event.action\"\n - from: \"soc.level\"\n to: \"log.level\"\n ignore_missing: true",
|
|
||||||
"tags": [
|
"tags": [
|
||||||
"so-soc"
|
"so-soc"
|
||||||
],
|
],
|
||||||
"recursive_glob": true,
|
"processors": "- decode_json_fields:\n fields: [\"message\"]\n target: \"soc\"\n process_array: true\n max_depth: 2\n add_error_key: true \n- add_fields:\n target: event\n fields:\n category: host\n module: soc\n dataset_temp: detections\n- rename:\n fields:\n - from: \"soc.fields.sourceIp\"\n to: \"source.ip\"\n - from: \"soc.fields.status\"\n to: \"http.response.status_code\"\n - from: \"soc.fields.method\"\n to: \"http.request.method\"\n - from: \"soc.fields.path\"\n to: \"url.path\"\n - from: \"soc.message\"\n to: \"event.action\"\n - from: \"soc.level\"\n to: \"log.level\"\n ignore_missing: true",
|
||||||
"ignore_older": "72h",
|
"custom": "pipeline: common"
|
||||||
"clean_inactive": -1,
|
|
||||||
"harvester_limit": 0,
|
|
||||||
"fingerprint": false,
|
|
||||||
"fingerprint_offset": 0,
|
|
||||||
"fingerprint_length": "64",
|
|
||||||
"file_identity_native": true,
|
|
||||||
"exclude_lines": [],
|
|
||||||
"include_lines": []
|
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
},
|
},
|
||||||
"force": true
|
"force": true
|
||||||
}
|
}
|
||||||
|
|||||||
@@ -1,46 +1,30 @@
|
|||||||
{
|
{
|
||||||
"package": {
|
"package": {
|
||||||
"name": "filestream",
|
"name": "log",
|
||||||
"version": ""
|
"version": ""
|
||||||
},
|
},
|
||||||
"name": "soc-salt-relay-logs",
|
"name": "soc-salt-relay-logs",
|
||||||
|
"namespace": "so",
|
||||||
"description": "Security Onion - Salt Relay - Logs",
|
"description": "Security Onion - Salt Relay - Logs",
|
||||||
"policy_id": "so-grid-nodes_general",
|
"policy_id": "so-grid-nodes_general",
|
||||||
"namespace": "so",
|
|
||||||
"inputs": {
|
"inputs": {
|
||||||
"filestream-filestream": {
|
"logs-logfile": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"streams": {
|
"streams": {
|
||||||
"filestream.generic": {
|
"log.logs": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"vars": {
|
"vars": {
|
||||||
"paths": [
|
"paths": [
|
||||||
"/opt/so/log/soc/salt-relay.log"
|
"/opt/so/log/soc/salt-relay.log"
|
||||||
],
|
],
|
||||||
"data_stream.dataset": "soc",
|
"data_stream.dataset": "soc",
|
||||||
"pipeline": "common",
|
"tags": ["so-soc"],
|
||||||
"parsers": "#- ndjson:\n# target: \"\"\n# message_key: msg\n#- multiline:\n# type: count\n# count_lines: 3\n",
|
|
||||||
"exclude_files": [
|
|
||||||
"\\.gz$"
|
|
||||||
],
|
|
||||||
"include_files": [],
|
|
||||||
"processors": "- dissect:\n tokenizer: \"%{soc.ts} | %{event.action}\"\n field: \"message\"\n target_prefix: \"\"\n- add_fields:\n target: event\n fields:\n category: host\n module: soc\n dataset_temp: salt_relay",
|
"processors": "- dissect:\n tokenizer: \"%{soc.ts} | %{event.action}\"\n field: \"message\"\n target_prefix: \"\"\n- add_fields:\n target: event\n fields:\n category: host\n module: soc\n dataset_temp: salt_relay",
|
||||||
"tags": [
|
"custom": "pipeline: common"
|
||||||
"so-soc"
|
|
||||||
],
|
|
||||||
"recursive_glob": true,
|
|
||||||
"clean_inactive": -1,
|
|
||||||
"harvester_limit": 0,
|
|
||||||
"fingerprint": false,
|
|
||||||
"fingerprint_offset": 0,
|
|
||||||
"fingerprint_length": "64",
|
|
||||||
"file_identity_native": true,
|
|
||||||
"exclude_lines": [],
|
|
||||||
"include_lines": []
|
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
},
|
},
|
||||||
"force": true
|
"force": true
|
||||||
}
|
}
|
||||||
|
|||||||
@@ -1,44 +1,30 @@
|
|||||||
{
|
{
|
||||||
"package": {
|
"package": {
|
||||||
"name": "filestream",
|
"name": "log",
|
||||||
"version": ""
|
"version": ""
|
||||||
},
|
},
|
||||||
"name": "soc-sensoroni-logs",
|
"name": "soc-sensoroni-logs",
|
||||||
|
"namespace": "so",
|
||||||
"description": "Security Onion - Sensoroni - Logs",
|
"description": "Security Onion - Sensoroni - Logs",
|
||||||
"policy_id": "so-grid-nodes_general",
|
"policy_id": "so-grid-nodes_general",
|
||||||
"namespace": "so",
|
|
||||||
"inputs": {
|
"inputs": {
|
||||||
"filestream-filestream": {
|
"logs-logfile": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"streams": {
|
"streams": {
|
||||||
"filestream.generic": {
|
"log.logs": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"vars": {
|
"vars": {
|
||||||
"paths": [
|
"paths": [
|
||||||
"/opt/so/log/sensoroni/sensoroni.log"
|
"/opt/so/log/sensoroni/sensoroni.log"
|
||||||
],
|
],
|
||||||
"data_stream.dataset": "soc",
|
"data_stream.dataset": "soc",
|
||||||
"pipeline": "common",
|
|
||||||
"parsers": "#- ndjson:\n# target: \"\"\n# message_key: msg\n#- multiline:\n# type: count\n# count_lines: 3\n",
|
|
||||||
"exclude_files": [
|
|
||||||
"\\.gz$"
|
|
||||||
],
|
|
||||||
"include_files": [],
|
|
||||||
"processors": "- decode_json_fields:\n fields: [\"message\"]\n target: \"sensoroni\"\n process_array: true\n max_depth: 2\n add_error_key: true \n- add_fields:\n target: event\n fields:\n category: host\n module: soc\n dataset_temp: sensoroni\n- rename:\n fields:\n - from: \"sensoroni.fields.sourceIp\"\n to: \"source.ip\"\n - from: \"sensoroni.fields.status\"\n to: \"http.response.status_code\"\n - from: \"sensoroni.fields.method\"\n to: \"http.request.method\"\n - from: \"sensoroni.fields.path\"\n to: \"url.path\"\n - from: \"sensoroni.message\"\n to: \"event.action\"\n - from: \"sensoroni.level\"\n to: \"log.level\"\n ignore_missing: true",
|
|
||||||
"tags": [],
|
"tags": [],
|
||||||
"recursive_glob": true,
|
"processors": "- decode_json_fields:\n fields: [\"message\"]\n target: \"sensoroni\"\n process_array: true\n max_depth: 2\n add_error_key: true \n- add_fields:\n target: event\n fields:\n category: host\n module: soc\n dataset_temp: sensoroni\n- rename:\n fields:\n - from: \"sensoroni.fields.sourceIp\"\n to: \"source.ip\"\n - from: \"sensoroni.fields.status\"\n to: \"http.response.status_code\"\n - from: \"sensoroni.fields.method\"\n to: \"http.request.method\"\n - from: \"sensoroni.fields.path\"\n to: \"url.path\"\n - from: \"sensoroni.message\"\n to: \"event.action\"\n - from: \"sensoroni.level\"\n to: \"log.level\"\n ignore_missing: true",
|
||||||
"clean_inactive": -1,
|
"custom": "pipeline: common"
|
||||||
"harvester_limit": 0,
|
|
||||||
"fingerprint": false,
|
|
||||||
"fingerprint_offset": 0,
|
|
||||||
"fingerprint_length": "64",
|
|
||||||
"file_identity_native": true,
|
|
||||||
"exclude_lines": [],
|
|
||||||
"include_lines": []
|
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
},
|
},
|
||||||
"force": true
|
"force": true
|
||||||
}
|
}
|
||||||
|
|||||||
@@ -1,46 +1,30 @@
|
|||||||
{
|
{
|
||||||
"package": {
|
"package": {
|
||||||
"name": "filestream",
|
"name": "log",
|
||||||
"version": ""
|
"version": ""
|
||||||
},
|
},
|
||||||
"name": "soc-server-logs",
|
"name": "soc-server-logs",
|
||||||
|
"namespace": "so",
|
||||||
"description": "Security Onion Console Logs",
|
"description": "Security Onion Console Logs",
|
||||||
"policy_id": "so-grid-nodes_general",
|
"policy_id": "so-grid-nodes_general",
|
||||||
"namespace": "so",
|
|
||||||
"inputs": {
|
"inputs": {
|
||||||
"filestream-filestream": {
|
"logs-logfile": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"streams": {
|
"streams": {
|
||||||
"filestream.generic": {
|
"log.logs": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"vars": {
|
"vars": {
|
||||||
"paths": [
|
"paths": [
|
||||||
"/opt/so/log/soc/sensoroni-server.log"
|
"/opt/so/log/soc/sensoroni-server.log"
|
||||||
],
|
],
|
||||||
"data_stream.dataset": "soc",
|
"data_stream.dataset": "soc",
|
||||||
"pipeline": "common",
|
"tags": ["so-soc"],
|
||||||
"parsers": "#- ndjson:\n# target: \"\"\n# message_key: msg\n#- multiline:\n# type: count\n# count_lines: 3\n",
|
|
||||||
"exclude_files": [
|
|
||||||
"\\.gz$"
|
|
||||||
],
|
|
||||||
"include_files": [],
|
|
||||||
"processors": "- decode_json_fields:\n fields: [\"message\"]\n target: \"soc\"\n process_array: true\n max_depth: 2\n add_error_key: true \n- add_fields:\n target: event\n fields:\n category: host\n module: soc\n dataset_temp: server\n- rename:\n fields:\n - from: \"soc.fields.sourceIp\"\n to: \"source.ip\"\n - from: \"soc.fields.status\"\n to: \"http.response.status_code\"\n - from: \"soc.fields.method\"\n to: \"http.request.method\"\n - from: \"soc.fields.path\"\n to: \"url.path\"\n - from: \"soc.message\"\n to: \"event.action\"\n - from: \"soc.level\"\n to: \"log.level\"\n ignore_missing: true",
|
"processors": "- decode_json_fields:\n fields: [\"message\"]\n target: \"soc\"\n process_array: true\n max_depth: 2\n add_error_key: true \n- add_fields:\n target: event\n fields:\n category: host\n module: soc\n dataset_temp: server\n- rename:\n fields:\n - from: \"soc.fields.sourceIp\"\n to: \"source.ip\"\n - from: \"soc.fields.status\"\n to: \"http.response.status_code\"\n - from: \"soc.fields.method\"\n to: \"http.request.method\"\n - from: \"soc.fields.path\"\n to: \"url.path\"\n - from: \"soc.message\"\n to: \"event.action\"\n - from: \"soc.level\"\n to: \"log.level\"\n ignore_missing: true",
|
||||||
"tags": [
|
"custom": "pipeline: common"
|
||||||
"so-soc"
|
|
||||||
],
|
|
||||||
"recursive_glob": true,
|
|
||||||
"clean_inactive": -1,
|
|
||||||
"harvester_limit": 0,
|
|
||||||
"fingerprint": false,
|
|
||||||
"fingerprint_offset": 0,
|
|
||||||
"fingerprint_length": "64",
|
|
||||||
"file_identity_native": true,
|
|
||||||
"exclude_lines": [],
|
|
||||||
"include_lines": []
|
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
},
|
},
|
||||||
"force": true
|
"force": true
|
||||||
}
|
}
|
||||||
|
|||||||
@@ -1,44 +1,30 @@
|
|||||||
{
|
{
|
||||||
"package": {
|
"package": {
|
||||||
"name": "filestream",
|
"name": "log",
|
||||||
"version": ""
|
"version": ""
|
||||||
},
|
},
|
||||||
"name": "strelka-logs",
|
"name": "strelka-logs",
|
||||||
"description": "Strelka Logs",
|
|
||||||
"policy_id": "so-grid-nodes_general",
|
|
||||||
"namespace": "so",
|
"namespace": "so",
|
||||||
|
"description": "Strelka logs",
|
||||||
|
"policy_id": "so-grid-nodes_general",
|
||||||
"inputs": {
|
"inputs": {
|
||||||
"filestream-filestream": {
|
"logs-logfile": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"streams": {
|
"streams": {
|
||||||
"filestream.generic": {
|
"log.logs": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"vars": {
|
"vars": {
|
||||||
"paths": [
|
"paths": [
|
||||||
"/nsm/strelka/log/strelka.log"
|
"/nsm/strelka/log/strelka.log"
|
||||||
],
|
],
|
||||||
"data_stream.dataset": "strelka",
|
"data_stream.dataset": "strelka",
|
||||||
"pipeline": "strelka.file",
|
|
||||||
"parsers": "#- ndjson:\n# target: \"\"\n# message_key: msg\n#- multiline:\n# type: count\n# count_lines: 3\n",
|
|
||||||
"exclude_files": [
|
|
||||||
"\\.gz$"
|
|
||||||
],
|
|
||||||
"include_files": [],
|
|
||||||
"processors": "- add_fields:\n target: event\n fields:\n category: file\n module: strelka",
|
|
||||||
"tags": [],
|
"tags": [],
|
||||||
"recursive_glob": true,
|
"processors": "- add_fields:\n target: event\n fields:\n category: file\n module: strelka",
|
||||||
"clean_inactive": -1,
|
"custom": "pipeline: strelka.file"
|
||||||
"harvester_limit": 0,
|
|
||||||
"fingerprint": false,
|
|
||||||
"fingerprint_offset": 0,
|
|
||||||
"fingerprint_length": "64",
|
|
||||||
"file_identity_native": true,
|
|
||||||
"exclude_lines": [],
|
|
||||||
"include_lines": []
|
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
},
|
},
|
||||||
"force": true
|
"force": true
|
||||||
}
|
}
|
||||||
|
|||||||
@@ -1,40 +1,26 @@
|
|||||||
{
|
{
|
||||||
"package": {
|
"package": {
|
||||||
"name": "filestream",
|
"name": "log",
|
||||||
"version": ""
|
"version": ""
|
||||||
},
|
},
|
||||||
"name": "suricata-logs",
|
"name": "suricata-logs",
|
||||||
|
"namespace": "so",
|
||||||
"description": "Suricata integration",
|
"description": "Suricata integration",
|
||||||
"policy_id": "so-grid-nodes_general",
|
"policy_id": "so-grid-nodes_general",
|
||||||
"namespace": "so",
|
|
||||||
"inputs": {
|
"inputs": {
|
||||||
"filestream-filestream": {
|
"logs-logfile": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"streams": {
|
"streams": {
|
||||||
"filestream.generic": {
|
"log.logs": {
|
||||||
"enabled": true,
|
"enabled": true,
|
||||||
"vars": {
|
"vars": {
|
||||||
"paths": [
|
"paths": [
|
||||||
"/nsm/suricata/eve*.json"
|
"/nsm/suricata/eve*.json"
|
||||||
],
|
],
|
||||||
"data_stream.dataset": "suricata",
|
"data_stream.dataset": "suricata",
|
||||||
"pipeline": "suricata.common",
|
|
||||||
"parsers": "#- ndjson:\n# target: \"\"\n# message_key: msg\n#- multiline:\n# type: count\n# count_lines: 3\n",
|
|
||||||
"exclude_files": [
|
|
||||||
"\\.gz$"
|
|
||||||
],
|
|
||||||
"include_files": [],
|
|
||||||
"processors": "- add_fields:\n target: event\n fields:\n category: network\n module: suricata",
|
|
||||||
"tags": [],
|
"tags": [],
|
||||||
"recursive_glob": true,
|
"processors": "- add_fields:\n target: event\n fields:\n category: network\n module: suricata",
|
||||||
"clean_inactive": -1,
|
"custom": "pipeline: suricata.common"
|
||||||
"harvester_limit": 0,
|
|
||||||
"fingerprint": false,
|
|
||||||
"fingerprint_offset": 0,
|
|
||||||
"fingerprint_length": "64",
|
|
||||||
"file_identity_native": true,
|
|
||||||
"exclude_lines": [],
|
|
||||||
"include_lines": []
|
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
}
|
}
|
||||||
|
|||||||
@@ -1,107 +0,0 @@
|
|||||||
{
|
|
||||||
"package": {
|
|
||||||
"name": "elasticsearch",
|
|
||||||
"version": ""
|
|
||||||
},
|
|
||||||
"name": "elasticsearch-grid-nodes_heavy",
|
|
||||||
"namespace": "default",
|
|
||||||
"description": "Elasticsearch Logs",
|
|
||||||
"policy_id": "so-grid-nodes_heavy",
|
|
||||||
"inputs": {
|
|
||||||
"elasticsearch-logfile": {
|
|
||||||
"enabled": true,
|
|
||||||
"streams": {
|
|
||||||
"elasticsearch.audit": {
|
|
||||||
"enabled": false,
|
|
||||||
"vars": {
|
|
||||||
"paths": [
|
|
||||||
"/var/log/elasticsearch/*_audit.json"
|
|
||||||
]
|
|
||||||
}
|
|
||||||
},
|
|
||||||
"elasticsearch.deprecation": {
|
|
||||||
"enabled": false,
|
|
||||||
"vars": {
|
|
||||||
"paths": [
|
|
||||||
"/var/log/elasticsearch/*_deprecation.json"
|
|
||||||
]
|
|
||||||
}
|
|
||||||
},
|
|
||||||
"elasticsearch.gc": {
|
|
||||||
"enabled": false,
|
|
||||||
"vars": {
|
|
||||||
"paths": [
|
|
||||||
"/var/log/elasticsearch/gc.log.[0-9]*",
|
|
||||||
"/var/log/elasticsearch/gc.log"
|
|
||||||
]
|
|
||||||
}
|
|
||||||
},
|
|
||||||
"elasticsearch.server": {
|
|
||||||
"enabled": true,
|
|
||||||
"vars": {
|
|
||||||
"paths": [
|
|
||||||
"/opt/so/log/elasticsearch/*.json"
|
|
||||||
]
|
|
||||||
}
|
|
||||||
},
|
|
||||||
"elasticsearch.slowlog": {
|
|
||||||
"enabled": false,
|
|
||||||
"vars": {
|
|
||||||
"paths": [
|
|
||||||
"/var/log/elasticsearch/*_index_search_slowlog.json",
|
|
||||||
"/var/log/elasticsearch/*_index_indexing_slowlog.json"
|
|
||||||
]
|
|
||||||
}
|
|
||||||
}
|
|
||||||
}
|
|
||||||
},
|
|
||||||
"elasticsearch-elasticsearch/metrics": {
|
|
||||||
"enabled": false,
|
|
||||||
"vars": {
|
|
||||||
"hosts": [
|
|
||||||
"http://localhost:9200"
|
|
||||||
],
|
|
||||||
"scope": "node"
|
|
||||||
},
|
|
||||||
"streams": {
|
|
||||||
"elasticsearch.stack_monitoring.ccr": {
|
|
||||||
"enabled": false
|
|
||||||
},
|
|
||||||
"elasticsearch.stack_monitoring.cluster_stats": {
|
|
||||||
"enabled": false
|
|
||||||
},
|
|
||||||
"elasticsearch.stack_monitoring.enrich": {
|
|
||||||
"enabled": false
|
|
||||||
},
|
|
||||||
"elasticsearch.stack_monitoring.index": {
|
|
||||||
"enabled": false
|
|
||||||
},
|
|
||||||
"elasticsearch.stack_monitoring.index_recovery": {
|
|
||||||
"enabled": false,
|
|
||||||
"vars": {
|
|
||||||
"active.only": true
|
|
||||||
}
|
|
||||||
},
|
|
||||||
"elasticsearch.stack_monitoring.index_summary": {
|
|
||||||
"enabled": false
|
|
||||||
},
|
|
||||||
"elasticsearch.stack_monitoring.ml_job": {
|
|
||||||
"enabled": false
|
|
||||||
},
|
|
||||||
"elasticsearch.stack_monitoring.node": {
|
|
||||||
"enabled": false
|
|
||||||
},
|
|
||||||
"elasticsearch.stack_monitoring.node_stats": {
|
|
||||||
"enabled": false
|
|
||||||
},
|
|
||||||
"elasticsearch.stack_monitoring.pending_tasks": {
|
|
||||||
"enabled": false
|
|
||||||
},
|
|
||||||
"elasticsearch.stack_monitoring.shard": {
|
|
||||||
"enabled": false
|
|
||||||
}
|
|
||||||
}
|
|
||||||
}
|
|
||||||
},
|
|
||||||
"force": true
|
|
||||||
}
|
|
||||||
@@ -8,9 +8,7 @@
|
|||||||
{% endif %}
|
{% endif %}
|
||||||
|
|
||||||
{% set AGENT_STATUS = salt['service.available']('elastic-agent') %}
|
{% set AGENT_STATUS = salt['service.available']('elastic-agent') %}
|
||||||
{% set AGENT_EXISTS = salt['file.file_exists']('/opt/Elastic/Agent/elastic-agent') %}
|
{% if not AGENT_STATUS %}
|
||||||
|
|
||||||
{% if not AGENT_STATUS or not AGENT_EXISTS %}
|
|
||||||
|
|
||||||
pull_agent_installer:
|
pull_agent_installer:
|
||||||
file.managed:
|
file.managed:
|
||||||
@@ -21,7 +19,7 @@ pull_agent_installer:
|
|||||||
|
|
||||||
run_installer:
|
run_installer:
|
||||||
cmd.run:
|
cmd.run:
|
||||||
- name: ./so-elastic-agent_linux_amd64 -token={{ GRIDNODETOKEN }} -force
|
- name: ./so-elastic-agent_linux_amd64 -token={{ GRIDNODETOKEN }}
|
||||||
- cwd: /opt/so
|
- cwd: /opt/so
|
||||||
- retry:
|
- retry:
|
||||||
attempts: 3
|
attempts: 3
|
||||||
|
|||||||
@@ -21,7 +21,6 @@
|
|||||||
'azure_application_insights.app_state': 'azure.app_state',
|
'azure_application_insights.app_state': 'azure.app_state',
|
||||||
'azure_billing.billing': 'azure.billing',
|
'azure_billing.billing': 'azure.billing',
|
||||||
'azure_functions.metrics': 'azure.function',
|
'azure_functions.metrics': 'azure.function',
|
||||||
'azure_ai_foundry.metrics': 'azure.ai_foundry',
|
|
||||||
'azure_metrics.compute_vm_scaleset': 'azure.compute_vm_scaleset',
|
'azure_metrics.compute_vm_scaleset': 'azure.compute_vm_scaleset',
|
||||||
'azure_metrics.compute_vm': 'azure.compute_vm',
|
'azure_metrics.compute_vm': 'azure.compute_vm',
|
||||||
'azure_metrics.container_instance': 'azure.container_instance',
|
'azure_metrics.container_instance': 'azure.container_instance',
|
||||||
|
|||||||
@@ -1,186 +0,0 @@
|
|||||||
# Copyright Security Onion Solutions LLC and/or licensed to Security Onion Solutions LLC under one
|
|
||||||
# or more contributor license agreements. Licensed under the Elastic License 2.0 as shown at
|
|
||||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
|
||||||
# Elastic License 2.0.
|
|
||||||
|
|
||||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
|
||||||
{% if sls.split('.')[0] in allowed_states %}
|
|
||||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
|
||||||
{% from 'elasticfleet/map.jinja' import ELASTICFLEETMERGED %}
|
|
||||||
{% from 'ca/map.jinja' import CA %}
|
|
||||||
|
|
||||||
{% if GLOBALS.is_manager or GLOBALS.role in ['so-heavynode', 'so-fleet', 'so-receiver'] %}
|
|
||||||
|
|
||||||
{% if grains['role'] not in [ 'so-heavynode', 'so-receiver'] %}
|
|
||||||
# Start -- Elastic Fleet Host Cert
|
|
||||||
etc_elasticfleet_key:
|
|
||||||
x509.private_key_managed:
|
|
||||||
- name: /etc/pki/elasticfleet-server.key
|
|
||||||
- keysize: 4096
|
|
||||||
- backup: True
|
|
||||||
- new: True
|
|
||||||
{% if salt['file.file_exists']('/etc/pki/elasticfleet-server.key') -%}
|
|
||||||
- prereq:
|
|
||||||
- x509: etc_elasticfleet_crt
|
|
||||||
{%- endif %}
|
|
||||||
- retry:
|
|
||||||
attempts: 5
|
|
||||||
interval: 30
|
|
||||||
|
|
||||||
etc_elasticfleet_crt:
|
|
||||||
x509.certificate_managed:
|
|
||||||
- name: /etc/pki/elasticfleet-server.crt
|
|
||||||
- ca_server: {{ CA.server }}
|
|
||||||
- signing_policy: elasticfleet
|
|
||||||
- private_key: /etc/pki/elasticfleet-server.key
|
|
||||||
- CN: {{ GLOBALS.hostname }}
|
|
||||||
- subjectAltName: DNS:{{ GLOBALS.hostname }},DNS:{{ GLOBALS.url_base }},IP:{{ GLOBALS.node_ip }}{% if ELASTICFLEETMERGED.config.server.custom_fqdn | length > 0 %},DNS:{{ ELASTICFLEETMERGED.config.server.custom_fqdn | join(',DNS:') }}{% endif %}
|
|
||||||
- days_remaining: 7
|
|
||||||
- days_valid: 820
|
|
||||||
- backup: True
|
|
||||||
- timeout: 30
|
|
||||||
- retry:
|
|
||||||
attempts: 5
|
|
||||||
interval: 30
|
|
||||||
|
|
||||||
efperms:
|
|
||||||
file.managed:
|
|
||||||
- replace: False
|
|
||||||
- name: /etc/pki/elasticfleet-server.key
|
|
||||||
- mode: 640
|
|
||||||
- group: 939
|
|
||||||
|
|
||||||
chownelasticfleetcrt:
|
|
||||||
file.managed:
|
|
||||||
- replace: False
|
|
||||||
- name: /etc/pki/elasticfleet-server.crt
|
|
||||||
- mode: 640
|
|
||||||
- user: 947
|
|
||||||
- group: 939
|
|
||||||
|
|
||||||
chownelasticfleetkey:
|
|
||||||
file.managed:
|
|
||||||
- replace: False
|
|
||||||
- name: /etc/pki/elasticfleet-server.key
|
|
||||||
- mode: 640
|
|
||||||
- user: 947
|
|
||||||
- group: 939
|
|
||||||
# End -- Elastic Fleet Host Cert
|
|
||||||
{% endif %} # endif is for not including HeavyNodes & Receivers
|
|
||||||
|
|
||||||
|
|
||||||
# Start -- Elastic Fleet Client Cert for Agent (Mutual Auth with Logstash Output)
|
|
||||||
etc_elasticfleet_agent_key:
|
|
||||||
x509.private_key_managed:
|
|
||||||
- name: /etc/pki/elasticfleet-agent.key
|
|
||||||
- keysize: 4096
|
|
||||||
- backup: True
|
|
||||||
- new: True
|
|
||||||
{% if salt['file.file_exists']('/etc/pki/elasticfleet-agent.key') -%}
|
|
||||||
- prereq:
|
|
||||||
- x509: etc_elasticfleet_agent_crt
|
|
||||||
{%- endif %}
|
|
||||||
- retry:
|
|
||||||
attempts: 5
|
|
||||||
interval: 30
|
|
||||||
|
|
||||||
etc_elasticfleet_agent_crt:
|
|
||||||
x509.certificate_managed:
|
|
||||||
- name: /etc/pki/elasticfleet-agent.crt
|
|
||||||
- ca_server: {{ CA.server }}
|
|
||||||
- signing_policy: elasticfleet
|
|
||||||
- private_key: /etc/pki/elasticfleet-agent.key
|
|
||||||
- CN: {{ GLOBALS.hostname }}
|
|
||||||
- days_remaining: 7
|
|
||||||
- days_valid: 820
|
|
||||||
- backup: True
|
|
||||||
- timeout: 30
|
|
||||||
- retry:
|
|
||||||
attempts: 5
|
|
||||||
interval: 30
|
|
||||||
cmd.run:
|
|
||||||
- name: "/usr/bin/openssl pkcs8 -in /etc/pki/elasticfleet-agent.key -topk8 -out /etc/pki/elasticfleet-agent.p8 -nocrypt"
|
|
||||||
- onchanges:
|
|
||||||
- x509: etc_elasticfleet_agent_key
|
|
||||||
|
|
||||||
efagentperms:
|
|
||||||
file.managed:
|
|
||||||
- replace: False
|
|
||||||
- name: /etc/pki/elasticfleet-agent.key
|
|
||||||
- mode: 640
|
|
||||||
- group: 939
|
|
||||||
|
|
||||||
chownelasticfleetagentcrt:
|
|
||||||
file.managed:
|
|
||||||
- replace: False
|
|
||||||
- name: /etc/pki/elasticfleet-agent.crt
|
|
||||||
- mode: 640
|
|
||||||
- user: 947
|
|
||||||
- group: 939
|
|
||||||
|
|
||||||
chownelasticfleetagentkey:
|
|
||||||
file.managed:
|
|
||||||
- replace: False
|
|
||||||
- name: /etc/pki/elasticfleet-agent.key
|
|
||||||
- mode: 640
|
|
||||||
- user: 947
|
|
||||||
- group: 939
|
|
||||||
# End -- Elastic Fleet Client Cert for Agent (Mutual Auth with Logstash Output)
|
|
||||||
|
|
||||||
{% endif %}
|
|
||||||
|
|
||||||
{% if GLOBALS.role in ['so-manager', 'so-managerhype', 'so-managersearch', 'so-standalone'] %}
|
|
||||||
elasticfleet_kafka_key:
|
|
||||||
x509.private_key_managed:
|
|
||||||
- name: /etc/pki/elasticfleet-kafka.key
|
|
||||||
- keysize: 4096
|
|
||||||
- backup: True
|
|
||||||
- new: True
|
|
||||||
{% if salt['file.file_exists']('/etc/pki/elasticfleet-kafka.key') -%}
|
|
||||||
- prereq:
|
|
||||||
- x509: elasticfleet_kafka_crt
|
|
||||||
{%- endif %}
|
|
||||||
- retry:
|
|
||||||
attempts: 5
|
|
||||||
interval: 30
|
|
||||||
|
|
||||||
elasticfleet_kafka_crt:
|
|
||||||
x509.certificate_managed:
|
|
||||||
- name: /etc/pki/elasticfleet-kafka.crt
|
|
||||||
- ca_server: {{ CA.server }}
|
|
||||||
- signing_policy: kafka
|
|
||||||
- private_key: /etc/pki/elasticfleet-kafka.key
|
|
||||||
- CN: {{ GLOBALS.hostname }}
|
|
||||||
- subjectAltName: DNS:{{ GLOBALS.hostname }}, IP:{{ GLOBALS.node_ip }}
|
|
||||||
- days_remaining: 7
|
|
||||||
- days_valid: 820
|
|
||||||
- backup: True
|
|
||||||
- timeout: 30
|
|
||||||
- retry:
|
|
||||||
attempts: 5
|
|
||||||
interval: 30
|
|
||||||
|
|
||||||
elasticfleet_kafka_cert_perms:
|
|
||||||
file.managed:
|
|
||||||
- replace: False
|
|
||||||
- name: /etc/pki/elasticfleet-kafka.crt
|
|
||||||
- mode: 640
|
|
||||||
- user: 947
|
|
||||||
- group: 939
|
|
||||||
|
|
||||||
elasticfleet_kafka_key_perms:
|
|
||||||
file.managed:
|
|
||||||
- replace: False
|
|
||||||
- name: /etc/pki/elasticfleet-kafka.key
|
|
||||||
- mode: 640
|
|
||||||
- user: 947
|
|
||||||
- group: 939
|
|
||||||
{% endif %}
|
|
||||||
|
|
||||||
{% else %}
|
|
||||||
|
|
||||||
{{sls}}_state_not_allowed:
|
|
||||||
test.fail_without_changes:
|
|
||||||
- name: {{sls}}_state_not_allowed
|
|
||||||
|
|
||||||
{% endif %}
|
|
||||||
@@ -17,9 +17,9 @@ if [ ! -f /opt/so/state/eaintegrations.txt ]; then
|
|||||||
|
|
||||||
# Third, configure Elastic Defend Integration seperately
|
# Third, configure Elastic Defend Integration seperately
|
||||||
/usr/sbin/so-elastic-fleet-integration-policy-elastic-defend
|
/usr/sbin/so-elastic-fleet-integration-policy-elastic-defend
|
||||||
|
|
||||||
# Initial Endpoints
|
# Initial Endpoints
|
||||||
for INTEGRATION in /opt/so/conf/elastic-fleet/integrations/endpoints-initial/*.json; do
|
for INTEGRATION in /opt/so/conf/elastic-fleet/integrations/endpoints-initial/*.json
|
||||||
|
do
|
||||||
printf "\n\nInitial Endpoints Policy - Loading $INTEGRATION\n"
|
printf "\n\nInitial Endpoints Policy - Loading $INTEGRATION\n"
|
||||||
elastic_fleet_integration_check "endpoints-initial" "$INTEGRATION"
|
elastic_fleet_integration_check "endpoints-initial" "$INTEGRATION"
|
||||||
if [ -n "$INTEGRATION_ID" ]; then
|
if [ -n "$INTEGRATION_ID" ]; then
|
||||||
@@ -40,7 +40,8 @@ if [ ! -f /opt/so/state/eaintegrations.txt ]; then
|
|||||||
done
|
done
|
||||||
|
|
||||||
# Grid Nodes - General
|
# Grid Nodes - General
|
||||||
for INTEGRATION in /opt/so/conf/elastic-fleet/integrations/grid-nodes_general/*.json; do
|
for INTEGRATION in /opt/so/conf/elastic-fleet/integrations/grid-nodes_general/*.json
|
||||||
|
do
|
||||||
printf "\n\nGrid Nodes Policy_General - Loading $INTEGRATION\n"
|
printf "\n\nGrid Nodes Policy_General - Loading $INTEGRATION\n"
|
||||||
elastic_fleet_integration_check "so-grid-nodes_general" "$INTEGRATION"
|
elastic_fleet_integration_check "so-grid-nodes_general" "$INTEGRATION"
|
||||||
if [ -n "$INTEGRATION_ID" ]; then
|
if [ -n "$INTEGRATION_ID" ]; then
|
||||||
@@ -59,9 +60,13 @@ if [ ! -f /opt/so/state/eaintegrations.txt ]; then
|
|||||||
fi
|
fi
|
||||||
fi
|
fi
|
||||||
done
|
done
|
||||||
|
if [[ "$RETURN_CODE" != "1" ]]; then
|
||||||
|
touch /opt/so/state/eaintegrations.txt
|
||||||
|
fi
|
||||||
|
|
||||||
# Grid Nodes - Heavy
|
# Grid Nodes - Heavy
|
||||||
for INTEGRATION in /opt/so/conf/elastic-fleet/integrations/grid-nodes_heavy/*.json; do
|
for INTEGRATION in /opt/so/conf/elastic-fleet/integrations/grid-nodes_heavy/*.json
|
||||||
|
do
|
||||||
printf "\n\nGrid Nodes Policy_Heavy - Loading $INTEGRATION\n"
|
printf "\n\nGrid Nodes Policy_Heavy - Loading $INTEGRATION\n"
|
||||||
elastic_fleet_integration_check "so-grid-nodes_heavy" "$INTEGRATION"
|
elastic_fleet_integration_check "so-grid-nodes_heavy" "$INTEGRATION"
|
||||||
if [ -n "$INTEGRATION_ID" ]; then
|
if [ -n "$INTEGRATION_ID" ]; then
|
||||||
@@ -73,16 +78,22 @@ if [ ! -f /opt/so/state/eaintegrations.txt ]; then
|
|||||||
fi
|
fi
|
||||||
else
|
else
|
||||||
printf "\n\nIntegration does not exist - Creating integration\n"
|
printf "\n\nIntegration does not exist - Creating integration\n"
|
||||||
if ! elastic_fleet_integration_create "@$INTEGRATION"; then
|
if [ "$NAME" != "elasticsearch-logs" ]; then
|
||||||
echo -e "\nFailed to create integration for ${INTEGRATION##*/}"
|
if ! elastic_fleet_integration_create "@$INTEGRATION"; then
|
||||||
RETURN_CODE=1
|
echo -e "\nFailed to create integration for ${INTEGRATION##*/}"
|
||||||
continue
|
RETURN_CODE=1
|
||||||
|
continue
|
||||||
|
fi
|
||||||
fi
|
fi
|
||||||
fi
|
fi
|
||||||
done
|
done
|
||||||
|
if [[ "$RETURN_CODE" != "1" ]]; then
|
||||||
|
touch /opt/so/state/eaintegrations.txt
|
||||||
|
fi
|
||||||
|
|
||||||
# Fleet Server - Optional integrations
|
# Fleet Server - Optional integrations
|
||||||
for INTEGRATION in /opt/so/conf/elastic-fleet/integrations-optional/FleetServer*/*.json; do
|
for INTEGRATION in /opt/so/conf/elastic-fleet/integrations-optional/FleetServer*/*.json
|
||||||
|
do
|
||||||
if ! [ "$INTEGRATION" == "/opt/so/conf/elastic-fleet/integrations-optional/FleetServer*/*.json" ]; then
|
if ! [ "$INTEGRATION" == "/opt/so/conf/elastic-fleet/integrations-optional/FleetServer*/*.json" ]; then
|
||||||
FLEET_POLICY=`echo "$INTEGRATION"| cut -d'/' -f7`
|
FLEET_POLICY=`echo "$INTEGRATION"| cut -d'/' -f7`
|
||||||
printf "\n\nFleet Server Policy - Loading $INTEGRATION\n"
|
printf "\n\nFleet Server Policy - Loading $INTEGRATION\n"
|
||||||
@@ -106,8 +117,6 @@ if [ ! -f /opt/so/state/eaintegrations.txt ]; then
|
|||||||
fi
|
fi
|
||||||
fi
|
fi
|
||||||
done
|
done
|
||||||
|
|
||||||
# Only create the state file if all policies were created/updated successfully
|
|
||||||
if [[ "$RETURN_CODE" != "1" ]]; then
|
if [[ "$RETURN_CODE" != "1" ]]; then
|
||||||
touch /opt/so/state/eaintegrations.txt
|
touch /opt/so/state/eaintegrations.txt
|
||||||
fi
|
fi
|
||||||
|
|||||||
@@ -14,7 +14,7 @@ if ! is_manager_node; then
|
|||||||
fi
|
fi
|
||||||
|
|
||||||
# Get current list of Grid Node Agents that need to be upgraded
|
# Get current list of Grid Node Agents that need to be upgraded
|
||||||
RAW_JSON=$(curl -K /opt/so/conf/elasticsearch/curl.config -L "http://localhost:5601/api/fleet/agents?perPage=20&page=1&kuery=NOT%20agent.version%3A%20{{ELASTICSEARCHDEFAULTS.elasticsearch.version}}%20AND%20policy_id%3A%20so-grid-nodes_%2A&showInactive=false&getStatusSummary=true" --retry 3 --retry-delay 30 --fail 2>/dev/null)
|
RAW_JSON=$(curl -K /opt/so/conf/elasticsearch/curl.config -L "http://localhost:5601/api/fleet/agents?perPage=20&page=1&kuery=NOT%20agent.version%20:%20%22{{ELASTICSEARCHDEFAULTS.elasticsearch.version}}%22%20and%20policy_id%20:%20%22so-grid-nodes_general%22&showInactive=false&getStatusSummary=true")
|
||||||
|
|
||||||
# Check to make sure that the server responded with good data - else, bail from script
|
# Check to make sure that the server responded with good data - else, bail from script
|
||||||
CHECKSUM=$(jq -r '.page' <<< "$RAW_JSON")
|
CHECKSUM=$(jq -r '.page' <<< "$RAW_JSON")
|
||||||
|
|||||||
@@ -26,7 +26,7 @@ function update_es_urls() {
|
|||||||
}
|
}
|
||||||
|
|
||||||
# Get current list of Fleet Elasticsearch URLs
|
# Get current list of Fleet Elasticsearch URLs
|
||||||
RAW_JSON=$(curl -K /opt/so/conf/elasticsearch/curl.config 'http://localhost:5601/api/fleet/outputs/so-manager_elasticsearch' --retry 3 --retry-delay 30 --fail 2>/dev/null)
|
RAW_JSON=$(curl -K /opt/so/conf/elasticsearch/curl.config 'http://localhost:5601/api/fleet/outputs/so-manager_elasticsearch')
|
||||||
|
|
||||||
# Check to make sure that the server responded with good data - else, bail from script
|
# Check to make sure that the server responded with good data - else, bail from script
|
||||||
CHECKSUM=$(jq -r '.item.id' <<< "$RAW_JSON")
|
CHECKSUM=$(jq -r '.item.id' <<< "$RAW_JSON")
|
||||||
|
|||||||
@@ -86,7 +86,7 @@ if [[ -f $STATE_FILE_SUCCESS ]]; then
|
|||||||
latest_package_list=$(/usr/sbin/so-elastic-fleet-package-list)
|
latest_package_list=$(/usr/sbin/so-elastic-fleet-package-list)
|
||||||
echo '{ "packages" : []}' > $BULK_INSTALL_PACKAGE_LIST
|
echo '{ "packages" : []}' > $BULK_INSTALL_PACKAGE_LIST
|
||||||
rm -f $INSTALLED_PACKAGE_LIST
|
rm -f $INSTALLED_PACKAGE_LIST
|
||||||
echo $latest_package_list | jq '{packages: [.items[] | {name: .name, latest_version: .version, installed_version: .installationInfo.version, subscription: .conditions.elastic.subscription }]}' >> $INSTALLED_PACKAGE_LIST
|
echo $latest_package_list | jq '{packages: [.items[] | {name: .name, latest_version: .version, installed_version: .savedObject.attributes.install_version, subscription: .conditions.elastic.subscription }]}' >> $INSTALLED_PACKAGE_LIST
|
||||||
|
|
||||||
while read -r package; do
|
while read -r package; do
|
||||||
# get package details
|
# get package details
|
||||||
|
|||||||
@@ -142,7 +142,7 @@ function update_kafka_outputs() {
|
|||||||
|
|
||||||
{% if GLOBALS.pipeline == "KAFKA" %}
|
{% if GLOBALS.pipeline == "KAFKA" %}
|
||||||
# Get current list of Kafka Outputs
|
# Get current list of Kafka Outputs
|
||||||
RAW_JSON=$(curl -K /opt/so/conf/elasticsearch/curl.config 'http://localhost:5601/api/fleet/outputs/so-manager_kafka' --retry 3 --retry-delay 30 --fail 2>/dev/null)
|
RAW_JSON=$(curl -K /opt/so/conf/elasticsearch/curl.config 'http://localhost:5601/api/fleet/outputs/so-manager_kafka')
|
||||||
|
|
||||||
# Check to make sure that the server responded with good data - else, bail from script
|
# Check to make sure that the server responded with good data - else, bail from script
|
||||||
CHECKSUM=$(jq -r '.item.id' <<< "$RAW_JSON")
|
CHECKSUM=$(jq -r '.item.id' <<< "$RAW_JSON")
|
||||||
@@ -168,7 +168,7 @@ function update_kafka_outputs() {
|
|||||||
{# If global pipeline isn't set to KAFKA then assume default of REDIS / logstash #}
|
{# If global pipeline isn't set to KAFKA then assume default of REDIS / logstash #}
|
||||||
{% else %}
|
{% else %}
|
||||||
# Get current list of Logstash Outputs
|
# Get current list of Logstash Outputs
|
||||||
RAW_JSON=$(curl -K /opt/so/conf/elasticsearch/curl.config 'http://localhost:5601/api/fleet/outputs/so-manager_logstash' --retry 3 --retry-delay 30 --fail 2>/dev/null)
|
RAW_JSON=$(curl -K /opt/so/conf/elasticsearch/curl.config 'http://localhost:5601/api/fleet/outputs/so-manager_logstash')
|
||||||
|
|
||||||
# Check to make sure that the server responded with good data - else, bail from script
|
# Check to make sure that the server responded with good data - else, bail from script
|
||||||
CHECKSUM=$(jq -r '.item.id' <<< "$RAW_JSON")
|
CHECKSUM=$(jq -r '.item.id' <<< "$RAW_JSON")
|
||||||
|
|||||||
@@ -241,11 +241,9 @@ printf '%s\n'\
|
|||||||
"" >> "$global_pillar_file"
|
"" >> "$global_pillar_file"
|
||||||
|
|
||||||
# Call Elastic-Fleet Salt State
|
# Call Elastic-Fleet Salt State
|
||||||
printf "\nApplying elasticfleet state"
|
|
||||||
salt-call state.apply elasticfleet queue=True
|
salt-call state.apply elasticfleet queue=True
|
||||||
|
|
||||||
# Generate installers & install Elastic Agent on the node
|
# Generate installers & install Elastic Agent on the node
|
||||||
so-elastic-agent-gen-installers
|
so-elastic-agent-gen-installers
|
||||||
printf "\nApplying elasticfleet.install_agent_grid state"
|
|
||||||
salt-call state.apply elasticfleet.install_agent_grid queue=True
|
salt-call state.apply elasticfleet.install_agent_grid queue=True
|
||||||
exit 0
|
exit 0
|
||||||
|
|||||||
@@ -23,7 +23,7 @@ function update_fleet_urls() {
|
|||||||
}
|
}
|
||||||
|
|
||||||
# Get current list of Fleet Server URLs
|
# Get current list of Fleet Server URLs
|
||||||
RAW_JSON=$(curl -K /opt/so/conf/elasticsearch/curl.config 'http://localhost:5601/api/fleet/fleet_server_hosts/grid-default' --retry 3 --retry-delay 30 --fail 2>/dev/null)
|
RAW_JSON=$(curl -K /opt/so/conf/elasticsearch/curl.config 'http://localhost:5601/api/fleet/fleet_server_hosts/grid-default')
|
||||||
|
|
||||||
# Check to make sure that the server responded with good data - else, bail from script
|
# Check to make sure that the server responded with good data - else, bail from script
|
||||||
CHECKSUM=$(jq -r '.item.id' <<< "$RAW_JSON")
|
CHECKSUM=$(jq -r '.item.id' <<< "$RAW_JSON")
|
||||||
|
|||||||
@@ -34,11 +34,6 @@ if [[ "$RETURN_CODE" != "0" ]]; then
|
|||||||
exit 1
|
exit 1
|
||||||
fi
|
fi
|
||||||
|
|
||||||
if [[ ! -f /etc/pki/elasticfleet-kafka.crt || ! -f /etc/pki/elasticfleet-kafka.key ]]; then
|
|
||||||
echo -e "\nKafka certificates not found, can't setup Elastic Fleet output policy for Kafka...\n"
|
|
||||||
exit 1
|
|
||||||
fi
|
|
||||||
|
|
||||||
KAFKACRT=$(openssl x509 -in /etc/pki/elasticfleet-kafka.crt)
|
KAFKACRT=$(openssl x509 -in /etc/pki/elasticfleet-kafka.crt)
|
||||||
KAFKAKEY=$(openssl rsa -in /etc/pki/elasticfleet-kafka.key)
|
KAFKAKEY=$(openssl rsa -in /etc/pki/elasticfleet-kafka.key)
|
||||||
KAFKACA=$(openssl x509 -in /etc/pki/tls/certs/intca.crt)
|
KAFKACA=$(openssl x509 -in /etc/pki/tls/certs/intca.crt)
|
||||||
@@ -52,7 +47,7 @@ if ! kafka_output=$(curl -sK /opt/so/conf/elasticsearch/curl.config -L "http://l
|
|||||||
--arg KAFKACA "$KAFKACA" \
|
--arg KAFKACA "$KAFKACA" \
|
||||||
--arg MANAGER_IP "{{ GLOBALS.manager_ip }}:9092" \
|
--arg MANAGER_IP "{{ GLOBALS.manager_ip }}:9092" \
|
||||||
--arg KAFKA_OUTPUT_VERSION "$KAFKA_OUTPUT_VERSION" \
|
--arg KAFKA_OUTPUT_VERSION "$KAFKA_OUTPUT_VERSION" \
|
||||||
'{"name":"grid-kafka", "id":"so-manager_kafka","type":"kafka","hosts":[ $MANAGER_IP ],"is_default":false,"is_default_monitoring":false,"config_yaml":"","ssl":{"certificate_authorities":[ $KAFKACA ],"certificate": $KAFKACRT ,"key":"","verification_mode":"full"},"proxy_id":null,"client_id":"Elastic","version": $KAFKA_OUTPUT_VERSION ,"compression":"none","auth_type":"ssl","partition":"round_robin","round_robin":{"group_events":10},"topic":"default-securityonion","headers":[{"key":"","value":""}],"timeout":30,"broker_timeout":30,"required_acks":1,"secrets":{"ssl":{"key": $KAFKAKEY }}}'
|
'{"name":"grid-kafka", "id":"so-manager_kafka","type":"kafka","hosts":[ $MANAGER_IP ],"is_default":false,"is_default_monitoring":false,"config_yaml":"","ssl":{"certificate_authorities":[ $KAFKACA ],"certificate": $KAFKACRT ,"key":"","verification_mode":"full"},"proxy_id":null,"client_id":"Elastic","version": $KAFKA_OUTPUT_VERSION ,"compression":"none","auth_type":"ssl","partition":"round_robin","round_robin":{"group_events":10},"topics":[{"topic":"default-securityonion"}],"headers":[{"key":"","value":""}],"timeout":30,"broker_timeout":30,"required_acks":1,"secrets":{"ssl":{"key": $KAFKAKEY }}}'
|
||||||
)
|
)
|
||||||
if ! response=$(curl -sK /opt/so/conf/elasticsearch/curl.config -L -X POST "localhost:5601/api/fleet/outputs" -H 'kbn-xsrf: true' -H 'Content-Type: application/json' -d "$JSON_STRING" --fail 2>/dev/null); then
|
if ! response=$(curl -sK /opt/so/conf/elasticsearch/curl.config -L -X POST "localhost:5601/api/fleet/outputs" -H 'kbn-xsrf: true' -H 'Content-Type: application/json' -d "$JSON_STRING" --fail 2>/dev/null); then
|
||||||
echo -e "\nFailed to setup Elastic Fleet output policy for Kafka...\n"
|
echo -e "\nFailed to setup Elastic Fleet output policy for Kafka...\n"
|
||||||
@@ -72,7 +67,7 @@ elif kafka_output=$(curl -sK /opt/so/conf/elasticsearch/curl.config -L "http://l
|
|||||||
--arg ENABLED_DISABLED "$ENABLED_DISABLED"\
|
--arg ENABLED_DISABLED "$ENABLED_DISABLED"\
|
||||||
--arg KAFKA_OUTPUT_VERSION "$KAFKA_OUTPUT_VERSION" \
|
--arg KAFKA_OUTPUT_VERSION "$KAFKA_OUTPUT_VERSION" \
|
||||||
--argjson HOSTS "$HOSTS" \
|
--argjson HOSTS "$HOSTS" \
|
||||||
'{"name":"grid-kafka","type":"kafka","hosts":$HOSTS,"is_default":$ENABLED_DISABLED,"is_default_monitoring":$ENABLED_DISABLED,"config_yaml":"","ssl":{"certificate_authorities":[ $KAFKACA ],"certificate": $KAFKACRT ,"key":"","verification_mode":"full"},"proxy_id":null,"client_id":"Elastic","version": $KAFKA_OUTPUT_VERSION ,"compression":"none","auth_type":"ssl","partition":"round_robin","round_robin":{"group_events":10},"topic":"default-securityonion","headers":[{"key":"","value":""}],"timeout":30,"broker_timeout":30,"required_acks":1,"secrets":{"ssl":{"key": $KAFKAKEY }}}'
|
'{"name":"grid-kafka","type":"kafka","hosts":$HOSTS,"is_default":$ENABLED_DISABLED,"is_default_monitoring":$ENABLED_DISABLED,"config_yaml":"","ssl":{"certificate_authorities":[ $KAFKACA ],"certificate": $KAFKACRT ,"key":"","verification_mode":"full"},"proxy_id":null,"client_id":"Elastic","version": $KAFKA_OUTPUT_VERSION ,"compression":"none","auth_type":"ssl","partition":"round_robin","round_robin":{"group_events":10},"topics":[{"topic":"default-securityonion"}],"headers":[{"key":"","value":""}],"timeout":30,"broker_timeout":30,"required_acks":1,"secrets":{"ssl":{"key": $KAFKAKEY }}}'
|
||||||
)
|
)
|
||||||
if ! response=$(curl -sK /opt/so/conf/elasticsearch/curl.config -L -X PUT "localhost:5601/api/fleet/outputs/so-manager_kafka" -H 'kbn-xsrf: true' -H 'Content-Type: application/json' -d "$JSON_STRING" --fail 2>/dev/null); then
|
if ! response=$(curl -sK /opt/so/conf/elasticsearch/curl.config -L -X PUT "localhost:5601/api/fleet/outputs/so-manager_kafka" -H 'kbn-xsrf: true' -H 'Content-Type: application/json' -d "$JSON_STRING" --fail 2>/dev/null); then
|
||||||
echo -e "\nFailed to force update to Elastic Fleet output policy for Kafka...\n"
|
echo -e "\nFailed to force update to Elastic Fleet output policy for Kafka...\n"
|
||||||
|
|||||||
@@ -26,14 +26,14 @@ catrustscript:
|
|||||||
GLOBALS: {{ GLOBALS }}
|
GLOBALS: {{ GLOBALS }}
|
||||||
{% endif %}
|
{% endif %}
|
||||||
|
|
||||||
elasticsearch_cacerts:
|
cacertz:
|
||||||
file.managed:
|
file.managed:
|
||||||
- name: /opt/so/conf/ca/cacerts
|
- name: /opt/so/conf/ca/cacerts
|
||||||
- source: salt://elasticsearch/cacerts
|
- source: salt://elasticsearch/cacerts
|
||||||
- user: 939
|
- user: 939
|
||||||
- group: 939
|
- group: 939
|
||||||
|
|
||||||
elasticsearch_capems:
|
capemz:
|
||||||
file.managed:
|
file.managed:
|
||||||
- name: /opt/so/conf/ca/tls-ca-bundle.pem
|
- name: /opt/so/conf/ca/tls-ca-bundle.pem
|
||||||
- source: salt://elasticsearch/tls-ca-bundle.pem
|
- source: salt://elasticsearch/tls-ca-bundle.pem
|
||||||
|
|||||||
@@ -6,6 +6,8 @@
|
|||||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||||
{% import_yaml 'elasticsearch/defaults.yaml' as ELASTICSEARCHDEFAULTS with context %}
|
{% import_yaml 'elasticsearch/defaults.yaml' as ELASTICSEARCHDEFAULTS with context %}
|
||||||
|
|
||||||
|
{% set HIGHLANDER = salt['pillar.get']('global:highlander', False) %}
|
||||||
|
|
||||||
{# this is a list of dicts containing hostname:ip for elasticsearch nodes that need to know about each other for cluster #}
|
{# this is a list of dicts containing hostname:ip for elasticsearch nodes that need to know about each other for cluster #}
|
||||||
{% set ELASTICSEARCH_SEED_HOSTS = [] %}
|
{% set ELASTICSEARCH_SEED_HOSTS = [] %}
|
||||||
{% set node_data = salt['pillar.get']('elasticsearch:nodes', {GLOBALS.role.split('-')[1]: {GLOBALS.hostname: {'ip': GLOBALS.node_ip}}}) %}
|
{% set node_data = salt['pillar.get']('elasticsearch:nodes', {GLOBALS.role.split('-')[1]: {GLOBALS.hostname: {'ip': GLOBALS.node_ip}}}) %}
|
||||||
@@ -34,8 +36,14 @@
|
|||||||
{% endfor %}
|
{% endfor %}
|
||||||
{% endif %}
|
{% endif %}
|
||||||
{% elif grains.id.split('_') | last == 'searchnode' %}
|
{% elif grains.id.split('_') | last == 'searchnode' %}
|
||||||
|
{% if HIGHLANDER %}
|
||||||
|
{% do ELASTICSEARCHDEFAULTS.elasticsearch.config.node.roles.extend(['ml', 'master', 'transform']) %}
|
||||||
|
{% endif %}
|
||||||
{% do ELASTICSEARCHDEFAULTS.elasticsearch.config.update({'discovery': {'seed_hosts': [GLOBALS.manager]}}) %}
|
{% do ELASTICSEARCHDEFAULTS.elasticsearch.config.update({'discovery': {'seed_hosts': [GLOBALS.manager]}}) %}
|
||||||
{% endif %}
|
{% endif %}
|
||||||
|
{% if HIGHLANDER %}
|
||||||
|
{% do ELASTICSEARCHDEFAULTS.elasticsearch.config.xpack.ml.update({'enabled': true}) %}
|
||||||
|
{% endif %}
|
||||||
|
|
||||||
{% do ELASTICSEARCHDEFAULTS.elasticsearch.config.node.update({'name': GLOBALS.hostname}) %}
|
{% do ELASTICSEARCHDEFAULTS.elasticsearch.config.node.update({'name': GLOBALS.hostname}) %}
|
||||||
{% do ELASTICSEARCHDEFAULTS.elasticsearch.config.cluster.update({'name': GLOBALS.hostname}) %}
|
{% do ELASTICSEARCHDEFAULTS.elasticsearch.config.cluster.update({'name': GLOBALS.hostname}) %}
|
||||||
|
|||||||
@@ -5,6 +5,11 @@
|
|||||||
|
|
||||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
{% from 'allowed_states.map.jinja' import allowed_states %}
|
||||||
{% if sls.split('.')[0] in allowed_states %}
|
{% if sls.split('.')[0] in allowed_states %}
|
||||||
|
|
||||||
|
include:
|
||||||
|
- ssl
|
||||||
|
- elasticsearch.ca
|
||||||
|
|
||||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||||
{% from 'elasticsearch/config.map.jinja' import ELASTICSEARCHMERGED %}
|
{% from 'elasticsearch/config.map.jinja' import ELASTICSEARCHMERGED %}
|
||||||
|
|
||||||
@@ -98,6 +103,10 @@ esrolesdir:
|
|||||||
- group: 939
|
- group: 939
|
||||||
- makedirs: True
|
- makedirs: True
|
||||||
|
|
||||||
|
eslibdir:
|
||||||
|
file.absent:
|
||||||
|
- name: /opt/so/conf/elasticsearch/lib
|
||||||
|
|
||||||
esingestdynamicconf:
|
esingestdynamicconf:
|
||||||
file.recurse:
|
file.recurse:
|
||||||
- name: /opt/so/conf/elasticsearch/ingest
|
- name: /opt/so/conf/elasticsearch/ingest
|
||||||
@@ -115,6 +124,11 @@ esingestconf:
|
|||||||
- group: 939
|
- group: 939
|
||||||
- show_changes: False
|
- show_changes: False
|
||||||
|
|
||||||
|
# Remove .fleet_final_pipeline-1 because we are using global@custom now
|
||||||
|
so-fleet-final-pipeline-remove:
|
||||||
|
file.absent:
|
||||||
|
- name: /opt/so/conf/elasticsearch/ingest/.fleet_final_pipeline-1
|
||||||
|
|
||||||
# Auto-generate Elasticsearch ingest node pipelines from pillar
|
# Auto-generate Elasticsearch ingest node pipelines from pillar
|
||||||
{% for pipeline, config in ELASTICSEARCHMERGED.pipelines.items() %}
|
{% for pipeline, config in ELASTICSEARCHMERGED.pipelines.items() %}
|
||||||
es_ingest_conf_{{pipeline}}:
|
es_ingest_conf_{{pipeline}}:
|
||||||
|
|||||||
@@ -1,13 +1,11 @@
|
|||||||
elasticsearch:
|
elasticsearch:
|
||||||
enabled: false
|
enabled: false
|
||||||
version: 9.0.8
|
version: 8.18.8
|
||||||
index_clean: true
|
index_clean: true
|
||||||
config:
|
config:
|
||||||
action:
|
action:
|
||||||
destructive_requires_name: true
|
destructive_requires_name: true
|
||||||
cluster:
|
cluster:
|
||||||
logsdb:
|
|
||||||
enabled: false
|
|
||||||
routing:
|
routing:
|
||||||
allocation:
|
allocation:
|
||||||
disk:
|
disk:
|
||||||
@@ -693,6 +691,7 @@ elasticsearch:
|
|||||||
match_mapping_type: string
|
match_mapping_type: string
|
||||||
settings:
|
settings:
|
||||||
index:
|
index:
|
||||||
|
final_pipeline: .fleet_final_pipeline-1
|
||||||
lifecycle:
|
lifecycle:
|
||||||
name: so-import-logs
|
name: so-import-logs
|
||||||
mapping:
|
mapping:
|
||||||
@@ -858,13 +857,53 @@ elasticsearch:
|
|||||||
composed_of:
|
composed_of:
|
||||||
- agent-mappings
|
- agent-mappings
|
||||||
- dtc-agent-mappings
|
- dtc-agent-mappings
|
||||||
|
- base-mappings
|
||||||
|
- dtc-base-mappings
|
||||||
|
- client-mappings
|
||||||
|
- dtc-client-mappings
|
||||||
|
- container-mappings
|
||||||
|
- destination-mappings
|
||||||
|
- dtc-destination-mappings
|
||||||
|
- pb-override-destination-mappings
|
||||||
|
- dll-mappings
|
||||||
|
- dns-mappings
|
||||||
|
- dtc-dns-mappings
|
||||||
|
- ecs-mappings
|
||||||
|
- dtc-ecs-mappings
|
||||||
|
- error-mappings
|
||||||
- event-mappings
|
- event-mappings
|
||||||
|
- dtc-event-mappings
|
||||||
- file-mappings
|
- file-mappings
|
||||||
|
- dtc-file-mappings
|
||||||
|
- group-mappings
|
||||||
- host-mappings
|
- host-mappings
|
||||||
- dtc-host-mappings
|
- dtc-host-mappings
|
||||||
- http-mappings
|
- http-mappings
|
||||||
- dtc-http-mappings
|
- dtc-http-mappings
|
||||||
|
- log-mappings
|
||||||
- metadata-mappings
|
- metadata-mappings
|
||||||
|
- network-mappings
|
||||||
|
- dtc-network-mappings
|
||||||
|
- observer-mappings
|
||||||
|
- dtc-observer-mappings
|
||||||
|
- organization-mappings
|
||||||
|
- package-mappings
|
||||||
|
- process-mappings
|
||||||
|
- dtc-process-mappings
|
||||||
|
- related-mappings
|
||||||
|
- rule-mappings
|
||||||
|
- dtc-rule-mappings
|
||||||
|
- server-mappings
|
||||||
|
- service-mappings
|
||||||
|
- dtc-service-mappings
|
||||||
|
- source-mappings
|
||||||
|
- dtc-source-mappings
|
||||||
|
- pb-override-source-mappings
|
||||||
|
- threat-mappings
|
||||||
|
- tls-mappings
|
||||||
|
- url-mappings
|
||||||
|
- user_agent-mappings
|
||||||
|
- dtc-user_agent-mappings
|
||||||
- common-settings
|
- common-settings
|
||||||
- common-dynamic-mappings
|
- common-dynamic-mappings
|
||||||
data_stream:
|
data_stream:
|
||||||
|
|||||||
@@ -6,7 +6,7 @@
|
|||||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
{% from 'allowed_states.map.jinja' import allowed_states %}
|
||||||
{% if sls.split('.')[0] in allowed_states %}
|
{% if sls.split('.')[0] in allowed_states %}
|
||||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||||
{% from 'docker/docker.map.jinja' import DOCKERMERGED %}
|
{% from 'docker/docker.map.jinja' import DOCKER %}
|
||||||
{% from 'elasticsearch/config.map.jinja' import ELASTICSEARCH_NODES %}
|
{% from 'elasticsearch/config.map.jinja' import ELASTICSEARCH_NODES %}
|
||||||
{% from 'elasticsearch/config.map.jinja' import ELASTICSEARCH_SEED_HOSTS %}
|
{% from 'elasticsearch/config.map.jinja' import ELASTICSEARCH_SEED_HOSTS %}
|
||||||
{% from 'elasticsearch/config.map.jinja' import ELASTICSEARCHMERGED %}
|
{% from 'elasticsearch/config.map.jinja' import ELASTICSEARCHMERGED %}
|
||||||
@@ -14,9 +14,6 @@
|
|||||||
{% from 'elasticsearch/template.map.jinja' import ES_INDEX_SETTINGS %}
|
{% from 'elasticsearch/template.map.jinja' import ES_INDEX_SETTINGS %}
|
||||||
|
|
||||||
include:
|
include:
|
||||||
- ca
|
|
||||||
- elasticsearch.ca
|
|
||||||
- elasticsearch.ssl
|
|
||||||
- elasticsearch.config
|
- elasticsearch.config
|
||||||
- elasticsearch.sostatus
|
- elasticsearch.sostatus
|
||||||
|
|
||||||
@@ -28,15 +25,15 @@ so-elasticsearch:
|
|||||||
- user: elasticsearch
|
- user: elasticsearch
|
||||||
- networks:
|
- networks:
|
||||||
- sobridge:
|
- sobridge:
|
||||||
- ipv4_address: {{ DOCKERMERGED.containers['so-elasticsearch'].ip }}
|
- ipv4_address: {{ DOCKER.containers['so-elasticsearch'].ip }}
|
||||||
- extra_hosts:
|
- extra_hosts:
|
||||||
{% for node in ELASTICSEARCH_NODES %}
|
{% for node in ELASTICSEARCH_NODES %}
|
||||||
{% for hostname, ip in node.items() %}
|
{% for hostname, ip in node.items() %}
|
||||||
- {{hostname}}:{{ip}}
|
- {{hostname}}:{{ip}}
|
||||||
{% endfor %}
|
{% endfor %}
|
||||||
{% endfor %}
|
{% endfor %}
|
||||||
{% if DOCKERMERGED.containers['so-elasticsearch'].extra_hosts %}
|
{% if DOCKER.containers['so-elasticsearch'].extra_hosts %}
|
||||||
{% for XTRAHOST in DOCKERMERGED.containers['so-elasticsearch'].extra_hosts %}
|
{% for XTRAHOST in DOCKER.containers['so-elasticsearch'].extra_hosts %}
|
||||||
- {{ XTRAHOST }}
|
- {{ XTRAHOST }}
|
||||||
{% endfor %}
|
{% endfor %}
|
||||||
{% endif %}
|
{% endif %}
|
||||||
@@ -45,19 +42,17 @@ so-elasticsearch:
|
|||||||
- discovery.type=single-node
|
- discovery.type=single-node
|
||||||
{% endif %}
|
{% endif %}
|
||||||
- ES_JAVA_OPTS=-Xms{{ GLOBALS.elasticsearch.es_heap }} -Xmx{{ GLOBALS.elasticsearch.es_heap }} -Des.transport.cname_in_publish_address=true -Dlog4j2.formatMsgNoLookups=true
|
- ES_JAVA_OPTS=-Xms{{ GLOBALS.elasticsearch.es_heap }} -Xmx{{ GLOBALS.elasticsearch.es_heap }} -Des.transport.cname_in_publish_address=true -Dlog4j2.formatMsgNoLookups=true
|
||||||
{% if DOCKERMERGED.containers['so-elasticsearch'].extra_env %}
|
ulimits:
|
||||||
{% for XTRAENV in DOCKERMERGED.containers['so-elasticsearch'].extra_env %}
|
- memlock=-1:-1
|
||||||
|
- nofile=65536:65536
|
||||||
|
- nproc=4096
|
||||||
|
{% if DOCKER.containers['so-elasticsearch'].extra_env %}
|
||||||
|
{% for XTRAENV in DOCKER.containers['so-elasticsearch'].extra_env %}
|
||||||
- {{ XTRAENV }}
|
- {{ XTRAENV }}
|
||||||
{% endfor %}
|
{% endfor %}
|
||||||
{% endif %}
|
{% endif %}
|
||||||
{% if DOCKERMERGED.containers['so-elasticsearch'].ulimits %}
|
|
||||||
- ulimits:
|
|
||||||
{% for ULIMIT in DOCKERMERGED.containers['so-elasticsearch'].ulimits %}
|
|
||||||
- {{ ULIMIT.name }}={{ ULIMIT.soft }}:{{ ULIMIT.hard }}
|
|
||||||
{% endfor %}
|
|
||||||
{% endif %}
|
|
||||||
- port_bindings:
|
- port_bindings:
|
||||||
{% for BINDING in DOCKERMERGED.containers['so-elasticsearch'].port_bindings %}
|
{% for BINDING in DOCKER.containers['so-elasticsearch'].port_bindings %}
|
||||||
- {{ BINDING }}
|
- {{ BINDING }}
|
||||||
{% endfor %}
|
{% endfor %}
|
||||||
- binds:
|
- binds:
|
||||||
@@ -66,7 +61,11 @@ so-elasticsearch:
|
|||||||
- /nsm/elasticsearch:/usr/share/elasticsearch/data:rw
|
- /nsm/elasticsearch:/usr/share/elasticsearch/data:rw
|
||||||
- /opt/so/log/elasticsearch:/var/log/elasticsearch:rw
|
- /opt/so/log/elasticsearch:/var/log/elasticsearch:rw
|
||||||
- /opt/so/conf/ca/cacerts:/usr/share/elasticsearch/jdk/lib/security/cacerts:ro
|
- /opt/so/conf/ca/cacerts:/usr/share/elasticsearch/jdk/lib/security/cacerts:ro
|
||||||
|
{% if GLOBALS.is_manager %}
|
||||||
|
- /etc/pki/ca.crt:/usr/share/elasticsearch/config/ca.crt:ro
|
||||||
|
{% else %}
|
||||||
- /etc/pki/tls/certs/intca.crt:/usr/share/elasticsearch/config/ca.crt:ro
|
- /etc/pki/tls/certs/intca.crt:/usr/share/elasticsearch/config/ca.crt:ro
|
||||||
|
{% endif %}
|
||||||
- /etc/pki/elasticsearch.crt:/usr/share/elasticsearch/config/elasticsearch.crt:ro
|
- /etc/pki/elasticsearch.crt:/usr/share/elasticsearch/config/elasticsearch.crt:ro
|
||||||
- /etc/pki/elasticsearch.key:/usr/share/elasticsearch/config/elasticsearch.key:ro
|
- /etc/pki/elasticsearch.key:/usr/share/elasticsearch/config/elasticsearch.key:ro
|
||||||
- /etc/pki/elasticsearch.p12:/usr/share/elasticsearch/config/elasticsearch.p12:ro
|
- /etc/pki/elasticsearch.p12:/usr/share/elasticsearch/config/elasticsearch.p12:ro
|
||||||
@@ -77,27 +76,28 @@ so-elasticsearch:
|
|||||||
- {{ repo }}:{{ repo }}:rw
|
- {{ repo }}:{{ repo }}:rw
|
||||||
{% endfor %}
|
{% endfor %}
|
||||||
{% endif %}
|
{% endif %}
|
||||||
{% if DOCKERMERGED.containers['so-elasticsearch'].custom_bind_mounts %}
|
{% if DOCKER.containers['so-elasticsearch'].custom_bind_mounts %}
|
||||||
{% for BIND in DOCKERMERGED.containers['so-elasticsearch'].custom_bind_mounts %}
|
{% for BIND in DOCKER.containers['so-elasticsearch'].custom_bind_mounts %}
|
||||||
- {{ BIND }}
|
- {{ BIND }}
|
||||||
{% endfor %}
|
{% endfor %}
|
||||||
{% endif %}
|
{% endif %}
|
||||||
- watch:
|
- watch:
|
||||||
- file: trusttheca
|
- file: cacertz
|
||||||
- x509: elasticsearch_crt
|
|
||||||
- x509: elasticsearch_key
|
|
||||||
- file: elasticsearch_cacerts
|
|
||||||
- file: esyml
|
- file: esyml
|
||||||
- require:
|
- require:
|
||||||
- file: trusttheca
|
|
||||||
- x509: elasticsearch_crt
|
|
||||||
- x509: elasticsearch_key
|
|
||||||
- file: elasticsearch_cacerts
|
|
||||||
- file: esyml
|
- file: esyml
|
||||||
- file: eslog4jfile
|
- file: eslog4jfile
|
||||||
- file: nsmesdir
|
- file: nsmesdir
|
||||||
- file: eslogdir
|
- file: eslogdir
|
||||||
|
- file: cacertz
|
||||||
|
- x509: /etc/pki/elasticsearch.crt
|
||||||
|
- x509: /etc/pki/elasticsearch.key
|
||||||
- file: elasticp12perms
|
- file: elasticp12perms
|
||||||
|
{% if GLOBALS.is_manager %}
|
||||||
|
- x509: pki_public_ca_crt
|
||||||
|
{% else %}
|
||||||
|
- x509: trusttheca
|
||||||
|
{% endif %}
|
||||||
- cmd: auth_users_roles_inode
|
- cmd: auth_users_roles_inode
|
||||||
- cmd: auth_users_inode
|
- cmd: auth_users_inode
|
||||||
|
|
||||||
|
|||||||
@@ -1,3 +1,5 @@
|
|||||||
|
{%- set HIGHLANDER = salt['pillar.get']('global:highlander', False) -%}
|
||||||
|
{%- raw -%}
|
||||||
{
|
{
|
||||||
"description" : "common",
|
"description" : "common",
|
||||||
"processors" : [
|
"processors" : [
|
||||||
@@ -65,7 +67,19 @@
|
|||||||
{ "append": { "if": "ctx.dataset_tag_temp != null", "field": "tags", "value": "{{dataset_tag_temp.1}}" } },
|
{ "append": { "if": "ctx.dataset_tag_temp != null", "field": "tags", "value": "{{dataset_tag_temp.1}}" } },
|
||||||
{ "grok": { "if": "ctx.http?.response?.status_code != null", "field": "http.response.status_code", "patterns": ["%{NUMBER:http.response.status_code:long} %{GREEDYDATA}"]} },
|
{ "grok": { "if": "ctx.http?.response?.status_code != null", "field": "http.response.status_code", "patterns": ["%{NUMBER:http.response.status_code:long} %{GREEDYDATA}"]} },
|
||||||
{ "set": { "if": "ctx?.metadata?.kafka != null" , "field": "kafka.id", "value": "{{metadata.kafka.partition}}{{metadata.kafka.offset}}{{metadata.kafka.timestamp}}", "ignore_failure": true } },
|
{ "set": { "if": "ctx?.metadata?.kafka != null" , "field": "kafka.id", "value": "{{metadata.kafka.partition}}{{metadata.kafka.offset}}{{metadata.kafka.timestamp}}", "ignore_failure": true } },
|
||||||
{ "remove": { "field": [ "message2", "type", "fields", "category", "module", "dataset", "dataset_tag_temp", "event.dataset_temp" ], "ignore_missing": true, "ignore_failure": true } },
|
{ "remove": { "field": [ "message2", "type", "fields", "category", "module", "dataset", "dataset_tag_temp", "event.dataset_temp" ], "ignore_missing": true, "ignore_failure": true } }
|
||||||
|
{%- endraw %}
|
||||||
|
{%- if HIGHLANDER %}
|
||||||
|
,
|
||||||
|
{
|
||||||
|
"pipeline": {
|
||||||
|
"name": "ecs"
|
||||||
|
}
|
||||||
|
}
|
||||||
|
{%- endif %}
|
||||||
|
{%- raw %}
|
||||||
|
,
|
||||||
{ "pipeline": { "name": "global@custom", "ignore_missing_pipeline": true, "description": "[Fleet] Global pipeline for all data streams" } }
|
{ "pipeline": { "name": "global@custom", "ignore_missing_pipeline": true, "description": "[Fleet] Global pipeline for all data streams" } }
|
||||||
]
|
]
|
||||||
}
|
}
|
||||||
|
{% endraw %}
|
||||||
@@ -1,212 +1,31 @@
|
|||||||
{
|
{
|
||||||
"version": 3,
|
"version": 3,
|
||||||
"_meta": {
|
"_meta": {
|
||||||
"managed_by": "securityonion",
|
"managed_by": "securityonion",
|
||||||
"managed": true
|
"managed": true
|
||||||
},
|
},
|
||||||
"description": "Custom pipeline for processing all incoming Fleet Agent documents. \n",
|
"description": "Custom pipeline for processing all incoming Fleet Agent documents. \n",
|
||||||
"processors": [
|
"processors": [
|
||||||
{
|
{ "set": { "ignore_failure": true, "field": "event.module", "value": "elastic_agent" } },
|
||||||
"set": {
|
{ "split": { "if": "ctx.event?.dataset != null && ctx.event.dataset.contains('.')", "field": "event.dataset", "separator": "\\.", "target_field": "module_temp" } },
|
||||||
"ignore_failure": true,
|
{ "split": { "if": "ctx.data_stream?.dataset != null && ctx.data_stream?.dataset.contains('.')", "field":"data_stream.dataset", "separator":"\\.", "target_field":"datastream_dataset_temp", "ignore_missing":true } },
|
||||||
"field": "event.module",
|
{ "set": { "if": "ctx.module_temp != null", "override": true, "field": "event.module", "value": "{{module_temp.0}}" } },
|
||||||
"value": "elastic_agent"
|
{ "set": { "if": "ctx.datastream_dataset_temp != null && ctx.datastream_dataset_temp[0] == 'network_traffic'", "field":"event.module", "value":"{{ datastream_dataset_temp.0 }}", "ignore_failure":true, "ignore_empty_value":true, "description":"Fix EA network packet capture" } },
|
||||||
}
|
{ "gsub": { "if": "ctx.event?.dataset != null && ctx.event.dataset.contains('.')", "field": "event.dataset", "pattern": "^[^.]*.", "replacement": "", "target_field": "dataset_tag_temp" } },
|
||||||
},
|
{ "append": { "if": "ctx.dataset_tag_temp != null", "field": "tags", "value": "{{dataset_tag_temp}}", "allow_duplicates": false } },
|
||||||
{
|
{ "set": { "if": "ctx.network?.direction == 'egress'", "override": true, "field": "network.initiated", "value": "true" } },
|
||||||
"split": {
|
{ "set": { "if": "ctx.network?.direction == 'ingress'", "override": true, "field": "network.initiated", "value": "false" } },
|
||||||
"if": "ctx.event?.dataset != null && ctx.event.dataset.contains('.')",
|
{ "set": { "if": "ctx.network?.type == 'ipv4'", "override": true, "field": "destination.ipv6", "value": "false" } },
|
||||||
"field": "event.dataset",
|
{ "set": { "if": "ctx.network?.type == 'ipv6'", "override": true, "field": "destination.ipv6", "value": "true" } },
|
||||||
"separator": "\\.",
|
{ "set": { "if": "ctx.tags != null && ctx.tags.contains('import')", "override": true, "field": "data_stream.dataset", "value": "import" } },
|
||||||
"target_field": "module_temp"
|
{ "set": { "if": "ctx.tags != null && ctx.tags.contains('import')", "override": true, "field": "data_stream.namespace", "value": "so" } },
|
||||||
}
|
{ "community_id":{ "if": "ctx.event?.dataset == 'endpoint.events.network'", "ignore_failure":true } },
|
||||||
},
|
{ "set": { "if": "ctx.event?.module == 'fim'", "override": true, "field": "event.module", "value": "file_integrity" } },
|
||||||
{
|
{ "rename": { "if": "ctx.winlog?.provider_name == 'Microsoft-Windows-Windows Defender'", "ignore_missing": true, "field": "winlog.event_data.Threat Name", "target_field": "winlog.event_data.threat_name" } },
|
||||||
"split": {
|
{ "set": { "if": "ctx?.metadata?.kafka != null" , "field": "kafka.id", "value": "{{metadata.kafka.partition}}{{metadata.kafka.offset}}{{metadata.kafka.timestamp}}", "ignore_failure": true } },
|
||||||
"if": "ctx.data_stream?.dataset != null && ctx.data_stream?.dataset.contains('.')",
|
{ "set": { "if": "ctx.event?.dataset != null && ctx.event?.dataset == 'elasticsearch.server'", "field": "event.module", "value":"elasticsearch" }},
|
||||||
"field": "data_stream.dataset",
|
{"append": {"field":"related.ip","value":["{{source.ip}}","{{destination.ip}}"],"allow_duplicates":false,"if":"ctx?.event?.dataset == 'endpoint.events.network' && ctx?.source?.ip != null","ignore_failure":true}},
|
||||||
"separator": "\\.",
|
{"foreach": {"field":"host.ip","processor":{"append":{"field":"related.ip","value":"{{_ingest._value}}","allow_duplicates":false}},"if":"ctx?.event?.module == 'endpoint' && ctx?.host?.ip != null","ignore_missing":true, "description":"Extract IPs from Elastic Agent events (host.ip) and adds them to related.ip"}},
|
||||||
"target_field": "datastream_dataset_temp",
|
{ "remove": { "field": [ "message2", "type", "fields", "category", "module", "dataset", "event.dataset_temp", "dataset_tag_temp", "module_temp", "datastream_dataset_temp" ], "ignore_missing": true, "ignore_failure": true } }
|
||||||
"ignore_missing": true
|
]
|
||||||
}
|
}
|
||||||
},
|
|
||||||
{
|
|
||||||
"set": {
|
|
||||||
"if": "ctx.module_temp != null",
|
|
||||||
"override": true,
|
|
||||||
"field": "event.module",
|
|
||||||
"value": "{{module_temp.0}}"
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"set": {
|
|
||||||
"if": "ctx.datastream_dataset_temp != null && ctx.datastream_dataset_temp[0] == 'network_traffic'",
|
|
||||||
"field": "event.module",
|
|
||||||
"value": "{{ datastream_dataset_temp.0 }}",
|
|
||||||
"ignore_failure": true,
|
|
||||||
"ignore_empty_value": true,
|
|
||||||
"description": "Fix EA network packet capture"
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"gsub": {
|
|
||||||
"if": "ctx.event?.dataset != null && ctx.event.dataset.contains('.')",
|
|
||||||
"field": "event.dataset",
|
|
||||||
"pattern": "^[^.]*.",
|
|
||||||
"replacement": "",
|
|
||||||
"target_field": "dataset_tag_temp"
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"append": {
|
|
||||||
"if": "ctx.dataset_tag_temp != null",
|
|
||||||
"field": "tags",
|
|
||||||
"value": "{{dataset_tag_temp}}",
|
|
||||||
"allow_duplicates": false
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"set": {
|
|
||||||
"if": "ctx.network?.direction == 'egress'",
|
|
||||||
"override": true,
|
|
||||||
"field": "network.initiated",
|
|
||||||
"value": "true"
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"set": {
|
|
||||||
"if": "ctx.network?.direction == 'ingress'",
|
|
||||||
"override": true,
|
|
||||||
"field": "network.initiated",
|
|
||||||
"value": "false"
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"set": {
|
|
||||||
"if": "ctx.network?.type == 'ipv4'",
|
|
||||||
"override": true,
|
|
||||||
"field": "destination.ipv6",
|
|
||||||
"value": "false"
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"set": {
|
|
||||||
"if": "ctx.network?.type == 'ipv6'",
|
|
||||||
"override": true,
|
|
||||||
"field": "destination.ipv6",
|
|
||||||
"value": "true"
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"set": {
|
|
||||||
"if": "ctx.tags != null && ctx.tags.contains('import')",
|
|
||||||
"override": true,
|
|
||||||
"field": "data_stream.dataset",
|
|
||||||
"value": "import"
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"set": {
|
|
||||||
"if": "ctx.tags != null && ctx.tags.contains('import')",
|
|
||||||
"override": true,
|
|
||||||
"field": "data_stream.namespace",
|
|
||||||
"value": "so"
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"community_id": {
|
|
||||||
"if": "ctx.event?.dataset == 'endpoint.events.network'",
|
|
||||||
"ignore_failure": true
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"set": {
|
|
||||||
"if": "ctx.event?.module == 'fim'",
|
|
||||||
"override": true,
|
|
||||||
"field": "event.module",
|
|
||||||
"value": "file_integrity"
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"rename": {
|
|
||||||
"if": "ctx.winlog?.provider_name == 'Microsoft-Windows-Windows Defender'",
|
|
||||||
"ignore_missing": true,
|
|
||||||
"field": "winlog.event_data.Threat Name",
|
|
||||||
"target_field": "winlog.event_data.threat_name"
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"set": {
|
|
||||||
"if": "ctx?.metadata?.kafka != null",
|
|
||||||
"field": "kafka.id",
|
|
||||||
"value": "{{metadata.kafka.partition}}{{metadata.kafka.offset}}{{metadata.kafka.timestamp}}",
|
|
||||||
"ignore_failure": true
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"set": {
|
|
||||||
"if": "ctx.event?.dataset != null && ctx.event?.dataset == 'elasticsearch.server'",
|
|
||||||
"field": "event.module",
|
|
||||||
"value": "elasticsearch"
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"append": {
|
|
||||||
"field": "related.ip",
|
|
||||||
"value": [
|
|
||||||
"{{source.ip}}",
|
|
||||||
"{{destination.ip}}"
|
|
||||||
],
|
|
||||||
"allow_duplicates": false,
|
|
||||||
"if": "ctx?.event?.dataset == 'endpoint.events.network' && ctx?.source?.ip != null",
|
|
||||||
"ignore_failure": true
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"foreach": {
|
|
||||||
"field": "host.ip",
|
|
||||||
"processor": {
|
|
||||||
"append": {
|
|
||||||
"field": "related.ip",
|
|
||||||
"value": "{{_ingest._value}}",
|
|
||||||
"allow_duplicates": false
|
|
||||||
}
|
|
||||||
},
|
|
||||||
"if": "ctx?.event?.module == 'endpoint' && ctx?.host?.ip != null",
|
|
||||||
"ignore_missing": true,
|
|
||||||
"description": "Extract IPs from Elastic Agent events (host.ip) and adds them to related.ip"
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"pipeline": {
|
|
||||||
"name": ".fleet_final_pipeline-1",
|
|
||||||
"ignore_missing_pipeline": true
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"remove": {
|
|
||||||
"field": "event.agent_id_status",
|
|
||||||
"ignore_missing": true,
|
|
||||||
"if": "ctx?.event?.agent_id_status == 'auth_metadata_missing'"
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"remove": {
|
|
||||||
"field": [
|
|
||||||
"message2",
|
|
||||||
"type",
|
|
||||||
"fields",
|
|
||||||
"category",
|
|
||||||
"module",
|
|
||||||
"dataset",
|
|
||||||
"event.dataset_temp",
|
|
||||||
"dataset_tag_temp",
|
|
||||||
"module_temp",
|
|
||||||
"datastream_dataset_temp"
|
|
||||||
],
|
|
||||||
"ignore_missing": true,
|
|
||||||
"ignore_failure": true
|
|
||||||
}
|
|
||||||
}
|
|
||||||
]
|
|
||||||
}
|
|
||||||
|
|||||||
@@ -1,98 +1,9 @@
|
|||||||
{
|
{
|
||||||
"description": "kratos",
|
"description" : "kratos",
|
||||||
"processors": [
|
"processors" : [
|
||||||
{
|
{"set":{"field":"audience","value":"access","override":false,"ignore_failure":true}},
|
||||||
"set": {
|
{"set":{"field":"event.dataset","ignore_empty_value":true,"ignore_failure":true,"value":"kratos.{{{audience}}}","media_type":"text/plain"}},
|
||||||
"field": "audience",
|
{"set":{"field":"event.action","ignore_failure":true,"copy_from":"msg" }},
|
||||||
"value": "access",
|
{ "pipeline": { "name": "common" } }
|
||||||
"override": false,
|
]
|
||||||
"ignore_failure": true
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"set": {
|
|
||||||
"field": "event.dataset",
|
|
||||||
"ignore_empty_value": true,
|
|
||||||
"ignore_failure": true,
|
|
||||||
"value": "kratos.{{{audience}}}",
|
|
||||||
"media_type": "text/plain"
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"set": {
|
|
||||||
"field": "event.action",
|
|
||||||
"ignore_failure": true,
|
|
||||||
"copy_from": "msg"
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"rename": {
|
|
||||||
"field": "http_request",
|
|
||||||
"target_field": "http.request",
|
|
||||||
"ignore_failure": true,
|
|
||||||
"ignore_missing": true
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"rename": {
|
|
||||||
"field": "http_response",
|
|
||||||
"target_field": "http.response",
|
|
||||||
"ignore_failure": true,
|
|
||||||
"ignore_missing": true
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"rename": {
|
|
||||||
"field": "http.request.path",
|
|
||||||
"target_field": "http.uri",
|
|
||||||
"ignore_failure": true,
|
|
||||||
"ignore_missing": true
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"rename": {
|
|
||||||
"field": "http.request.method",
|
|
||||||
"target_field": "http.method",
|
|
||||||
"ignore_failure": true,
|
|
||||||
"ignore_missing": true
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"rename": {
|
|
||||||
"field": "http.request.method",
|
|
||||||
"target_field": "http.method",
|
|
||||||
"ignore_failure": true,
|
|
||||||
"ignore_missing": true
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"rename": {
|
|
||||||
"field": "http.request.query",
|
|
||||||
"target_field": "http.query",
|
|
||||||
"ignore_failure": true,
|
|
||||||
"ignore_missing": true
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"rename": {
|
|
||||||
"field": "http.request.headers.user-agent",
|
|
||||||
"target_field": "http.useragent",
|
|
||||||
"ignore_failure": true,
|
|
||||||
"ignore_missing": true
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"rename": {
|
|
||||||
"field": "file",
|
|
||||||
"target_field": "file.path",
|
|
||||||
"ignore_failure": true,
|
|
||||||
"ignore_missing": true
|
|
||||||
}
|
|
||||||
},
|
|
||||||
{
|
|
||||||
"pipeline": {
|
|
||||||
"name": "common"
|
|
||||||
}
|
|
||||||
}
|
|
||||||
]
|
|
||||||
}
|
}
|
||||||
@@ -27,13 +27,6 @@ elasticsearch:
|
|||||||
readonly: True
|
readonly: True
|
||||||
global: True
|
global: True
|
||||||
helpLink: elasticsearch.html
|
helpLink: elasticsearch.html
|
||||||
logsdb:
|
|
||||||
enabled:
|
|
||||||
description: Enables or disables the Elasticsearch logsdb index mode. When enabled, most logs-* datastreams will convert to logsdb from standard after rolling over.
|
|
||||||
forcedType: bool
|
|
||||||
global: True
|
|
||||||
advanced: True
|
|
||||||
helpLink: elasticsearch.html
|
|
||||||
routing:
|
routing:
|
||||||
allocation:
|
allocation:
|
||||||
disk:
|
disk:
|
||||||
@@ -84,6 +77,13 @@ elasticsearch:
|
|||||||
custom008: *pipelines
|
custom008: *pipelines
|
||||||
custom009: *pipelines
|
custom009: *pipelines
|
||||||
custom010: *pipelines
|
custom010: *pipelines
|
||||||
|
managed_integrations:
|
||||||
|
description: List of integrations to add into SOC config UI. Enter the full or partial integration name. Eg. 1password, 1pass
|
||||||
|
forcedType: "[]string"
|
||||||
|
multiline: True
|
||||||
|
global: True
|
||||||
|
advanced: True
|
||||||
|
helpLink: elasticsearch.html
|
||||||
index_settings:
|
index_settings:
|
||||||
global_overrides:
|
global_overrides:
|
||||||
index_template:
|
index_template:
|
||||||
|
|||||||
@@ -1,66 +0,0 @@
|
|||||||
# Copyright Security Onion Solutions LLC and/or licensed to Security Onion Solutions LLC under one
|
|
||||||
# or more contributor license agreements. Licensed under the Elastic License 2.0 as shown at
|
|
||||||
# https://securityonion.net/license; you may not use this file except in compliance with the
|
|
||||||
# Elastic License 2.0.
|
|
||||||
|
|
||||||
{% from 'allowed_states.map.jinja' import allowed_states %}
|
|
||||||
{% if sls.split('.')[0] in allowed_states %}
|
|
||||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
|
||||||
{% from 'ca/map.jinja' import CA %}
|
|
||||||
|
|
||||||
# Create a cert for elasticsearch
|
|
||||||
elasticsearch_key:
|
|
||||||
x509.private_key_managed:
|
|
||||||
- name: /etc/pki/elasticsearch.key
|
|
||||||
- keysize: 4096
|
|
||||||
- backup: True
|
|
||||||
- new: True
|
|
||||||
{% if salt['file.file_exists']('/etc/pki/elasticsearch.key') -%}
|
|
||||||
- prereq:
|
|
||||||
- x509: /etc/pki/elasticsearch.crt
|
|
||||||
{%- endif %}
|
|
||||||
- retry:
|
|
||||||
attempts: 5
|
|
||||||
interval: 30
|
|
||||||
|
|
||||||
elasticsearch_crt:
|
|
||||||
x509.certificate_managed:
|
|
||||||
- name: /etc/pki/elasticsearch.crt
|
|
||||||
- ca_server: {{ CA.server }}
|
|
||||||
- signing_policy: registry
|
|
||||||
- private_key: /etc/pki/elasticsearch.key
|
|
||||||
- CN: {{ GLOBALS.hostname }}
|
|
||||||
- subjectAltName: DNS:{{ GLOBALS.hostname }}, IP:{{ GLOBALS.node_ip }}
|
|
||||||
- days_remaining: 7
|
|
||||||
- days_valid: 820
|
|
||||||
- backup: True
|
|
||||||
- timeout: 30
|
|
||||||
- retry:
|
|
||||||
attempts: 5
|
|
||||||
interval: 30
|
|
||||||
cmd.run:
|
|
||||||
- name: "/usr/bin/openssl pkcs12 -inkey /etc/pki/elasticsearch.key -in /etc/pki/elasticsearch.crt -export -out /etc/pki/elasticsearch.p12 -nodes -passout pass:"
|
|
||||||
- onchanges:
|
|
||||||
- x509: /etc/pki/elasticsearch.key
|
|
||||||
|
|
||||||
elastickeyperms:
|
|
||||||
file.managed:
|
|
||||||
- replace: False
|
|
||||||
- name: /etc/pki/elasticsearch.key
|
|
||||||
- mode: 640
|
|
||||||
- group: 930
|
|
||||||
|
|
||||||
elasticp12perms:
|
|
||||||
file.managed:
|
|
||||||
- replace: False
|
|
||||||
- name: /etc/pki/elasticsearch.p12
|
|
||||||
- mode: 640
|
|
||||||
- group: 930
|
|
||||||
|
|
||||||
{% else %}
|
|
||||||
|
|
||||||
{{sls}}_state_not_allowed:
|
|
||||||
test.fail_without_changes:
|
|
||||||
- name: {{sls}}_state_not_allowed
|
|
||||||
|
|
||||||
{% endif %}
|
|
||||||
@@ -1,103 +1,91 @@
|
|||||||
{
|
{
|
||||||
"_meta": {
|
"_meta": {
|
||||||
"documentation": "https://www.elastic.co/guide/en/ecs/current/ecs-dns.html",
|
"documentation": "https://www.elastic.co/guide/en/ecs/current/ecs-dns.html",
|
||||||
"ecs_version": "1.12.2"
|
"ecs_version": "1.12.2"
|
||||||
},
|
},
|
||||||
"template": {
|
"template": {
|
||||||
"mappings": {
|
"mappings": {
|
||||||
"properties": {
|
"properties": {
|
||||||
"dns": {
|
"dns": {
|
||||||
"properties": {
|
"properties": {
|
||||||
"answers": {
|
"answers": {
|
||||||
"properties": {
|
"properties": {
|
||||||
"class": {
|
"class": {
|
||||||
"ignore_above": 1024,
|
"ignore_above": 1024,
|
||||||
"type": "keyword"
|
"type": "keyword"
|
||||||
},
|
},
|
||||||
"data": {
|
"data": {
|
||||||
"ignore_above": 1024,
|
"ignore_above": 1024,
|
||||||
"type": "keyword"
|
"type": "keyword"
|
||||||
},
|
},
|
||||||
"name": {
|
"name": {
|
||||||
"ignore_above": 1024,
|
"ignore_above": 1024,
|
||||||
"type": "keyword"
|
"type": "keyword"
|
||||||
},
|
},
|
||||||
"ttl": {
|
"ttl": {
|
||||||
"type": "long"
|
"type": "long"
|
||||||
},
|
},
|
||||||
"type": {
|
"type": {
|
||||||
"ignore_above": 1024,
|
"ignore_above": 1024,
|
||||||
"type": "keyword"
|
"type": "keyword"
|
||||||
}
|
|
||||||
},
|
|
||||||
"type": "object"
|
|
||||||
},
|
|
||||||
"header_flags": {
|
|
||||||
"ignore_above": 1024,
|
|
||||||
"type": "keyword"
|
|
||||||
},
|
|
||||||
"id": {
|
|
||||||
"ignore_above": 1024,
|
|
||||||
"type": "keyword"
|
|
||||||
},
|
|
||||||
"op_code": {
|
|
||||||
"ignore_above": 1024,
|
|
||||||
"type": "keyword"
|
|
||||||
},
|
|
||||||
"question": {
|
|
||||||
"properties": {
|
|
||||||
"class": {
|
|
||||||
"ignore_above": 1024,
|
|
||||||
"type": "keyword"
|
|
||||||
},
|
|
||||||
"name": {
|
|
||||||
"ignore_above": 1024,
|
|
||||||
"type": "keyword"
|
|
||||||
},
|
|
||||||
"registered_domain": {
|
|
||||||
"ignore_above": 1024,
|
|
||||||
"type": "keyword"
|
|
||||||
},
|
|
||||||
"subdomain": {
|
|
||||||
"ignore_above": 1024,
|
|
||||||
"type": "keyword"
|
|
||||||
},
|
|
||||||
"top_level_domain": {
|
|
||||||
"ignore_above": 1024,
|
|
||||||
"type": "keyword"
|
|
||||||
},
|
|
||||||
"type": {
|
|
||||||
"ignore_above": 1024,
|
|
||||||
"type": "keyword"
|
|
||||||
}
|
|
||||||
}
|
|
||||||
},
|
|
||||||
"query": {
|
|
||||||
"properties" :{
|
|
||||||
"type":{
|
|
||||||
"ignore_above": 1024,
|
|
||||||
"type": "keyword"
|
|
||||||
},
|
|
||||||
"type_name": {
|
|
||||||
"ignore_above": 1024,
|
|
||||||
"type": "keyword"
|
|
||||||
}
|
|
||||||
}
|
|
||||||
},
|
|
||||||
"resolved_ip": {
|
|
||||||
"type": "ip"
|
|
||||||
},
|
|
||||||
"response_code": {
|
|
||||||
"ignore_above": 1024,
|
|
||||||
"type": "keyword"
|
|
||||||
},
|
|
||||||
"type": {
|
|
||||||
"ignore_above": 1024,
|
|
||||||
"type": "keyword"
|
|
||||||
}
|
|
||||||
}
|
|
||||||
}
|
}
|
||||||
|
},
|
||||||
|
"type": "object"
|
||||||
|
},
|
||||||
|
"header_flags": {
|
||||||
|
"ignore_above": 1024,
|
||||||
|
"type": "keyword"
|
||||||
|
},
|
||||||
|
"id": {
|
||||||
|
"ignore_above": 1024,
|
||||||
|
"type": "keyword"
|
||||||
|
},
|
||||||
|
"op_code": {
|
||||||
|
"ignore_above": 1024,
|
||||||
|
"type": "keyword"
|
||||||
|
},
|
||||||
|
"question": {
|
||||||
|
"properties": {
|
||||||
|
"class": {
|
||||||
|
"ignore_above": 1024,
|
||||||
|
"type": "keyword"
|
||||||
|
},
|
||||||
|
"name": {
|
||||||
|
"ignore_above": 1024,
|
||||||
|
"type": "keyword"
|
||||||
|
},
|
||||||
|
"registered_domain": {
|
||||||
|
"ignore_above": 1024,
|
||||||
|
"type": "keyword"
|
||||||
|
},
|
||||||
|
"subdomain": {
|
||||||
|
"ignore_above": 1024,
|
||||||
|
"type": "keyword"
|
||||||
|
},
|
||||||
|
"top_level_domain": {
|
||||||
|
"ignore_above": 1024,
|
||||||
|
"type": "keyword"
|
||||||
|
},
|
||||||
|
"type": {
|
||||||
|
"ignore_above": 1024,
|
||||||
|
"type": "keyword"
|
||||||
|
}
|
||||||
|
}
|
||||||
|
},
|
||||||
|
"resolved_ip": {
|
||||||
|
"type": "ip"
|
||||||
|
},
|
||||||
|
"response_code": {
|
||||||
|
"ignore_above": 1024,
|
||||||
|
"type": "keyword"
|
||||||
|
},
|
||||||
|
"type": {
|
||||||
|
"ignore_above": 1024,
|
||||||
|
"type": "keyword"
|
||||||
}
|
}
|
||||||
|
}
|
||||||
}
|
}
|
||||||
|
}
|
||||||
}
|
}
|
||||||
|
}
|
||||||
}
|
}
|
||||||
@@ -15,13 +15,6 @@
|
|||||||
"ignore_above": 1024,
|
"ignore_above": 1024,
|
||||||
"type": "keyword"
|
"type": "keyword"
|
||||||
},
|
},
|
||||||
"bytes": {
|
|
||||||
"properties": {
|
|
||||||
"missing": {
|
|
||||||
"type": "long"
|
|
||||||
}
|
|
||||||
}
|
|
||||||
},
|
|
||||||
"code_signature": {
|
"code_signature": {
|
||||||
"properties": {
|
"properties": {
|
||||||
"digest_algorithm": {
|
"digest_algorithm": {
|
||||||
|
|||||||
@@ -2,7 +2,7 @@
|
|||||||
"template": {
|
"template": {
|
||||||
"settings": {
|
"settings": {
|
||||||
"index": {
|
"index": {
|
||||||
"final_pipeline": "global@custom"
|
"final_pipeline": ".fleet_final_pipeline-1"
|
||||||
}
|
}
|
||||||
},
|
},
|
||||||
"mappings": {
|
"mappings": {
|
||||||
|
|||||||
@@ -14,9 +14,8 @@ set -e
|
|||||||
# Check to see if we have extracted the ca cert.
|
# Check to see if we have extracted the ca cert.
|
||||||
if [ ! -f /opt/so/saltstack/local/salt/elasticsearch/cacerts ]; then
|
if [ ! -f /opt/so/saltstack/local/salt/elasticsearch/cacerts ]; then
|
||||||
docker run -v /etc/pki/ca.crt:/etc/ssl/ca.crt --name so-elasticsearchca --user root --entrypoint jdk/bin/keytool {{ GLOBALS.registry_host }}:5000/{{ GLOBALS.image_repo }}/so-elasticsearch:$ELASTIC_AGENT_TARBALL_VERSION -keystore /usr/share/elasticsearch/jdk/lib/security/cacerts -alias SOSCA -import -file /etc/ssl/ca.crt -storepass changeit -noprompt
|
docker run -v /etc/pki/ca.crt:/etc/ssl/ca.crt --name so-elasticsearchca --user root --entrypoint jdk/bin/keytool {{ GLOBALS.registry_host }}:5000/{{ GLOBALS.image_repo }}/so-elasticsearch:$ELASTIC_AGENT_TARBALL_VERSION -keystore /usr/share/elasticsearch/jdk/lib/security/cacerts -alias SOSCA -import -file /etc/ssl/ca.crt -storepass changeit -noprompt
|
||||||
# Make sure symbolic links are followed when copying from container
|
docker cp so-elasticsearchca:/usr/share/elasticsearch/jdk/lib/security/cacerts /opt/so/saltstack/local/salt/elasticsearch/cacerts
|
||||||
docker cp -L so-elasticsearchca:/usr/share/elasticsearch/jdk/lib/security/cacerts /opt/so/saltstack/local/salt/elasticsearch/cacerts
|
docker cp so-elasticsearchca:/etc/ssl/certs/ca-certificates.crt /opt/so/saltstack/local/salt/elasticsearch/tls-ca-bundle.pem
|
||||||
docker cp -L so-elasticsearchca:/etc/pki/ca-trust/extracted/pem/tls-ca-bundle.pem /opt/so/saltstack/local/salt/elasticsearch/tls-ca-bundle.pem
|
|
||||||
docker rm so-elasticsearchca
|
docker rm so-elasticsearchca
|
||||||
echo "" >> /opt/so/saltstack/local/salt/elasticsearch/tls-ca-bundle.pem
|
echo "" >> /opt/so/saltstack/local/salt/elasticsearch/tls-ca-bundle.pem
|
||||||
echo "sosca" >> /opt/so/saltstack/local/salt/elasticsearch/tls-ca-bundle.pem
|
echo "sosca" >> /opt/so/saltstack/local/salt/elasticsearch/tls-ca-bundle.pem
|
||||||
|
|||||||
@@ -121,7 +121,7 @@ if [ ! -f $STATE_FILE_SUCCESS ]; then
|
|||||||
echo "Loading Security Onion index templates..."
|
echo "Loading Security Onion index templates..."
|
||||||
shopt -s extglob
|
shopt -s extglob
|
||||||
{% if GLOBALS.role == 'so-heavynode' %}
|
{% if GLOBALS.role == 'so-heavynode' %}
|
||||||
pattern="!(*1password*|*aws*|*azure*|*cloudflare*|*elastic_agent*|*fim*|*github*|*google*|*osquery*|*system*|*windows*|*endpoint*|*elasticsearch*|*generic*|*fleet_server*|*soc*)"
|
pattern="!(*1password*|*aws*|*azure*|*cloudflare*|*elastic_agent*|*fim*|*github*|*google*|*osquery*|*system*|*windows*)"
|
||||||
{% else %}
|
{% else %}
|
||||||
pattern="*"
|
pattern="*"
|
||||||
{% endif %}
|
{% endif %}
|
||||||
|
|||||||
@@ -27,12 +27,14 @@ iptables_config:
|
|||||||
- source: salt://firewall/iptables.jinja
|
- source: salt://firewall/iptables.jinja
|
||||||
- template: jinja
|
- template: jinja
|
||||||
|
|
||||||
|
{% if grains.os_family == 'RedHat' %}
|
||||||
disable_firewalld:
|
disable_firewalld:
|
||||||
service.dead:
|
service.dead:
|
||||||
- name: firewalld
|
- name: firewalld
|
||||||
- enable: False
|
- enable: False
|
||||||
- require:
|
- require:
|
||||||
- file: iptables_config
|
- file: iptables_config
|
||||||
|
{% endif %}
|
||||||
|
|
||||||
iptables_restore:
|
iptables_restore:
|
||||||
cmd.run:
|
cmd.run:
|
||||||
@@ -42,6 +44,7 @@ iptables_restore:
|
|||||||
- onlyif:
|
- onlyif:
|
||||||
- iptables-restore --test {{ iptmap.configfile }}
|
- iptables-restore --test {{ iptmap.configfile }}
|
||||||
|
|
||||||
|
{% if grains.os_family == 'RedHat' %}
|
||||||
enable_firewalld:
|
enable_firewalld:
|
||||||
service.running:
|
service.running:
|
||||||
- name: firewalld
|
- name: firewalld
|
||||||
@@ -49,6 +52,7 @@ enable_firewalld:
|
|||||||
- onfail:
|
- onfail:
|
||||||
- file: iptables_config
|
- file: iptables_config
|
||||||
- cmd: iptables_restore
|
- cmd: iptables_restore
|
||||||
|
{% endif %}
|
||||||
|
|
||||||
{% else %}
|
{% else %}
|
||||||
|
|
||||||
|
|||||||
@@ -1,6 +1,14 @@
|
|||||||
{% set iptmap = {
|
{% set iptmap = salt['grains.filter_by']({
|
||||||
'service': 'iptables',
|
'Debian': {
|
||||||
'iptpkg': 'iptables-nft',
|
'service': 'netfilter-persistent',
|
||||||
'persistpkg': 'iptables-nft-services',
|
'iptpkg': 'iptables',
|
||||||
'configfile': '/etc/sysconfig/iptables'
|
'persistpkg': 'iptables-persistent',
|
||||||
} %}
|
'configfile': '/etc/iptables/rules.v4'
|
||||||
|
},
|
||||||
|
'RedHat': {
|
||||||
|
'service': 'iptables',
|
||||||
|
'iptpkg': 'iptables-nft',
|
||||||
|
'persistpkg': 'iptables-nft-services',
|
||||||
|
'configfile': '/etc/sysconfig/iptables'
|
||||||
|
},
|
||||||
|
}) %}
|
||||||
|
|||||||
@@ -1,5 +1,5 @@
|
|||||||
{%- from 'vars/globals.map.jinja' import GLOBALS %}
|
{%- from 'vars/globals.map.jinja' import GLOBALS %}
|
||||||
{%- from 'docker/docker.map.jinja' import DOCKERMERGED %}
|
{%- from 'docker/docker.map.jinja' import DOCKER %}
|
||||||
{%- from 'firewall/map.jinja' import FIREWALL_MERGED %}
|
{%- from 'firewall/map.jinja' import FIREWALL_MERGED %}
|
||||||
{%- set role = GLOBALS.role.split('-')[1] %}
|
{%- set role = GLOBALS.role.split('-')[1] %}
|
||||||
{%- from 'firewall/containers.map.jinja' import NODE_CONTAINERS %}
|
{%- from 'firewall/containers.map.jinja' import NODE_CONTAINERS %}
|
||||||
@@ -8,9 +8,9 @@
|
|||||||
{%- set D1 = [] %}
|
{%- set D1 = [] %}
|
||||||
{%- set D2 = [] %}
|
{%- set D2 = [] %}
|
||||||
{%- for container in NODE_CONTAINERS %}
|
{%- for container in NODE_CONTAINERS %}
|
||||||
{%- set IP = DOCKERMERGED.containers[container].ip %}
|
{%- set IP = DOCKER.containers[container].ip %}
|
||||||
{%- if DOCKERMERGED.containers[container].port_bindings is defined %}
|
{%- if DOCKER.containers[container].port_bindings is defined %}
|
||||||
{%- for binding in DOCKERMERGED.containers[container].port_bindings %}
|
{%- for binding in DOCKER.containers[container].port_bindings %}
|
||||||
{#- cant split int so we convert to string #}
|
{#- cant split int so we convert to string #}
|
||||||
{%- set binding = binding|string %}
|
{%- set binding = binding|string %}
|
||||||
{#- split the port binding by /. if proto not specified, default is tcp #}
|
{#- split the port binding by /. if proto not specified, default is tcp #}
|
||||||
@@ -33,13 +33,13 @@
|
|||||||
{%- set hostPort = bsa[0] %}
|
{%- set hostPort = bsa[0] %}
|
||||||
{%- set containerPort = bsa[1] %}
|
{%- set containerPort = bsa[1] %}
|
||||||
{%- endif %}
|
{%- endif %}
|
||||||
{%- do PR.append("-A POSTROUTING -s " ~ DOCKERMERGED.containers[container].ip ~ "/32 -d " ~ DOCKERMERGED.containers[container].ip ~ "/32 -p " ~ proto ~ " -m " ~ proto ~ " --dport " ~ containerPort ~ " -j MASQUERADE") %}
|
{%- do PR.append("-A POSTROUTING -s " ~ DOCKER.containers[container].ip ~ "/32 -d " ~ DOCKER.containers[container].ip ~ "/32 -p " ~ proto ~ " -m " ~ proto ~ " --dport " ~ containerPort ~ " -j MASQUERADE") %}
|
||||||
{%- if bindip | length and bindip != '0.0.0.0' %}
|
{%- if bindip | length and bindip != '0.0.0.0' %}
|
||||||
{%- do D1.append("-A DOCKER -d " ~ bindip ~ "/32 ! -i sobridge -p " ~ proto ~ " -m " ~ proto ~ " --dport " ~ hostPort ~ " -j DNAT --to-destination " ~ DOCKERMERGED.containers[container].ip ~ ":" ~ containerPort) %}
|
{%- do D1.append("-A DOCKER -d " ~ bindip ~ "/32 ! -i sobridge -p " ~ proto ~ " -m " ~ proto ~ " --dport " ~ hostPort ~ " -j DNAT --to-destination " ~ DOCKER.containers[container].ip ~ ":" ~ containerPort) %}
|
||||||
{%- else %}
|
{%- else %}
|
||||||
{%- do D1.append("-A DOCKER ! -i sobridge -p " ~ proto ~ " -m " ~ proto ~ " --dport " ~ hostPort ~ " -j DNAT --to-destination " ~ DOCKERMERGED.containers[container].ip ~ ":" ~ containerPort) %}
|
{%- do D1.append("-A DOCKER ! -i sobridge -p " ~ proto ~ " -m " ~ proto ~ " --dport " ~ hostPort ~ " -j DNAT --to-destination " ~ DOCKER.containers[container].ip ~ ":" ~ containerPort) %}
|
||||||
{%- endif %}
|
{%- endif %}
|
||||||
{%- do D2.append("-A DOCKER -d " ~ DOCKERMERGED.containers[container].ip ~ "/32 ! -i sobridge -o sobridge -p " ~ proto ~ " -m " ~ proto ~ " --dport " ~ containerPort ~ " -j ACCEPT") %}
|
{%- do D2.append("-A DOCKER -d " ~ DOCKER.containers[container].ip ~ "/32 ! -i sobridge -o sobridge -p " ~ proto ~ " -m " ~ proto ~ " --dport " ~ containerPort ~ " -j ACCEPT") %}
|
||||||
{%- endfor %}
|
{%- endfor %}
|
||||||
{%- endif %}
|
{%- endif %}
|
||||||
{%- endfor %}
|
{%- endfor %}
|
||||||
@@ -52,7 +52,7 @@
|
|||||||
:DOCKER - [0:0]
|
:DOCKER - [0:0]
|
||||||
-A PREROUTING -m addrtype --dst-type LOCAL -j DOCKER
|
-A PREROUTING -m addrtype --dst-type LOCAL -j DOCKER
|
||||||
-A OUTPUT ! -d 127.0.0.0/8 -m addrtype --dst-type LOCAL -j DOCKER
|
-A OUTPUT ! -d 127.0.0.0/8 -m addrtype --dst-type LOCAL -j DOCKER
|
||||||
-A POSTROUTING -s {{DOCKERMERGED.range}} ! -o sobridge -j MASQUERADE
|
-A POSTROUTING -s {{DOCKER.range}} ! -o sobridge -j MASQUERADE
|
||||||
{%- for rule in PR %}
|
{%- for rule in PR %}
|
||||||
{{ rule }}
|
{{ rule }}
|
||||||
{%- endfor %}
|
{%- endfor %}
|
||||||
|
|||||||
@@ -1,11 +1,11 @@
|
|||||||
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
{% from 'vars/globals.map.jinja' import GLOBALS %}
|
||||||
{% from 'docker/docker.map.jinja' import DOCKERMERGED %}
|
{% from 'docker/docker.map.jinja' import DOCKER %}
|
||||||
{% import_yaml 'firewall/defaults.yaml' as FIREWALL_DEFAULT %}
|
{% import_yaml 'firewall/defaults.yaml' as FIREWALL_DEFAULT %}
|
||||||
|
|
||||||
{# add our ip to self #}
|
{# add our ip to self #}
|
||||||
{% do FIREWALL_DEFAULT.firewall.hostgroups.self.append(GLOBALS.node_ip) %}
|
{% do FIREWALL_DEFAULT.firewall.hostgroups.self.append(GLOBALS.node_ip) %}
|
||||||
{# add dockernet range #}
|
{# add dockernet range #}
|
||||||
{% do FIREWALL_DEFAULT.firewall.hostgroups.dockernet.append(DOCKERMERGED.range) %}
|
{% do FIREWALL_DEFAULT.firewall.hostgroups.dockernet.append(DOCKER.range) %}
|
||||||
|
|
||||||
{% if GLOBALS.role == 'so-idh' %}
|
{% if GLOBALS.role == 'so-idh' %}
|
||||||
{% from 'idh/opencanary_config.map.jinja' import IDH_PORTGROUPS %}
|
{% from 'idh/opencanary_config.map.jinja' import IDH_PORTGROUPS %}
|
||||||
|
|||||||
@@ -1,3 +1,3 @@
|
|||||||
global:
|
global:
|
||||||
pcapengine: SURICATA
|
pcapengine: STENO
|
||||||
pipeline: REDIS
|
pipeline: REDIS
|
||||||
Some files were not shown because too many files have changed in this diff Show More
Reference in New Issue
Block a user